On January 21st and 22nd, thousands tuned in for the 9th annual Cyber Threat Intelligence (CTI) Summit. Over two days, the CTI community came together for in-depth presentations and panel discussions focused on analytic techniques, case studies, and methods for producing actionable intelligence. It was a great opportunity for cybersecurity professionals and those new to the field.
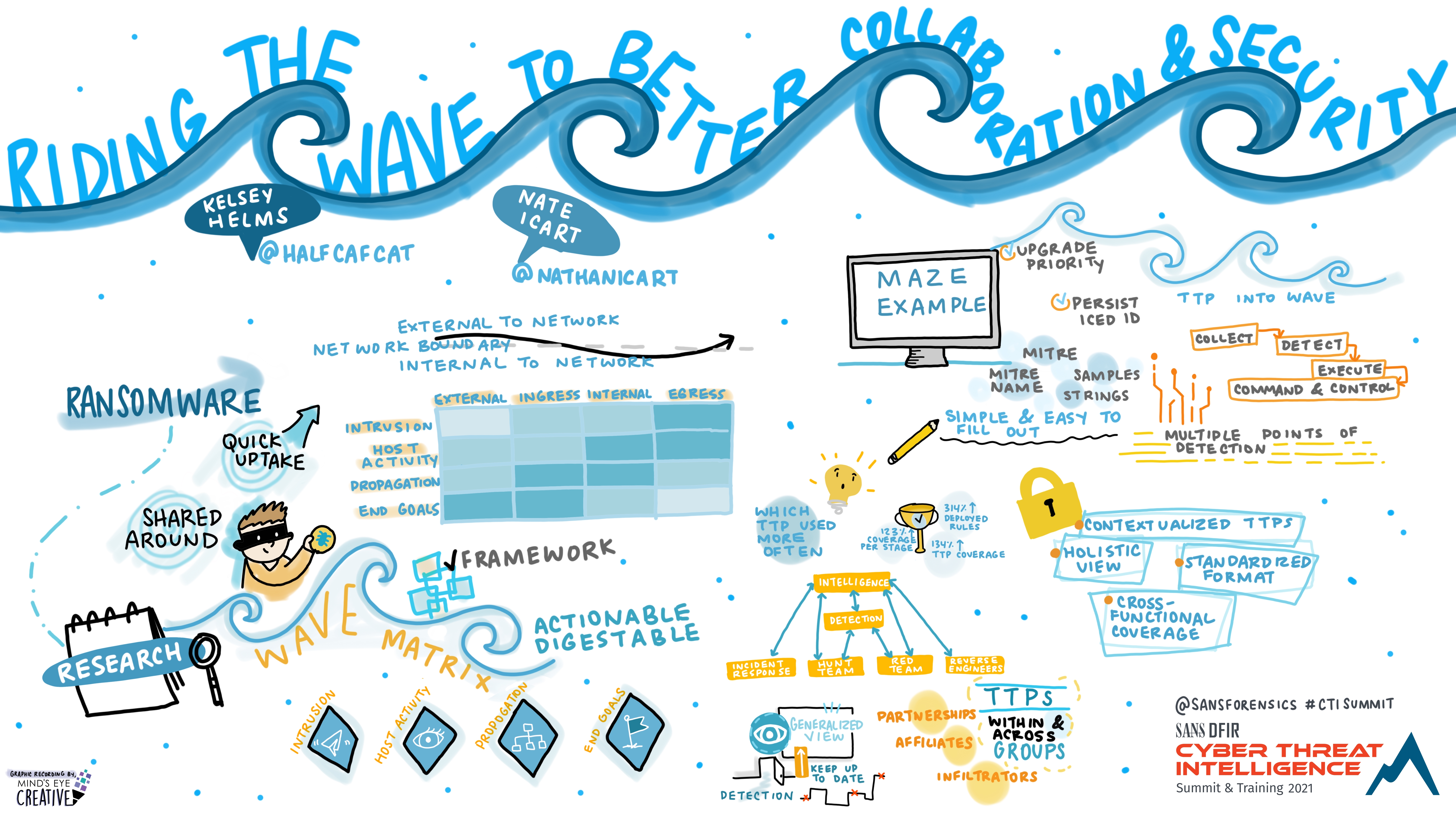
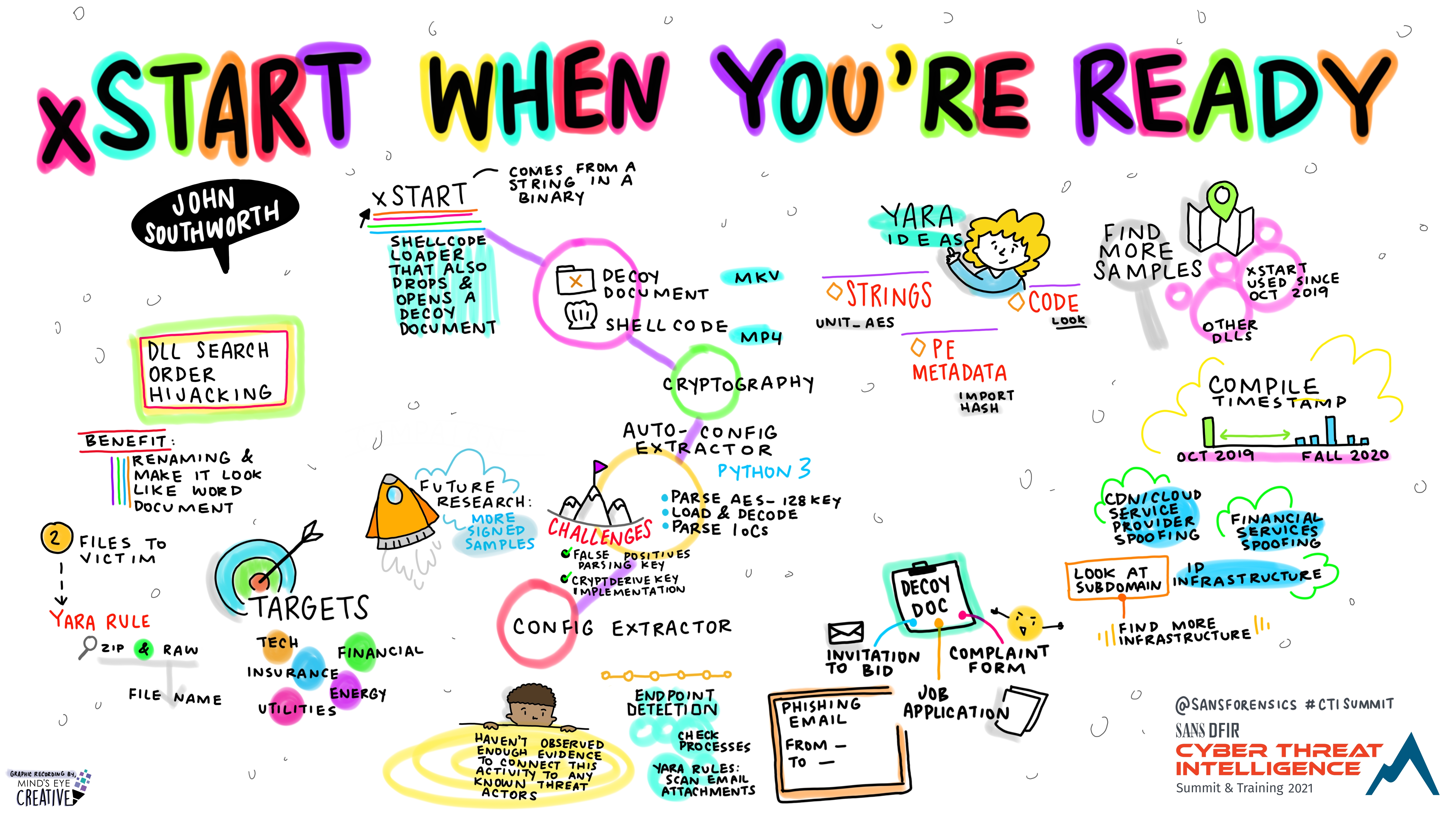
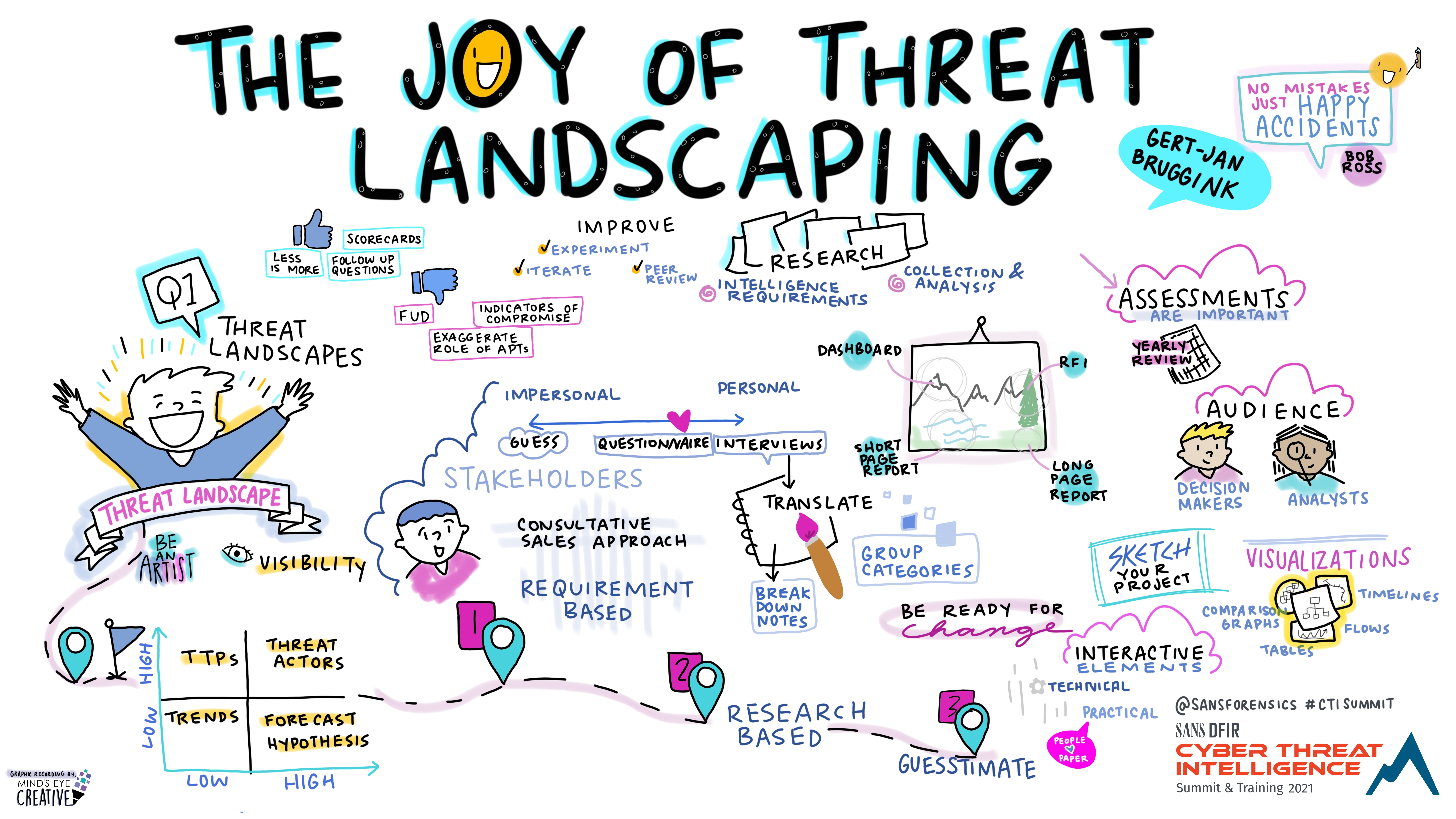
