In my time at SANS I have had the opportunity to work with an amazing group of ICS professionals, and helped to create some industry leading ICS courses as well as certifications. While we are always hard at work in helping our customers we are equally as focused on leveraging the opportunity that SANS provides to give back to the community. While these community efforts take many shapes, I will mention two resources here: ICS Posters, and the SANS ICS Community Forum. Both Free to you!
The ICS team works to create an industry poster every year and we always try to develop a theme that will help the community think about a problem in a new and helpful way or we work to develop graphic concepts and models designed to communicate a topic with stakeholders. During the development of our fourth ICS poster release we reached out to another SANS community resource — the ICS Forum. Within the forum we released the initial draft concepts of the poster, requested feedback from the thousands of ICS member professionals who actively participate in the forum and then worked the feedback into the final product. I believe this convergence of ICS community resources will begin to grow more and more integrated over time, eventually getting to a point where subject matter experts within the forum can begin directly working within the community to develop resources needed and supported by the community?. A self-help group for ICS :-) = awesome! (Think 12 step programs - "Hi my name is John and I believed in air gaps ..... hi John")
The theme of the fourth ICS poster is "Perspectives of a Cyber Attack" the two sided poster has one side focused on the perspectives of a defender responsible for a system and the other side considers the view of a target environment from the adversary perspective.
Decisions Must Be Made
Starting with the defender perspective we considered how much influence a defender has in shaping the landscape and determining what their next cyber-attack will look like.
System defenders will determine the overall design, architecture, engineering, infrastructure components, solution selection, implementation, and overall management of the environment. We considered the various elements that organizations must shape and manage to achieve their objectives.
A graphical concept of a 6 sided cube that represents the available components for an organization to work with was developed for the poster.
- Infrastructure
- System Vendor
- Applications
- System Management
- Network Architecture
- Organization Elements
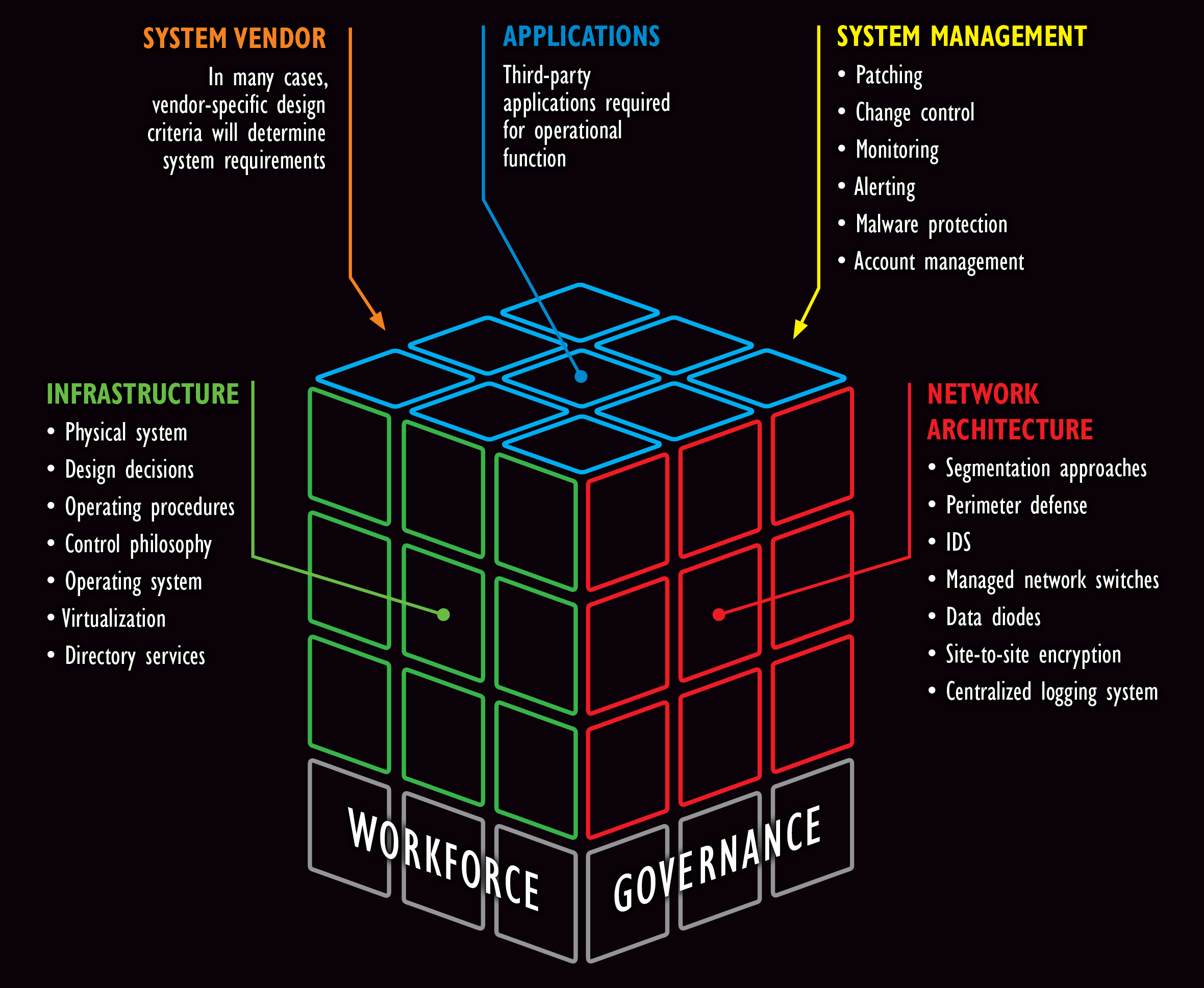
Engineer Your Environment
As organization specific decisions are made, there will be a resulting company specific environment that an adversary will encounter. This environment will determine what an adversary needs to do to engage the target and how they will achieve their goals.
This ultimate battle ground is based on the specific technical / leadership decisions made, operations requirements, budgetary drivers, risk management thresholds, overall organization capabilities and maturity.
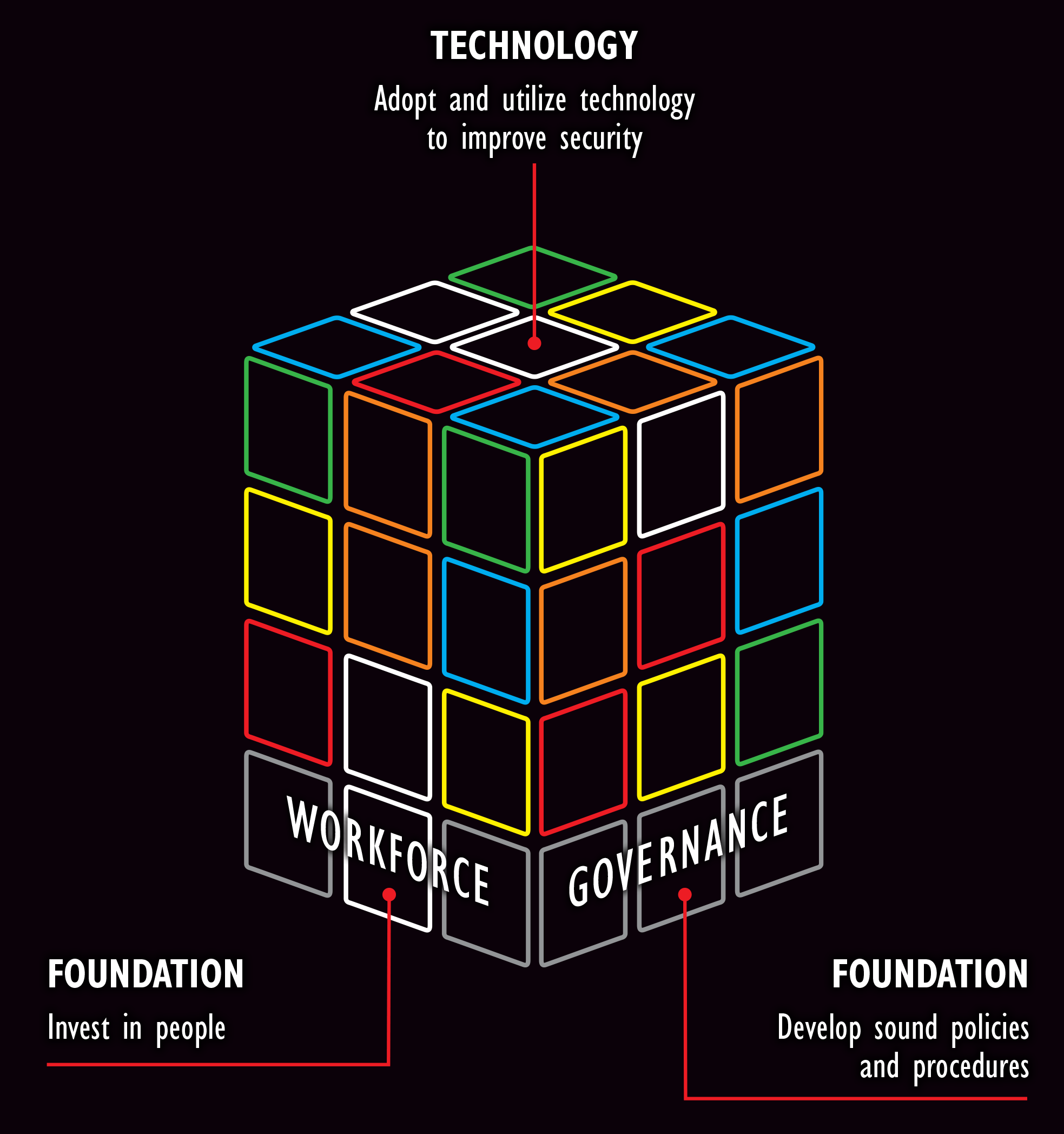
