Introduction
As industrial control system (ICS) security managers, we know cyber attackers have skills well beyond traditional information technology (IT) intrusions and data exfiltration techniques. They have long since set their sights on operating technology (OT) environments and demonstrated an understanding of ICS and the skills to develop ICS-capable attack tools to gain access and cause negative effects.
Cybersecurity attacks often focus on internal system damage, where the consequences for ICS are greater and potentially external in nature as well, because attacks can affect the safety of people and the environment, depending on the type of facility. ICS intrusions can change physical changes with potentially catastrophic consequences – consider for example a compromised Safety Instrumented System (SIS) that fails to monitor and safely shutdown a gas pipeline in an over-pressurized condition.
Consequences of modern ICS cyber-attacks on an even grander scale can include:
- Large power grid blackouts in large cities and entire regions
- Failure of critical manufacturing equipment
- Massive business financial losses
- Paralysis of smart city emergency infrastructure in large municipalities
- Injury of plant workers
- Serious environmental damage
ICS intrusions will continue to occur and likely increase in their severity and range of consequences across critical infrastructure sectors. However, managing control system cyber risk and tactical ICS/OT defense is do-able, and it can protect critical resources and focus on recovery that improves resilience and reduces mean recovery time.
Proactive ICS Cyber Defense and Incident Recovery
Whether you are a new, experienced or “step-up, step-over, or in-place ICS security manager”– the title of a blog on the SANS ICS418: Security Essentials for Managers course – you will do well to focus on ICS-specific defenses to prevent adversaries from getting into an industrial network in the first place. In parallel however, to protect critical infrastructure before an attack does occur, you’ll need to work with engineering teams to refine the recovery processes to improve resilience going forward.
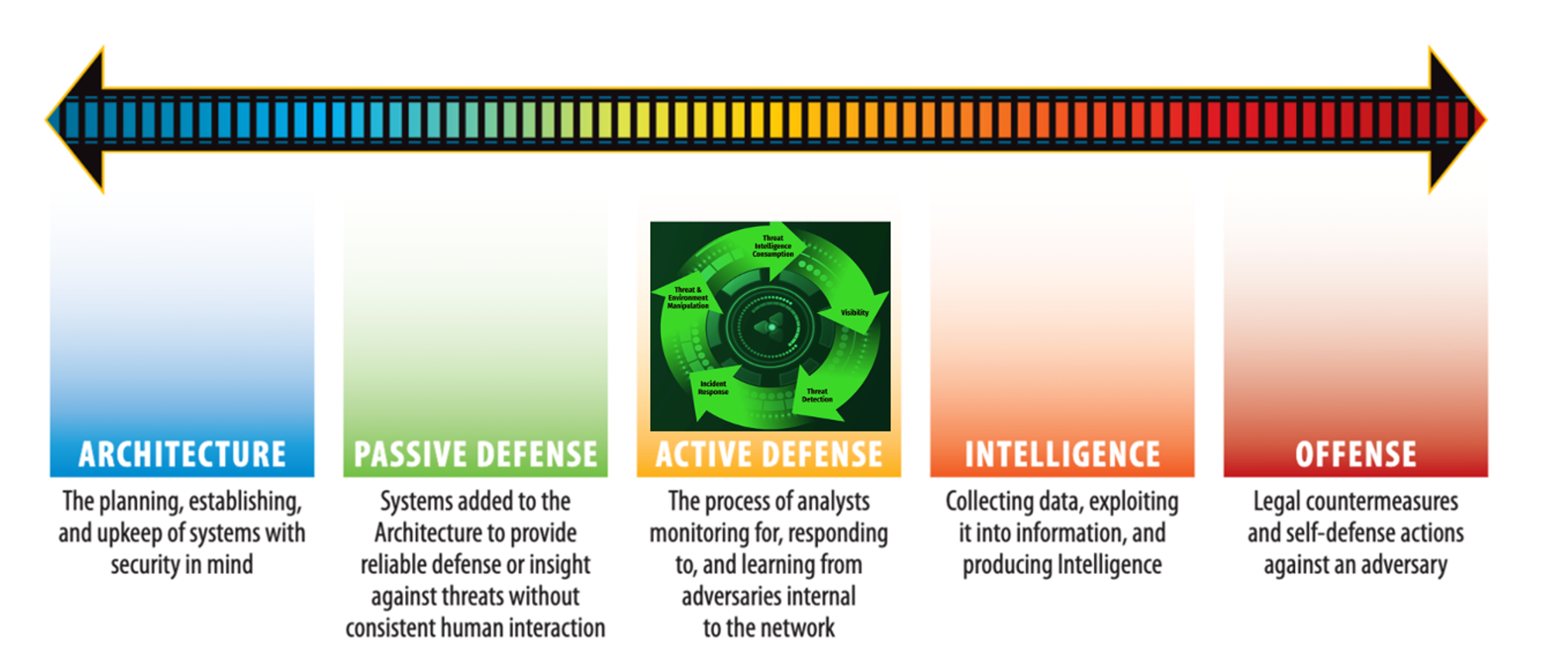
As ICS security managers, we need to support our teams and lead them to success. This first means positioning our team members and technologies in an Active Defense position within the Sliding Scale of Cyber Security. Active cyber defense is the process of trained ICS analysts leveraging technology to monitor, respond to, and learn from threats internal to the control network. Active Defense is most effective built on top of ICS network architecture, followed by passive defenses and a documented asset inventory.
