Tags:
You've purchased the smart cards for your Windows PKI, you can change the user's PIN on these cards, but if you cannot also change the cards' default Administrator PIN, the cards are nearly worthless. But watch out, some smart card vendors make it difficult to change the Administrator PIN as a marketing trick.
Background
The Administrator PIN, which is sometimes called the "Admin Key" or "Unblock PIN", is a different PIN than the user's. With knowledge of the Administrator PIN, an attacker could steal the smart card (or smart USB token) and then reset the user's PIN to anything, allowing the attacker to authenticate as that user.
Sometimes the Administrator PIN is not a number; it might be a password, passphrase, hexadecimal key or some other secret, but the idea is the same: with the Administrator PIN a stolen smart card can be changed to allow the attacker to use the card as the original owner.
The Problem
But the problem is that 1) the default Administrator PIN is well known, and 2) you often cannot change the Administrator PIN unless you purchase additional expensive management software (at least, that's what some vendors want you to think).
So, while you might think you've purchased vendor-neutral smart card hardware which you own free and clear, and while you might think you've got the necessary drivers and management tools for this hardware (just like for your video card or NIC), there is a good chance you'd be wrong. The smart card vendor's tools allow you to change the user's PIN, but can you actually change the Administrator PIN itself? Are you sure?
Some smart card vendors and resellers deliberately refuse to give away (or to sell cheaply) a tool to change the default Administrator PIN. Why? It's a devious marketing trick to get you to try out their cards and then hopefully you'll come back to buy their PKI management suite, which of course includes this tool. This is devious because it is done deliberately, the web sites of these vendors and resellers scarsely mention the risk of not changing the default Administrator PIN (if at all), and often the salespeople of these vendors/resellers only discuss the risk after you've purchased the cards and done your testing. In forums and newsgroups, customers have asked vendors for these tools for years, so it's not as though the vendors are unaware of the need.
I've spoken to some of these vendors and their defense is basically that the word "evaluation" or "kit" or "testing" appears somewhere on the page where the cards are sold. But this is clearly insufficient given the risk of leaving the Administrator PIN to the default and the inexperience of many IT staff who are new to the complexities of PKI. I've had multiple past attendees of my Windows PKI course at SANS complain about this problem as they've tried to deploy smart card solutions on a budget. Besides, you'd think you could trust the smart card vendors to warn you about this kind of huge vulnerability, right? Not really.
What To Do
Make sure you can get a tool to change the Administrator PIN. If you have a large number of planned smart card users, you might want to invest in a lifecycle management suite, but don't be strong-armed into making this purchase unnecessarily (especially with the capabilities already built into Windows Server and the client-side smart card support in Windows Vista/7 and later).
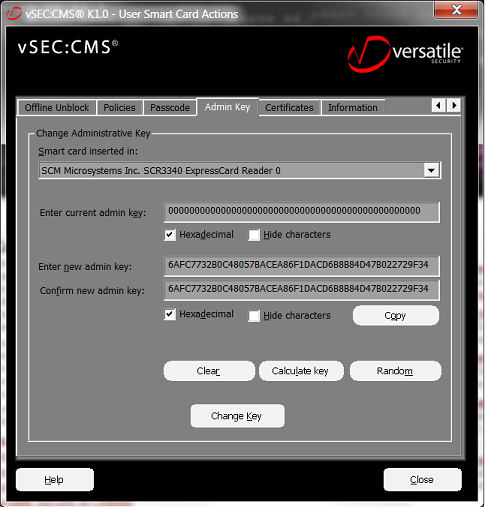
If you've already purchased smart cards but the vendor does not offer a tool you can afford, try to find a third-party alternative. For example, Versatile Security has a tool called "vSEC:CMS K-Series" that works with a variety of smart cards and tokens (Axalto Cryptoflex .NET, Gemalto .NET, Raak C2), and you can download this tool for free even if you don't purchase their management suite.
If, after searching the Internet, you cannot find a free or inexpensive tool to change the Administrator PIN, you might consider switching vendors. After all, do you really want to reward your vendor by purchasing their management suite if these are the kind of marketing tricks they pull?
And if you know of other free tools for managing smart card Administrator PINs on Windows, please let me know and I'll post the link here. I know that free tools are unlikely to scale to large deployments -smart card management suites exist for a reason, after all- but that's not the point. You own the smart cards, you should be able to fully use them.