This resulting mix of implemented elements will be a representation of the People, Process, and Technology environment that needs to be defended.
As companies face adaptive adversary groups, it may help to consider how adaptive will your defense approaches be.
How quickly can you re-arrange your cube in a way that disrupts the adversary, but does not disrupt your operations? This unique environment is what an adversary group will encounter when your organization is targeted, and considering how challenging that battleground will be for an adversary to achieve their goals will depend on the goals of the adversary and the cyber maturity of the defenders.
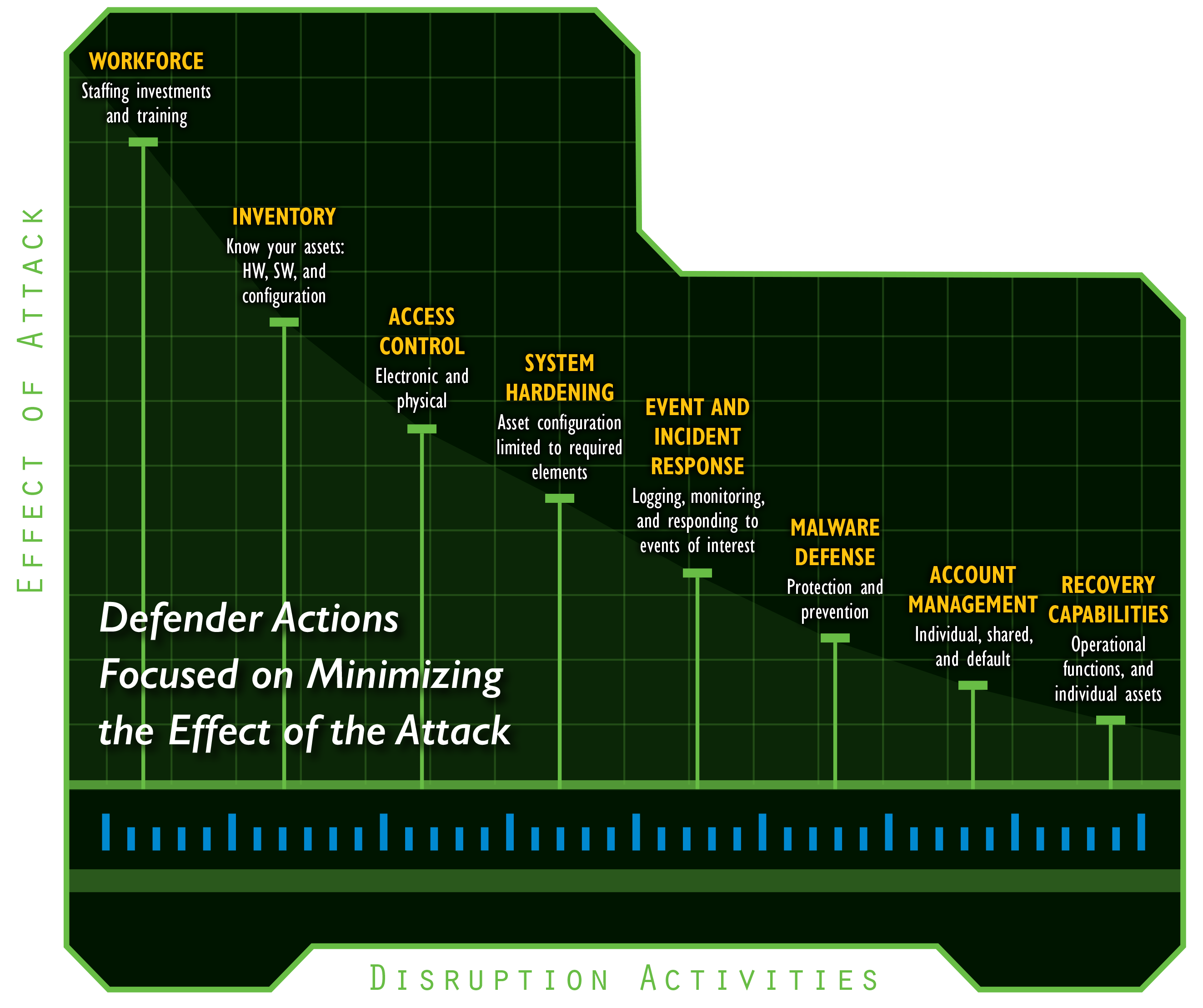
Which Levers Should You Pull
We developed two additional graphics that pertain to the defender perspective and are meant to visualize the cyber maturity of an environment and the defenders ability to disrupt an adversary's desired effect. As we considered the actions a defender could take, we thought about the most significant actions that would have the greatest effect on disrupting an adversary's ability to achieve an operational impact. Workforce capabilities stood out as having the most significant potential effect on an adversary actions and the easiest to adapt to a dynamic targeted attack campaign. The remaining actions that were considered for operational environments were prioritized based on how significant they were in enabling a defender's ability to reduce the effect of an adversary's attack. This first visual is shown below.
If We Look, We Might Find Something
