SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsThis blog describes the newest offering from SANS targeted specifically to managers involved in keeping industrial control systems (ICS) safe.

SANS ICS418: ICS Security Essentials for Managers is an intense two-day course that provides techniques to address a manager’s biggest concern: keeping industrial processes secure.
NOTE: THE SECOND BETA RUN OF THIS COURSE IS NOW OPEN FOR REGISTRATION. REGISTER HERE.
Industrial security has evolved rapidly over the past decade. Originally seen as an afterthought, industrial security is increasingly cited by executives and boards as a key ICS cyber risk to their organization. This is largely due to the prominence of real-world events, increased threats, and the tangible impacts of industrial cyber attacks—including stalled production, equipment damage, and even loss of life.
Over the past decade, SANS has specifically focused on providing ICS practitioners with hands-on learning that leverages actionable techniques and tools. The SANS ICS curriculum, which started in 2013 with ICS410: ICS/SCADA Security Essentials, today features four technical courses, each more advanced than the next. The course series culminates with the in-person ICS612: Cybersecurity in-Depth, which leverages an ICS test lab and network to defend based on real-world incidents.
All of these courses share a vision outlined by Mike Assante and the SANS ICS team to arm and train capable defenders with the skills needed to protect the essential services that enable our modern world to function:
A critical part of Mike’s vision is to develop leaders who can in turn enable technical practitioners, create a vision for ICS security, and measure the success of that vision across their team.
That is where ICS418 comes in. This new course blends ICS security essentials with advanced management techniques to train leaders, regardless of their background or prior experience with ICS, security, or engineering and operations.
ICS security is an ever-changing field that requires practitioners to continually adapt defense strategics to meet new challenges and threats. To compound the challenge, any security changes need to be 100% tested in order to ensure and maintain the safety and reliability of industrial operations.
The terms “critical infrastructure” and “operators of essential services” refer to countless industrial organizations across the globe. Some of them are lifelines for our modern society, such as water, energy, food processing, and critical manufacturing. Regardless of the field in which they operate, all industrial facilities must know that their processes are secure and safe. With increased threats, new trends in technology, and evolving workforce demands, it is vital that security managers in operational technology (OT) be trained in techniques to defend their facilities and their teams.
