[Editor's note: Volume Shadow copies on Windows completely rock. They give administrative tools (and penetration testers) access to all kinds of wonderful things on Windows, including recently deleted files, files with a lock on them, and much more. They are almost like a nifty side channel into the guts of the Windows file system, making it ripe for exploration, research, and pwnage with a heavy does of plundering mixed in for good measure. Mark Baggett has been one of the main gents (along with Tim Tomes) leading the charge in researching how pen testers can use Volume Shadow copies. In this post, Mark shows how you can use Python to interact with Volume Shadow copies, so you can explore them in-depth. After describing how to list, create, and access such copies from Python, he provides a nifty Python script called vssown.py that does all the work for you. I'm hoping that the info Mark provides here inspires readers to start more aggressive analysis of Volume Shadow copies from their own interactive Python shells to reveal more cool pen test uses of Volume Shadow copies. -Ed.]
Volume Shadow copies are immensely useful to penetration testers, often containing a treasure trove of valuable information. What if the domain administrator knows the penetration testers are coming, so he deletes "passwords.txt" from his desktop? No problem! The password file is sitting there waiting for you in the volume shadow copies. Files such as NTDS.DIT (the Active Directory Database) can be locked up by the operating system so you can't safely get to them. With Volume Shadow copies, no problemo! You can create a new volume shadow copy and grab the file from the copy and plunder it for hashes from anyone in the domain. If you are still not convinced, check out these posts that demonstrate the ever-loving-sweetness of Volume Shadow Copies.
http://pauldotcom.com/2012/10/volume-shadow-copies—the-los.html
http://pauldotcom.com/2011/11/safely-dumping-hashes-from-liv.html
http://lanmaster53.com/2013/03/taming-the-stubborn-tomcat/
The bad news is that there are not a lot of great libraries out there that use Volume Shadow copies in Python. The good news is that you can use the win32com module and the Component Object Model (COM) to interface with the WIN32_ShadowCopy service and do everything you need to do. BUT (more bad news here) using COM within Python is a pain in the tushie. The interface to COM objects is less than intuitive, and not easily accessible. BUT (ahhh... a lil' more good news), I've done the hard part for you. If you are creating a Python-based executable for Windows, and you need it to access Volume Shadows copies, this article will make your life a bit easier. Let's start with the easy stuff.
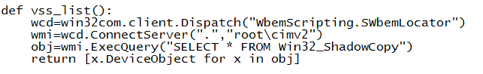
To get a list of the Volume Shadow copies on the system is pretty simple. You can take the code from vssown.vbs, lookup the corresponding python statement, and translate the code to Python. (VSSOWN.VBS is downloaded here: http://ptscripts.googlecode.com/svn/trunk/windows/vssown.vbs). After creating a scripting object and connecting to the server, you use ExecQuery to pull a list of all the Volume Shadow Copies on the system. Then you can use a for loop to step through each of the shadow copies and pull the "DeviceObject" attribute. The DeviceObject attribute is what you will use to access the data in the Volume Shadow Copies.
Some excellent sample code with a list of all the attributes you can access is available here: http://www.activexperts.com/admin/scripts/wmi/python/0274/
Creating a Volume Shadow Copy is more difficult. To do so, we have to call the "Create" method of the Win32_ShadowCopy COM object and, as I mentioned, documentation on the API is somewhat lacking. Anytime I am trying to learn something new in Python (or much of my penetration testing, for that matter), I experiment with it in a Python Shell. The interactive shell lets you experiment with objects' methods and attributes and see what they are used for, all in real-time, interactively. First, we import the required module and create an object called "wmi" that points to a "Win32_ShadowCopy" COM object. This can be done with two simple lines of code.
import win32com.client
wmi=win32com.client.GetObject("winmgmts:\\.\root\cimv2:Win32_ShadowCopy")
We want to call the "create" method for this Win32_ShadowCopy object. To execute a module, you use wmi object's ExecMethod() method. For example: "wmi.ExecMethod(<method name> , <com object parameters>)". The first argument is a string containing the target method's name. The second argument is a COM object that contains the target method's parameters. Setting those method parameters can be a bit confusing. Even knowing the correct parameters isn't straight forward.
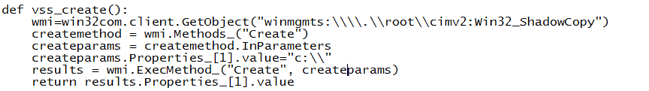
Here is how I did it. Remember, wmi points to a Win32_ShadowCopy object. First, I create an object called "createmethod" that points to the "Create" method on that object. Then, I create an object called "createparams" that points to the create methods parameters. After that, you can use the "createparams" object to examine the parameters and set their values. Here is an example:
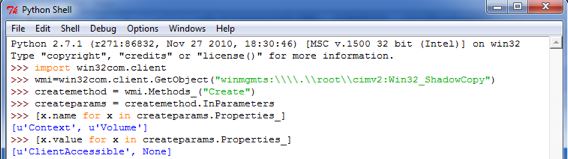
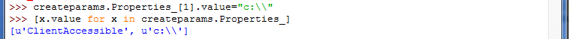
"CreateMethod" points to the "Create" method for the Win32_ShadowCopy object. "CreateParams" points to the input parameters for the Create method. Then, I use list comprehension to examine the names of each of the input parameters. The names of the parameters are stored in the .name attribute. Here you can see that Create method requires a parameter called "Context" and one called "Volume". "Context" is in the first position in the list, while "Volume" is in the second. Then I use list comprehension to examine the current values for each of these parameters. You can see that the "Context" is set to "ClientAccessible" and that the "Volume" is set to "None". If you examine the MSDN page for this object you will see that we have to specify a drive letter in the "Volume" parameter. I want the volume to be set to "C:\". So I set the value and check it again.