The Right Asset Inventory Information to Aid Rapid Recovery
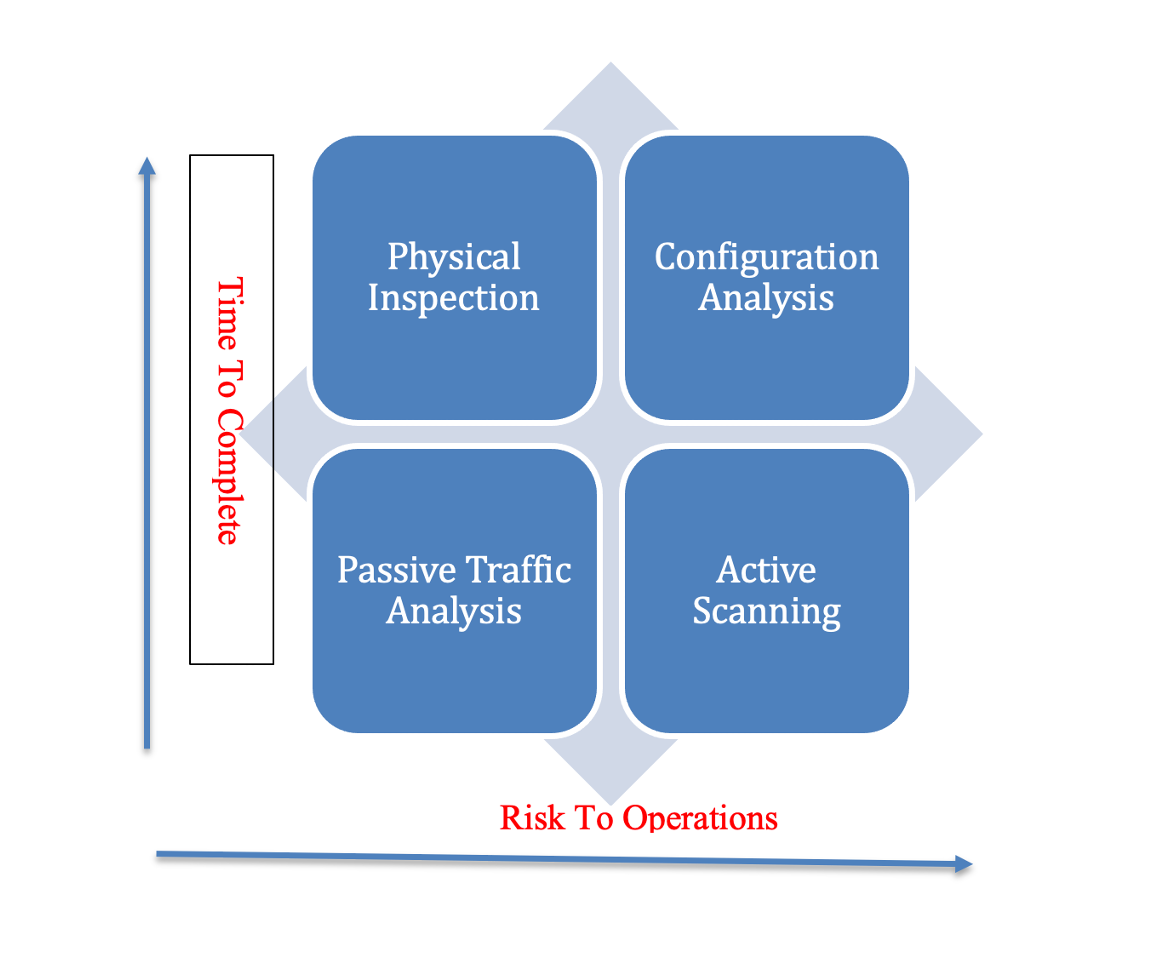
ICS asset identification can be broken down into four methods to be completed individually or combined for improved accuracy by your team: Physical Inspection, Passive Traffic Analysis, Active Scanning, and Configuration Analysis. Each method has different risks and times required to be completed, as shown below.