The second visual we developed in the cyber maturity section of the poster, is a consideration of how an attack would be detected, and the types of adversary tools and behaviors to anticipate as adversaries encounter target environments of varied cyber maturity levels. We considered the Initial, Defined, and Optimized levels of the CMMI model and aligned those three different cyber maturity levels with what an attack would possibly look like for an organization functioning at one of those levels.

Attacker Motivational Speaker
With these graphics and defender perspectives provided, we moved on to considering the perspective of an adversary group. As we began considering the perspectives and goals of an adversary team, I kept hearing the voice of Robert M. Lee saying "Remember, adversaries have managers and PowerPoint too." This struck me from the perspective of, what if I was their manager and had to create leadership presentations for my team with the goal of successfully targeting an ICS organization. For the poster we developed the following graphic to consider what highly effective adversary team behaviors would look like.
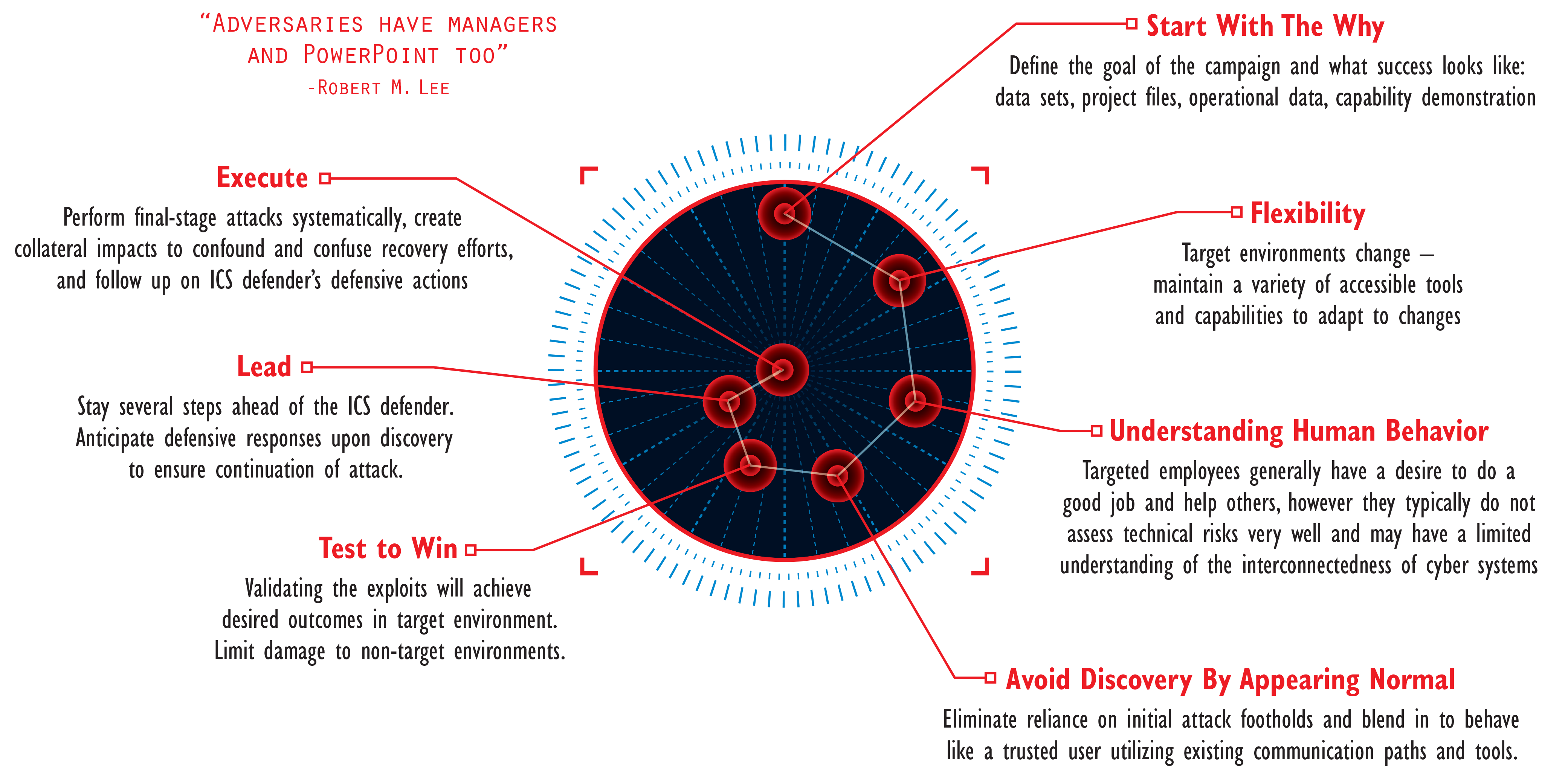
Mike Assante has created an excellent ICS community forum post that discusses the trends and concerns around adversary team actions and specifically the "defining attributes" that we worked to capture in the graphic. An excerpt from Mike's forum post that I believe is relevant to this graphic: "Many people have used the term Advanced Persistent Threat (APT) to label these actors, but that term best describes espionage-oriented actors (they want to stay in your system and siphon valuable data). We are seeing another type of actor that would like to achieve enough persistence to achieve their goals and is planning all along to reveal themselves, in some cases in a very noisy manner. The attributes of these folks can be boiled down to this basic list:
- Goal oriented
- Resourced, structured, with access to multiple skills
- Conduct planning and target reconnaissance/information gathering
- Exercise patience
These types of cyber adversaries have the resources to focus on defeating (or honestly simply bypassing) security controls and signature-based solutions."
Building Bridges
With an understanding of adversary goals and operating behaviors, we wanted to develop a graphic that visualized an adversary activity that is discussed frequently, but rarely with any explanation. We started with the common discussion that many in the ICS industry find themselves in: sitting in a room and talking about organization structure, technology budgets, workforce capability and eventually all roads lead to - the convergence of IT and OT from a technology perspective, as well as engaging in discussions about the existing divide between IT and OT from a cultural perspective. Typically, these conversations will focus on the lack of communication or coordination between these two parts of the organization, and usually moves to discussions on focused efforts to try and build bridges between the two cultures to leverage the benefits of both teams for the good of the mission.