This year, we invited Ashton Rodenhiser of Mind's Eye Creative to create graphic recordings of our Summit presentations. If you missed a talk or are looking to view the CTI Summit through a visual lens, take a look a the recordings below.
In addition to graphic recordings, PDFs of Summit presentations are available on the SANS Summit Archives page (SANS account required) and videos will be posted to YouTube over the next several months.
*If you registered for the Summit, video recordings are available on your Summit Access page in your SANS Portal.
CTI Summit - Day 1
Riding the WAVE to Better Collaboration and Security
Kelsey Helms, Lead Cyber Threat Intelligence Analyst, Target Corporation Nate Icart, Lead Threat Intelligence Detection Engineer, Target Corporation
Asleep at the wheel? The effects of sleep on CTI professionals
Lincoln Kaffenberger, @LincolnKberger, Threat Intelligence Service Lead, Deloitte Global

xStart When You’re Ready
John Southworth @BitsOfBinary, Threat Intelligence Analyst, PwC UK
The Joy of Threat Landscaping
Gert-Jan Bruggink @gertjanbruggink, Co-founder, CTI analyst & defensive specialist, FalconForce
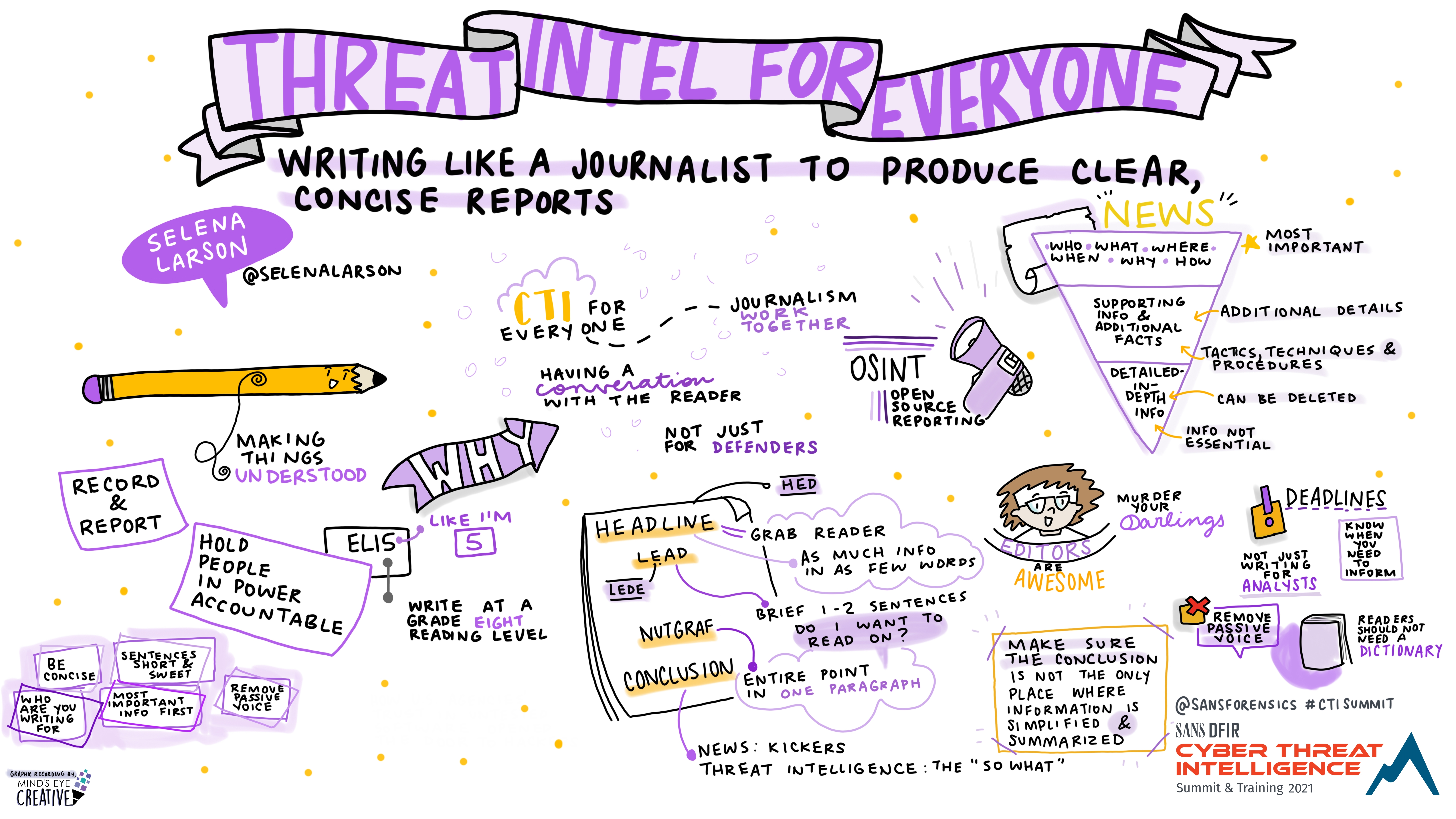
Threat Intel for Everyone: Writing Like A Journalist To Produce Clear, Concise Reports
Selena Larson @selenalarson, Cyber Threat Analyst, Dragos
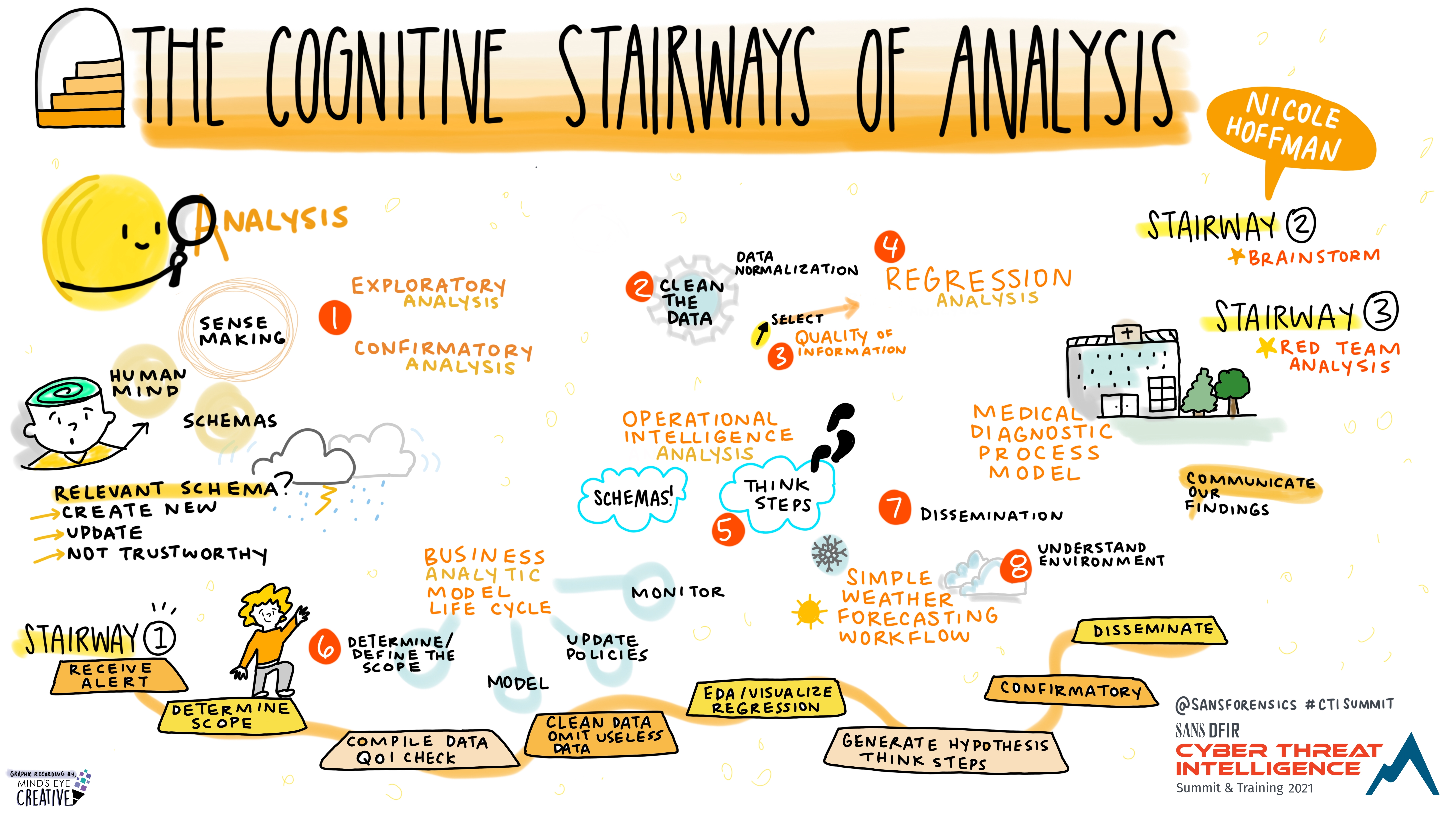
The Cognitive Stairways of Analysis
Nicole Hoffman @threathuntergrl, Intelligence Analyst, GroupSense
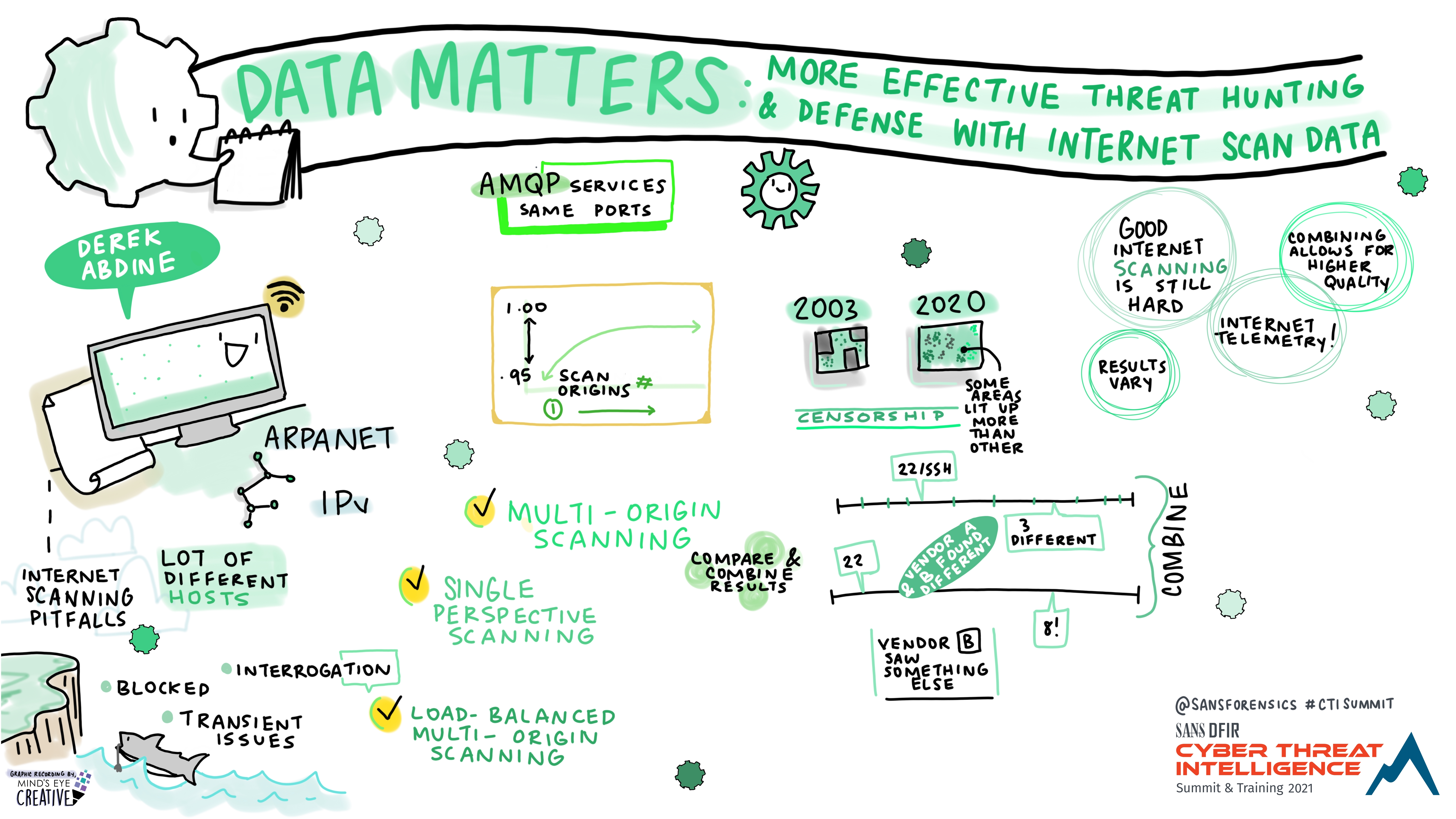
Data matters: More effective threat hunting and defense with internet scan data