Practical steps your team can take to establish an ICS asset inventory are to combine physical inspection, configuration analysis, and passive network traffic capture as follows, for example:
- Start by reviewing any already-created network diagrams and engineering documentation like “as-built documents” to capture the assets said to be in production.
- Use an encrypted laptop with at least a basic spreadsheet application to start cataloging and storing ICS asset information during a physical site walk-through. Don’t forget your safety training certificate and personal protective equipment to enter the site.
- Augment physical inspection with passive network packet captures on critical network segments that host critical ICS assets (PLCs, Data Historians, Human Machine Interfaces, Engineering Workstations) by using either a SPAN configuration off of a fully managed switch or a hardware network TAP.
- Ensure that field device configurations are securely recorded, stored, and available for comparison during an incident so that engineering staff can recover/reload the current uncontaminated project files and device settings during restoration efforts.
At a minimum, your team should capture the attributes below from the commonly targeted critical assets such as PLCs, Data Historians, Human Machine Interfaces, Engineering Workstations, core network devices, and active SIS being used. This can be used to understand the risk surface based on vulnerability disclosures and help to map protections on adversary’s tradecraft obtained from through intelligence sources.
Sample Asset Inventory Elements |
Site location |
Facility type |
Asset type and ID tag |
Asset location room, cabinet, rack |
Description of asset function |
Impact to operations if assets unavailable |
IP and MAC address |
Operating ICS protocols used |
Model/manufacturer, serial number |
Firmware version for controllers and related modules, chassis information |
Applications installed on critical assets with versions |
Assets deemed critical – Data Historians, HMIs, primary controllers, control system network switches |
Project file configuration on PLCs – last change date, etc.; store configurations securely. |
Dependencies – systems or other assets, etc. |
Change and Trusted Restore Points
For adversaries to have an impact they must change something. Can the engineering teams trust the production controller logic and other critical asset configurations?
Considering the consequences of these imminent intrusions, ICS security managers need to ensure ICS incident response recovery plans include technology solutions and trained personnel to aid engineering in rapid recovery to trusted restore points. With visibility into configuration changes, incident responders on our teams can quickly determine whether controllers or field devices have been manipulated, and specifically what may have changed during an attack. This illustrates the scope of our incident impact: identifying exactly which assets are compromised and in need of restoration.
Reliable change and version control should include controller project files and configuration of remote terminal units (RTUs) or other intelligent electronic devices – to have a “known good” state of operations for critical engineering assets.
ICS Incident Recovery Considerations
Our established asset inventory will have identified critical control assets (including but not limited to PLCs, Data Historians, Human Machine Interfaces, Engineering Workstations) as candidates for digital data acquisition and forensics analysis during ICS incident response. During an incident, malware code analysis is too time-consuming, and attention must be focused on rapid triage. The objective is to identify the scope of an intrusion, determine system changes, and identify only the systems in need of restoration as ICS security and engineering teams work together to fight through the attack. That would include our teams scoping for malicious activity in memory captures from those critical assets, using automated tools to streamline their efforts that have been tested to ensure safe operations in the ICS.
