I can honestly say that the most common question I am asked by examiners, investigators, students and even my neighbors is, "which phone is the most secure?" Obviously, the concern behind the question varies. Some want to secure their own device, and others, like myself, want to prove everyone in DFIR wrong by cracking into the toughest and most secure devices.
Smartphone security has gotten drastically stronger in 2014. This year, we are expecting even more challenges when examining smartphones. When thinking about the forensic aspects of smartphone security and encryption, we have to consider two things:
- How are we going to get access to the data?
- Even if we get a dump of the device, can we decrypt and examine the data?
- What happens if I can access the data, but the application data is encrypted?
Let's look at a few devices to consider our options. First, Windows Phone 8 (WP8) brought us new issues that commercial forensic kits could not fully support. The good news is that these devices only comprise approximately 2.5% of the smartphone market. The bad news — criminals still use them! My co-author for FOR585, Cindy Murphy, worked with others in DFIR to get over this hurdle when it really mattered. A criminal investigation forced Cindy into action when she realized the critical part of the crime was a Nokia 520 running WP8. Cindy essentially formed a "team" to divide and conquer on this WP8 device. They successfully obtained a JTAG image of the device and manually parsed the data. FYI, if you haven't looked at a smartphone dump in awhile, it's no longer just a few files you need to sift through like legacy mobile device images. You are now looking at a small hard drive of evidence needing to be manually parsed. This task alone could take a lot of patience and a really long time.
What makes WP8 devices so secure compared to the others? WP8 devices brought change that we, smartphone examiners, haven't faced in the past. This is the first OS introduced into the smartphone community that utilized BitLocker technology to support data encryption on the device with AES 128, which utilizes a Trust Platform Module (TPM) to protect the encryption key once the data is secure. These two factors have caused heartache for us smartphone examiners who have one of these devices appear in our evidence lineup. Fortunately, Cindy and her "team" were able to obtain a physical image, bypass the encryption and parse the relevant evidence to support her criminal investigation. Their work can be found here: http://dfir.to/Win8Phone-Forensics If you haven't read this paper, you should!
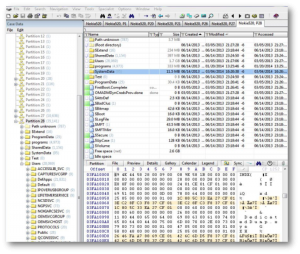
Cindy and her "team" worked directly with Cellebrite developers to provide a recent release supporting the Nokia 520 and similar WP8 devices, thus making your life easier. In FOR585 we stress the importance on understanding how the data is stored and parsed by your tool. One tool cannot uncover and decode all data on a smartphone. It's your job to learn the file system structures, data formats, encoding schemas and all of the other fun bit of smartphone forensics. Additionally, in Cindy's case, one single tool did not parse or interpret all of the data from this device. The smartphone forensic tools could not handle the data dump. You will find this is true for some smartphones, so you need to understand all concepts of smartphone data. Your toolbox must contain both smartphone forensic tools as well as standard DFIR tools (yes, the same ones your learned about in FOR408 and FOR572). Below we see X-Ways being used to examine a WP8 smartphone image.
Here are some cheat sheet locations where evidence on the WP8 resides (for more details on how to manually parse the data, please refer to the referenced paper, above):
SMS and Contacts:
Users\WPCOMMSERVICES\APPDATA\Local\Unistore\store.vol
MMS:
SharedData\Comms\Unistore\Data
Call Logs:
Users\WPCOMMSERVICES\APPDATA\Local\UserData\phone
Internet History and Cookies:
Users\DefApps\APPDATA\INTERNETEXPLORER\INetCahe\.
Multimedia Files:
Users\Public\Pictures\CamerRoll\.
Application data and other traces of user activity were located on this device and required manual examination, custom Python scripts and intensive reconfiguration of raw data. Keep in mind that all 3rd party applications are different, store data with different obfuscation levels and require manual parsing (aka, don't trust your tool — be smarter than it and validate your findings).
Now let's consider the other devices that are trying to outsmart us. BlackBerry has always been secure. Pre-paid phones have locked data ports and knock-off devices are counterfeit, so support is inconsistent. iOS devices containing the A5-A8 chips are difficult if they are locked. There are methods for bypassing the lock, such as using the host computer Lockdown files as well as attempting to crack the PIN with the IP-BOX. If the user doesn't back up their iOS device with a computer and uses a complex passcode? let's just say you may not be getting access to that device, unless of course it's jailbroken and not 64-bit. So may considerations, right?
Then there is Android Lollipop, which introduced the first default full disk encryption for this OS. How this will change our methods is TBD. I suggest you sign up for a FOR585 class to see how these devices can be accessed when you seem to have been outsmarted.
When considering which SANS course to take next, consider this — smartphone operating systems contain file systems similar to those discussed in FOR408 and FOR518, but need to be handled in a unique way. What about network traffic on smartphones? Here's something to consider that you may have learned in FOR572 that should lead you to take FOR585 next.
"This class is critical for any forensicator in 2015," said Phil Hagen, SANS Certified Instructor and course lead for FOR572, Advanced Network Forensics and Analysis. "One thing we focus on from the network side is to hunt for adversaries in an environment and identify which endpoints require detailed examination. When those are workstations or servers, the analysis path is very well-established. However, if that endpoint is a modern mobile device, a forensicator must have the skills necessary to perform a comprehensive examination. With 'smart' mobile devices, the techniques are often vastly different than those required for traditional computing devices."
References:
[1] http://dfir.to/Win8Phone-Forensics
[2] Practical Mobile Forensics
Heather Mahalik serves as a PM and leads the forensic effort for Oceans Edge, Inc. She has spent over twelve years conducing computer crime investigations ranging counter-intelligence to high profile criminal investigations. She is a Certified Instructor, course lead and co-author of FOR585 Advanced Smartphone Forensics and co-author of FOR518 Mac Forensic Analysis at the SANS Institute. Heather is co-author of Practical Mobile Forensics, by Packt Publishing. Find her on Twitter @HeatherMahalik and on her personal website/blog smarterforensics.com.