Derek Abdine @dabdine, Chief Technology Officer, Censys
Full Cycle: Blending Intelligence Requirements and Custom Dissemination Tools to Drive Operation
Jon Jurado, Principle Associate, Cyber Threat Intelligence, Capital One
Robert McLean, Senior Manager, Cyber Threat Intelligence, Capital One

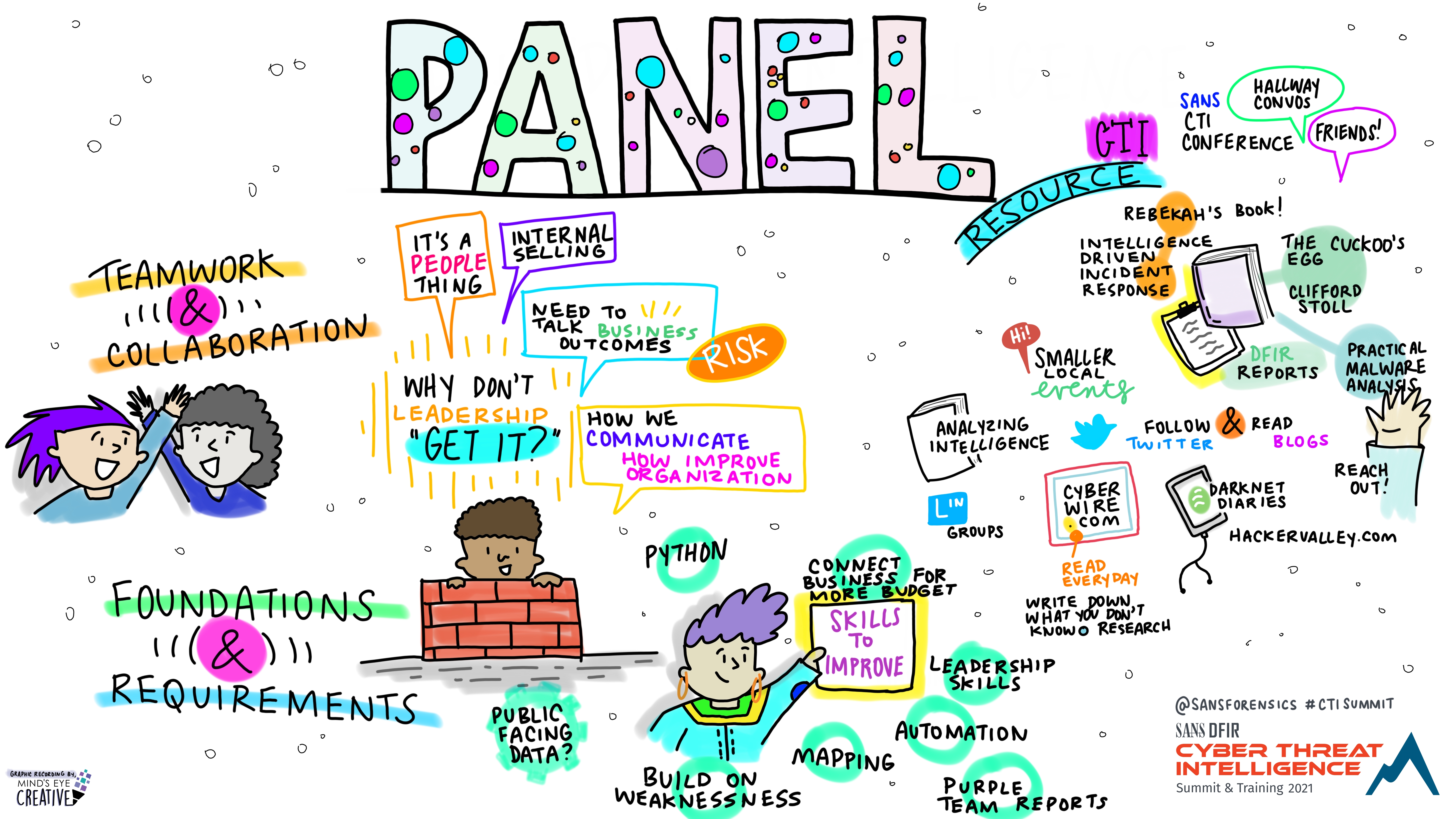
Day 1 Wrap-Up Panel
CTI Summit – Day 2
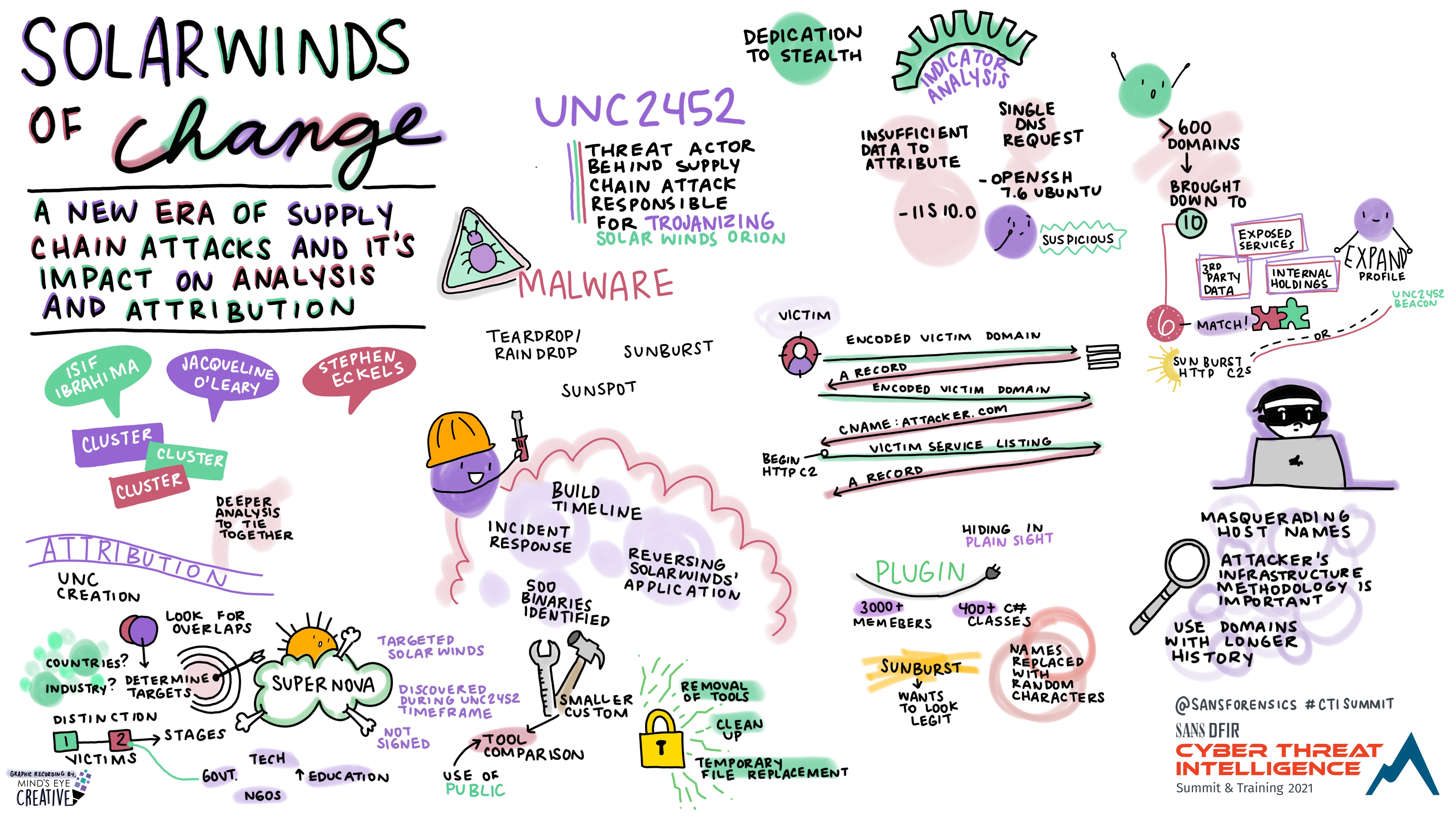
SolarWinds of Change: A New Era of Supply Chain Attacks and its Impact on Analysis and Attribution
