If you missed the Conference or the CTF, please register here to get access to the recording sessions and to get notified when CTF content be available for download.
On May 1, 2020 SANS and Dragos, Inc. joined forces to provide a fully virtual conference open for free to the Industrial Control Systems (ICS) community. The conference shared technical insights, lessons learned, and best practices for ICS/OT cybersecurity. The conference content covered a variety of material including how to operationalize ICS intel, new ways to attack controllers, and incident response best practices.
The DISC – SANS ICS Virtual Conference is by far the biggest cybersecurity event ever run, with more than 8,000 people tuning into for two days of relevant content for the ICS community.
“It is always impressive to see the passion and dedication of our security community. Everyone is busy, yet thousands showed up because their focus on and interest in ICS/OT cybersecurity. Thank you to everyone who took the timeout to learn and engage!”
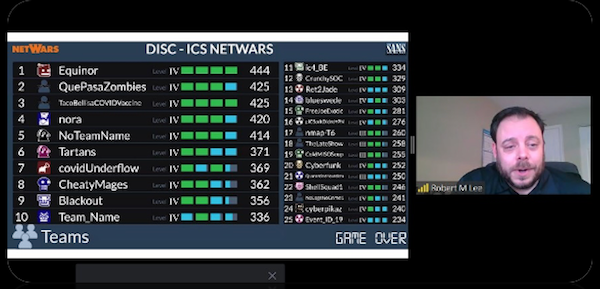
Conference chairs Robert M. Lee and Tim Conway understood it was important to offer a one-of-a-kind conference that could highlight the most up-to-date content as well as a provide an opportunity for attendees to test their skills. For days, the teams at Dragos and SANS worked together to provide the community with a unique “Capture the Flag” (CTF) Challenge to test their skills.

The result? An ICS CTF developed with a unique data set which allowed competitors to conquer several levels of difficulty. Winners were announced at the conference, along with a detailed session that went over results and answers presented by Austin Scott, Principal Industrial Penetration Tester, Dragos Inc., and Jon Lavender, Chief Technology Officer and Co-Founder, Dragos Inc.
Reviews of the DICS ICS Capture the Flag (CTF):
"Thank you for putting this together. It was a great learning experience. I look forward to being able to go over how to solve the questions."
"Had a blast dusting off the WireShark commands and jumping in. Thanks for putting this together!"
"Love the game, hate the content - but just because I've never seen/read/heard about ICS before this! AMAZING. Thank you for the great experience!"
"The content is great, better than the last several netwars events I have participated in. Kudos to the team that developed this."
"I love the product and deeply appreciate being able to do this at home and for free! "
DISC SANS Virtual Conference CTF Challenge – Unique Dataset
The DISC – SANS ICS NetWars Challenge featured four levels of ICS tailored learning opportunities: The SANS ICS team developed Level 1 and Level 2 questions related to ICS architectures, protocols, configurations, standards, ICS hardware and software components, as well as logic troubleshooting and specific device configuration challenges. Level 3 and Level 4 featured an attack orchestrated against the range by the Dragos red team for defenders to review and analyze. In addition, there were a wide variety of flags to find, so attendees could test their ICS network security skills.
This was a gift form SANS & Dragos Inc., to the ICS community in the hopes that attendees could learn more about ICS and get excited about such a wonderful community of asset owners and operators, such as electric power, oil and gas, water, manufacturing, mining, and transportation providers, to name a few.
The data set is also accompanied by the questions and answers. Attendees might use this data set for self-training; it is not meant for commercial purposes and such use is strictly prohibited. The skills required to compete the challenge map directly to the SANS ICS410: ICS/SCADA Security Essentials, ICS456: Essentials for NERC Critical Infrastructure Protection , ICS515: ICS Active Defense and Incident Response, and ICS612: ICS Cybersecurity In-Depth courses.
One Day of full content, networking, Q&A, and above all learning
The conference started with opening remarks by conference Co-chairs Tim Conway and Robert M. Lee, followed by a presentation from Jason Christopher, Principal Cyber Risk Advisor from Dragos, Inc. and SANS Certified Instructor.
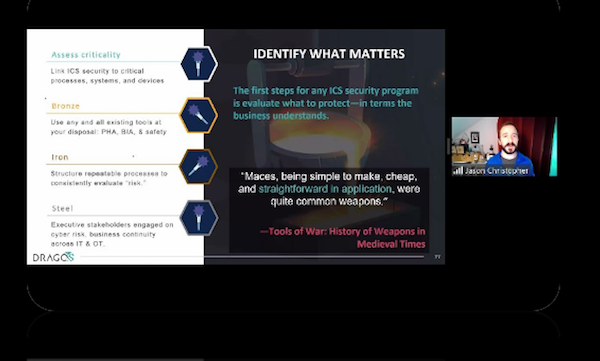
Christopher showed real use cases to teach attendees practical steps in either creating or refining their ICS-specific security program.
"When we combine technology with the right people and robust processes, organizations create a strong culture of security and forge lasting legacies for critical infrastructure protection.” he said.
