SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsIt's a bit like "Simon Says"

Cloud security compliance is following the regulatory and industry-specific rules and requirements by providers and customers to ensure the security, privacy, and legal compliance of data, the associated applications, and of how the data is stored and processed in the cloud environment.
Cloud security compliance is analogous to the good old-fashioned children’s game – “Simon Says” where you either follow the rules or in simple terms - you are out of the game! In general, cloud compliance refers to the enforcement of specific regulations, standards, and best practices designed to ensure the security and privacy of data stored and processed in cloud environments. Furthermore, cloud compliance involves implementing the necessary administrative and technical controls to protect data, systems, and applications from unauthorized access, data breaches, and other security risks.
Adherence to the industry-specific regulations, such as the Health Insurance Portability and Accountability Act (HIPAA) for the healthcare industry, the Payment Card Industry Data Security Standard (PCI DSS) for organizations handling credit card information, or General Data Protection Regulation (GDPR) to protect European Union citizen data are just a few of the many regulations with which organizations may need to comply.
The “lifting and shifting” of systems, infrastructure, and applications from on premise to the various cloud providers has become a widespread option for many organizations to store, process, and access data; however, it also introduces new security challenges due to the landscape of shared infrastructure and remote data storage. Cloud service providers (CSPs) play a fundamental role in ensuring cloud compliance. CSPs offer a wide variety of security features and controls, such as data encryption, identity & access management, network access controls, and security monitoring; to assist organizations in meeting compliance requirements. CSPs are also required to undertake independent audits and certifications to verify their adherence to many of the same industry regulations, specific security standards, and best practices – providing these attestations to their constituents. For example, the big 3 cloud providers have resources to demonstrate their compliance capabilities:
AWS: aws.amazon.com/compliance/
Azure: azure.microsoft.com/en-us/explore/trusted-cloud/compliance
GCP: cloud.google.com/security/compliance
Starting with governance, a system directed by executive leadership who are responsible for making decisions and priorities related to minimizing the security risks for an organization, the governance body oversees meeting the security objectives for the organization. With this authority in place, the security & compliance teams’ role is to assess and manage risks, establish security policies and procedures, and implement technical controls to protect their cloud-based systems and data. Other supporting activities include conducting regular vulnerability assessments, implementing strong authentication mechanisms, encrypting sensitive data, and monitoring system logs for suspicious activities. To aid in the understanding of the workloads and security posture, many organizations will then rely on utilities from third-parties, or some of which are provided by the CSP, such as:

Image 1:AWS Security Hub1
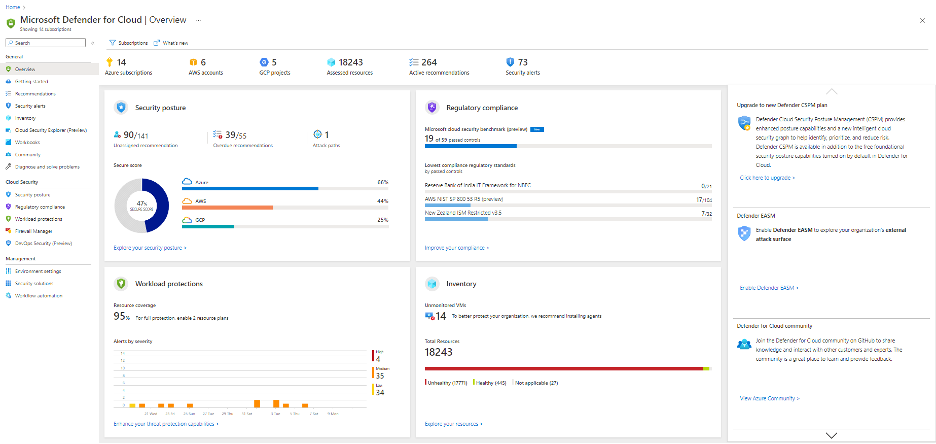
Image 2. Microsoft Defender for Cloud2
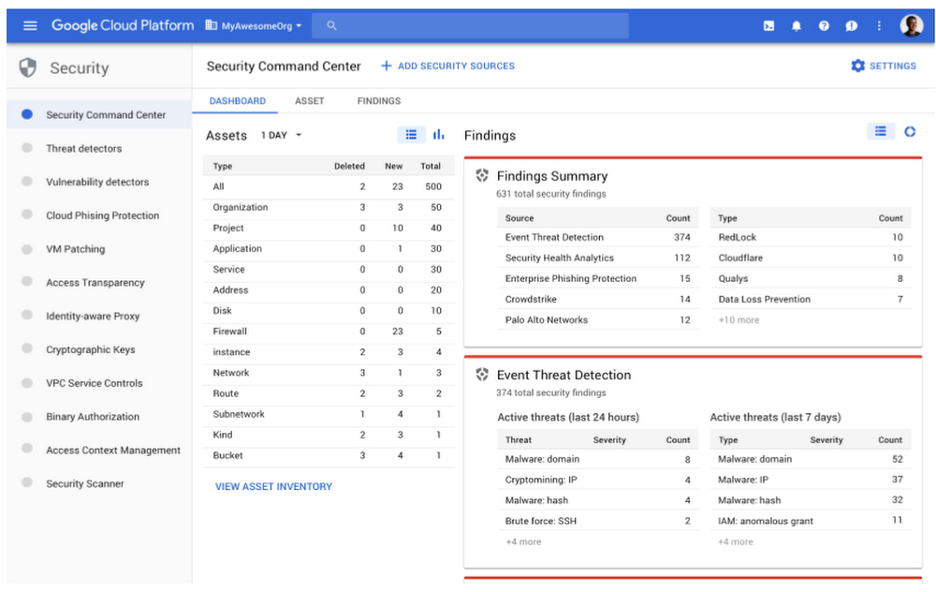
Image 3: GCP Security Command Center3
Additionally, considering the rapid nature of cloud resources being created, modified, and destroyed at a moment’s notice along with the advent of many organizations leveraging multiple cloud providers, this will likely require specialized tools such as cloud security posture management (CSPM) and cloud workload protection platform (CWPP) to determine the compliance objectives are being met to account for this increasingly dynamic ecosystem.
The most common frameworks for cloud compliance include the Cloud Security Alliance (CSA) Cloud Controls Matrix (CCM), the International Organization for Standardization (ISO) 27001, and the National Institute of Standards and Technology (NIST) Special Publication 800-53. The CSA CCM provides a comprehensive set of controls and guidelines for assessing the security posture of cloud service providers and their customers. ISO 27001, on the other hand, is an internationally recognized standard for information security management systems, offering a framework for organizations to establish, implement, maintain, and continually improve their information security. NIST SP 800-53, developed by the U.S. government, offers a detailed catalog of security controls and guidelines to help federal agencies and organizations in various sectors achieve compliance with regulatory requirements. These frameworks play a crucial role in ensuring data security, privacy, and regulatory compliance in the cloud, addressing the unique challenges presented by the dynamic nature of cloud computing environments.
Cloud security standards are essential guidelines and best practices for ensuring the protection of data and applications in cloud environments. These standards, such as ISO 27001, the Cloud Security Alliance's Cloud Controls Matrix (CCM), and NIST Special Publication 800-53, provide a structured framework to address security challenges associated with cloud computing. They define controls for data privacy, access management, encryption, and risk mitigation. By adhering to these standards, organizations can bolster their security posture, achieve compliance with regulations, and demonstrate their commitment to safeguarding digital assets, fostering trust in cloud services. These standards play a crucial role in maintaining the integrity and confidentiality of data in an increasingly interconnected and dynamic digital landscape.
Overall, cloud security compliance provides assurance to organizations and their stakeholders that appropriate security measures are in place to protect sensitive data and maintain regulatory compliance in cloud environments.
Learn more about cloud security compliance from SANS Cloud Security training courses at sans.org/cloud-security/
[2] https://learn.microsoft.com/en-us/azure/defender-for-cloud/overview-page
The Ultimate List of SANS Cheat Sheets


Chris Edmundson has been employed in the information technology arena for over 25 years, working in a wide variety of roles, primarily in the public sector related to administration of K-12 public schools and at higher education institutions.
Read more about Chris Edmundson