Isif Ibrahima @isifmobile, FLARE-AP Principal Threat Analyst, Mandiant
Jacqueline O’Leary, Manager, Advanced Analysis, Mandiant
Stephen Eckels @stevemk14ebr, FLARE Reverse Engineer, Mandiant
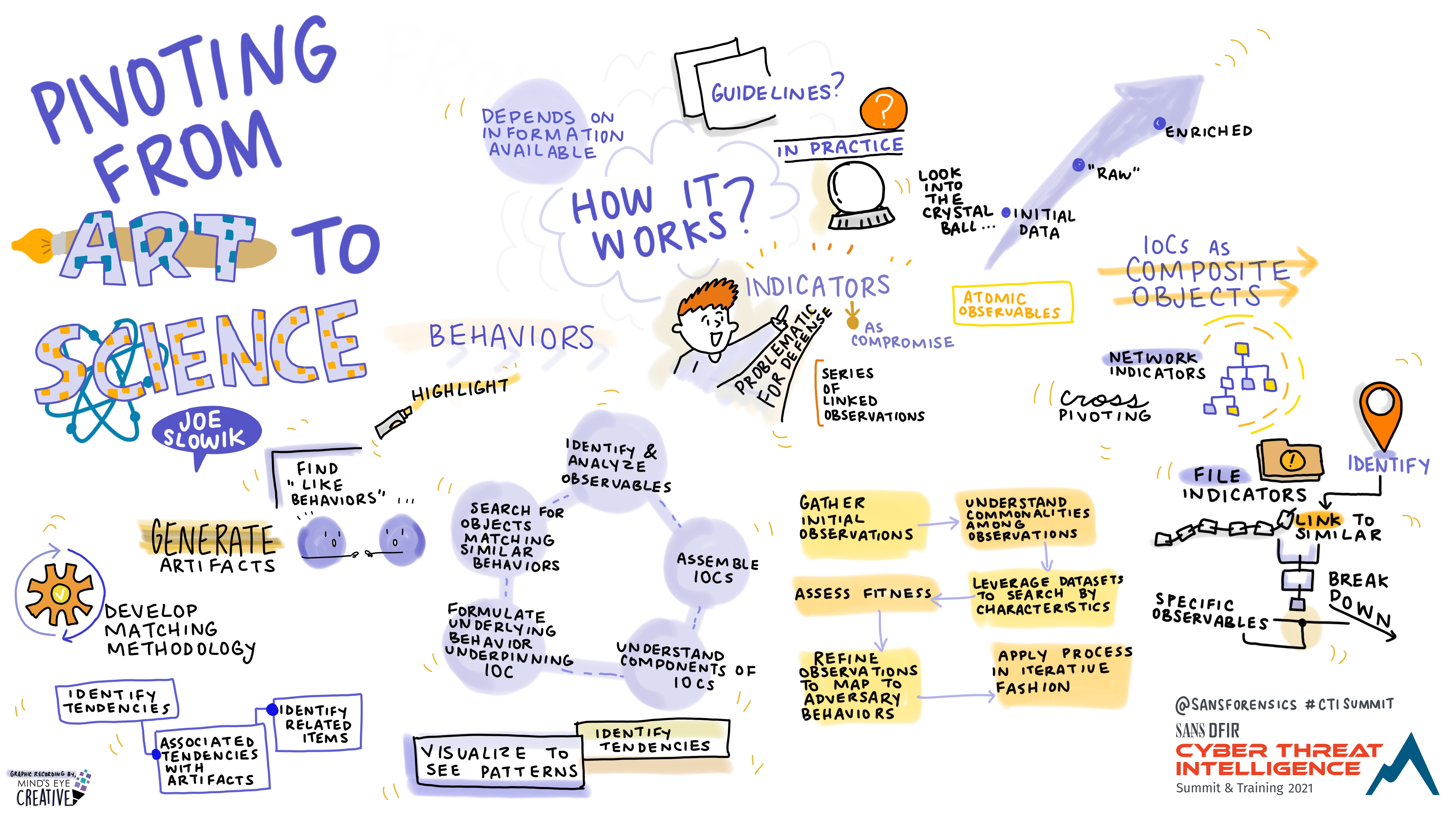
Pivoting from Art to Science
Joe Slowik @jfslowik, Senior Security Researcher, DomainTools
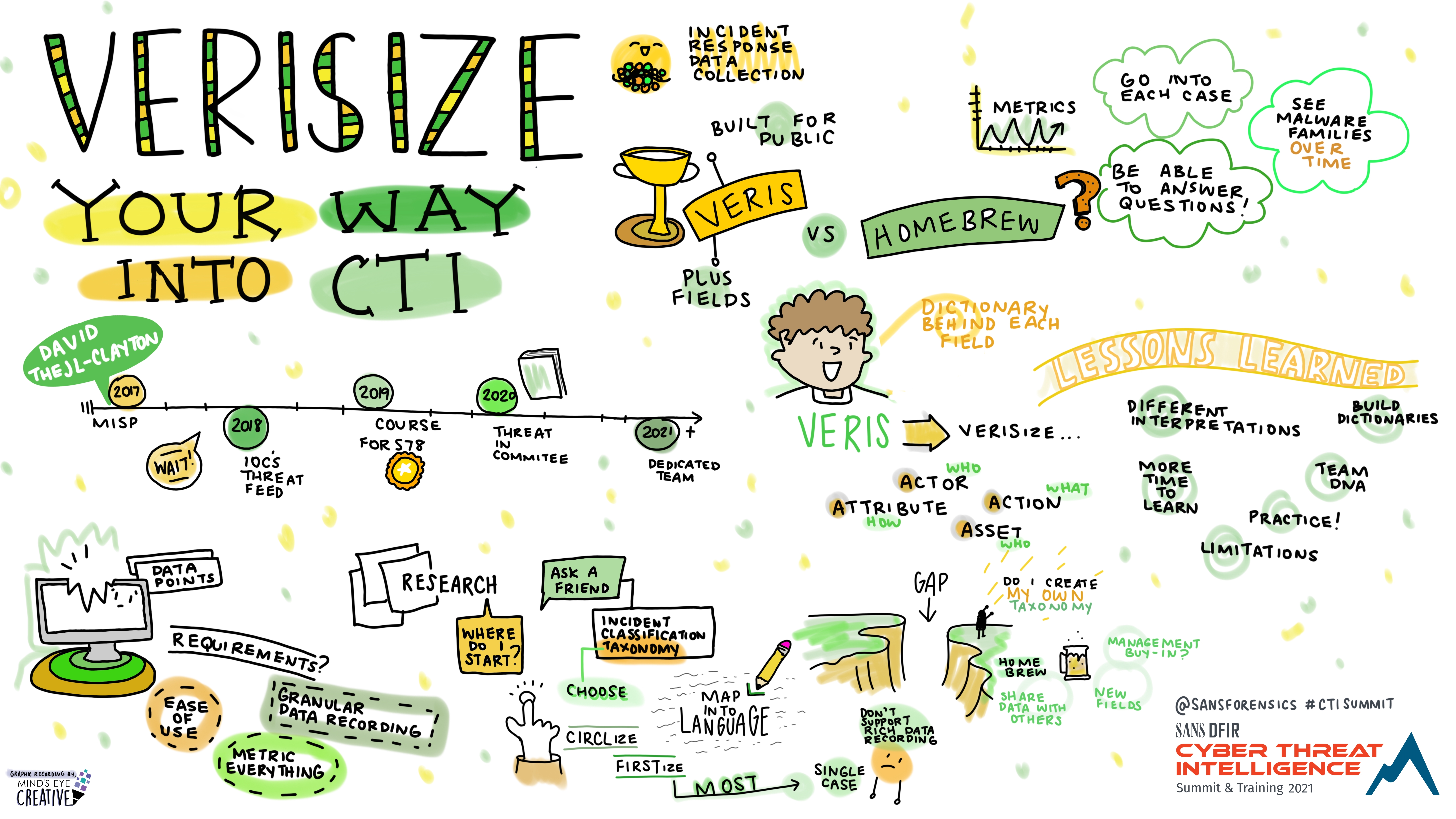
VERISIZE your way into CTI
David Thejl-Clayton, Cyber Defence Center Department Manager, JN Data
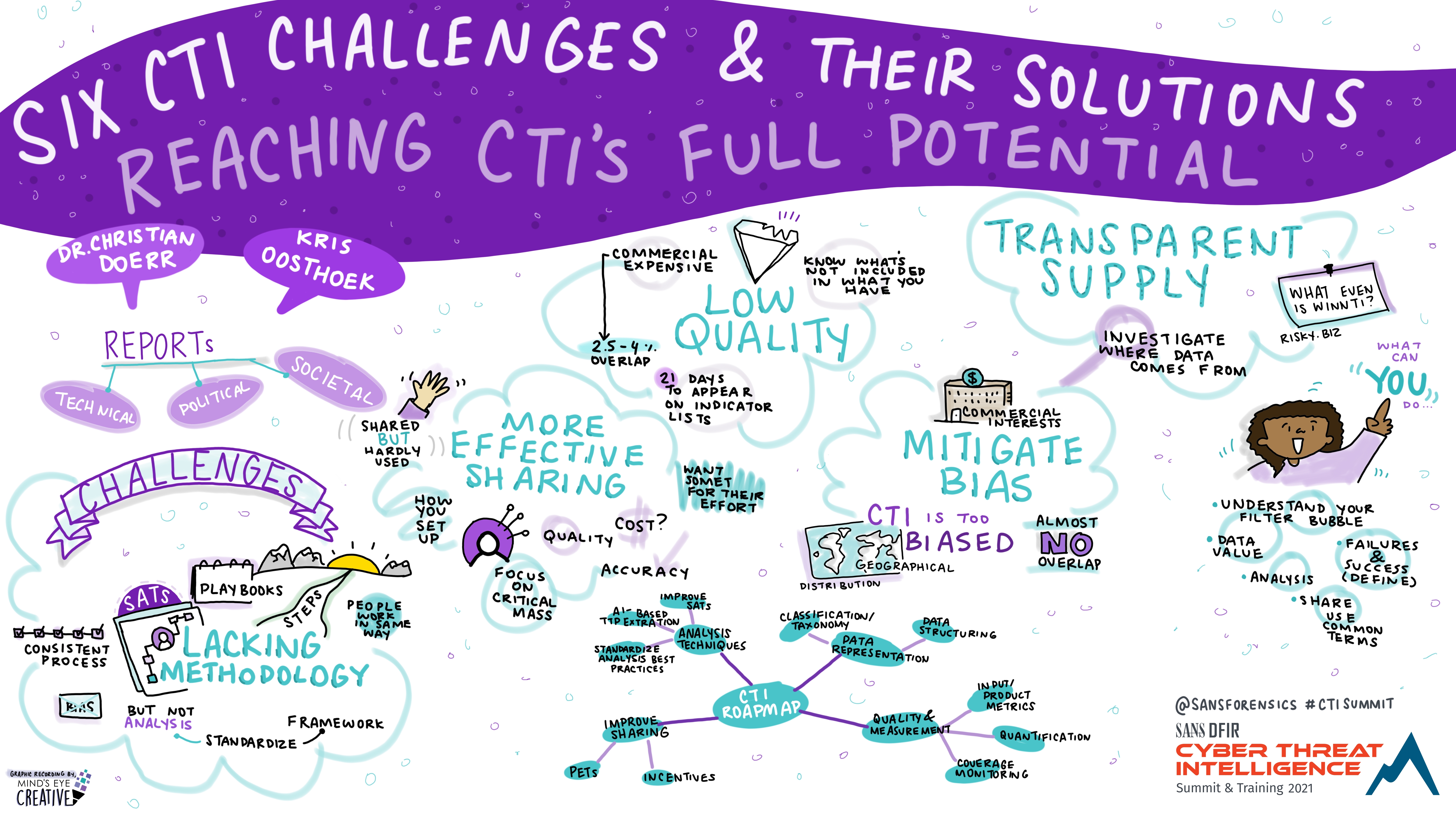
