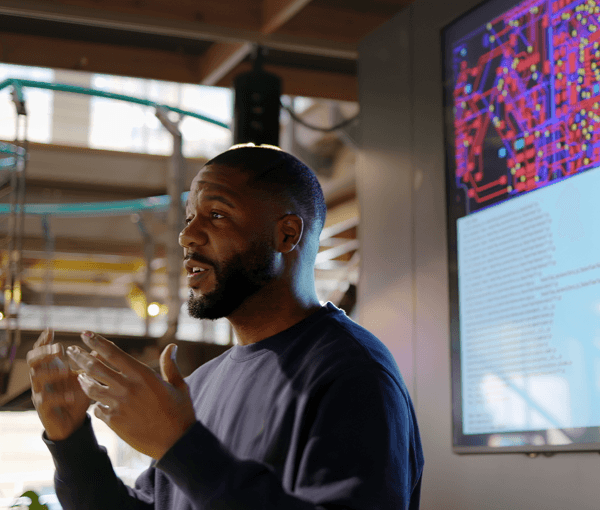
Robert M. Lee
FellowCEO at Dragos, Inc
Specialities
Industrial Control Systems Security, Digital Forensics and Incident Response

Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsIndustrial Control Systems Security, Digital Forensics and Incident Response

Robert M. Lee sets the standard for modern industrial defense. A SANS Fellow and CEO and Co-Founder of Dragos, Inc., Robert is the author of SANS ICS515: ICS Visibility, Detection, and Response, lead author of SANS FOR578: Cyber Threat Intelligence, and co-author of SANS ICS310: ICS Cybersecurity Foundations. He brings real incidents, clear models, and hands-on labs to every class, showing not just how adversaries operate, but how defenders win.
I’ve been studying and working in the intelligence field for almost 10 years and it amazes me the amount of things that I still have to learn and how the field evolves. Rob does a great job at pulling out the key concepts while still bringing in new and relevant content.
Rob is an awesome teacher. Love the real world experience & stories. Really improves the class.
This course is terrific! Class discussion and Rob's relevant case studies are extremely helpful for better understanding the content.
Here are upcoming opportunities to train with this expert instructor.
Explore content featuring this instructor’s insights and expertise.
Grounded in current SANS research and frontline operational experience, this one-hour session brings together Tim Conway, Robert M. Lee, Jason D. Christopher, and Dean Parsons to deliver leadership-level guidance for practitioners and executives.
The threat landscape won’t wait—and neither should you. Register now for this essential webinar and protect your organization’s operational technology from costly breaches.

As cyber threats become increasingly advanced and persistent, traditional perimeter-based defenses are no longer sufficient to protect critical infrastructure.

OT ransomware is a growing threat to any organization that relies on ICS/OT to power its operations. Whether securing critical infrastructure or ensuring the continuity of manufacturing, pharmaceuticals, food and beverage production, or other industrial processes, protecting these environments is essential.

SANS is excited to launch the SANS ICS/OT Practice Area under the leadership of SANS Fellow Robert M. Lee. Building on the vision of the late Michael Assante, this initiative is designed to enhance engagement with the cybersecurity community by tailoring course accessibility, content development, and strategic outreach to better serve the ICS/OT community.

Discover how the new ICS310: ICS Cybersecurity Foundations course is transforming the way professionals enter the critical field of ICS/OT cybersecurity. The world relies on critical infrastructure for all aspects of daily life, and sectors across the board have integrated Industrial Control Systems (ICS) and Operational Technology (OT) into their key operations. This evolution has created a pressing need for a uniquely skilled, diverse workforce equipped with expertise in engineering, operations, IT/OT, and cybersecurity.

In an era where cybersecurity threats are escalating, the oversight of Industrial Control Systems (ICS) is more critical than ever. Join us for an exclusive panel discussion with SANS instructors Robert M. Lee, Tim Conway, Dean Parsons, and Jason Christopher, as they address cybersecurity leaders on the imperative of securing ICS.

The Dragos OT Cybersecurity Year in Review is a mainstay for ICS asset owners and defenders to stay abreast of cyber threats, vulnerabilities, and frontline observations from the previous year. Covering the key OT cybersecurity events that shaped the threat landscape for industrial sectors, how the ICS community is performing, areas of improvement for safe and reliable operations.Join Dragos CEO and SANS Fellow Robert M. Lee for a look at the most important OT cybersecurity events and lessons learned in 2023. This webinar features exclusive data-driven analysis and recommendations on:

This talk will give an introduction to ICS/OT followed by an in depth discussion on the changes that are taking place in the industrial world such as digital transformation as a precursor to an in-depth discussion on the threats. The talk will cover new adversary groups targeting industrial networks, the trends to watch, and make recommendations with a walkthrough of the SANS ICS five critical controls.This talk is accessible to everyone of any background.

The ICS/OT community has long suffered from a lack of insight into cyber threats, vulnerabilities, and incident response observations. The annual Dragos ICS/OT Cybersecurity Year in Review provides a comprehensive look at the events that shaped the ICS/OT community and the current threat landscape. It also reports on how the community is performing, and surfaces areas of improvement needed to provide safe and reliable operations.

SANS authors and instructors Robert M. Lee and Tim Conway have been working with the community to analyze all the known ICS cyber attacks for the purpose of creating the most important cybersecurity controls for organizations to implement.

The ICS/OT community has long suffered from a lack of insight into cyber threats, vulnerabilities, and incident response observations. The annual Dragos ICS/OT Year in Review reports on how the community is performing and surfaces areas of improvement needed to provide safe and reliable operations.
Review relevant educational resources made with contribution from this instructor.