Now I can call ExecMethod() and retrieve the result. The result will be in the "Properties_" attribute in the form of a list of COM Objects. The ".value" of the first item in the list is the response code. You can find a reference for all of the response codes here:
http://msdn.microsoft.com/en-us/library/windows/desktop/aa394428%28v=vs.85%29.aspx
If the response code is a zero, then the 2nd item in the list will contain the ID for the new Volume Shadow Copy.
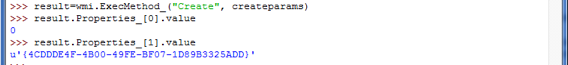
So my new shadow copy ID number is 4CDDDE4F-4B00-49FE-BF07-1D89B3325ADD. Let's check it with VSSADMIN to see if it was really created.
To check which volume copies exist we type "vssadmin list shadows". At the bottom of the list we should see our new shadow copy.
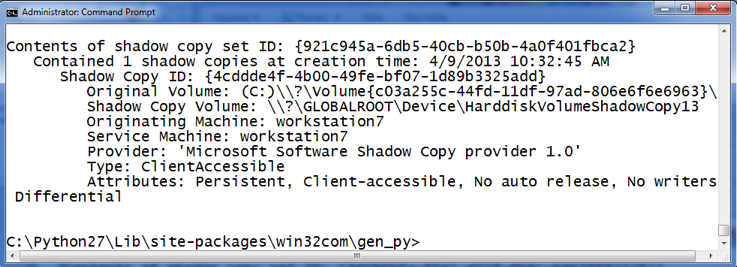
It is there! We created a Volume Shadow Copy! Note the matching Shadow Copy ID. Put all that together and we get the following function to create a volume shadow copy.
Now, here is the best part. You don't have to do ANYTHING special to access data stored in the volume shadow copies. Dude... read that again. That is awesome. Thank you, Volume Shadow copies and Python! You can read from them just like you would any other file in the file system. NOTE: Shadow Copies are read only and cannot be written to with any utilities.
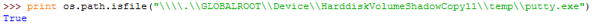
So, if you want to see if a file exists you can do that using standard Python file-system-interaction techniques:
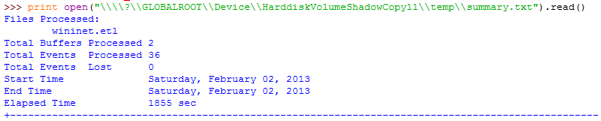
If you want to open a file and read the file contents, you just treat it like any other file:
As a matter of fact, the only two functions I really need to do just about anything I want with Volume Shadow copies are vss_list() and vss_create(). These functions can be easily adapted if you do need something else.
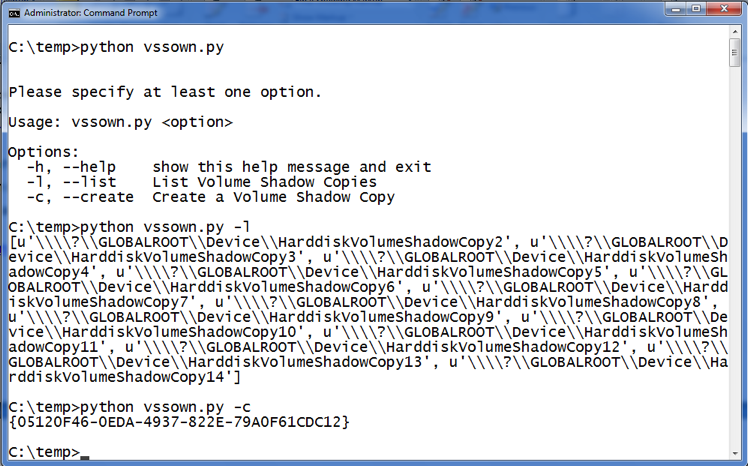
If you just want someone to write a script for you that does all this, simply ask and ye shall receive. Well, you don't even have to ask. I already did it for ya. Here you go. Feel free to grab a copy of my vssown.py script, which does all the heavy lifting for you to list, create, and then interact with Volume Shadow copies, all within your comfy interactive Python shell or from within your own scripts. Just download that txt file and shave off the .txt suffix.
Here is what it looks like when you run the vssown.py script. Remember, you need admin privs to access the Volume Shadow Copy Service.
If you want to learn how to use techniques like this in your own programs, then check out my brand spanking new SANS course, SEC573 Python For Penetration Testers. Here are some upcoming dates for the class:
http://www.sans.org/course/python-for-pen-testers
-Mark Baggett
Follow me on twitter: @MarkBaggett