Six CTI Challenges and Their Solutions - Reaching CTI's Full Potential
Dr. Christian Doerr, Chair of Cyber Security and Enterprise Security, Hasso Plattner Institute
Kris Oosthoek @f00th0ld, Senior CTI Analyst, Rijkswaterstaat (Dutch Public Works / Critical Infrastructure Agency)
Still thinking about your Ex(cel)? Here are some TIPs
Andreas Sfakianakis @asfakian, Cyber Threat Intelligence Analyst
_-_Here_are_Some_TIPs_Andreas_Sfakianakis_-_Graphic_Recording.jpg)
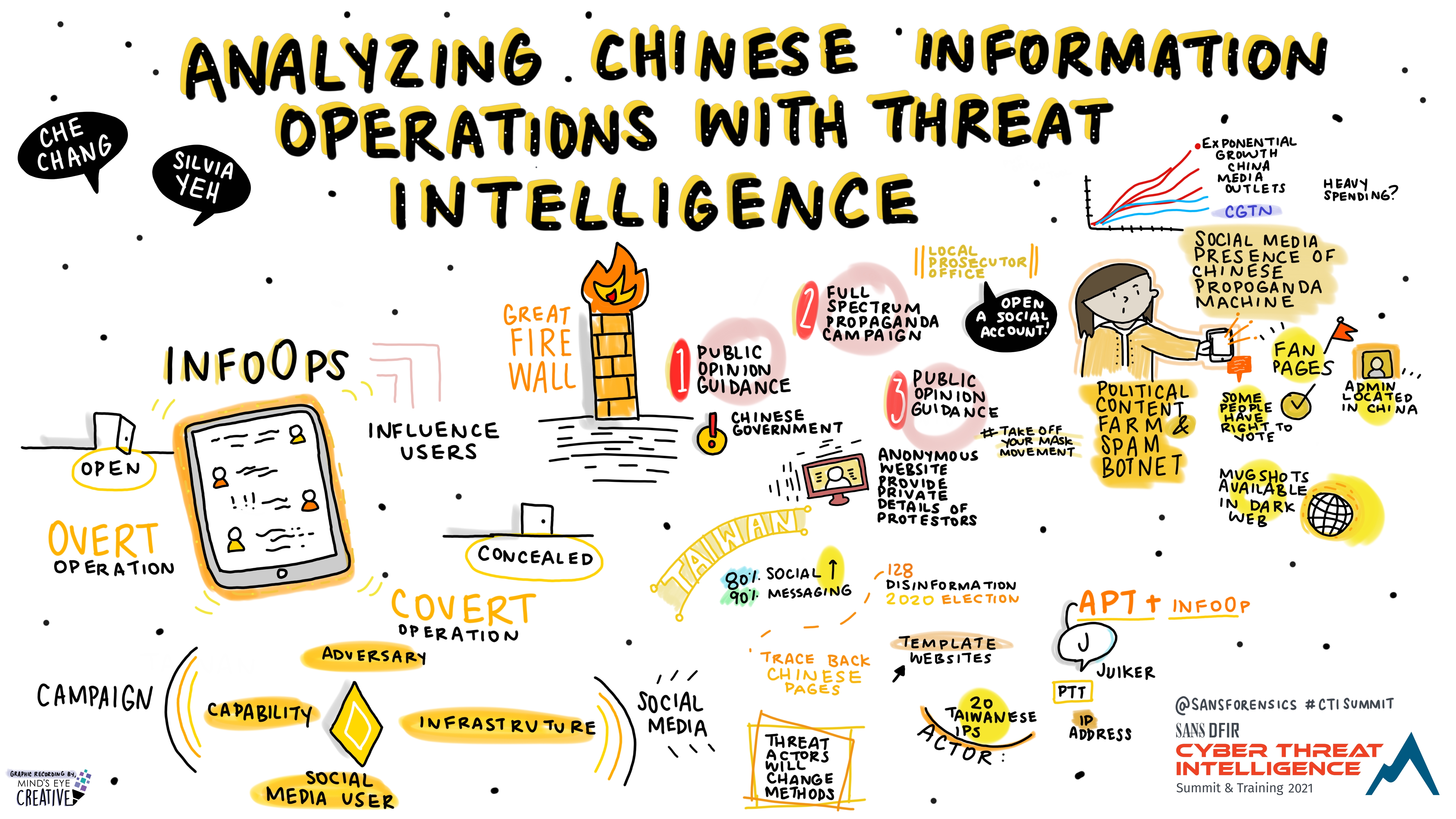