ICS418 fills the identified gap among leaders working across critical infrastructure and OT environments. It equips both new and experienced managers responsible for OT/ICS or converged IT/OT cybersecurity. The course provides the experience and tools to address industry pressures to manage cyber risk in a way that prioritizes the business side as well as the safety and reliability of operations. ICS leaders will leave the course with a firm understanding of the drivers and constraints in these cyber-physical environments and will gain a nuanced understanding of how to manage the people, processes, and technologies in their organizations.

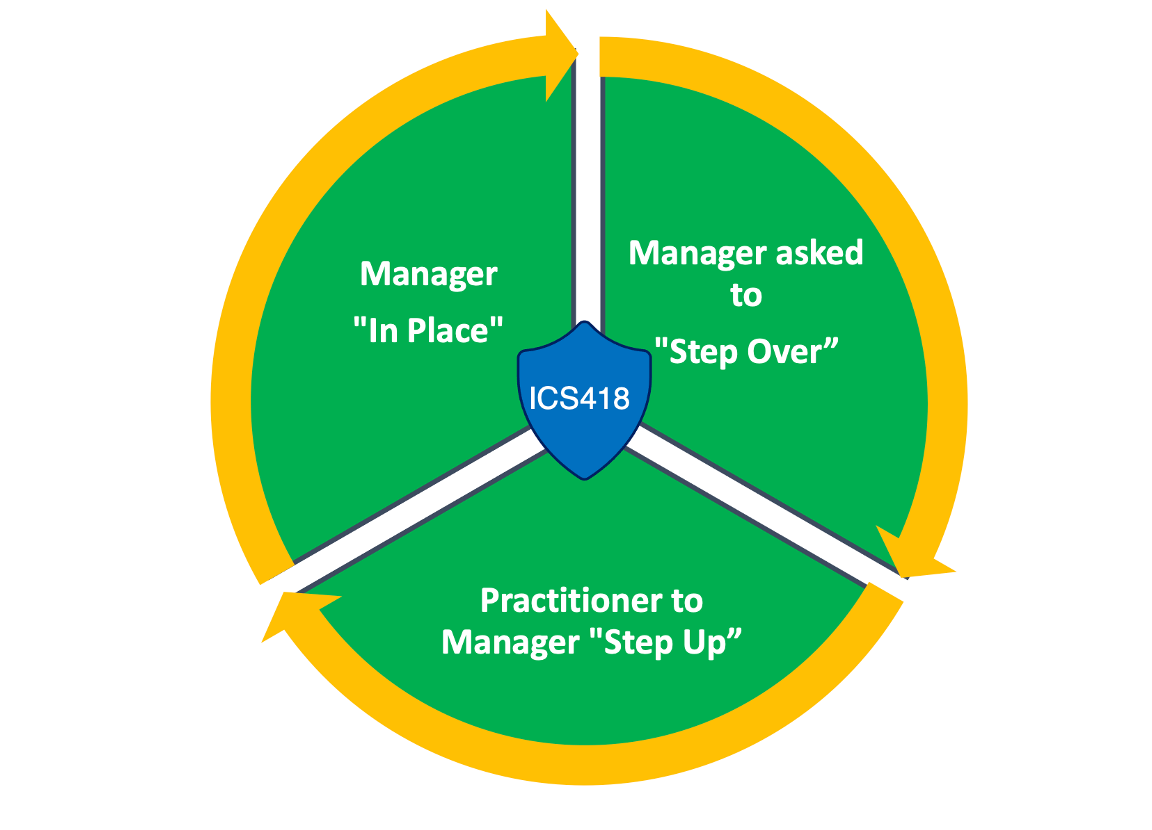
ICS418 is aimed at managers of personnel responsible for securing the day-to-day operations across an organization’s OT and ICS environments. This includes distributed control systems (DCS) and supervisory control and data acquisition (SCADA) systems. Managers of these teams often come from diverse backgrounds with a focus either on management skills, with minimal understanding of ICS environments, or on technical skills, with minimal management skills.
The course is designed to bridge the gap between those two skill sets by following the axiom that a “rising tide lifts all boats” when it comes to ICS security managers. The course addresses the needs of the full range of managers, including:
Unlike IT systems, ICS and their corresponding industrial facilities require considerations beyond traditional cybersecurity controls. Within IT networks, the main security concerns may revolve around exfiltration of data (such as customer or employee records) or the destruction/unavailability of data (as in a ransomware attack). In OT environments, on the other hand, the loss or manipulation of visibility, control, or safety can lead to physical impacts in the tangible world. These sorts of scenarios highlight the importance of preventing and detecting cybersecurity incidents, but what can you do with devices that may be 30+ years old and are generally incapable of providing access controls, end point protection, or system hardening? How do you build a team of defenders who need to understand both security and engineering? What do you do when your organization spends more on its website than on industrial security?
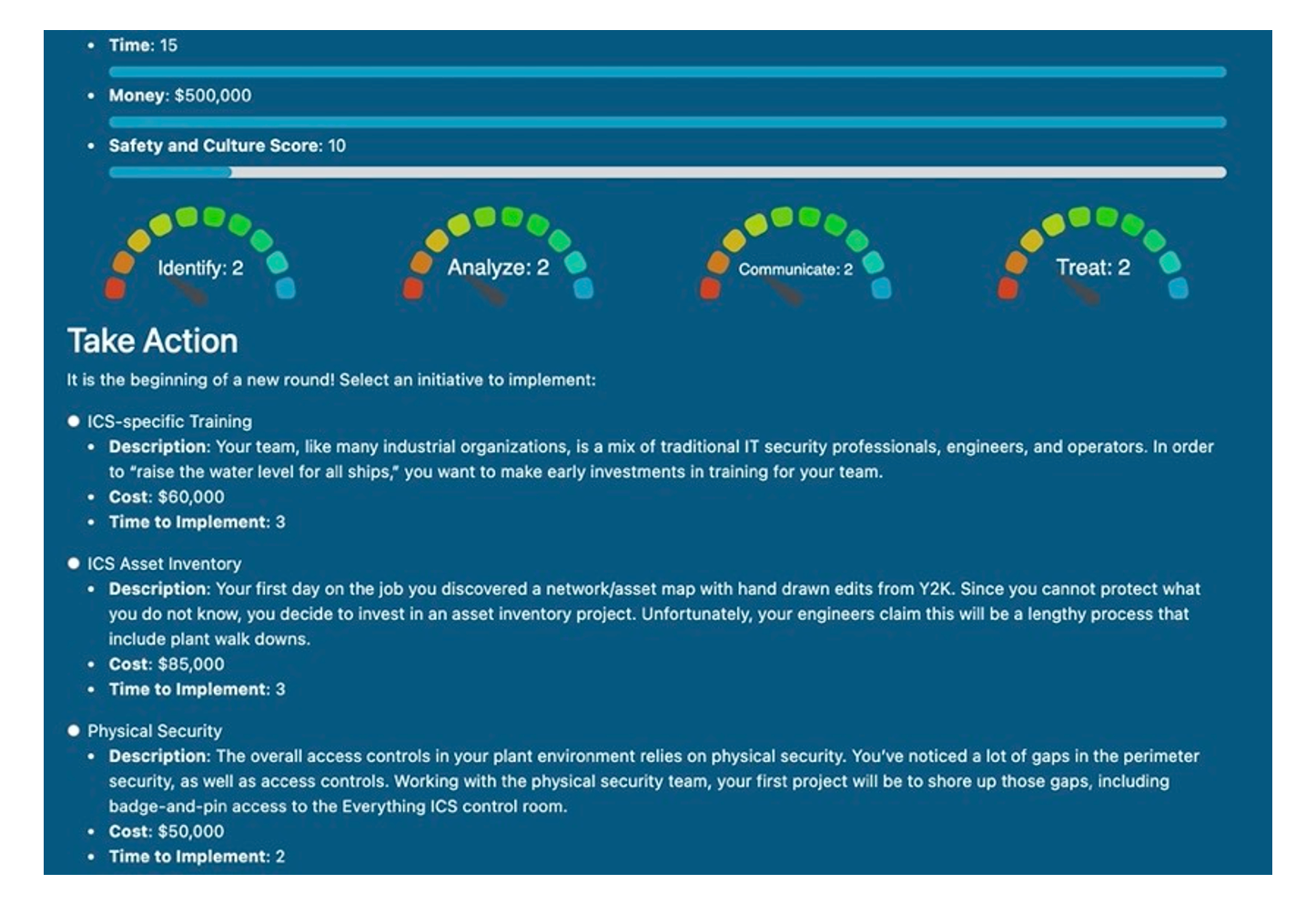
ICS418 is designed to address these concerns —and many more. An ICS418 course graduate will be able to:
It wouldn’t be a SANS class without considering what happens after the course is over—in this case, what we might call “Day 3.” That’s right: a two-day course where we address what to do next in the days and months after the course is finished. Beyond the hours of content, we have loaded ICS418 with extra material to apply to your current (and future) ICS security strategy. Bonus material includes handouts for forecasting, tools for ICS security assessments, and much more! You can take the applied guided discussions and labs and tailor them based on your unique operating environment—essentially a gift from SANS to the students and the larger ICS security community.
