https://www.youtube.com/watch?v=h076AA1ZroY
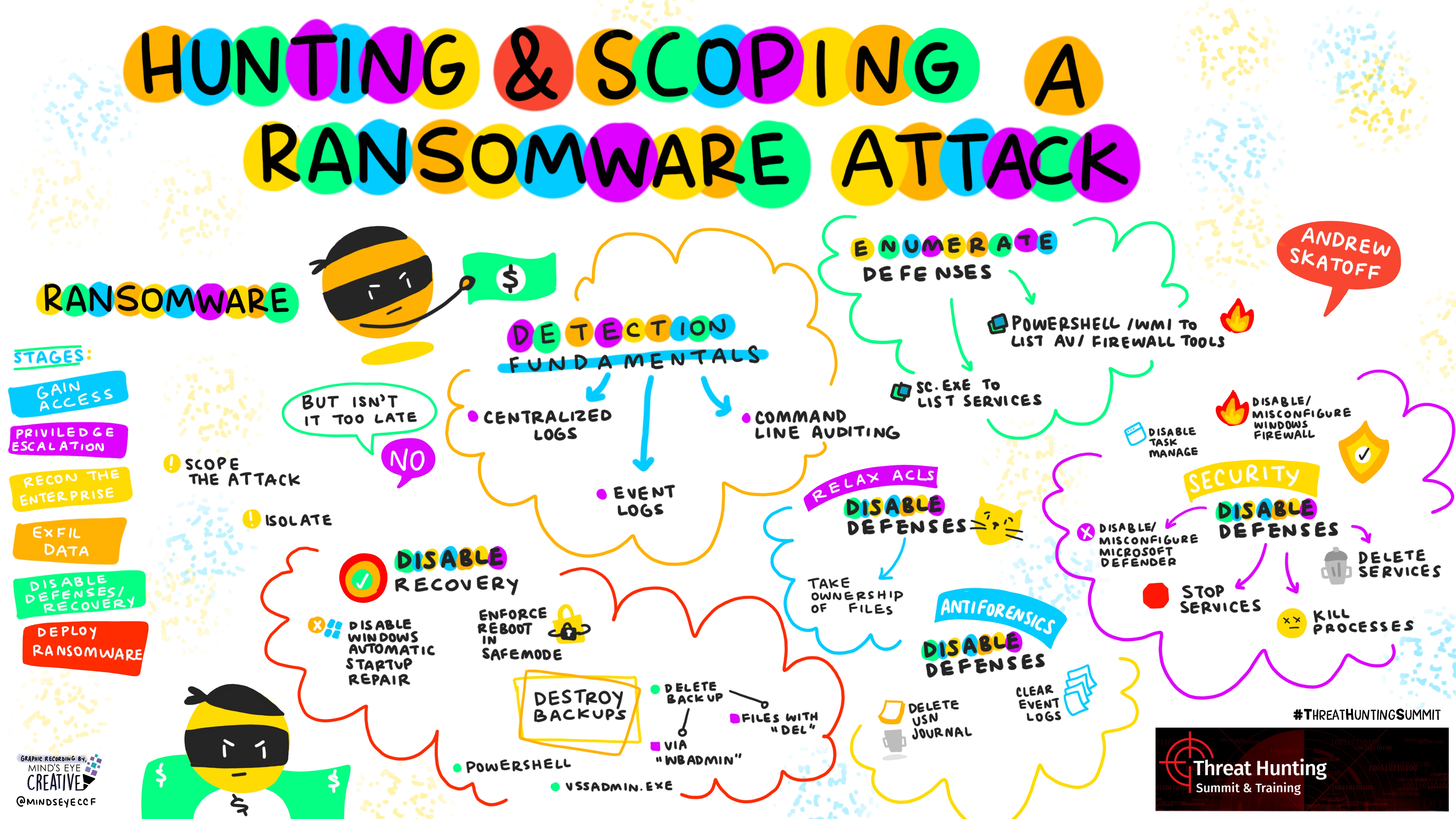
Hunting and Scoping A Ransomware Attack
Encrypting all your files is a ransomware actors' final objective. But when the frantic helpdesk calls start coming in, can you quickly identify all impacted devices? Can you determine if data exfil and extortion are part of the attack? Can you tell if they destroyed your backups? This talk will cover common ransomware gang "hands on keyboard" techniques for stealing your data, disabling defenses, and making your data and devices resistant to recovery. Participants will take away hunt logic which can be employed right away for early detection and rapidly scoping a ransomware compromise.