Undertaking all of these steps provides more accurate reporting to upper management when incidents do occur about incident scope and restoration times directed towards reducing recovery time. Prior to incidents, we as ICS security managers need to have answers for these questions to give leadership confidence in meeting the Recovery Time Objective (RTO) for the ICS.
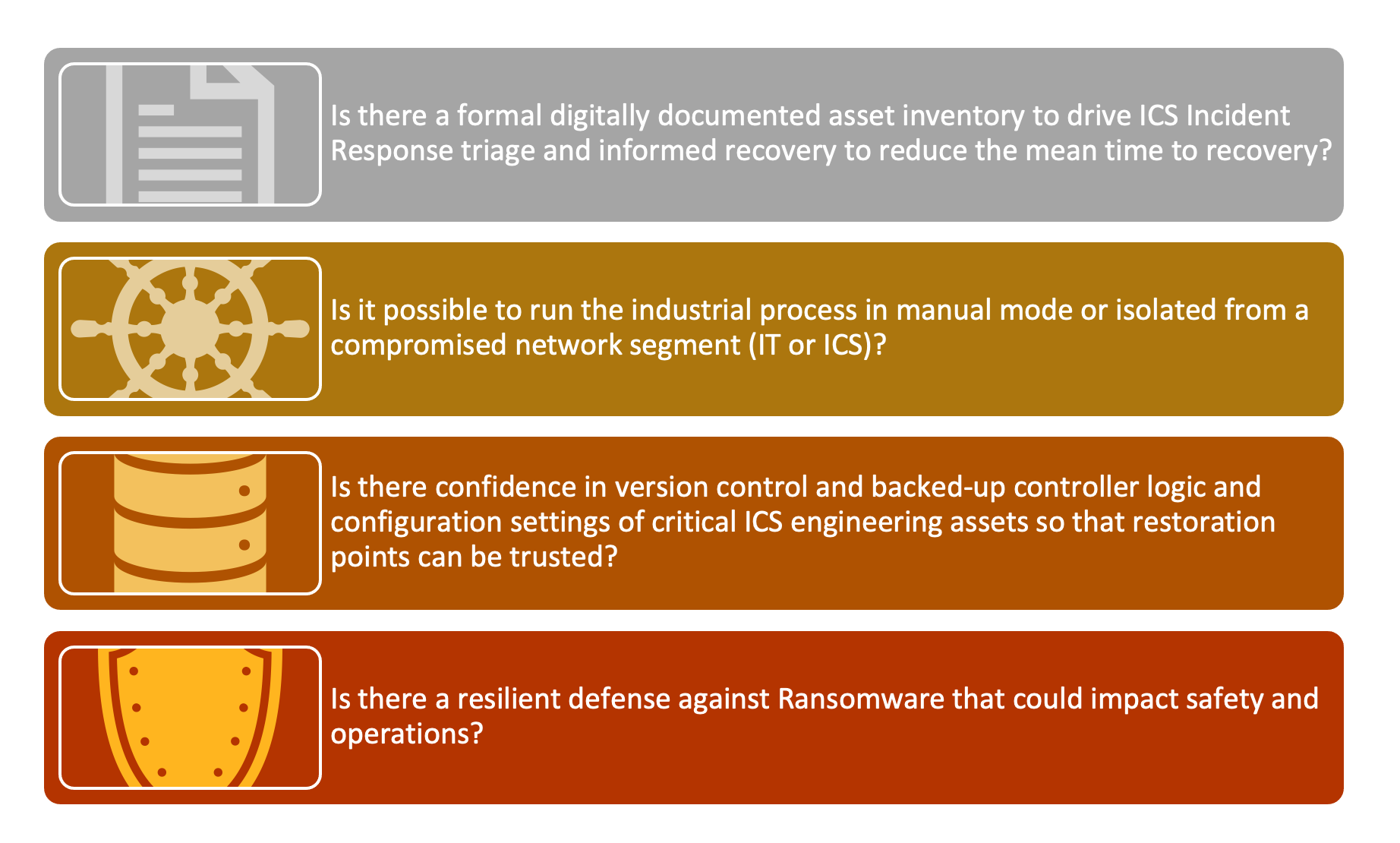
ICS managers can regularly run incident response tabletops, which have a high return on investment. The tabletops, which can focus both on threat detection and recovery, help get answers to questions about the efforts being made to reduce the overall consequence of an incident. Moreover, they help our security teams learn about the engineering process in depth, building relationships between engineering teams working together during ICS cyber incidents. ICS security managers can start a consequence-driven tabletop with guidance outlined in the blog entitled Top 5 ICS Incident Response Tabletops and How to Run Them.
In Conclusion
Adversaries continue to evolve their attack tradecraft, increasingly targeting control networks and critical infrastructure with improved knowledge of how to abuse ICS systems and exploit control system vulnerabilities. In their wake they leave serious financial, brand, operational impacts, with potential catastrophic consequences for organizations, the environment, and people’s safety.
ICS security mangers looking to improve the resilience of their ICS security program can begin by undertaking an official asset inventory with the methodologies described above, and then leveraging and maturing to an active defense position. The objective is to ensure that security controls are in place specifically for industrial control systems, with network and OT and engineering devices visible inside the ICS, in order to be ready for rapid ICS incident triage and the recovery to trusted restore points. The following takeaways can serve as a guide:
- Combine asset inventory knowledge with ICS active defense to monitor for traffic anomalies that may lead early-stage threat detection to reduce the need for down time and related recovery efforts.
- Deploy an active cyber defense position for ICS using proactive ICS defense focused on network and endpoint visibility inside the control system network starting with PLCs, Data Historians, Human Machine Interfaces, Engineering Workstations, core network devices, and active SIS.
- Leverage consequence-driven incident response tabletops focused on recovery to spot opportunities for improvement while leveraging configuration change control to detect changes during an incident.
- Leverage threat intelligence to drive searches across an established asset inventory database to prioritize proactive defense changes around ICS assets that have identified publicly available exploit kits for impactful vulnerabilities likely to be exploited.
- Ensure that managers retain and train cybersecurity defenders who are knowledgeable in both IT and specific ICS/OT cybersecurity incident response and who also have high-level technical engineering knowledge.
Join Dean when he teaches:
Review Dean's ICS Community Contributions and Bio
www.sans.org/profiles/dean-parsons/
Join the SANS ICS Community Forum
Tips, tricks and Q&A to secure your ICS. Join here.