SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsA dedicated ICS security awareness training program is no longer an option, it’s imperative to help manage human risk


Industrial Control Systems (ICS) and Operational Technology (OT) systems run electricity generation, water supply, oil and gas, transportation networks, manufacturing processes, and more. The importance of protecting critical infrastructure that support our daily lives, and ensuring they operate safety, cannot be overstated. For several years now, the human element has been involved in approximately 80% of all breaches. This metric illustrates that security is not just a technology challenge but also a challenge in managing human risk. In the case of ICS/OT systems, where preventing safety impacts are paramount, this is clearly an identified risk that must be properly managed for our critical infrastructure.
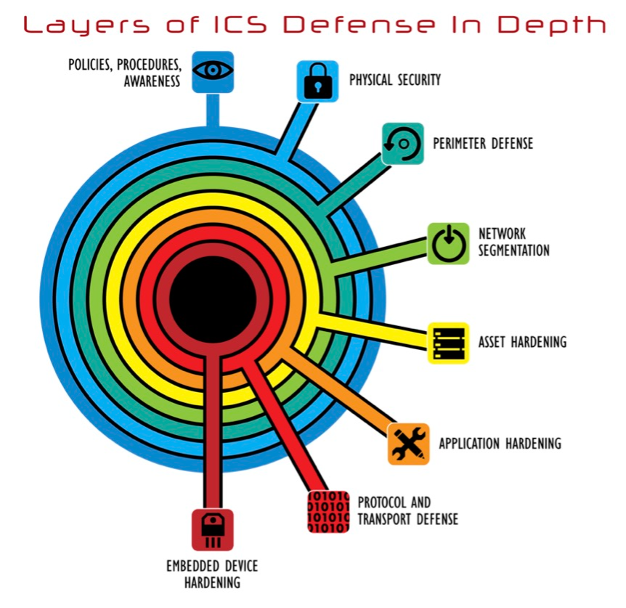
The first layer of the ICS defense in depth practice is Policies, Procedures, and Awareness. In this context, awareness means fostering a culture of ICS cybersecurity awareness among ICS operators, engineers, and stakeholders. Security awareness is crucial to safeguarding all critical infrastructure in every ICS sector. It is in fact, foundational to a functional ICS defense in depth strategy.
As ICS engineering processes become increasingly interconnected, the need for dedicated ICS cybersecurity awareness has never been more apparent. ICS security awareness empowers control system environments personnel to make informed decisions and contribute to a physically safer and more resilient engineering environment.
No matter your role in an organization with industrial control systems and processes, everyone has a part to play in securing the critical infrastructure systems that power our world against cyber threats.
ICS security awareness bridges the gaps and differences between IT and ICS, enables convergence of skillsets and modern threats, and considers legacy assets, unique control system risks, and required ICS incident response steps unlike what is used in IT. As such, for mature ICS facilities, a dedicated ICS Security Awareness program is part of their regular security defense and defense implementation plans. Many use the SANS Security Awareness Maturity Model. The SANS Security Awareness Maturity Model has become the industry standard which organizations use not only to benchmark the maturity of their security awareness program but leverage it as a strategic roadmap to both plan and communicate the impact of their program. What makes this model so powerful is that it helps organizations quickly determine why their program may not be having the impact they want, provides proven steps they can take to mature their program, and details how to communicate the value of the program to leadership. This model enables organizations and facilities to effectively manage their human risk in both IT and ICS/OT environments.
https://images.contentstack.io/v3/assets/blt36c2e63521272fdc/blt671d79c87251021f/6516d55f3ce1e84d48ffda8f/ssa-ics-blog-image-2.jpgShort ICS security awareness training modules with knowledge-checks make a positive change in culture to reduce overall ICS-specific risk and can improve safety in any ICS sector.
Modern security awareness initiatives for IT environments must continue. However, for ICS organizations, security awareness must go beyond traditional IT security awareness content. That’s why the SANS Institute is excited to announce the release of our NEW ICS Engineer Security Awareness Training. This new series of short-form ICS/OT cybersecurity awareness training modules helps reduce cyber risk and improve safety in critical infrastructure sectors that make, move, and power the world.
https://images.contentstack.io/v3/assets/blt36c2e63521272fdc/bltef90c8c7eebe40c0/6516d55e3366a48e20b32870/ssa-ics-blog-image-3.pngThe new SANS ICS security awareness training consists of more than 20 new training modules, specifically developed to address the unique risks and defense capabilities for individuals working in critical infrastructure environments. Each training module includes live course recordings delivered by certified instructors and related animations illustrating each learning objective. The modules are designed to detail recent ICS threats, related countermeasures, and critical, archivable risk-reducing improvements. They can be deployed in a newly established ICS security awareness program or added to an existing program to address ICS specific challenges, risks, and related control system defenses.
Each of the 21 new modules contain knowledge checks in a modern delivery style and cover the following main topics:
The new ICS security awareness training is role-based, so you can customize your security awareness training based on the needs of your specific workforce, from your non-technical staff to your veteran industrial cyber practitioners, all the way up to your executives and board of directors. Your ICS security awareness training program should target roles including but not limited to:
When a facility deploys the SANS Institute’s ICS security awareness training, the initiative can be measured to contribute to managing ICS risk reductions. In ICS418: ICS Security Essentials for Managers, we teach you and your workforce how to deploy, measure, and track ICS security awareness initiatives. For example, each of your employees that takes ICS418 walks through a leadership lab on how to tailor the ADKAR Model for ICS and how to be most effective at delivery and reducing ICS risk as it applies to an organization’s operating culture.
Tim Conway and I teamed up in the SANS recording studio to create all-new scripts and a new approach to on-screen graphics with a focus on content delivery for the most effective learning experience.
https://images.contentstack.io/v3/assets/blt36c2e63521272fdc/blt4280078bacfd9407/6516d55f6e4311006ded1b29/ssa-ics-blog-image-6.pngAs industrial control systems increasingly adopt new technology, threats posed by cybercriminals to critical infrastructure also increase. Industrial control system security awareness is no longer an option but an imperative. By fostering a culture of cybersecurity awareness, adopting best practices, and collaborating across sectors, we can build resilience and protect our critical infrastructure in the digital age. With targeted, easy-to-deploy ICS/OT-specific security awareness modules, facilities can deploy training, reduce human risk, and measure effectiveness and participation with quick knowledge checks. All of which is doable, measurable, and required for today’s modern ICS/OT cybersecurity defense programs.
Learn more about the NEW SANS ICS Security Awareness Training content and modules.
Learn more about the ICS418: ICS Security Essentials for Managers course.
Learn more about the ICS515: ICS Visibility, Detection, and Response course.


Dean Parsons, CEO of ICS Defense Force, teaches ICS515 and co-authors ICS418, emphasizing ICS-specific detection, incident response, and security programs that support OT operations—aligning practitioners and leaders on clear, defensible action.
Read more about Dean Parsons