Analyzing Chinese Information Operations with Threat Intelligence
Che Chang, Cyber Threat Analyst, TeamT5
Silvia Yeh @silvia_yeh, Cyber Threat Analyst, TeamT5
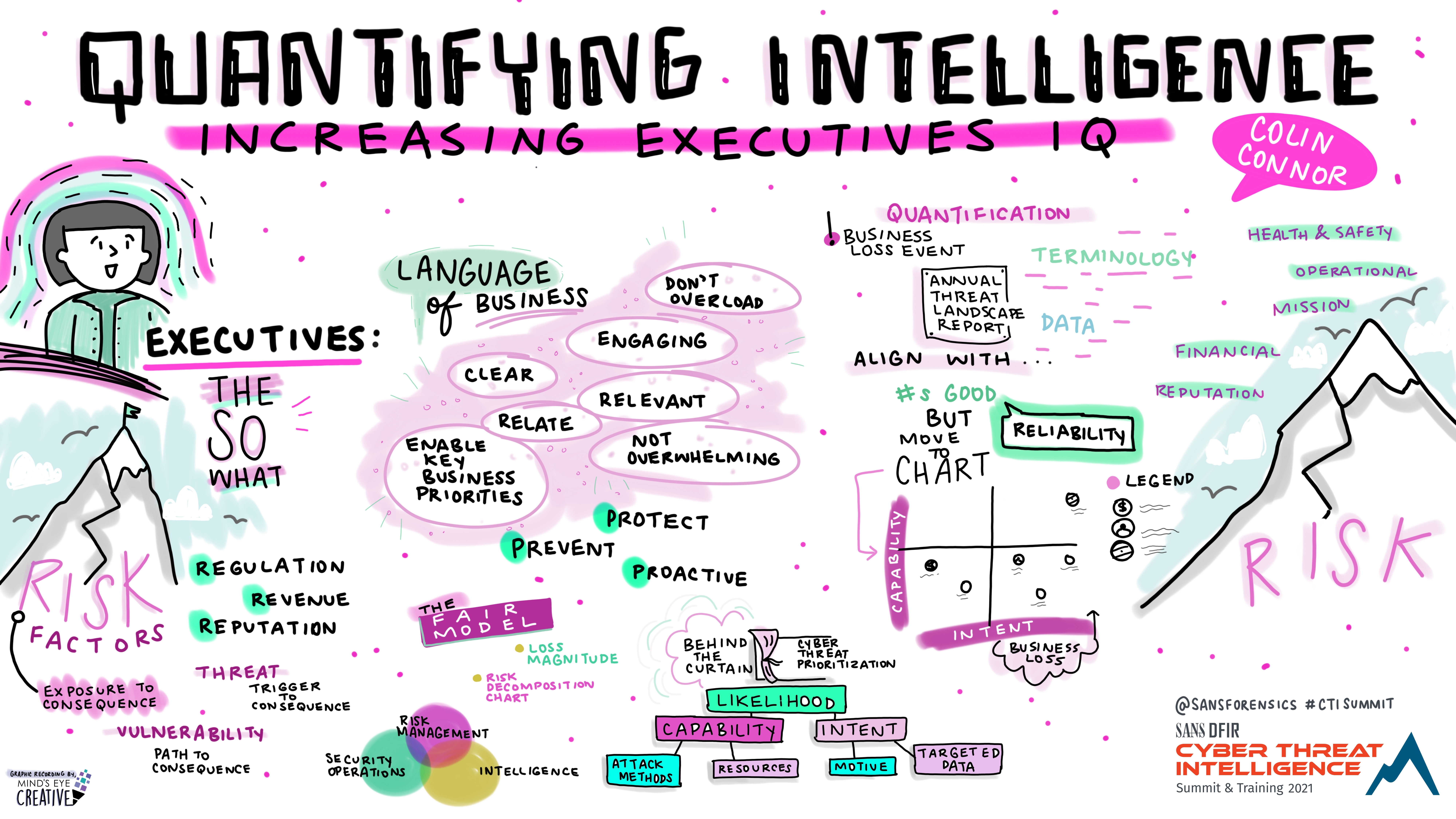
Quantifying Intelligence: Increasing Executives IQ
Colin Connor, Global Threat Intelligence Analyst, IBM
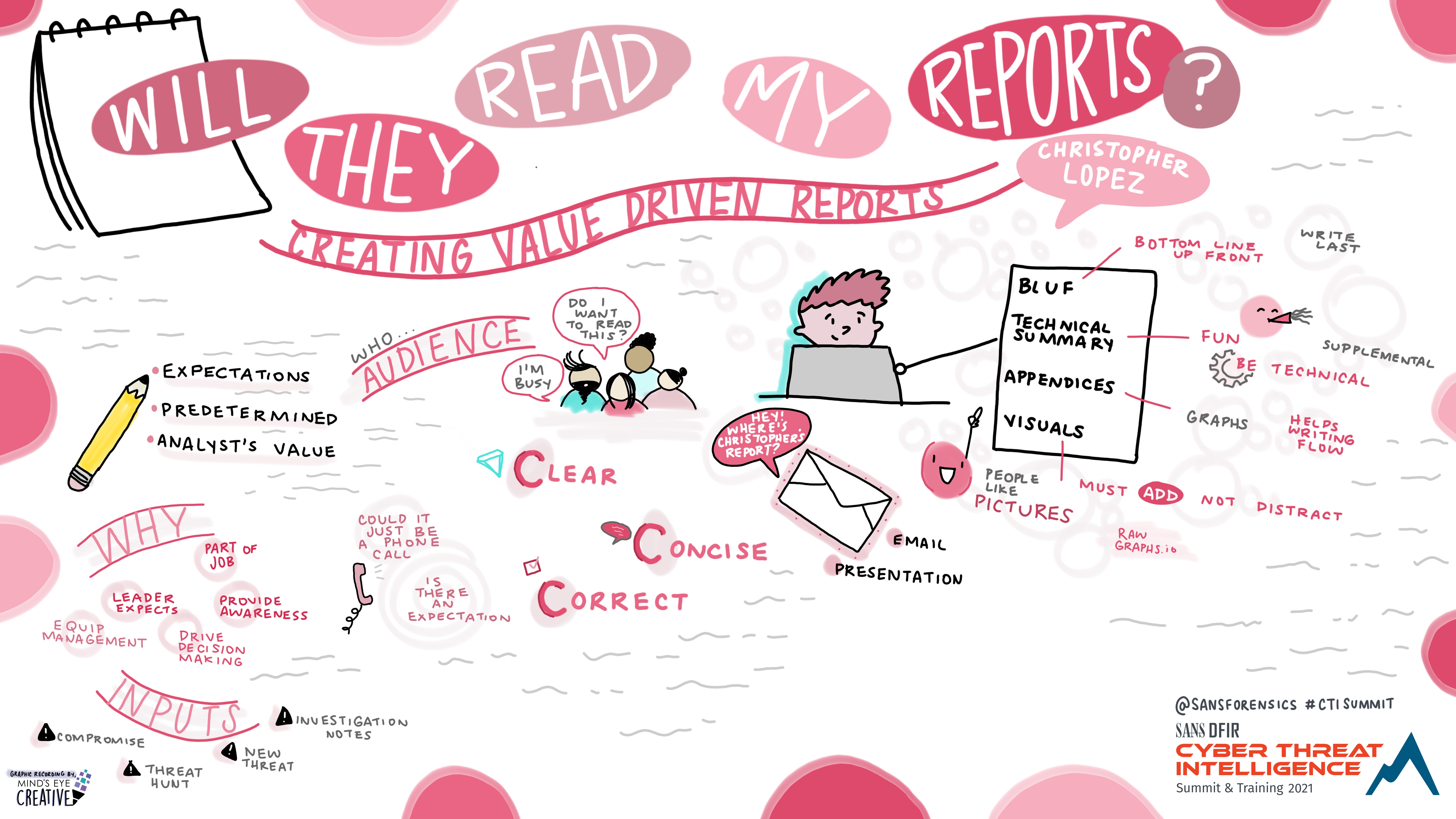
Will they Read my Reports? - Creating Value Driven Reports
Christopher Lopez @l0psec, Tanium
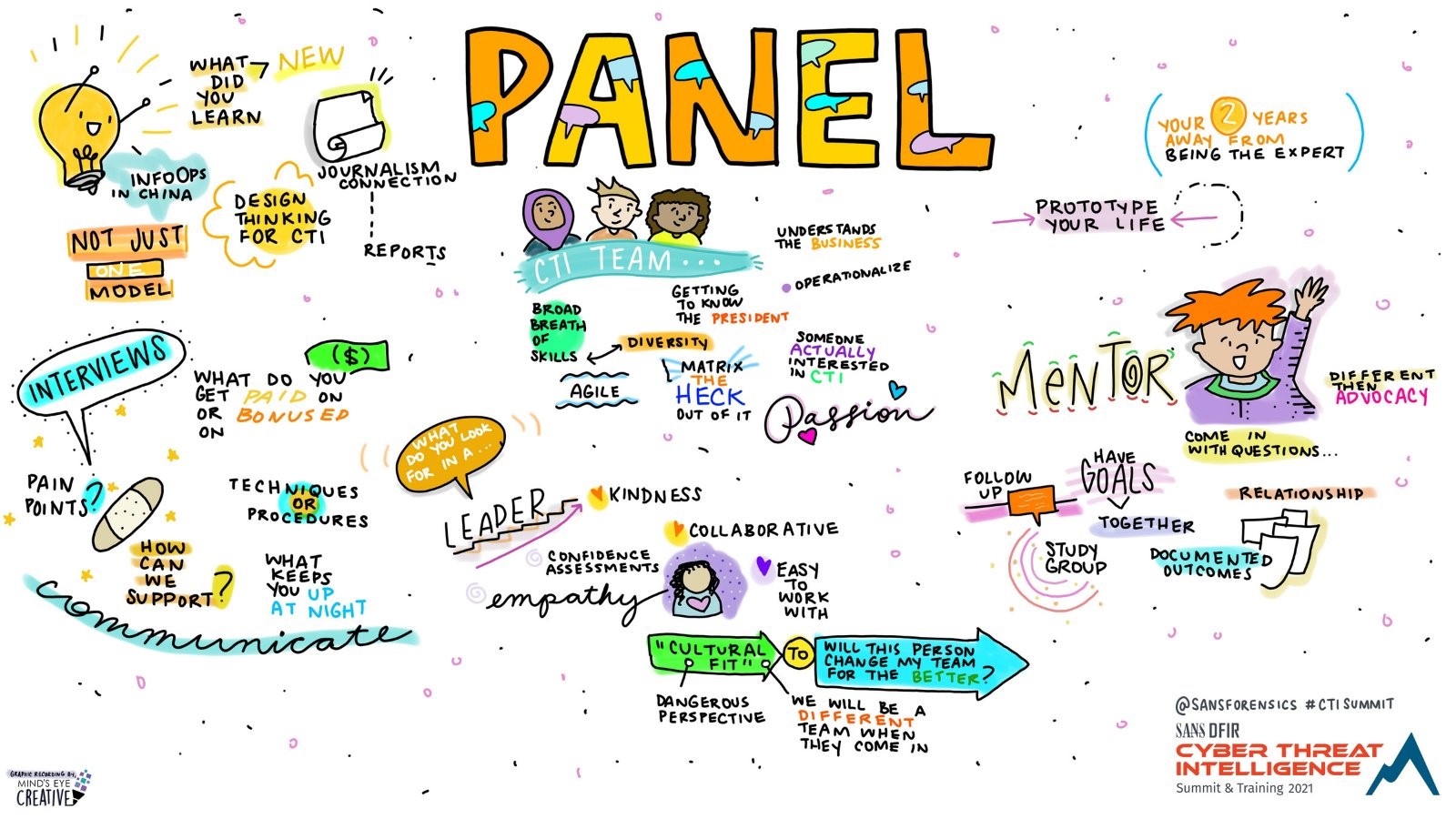
Day 2 Wrap-Up Panel

.png)