Reviews of Jason Christopher's session:
"Concise and full of well illustrated information. I think this was my first time hearing Jason but I hope to hear him more in the future. The crucible illustrations with the different tools and their relative materials helped drive points home for not only myself but, I'm sure, much of the audience. I've this seen and heard the subject matter discussed in the past with very dry and drawn out guidelines often losing most people's attention in the first 5 minutes. Jason clearly knew his content and his delivery was darn near flawless. Although my memory can be quite flawed, Jason's knowledge and illustrations throughout the presentation will now be one of the best models I'll be able to easily recall. Well done and thank you for presenting!"
"This presentation was very useful. Management expressed interest in an initial level of cyber measurements, and the crucible provides a good starting framework on which to start and develop a scale."
The conference gave special focus to ICS security efforts that can be accomplished with minimal effort during slow down periods and right from home, such as building an ICS Range and DIY for home learning.
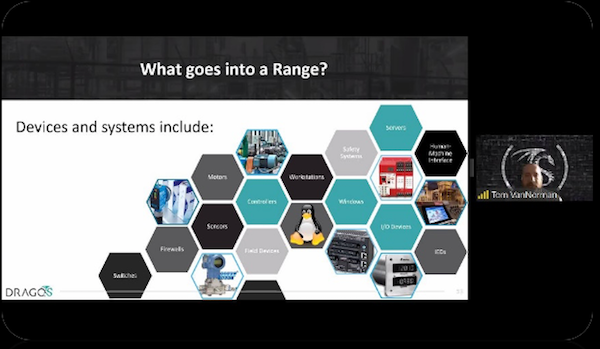
Tom VanNorman, Director of Engineering Services at Dragos, Inc. started his presentation with this question:
“Are you thinking about building your own ICS Range, but you have no idea where to start?”
He then proceeded to show attendees the pros and cons of different configurations as well first-hand knowledge of things that he found that work and do not work when it comes to starting projects for personal enrichment or for work.
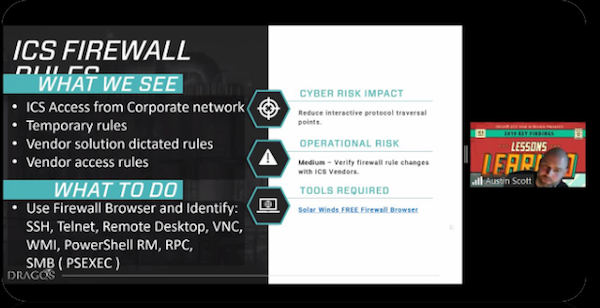
Continuing by providing attendees with simple wins during slowdowns, Austin Scott, Principal Industrial Penetration Tester, Dragos, Inc., talked about how the COVID-19 pandemic had added constraints to the ICS industry to move ICS cyber security programs forward.
Scott detailed several ways that ICS cybersecurity teams can work with existing technologies and infrastructure to identify and reduce cyber risk.
“Many of these recommendations can be done remotely and have a very low chance of inadvertently causing any operational issues,” he said.
Reviews of Austin Scott's session:
"Austin's presentation was excellent. He brought up some great tools that will definitely help us get better visibility into our networks right away."
"Awesome presentation! Thank you. I'll use some of your points in my own analysis and also forward this presentation to my pentest team so that they can have a better view on ICS world (they are still new there but am sure they are eager to learn more!!"
"It is very good to hear from people who know about the topic and can contribute to the dissemination of knowledge and in such a simple way to understand. It contributed a lot to my knowledge."
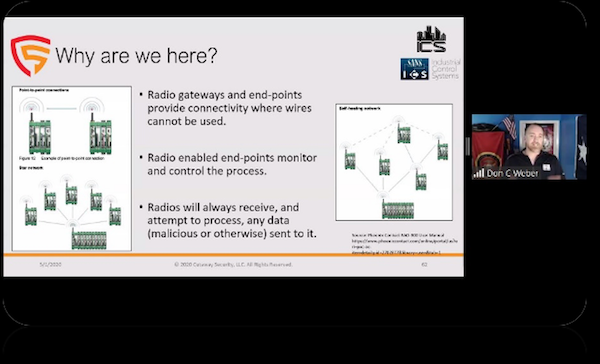
Don C. Weber, Instructor SANS ICS410: ICS/SCADA Security Essentials & HOSTED: Assessing and Exploiting Control Systems courses at SANS, took the virtual stage to review the capabilities of a wireless gateway, identifying the potential attacks on the technology, and outlining the methods to mitigate the threats.
“Security assessments help an organization understand the strengths and weaknesses of a technology. Technologies that provide public access to an environment, particularly those with operational technologies, deserve a very close look” he said.