We have filled this course to the brim with a combination of technical and managerial skill development tailored specifically for industrial organizations. Broken into two days, ICS418 is designed to “short circuit” the needed skills for ICS security leaders both in terms of covering topics specifically relevant to ICS, as well as developing abilities to manage people, processes, and technologies.
Then join us for ICS418! REGISTRATION IS NOW OPEN FOR BETA 2 - TAKING PLACE APRIL 4 & 5, LIVE ONLINE.
 |  |
Certified ICS SANS Instructor for ICS515: ICS Visibility, Detection, and Response | Certified ICS SANS Instructor for ICS456: Essentials for NERC Critical Infrastructure Protection |
Dean brings over 20 years of technical and management experience to the classroom. He has worked in both information technology and industrial control system (ICS) cyber defense in critical infrastructure sectors such as telecommunications, electricity generation, transmission, distribution, and oil and gas refineries, storage, and distribution. Dean is an ambassador for defending industrial systems and an advocate for the safety, reliability, and cyber protection of critical infrastructure. His mission as an instructor is to empower each of his students, and he earnestly preaches that “Defense is Do-able!” Over the course of his career, Dean’s accomplishments include establishing ICS security programs for critical infrastructure sectors, building and managing converged IT/OT incident response and threat hunt teams, and conducting ICS cyber defense assessments. | In his role at Dragos, Jason Christopher focuses on ICS monitoring technology, threat intelligence, and incident response. Previously he was the Chief Technology Officer for Axio. His experience includes providing technical leadership on security and resilience issues, and developing technology platforms for security metrics and benchmarking. Prior to Axio, Jason led cybersecurity metrics and information assurance research at the Electric Power Research Institute. He has also served as the technical lead for cybersecurity capability and risk management at the U.S. Department of Energy, where he managed the Cybersecurity for Energy Delivery Systems Operations Program that included the Cybersecurity Capability Maturity Model and other collaborative efforts. |
“Now, more than ever, it is important to train and equip ICS security leaders with the skills and knowledge they need to protect critical infrastructure. This course is the culmination of decades of experience in building and managing OT/ICS security teams -- and it is the course we wish was available to us when we started on our ICS security journey. We’ve drawn across our roles in different industrial sectors and teams-- as former company executives, team leads, incident responders, and managers-- to create a course empowering leaders facing the greatest challenge of our time: industrial control system cybersecurity.”
– Jason D. Christopher & Dean C. Parsons


Launched in 1989 as a cooperative for information security thought leadership, it is SANS’ ongoing mission to empower cybersecurity professionals with the practical skills and knowledge they need to make our world a safer place.
Read more about SANS Institute