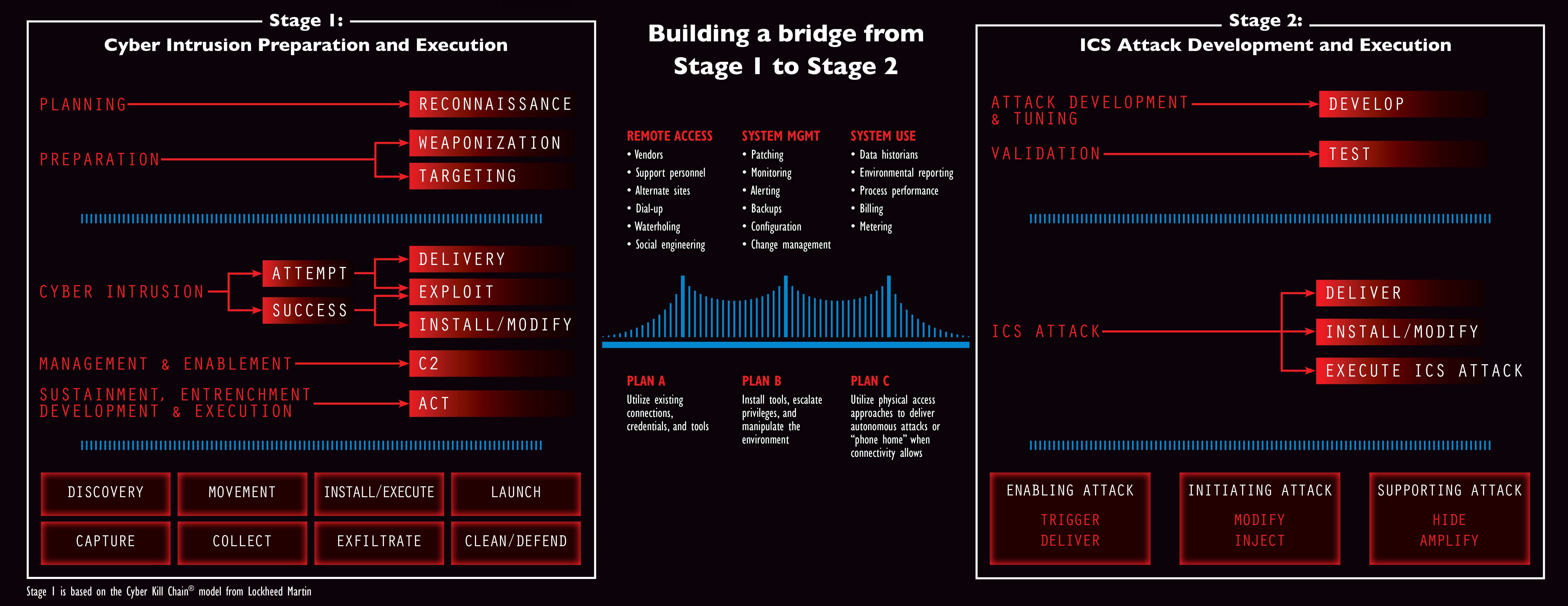
In our poster graphic we took the perspective of an adversary trying to manage through these same challenges of the IT / OT separation and at the same time leverage the growing trends of IT / OT convergence. We started working on this visualization with a view of the traditional Lockheed Martin Cyber Kill Chain that has been modified here as a Stage 1 graphic to reflect a multi stage ICS focused attack with a Stage 2 element.
Both Stage 1 and Stage 2 graphics and a full description on the activities that occur at each of these stages can be read in an earlier whitepaper authored by Michael Assante and Robert M Lee.
As SANS has already developed community resources describing Stage 1 and Stage 2 elements, what we focused on with this poster and the discussion around Stage 1 and Stage 2 is the concept of an adversary moving from a stage 1 attack into a stage 2 attack. Often we do not discuss the methods adversary's utilize when building the bridges from an IT environment to an operations environment, we typically just focus on the data an adversary was able to exfiltrate from IT environments or the damage to workstations or servers from the release of malware. In a small number of cases we have escalated the discussion to look at the impacts an attack team was able to achieve in a successful Operations focused attack.
Rarely do the discussions examine the bridge building required to move from IT to OT and the opportunities for defenders to mitigate. The graphics created for the poster are intended to show the adversary approaches to bridge building and IT / OT opportunities and challenges from the perspective of the attacker. We also considered the variations and dynamic nature of a targeted campaign and the need for a flexible adversary attack plan with many options (we represented an example Plan A, B, and C to demonstrate the point, while in reality there are tremendous variations of each plan for an adversary team).
The full poster graphic bridge concept is shown below (click to zoom).
Free Stuff Reminder!
The digital ICS poster resource is available Here
If you would like printed copies please send a request to: info@sans.org
I encourage everyone interested in ICS cyber security to join the daily discussions occurring in the ICS Community Forum, in addition if you are interested in obtaining the individual graphic elements used in this post please join the forum and download the files directly in a couple of different available formats. They are available for your use as resources, please reference the source