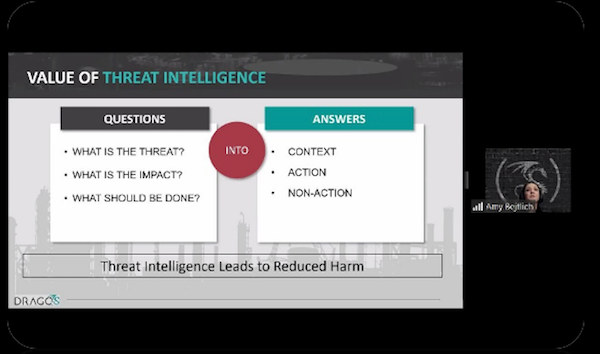
Threat intelligence was another big topic at the DISC – SANS ICS conference, as it allows asset owners and operations to make better cybersecurity decisions for ICS/OT environments. However, it is not easy.
Sergio Caltagirone, VP of Threat Intelligence, Dragos Inc., and Amy Bejtlich, Director of Threat Intelligence, Dragos Inc. discussed how to consume and digest threat intelligence to make it usable, and your operations better than before.
They addressed questions such as:
Do you need a "threat intelligence team?" How would you form one? Does your SOC need to know about threat intelligence? How do you measure the benefit of threat intelligence? They answer these questions and more.
Reviews of Sergio Caltagirone & Amy Bejtlich's session:
"Extremely important topic that is not well understood nor implemented asset owners. I really appreciated the point "Intelligence not used is of no value"
"Sergio - extremely good presentation. Specifically the points on data collection strategy and its implications, as well as the following emphasis on the threat classes and their understanding as vital for prioritizing defenses - spot on. Also the "what to use TI on and how to scale it" - great, useful and well articulated."
"Fantastic talk on ICS intelligence, and there was quite a bit that could be leveraged to teach folks about TI in general."
Managing and understanding the risk of vulnerabilities within ICS is crucial in protecting the delivery of the function. Katherine Vajda, Senior Intelligence and Vulnerability Analyst, Dragos, Inc., discussed highlights from the 2019 vulnerability year in review report. She went over lessons learned about these vulnerabilities and what to do with this information.
She went in-depth into processes and drivers for prioritizing and understanding the risks of vulnerabilities within ICS and how to get the best ROI on your efforts involving mitigation.
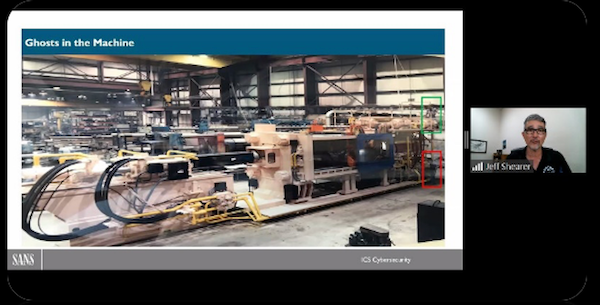
The second part of the Conference started with a presentation on ICS Cyber Attacks in the future. Jason Dely and Jeff Shearer, SANS Institute, Instructors and ICS612: ICS Cybersecurity In-Depth course Co-Authors provided a live demonstration of some common attack objectives and interesting ways to achieve those goals by attacking the control system through the control system itself.
Reviews of Jason Dely and Jeff Shearer's session:
"Demonstrations and visuals are excellent. This was a phenomenal presentation of what can be done in ICS to make it very clear to someone new to ICS. Lots of information to process here such that this will probably require watching a couple times to capture it all, but it never felt heavy or dense in watching it the first time."
"Awesome information! I found the demo very good for reinforcing the information....way more valuable than just power point."
"Great job Jeff and Jason! Really good examples of PID controls and potential compromises/mitigations."
One of the highlights of the conference was the presentation from Conference co-chair Tim Conway, SANS ICS Curriculum lead, as he covered new insights on upcoming changes to NERC CIP and commentary on the Executive Order. He also provided Incident Response guidance beyond the current requirements.
“There are benefits and challenges that organizations need to consider in relation to the new CIP-008-6 Standard going into effect starting Jan 1 next year,” he said.
Attendee feedback
As we welcomed 8,000+ attendees throughout the two-day DISC SANS Conference, we are thankful that we reached our goals to provide this free conference to the community. But do not take our word for it! Listen to what some of our attendees said about their learning experience at the conference:
"I’ve been to entire conferences and not received as much usable information in three days as I did in these fifteen minutes!"
“The presentation gave me some serious food for thought about application and evaluation of my current environment. Great takeaways.”
"Fantastic talk on ICS intelligence, and there was quite a bit that could be leveraged to teach folks about TI in general."
"I've been afraid by the 4 intelligence "sampling" depending on the audience (the one for the machine bottom/right) in Amy'slide but the next one was conform with the 3 types. Then the repetition of "Boogie Man" from Sergio sent my brain to the AC/DC song (the band, not Active Defense Cyber Cycle) ;) More seriously, winks aside, great presentations. Many thanks for sharing with us !
Extremely important topic that is not well understood nor implemented asset owners. I really appreciated the point "Intelligence not used is of no value"
"Really an excellent presentation and coverage of what threat intelligence really is, how to use it, and what kinds of practices can take advantage of it. All around, this was a very well-done presentation of pretty much how to really get smart about security in general."
Thank you for attending. We look forward the DISC - SANS ICS Virtual Conference 2021!