Tags:
Cybersecurity Leadership - Not Just for CISOs
To be effective as cybersecurity leaders, security managers need both technical knowledge and management skills to gain the respect of technical team members, understand what technical staff are actually doing, and appropriately plan and manage security projects and initiatives. This is a big and important job that requires an understanding of a wide array of security topics. The Cybersecurity Leadership Curriculum develops cyber leaders who have the practical skills to build and lead security teams, communicate with technical and business leaders alike, and develop capabilities that build your organization's success.

Current SANS Cybersecurity Leadership Curriculum
Download the SANS Cybersecurity Leadership Curriculum Brochure
Why Take Cybersecurity Leadership Training With SANS?
- Leadership Focused – appropriately plan and manage security projects and initiatives
- Technical Focused – gain the respect of technical team members and understand what technical staff are actually doing
- Holistic, Curated Curriculum – based on various job roles and focus areas
- Hands-On Labs – extensively focused on “the how” through non-traditional “lab work” such as analyzing case-studies, participating in team exercises, and competing against classmates in Cyber42 games
- World-Class Instructors – versatile, real-world security practitioners authoring & instructing
- Comprehensive Courseware – access to slides, notes, audio files, labs, and additional resources for future reference
- Certification Prep – specialized training that will help you prepare for a GIAC certification attempt
NEW COURSE 2024
NEW COURSES 2023
- LDR520: Cloud Security for Leaders- Now 5 Days!
- LDR553: Cyber Incident Management - Now 5 Days!
- LDR433: Managing Human Risk - Now 3 Days!
Cybersecurity Leadership Training
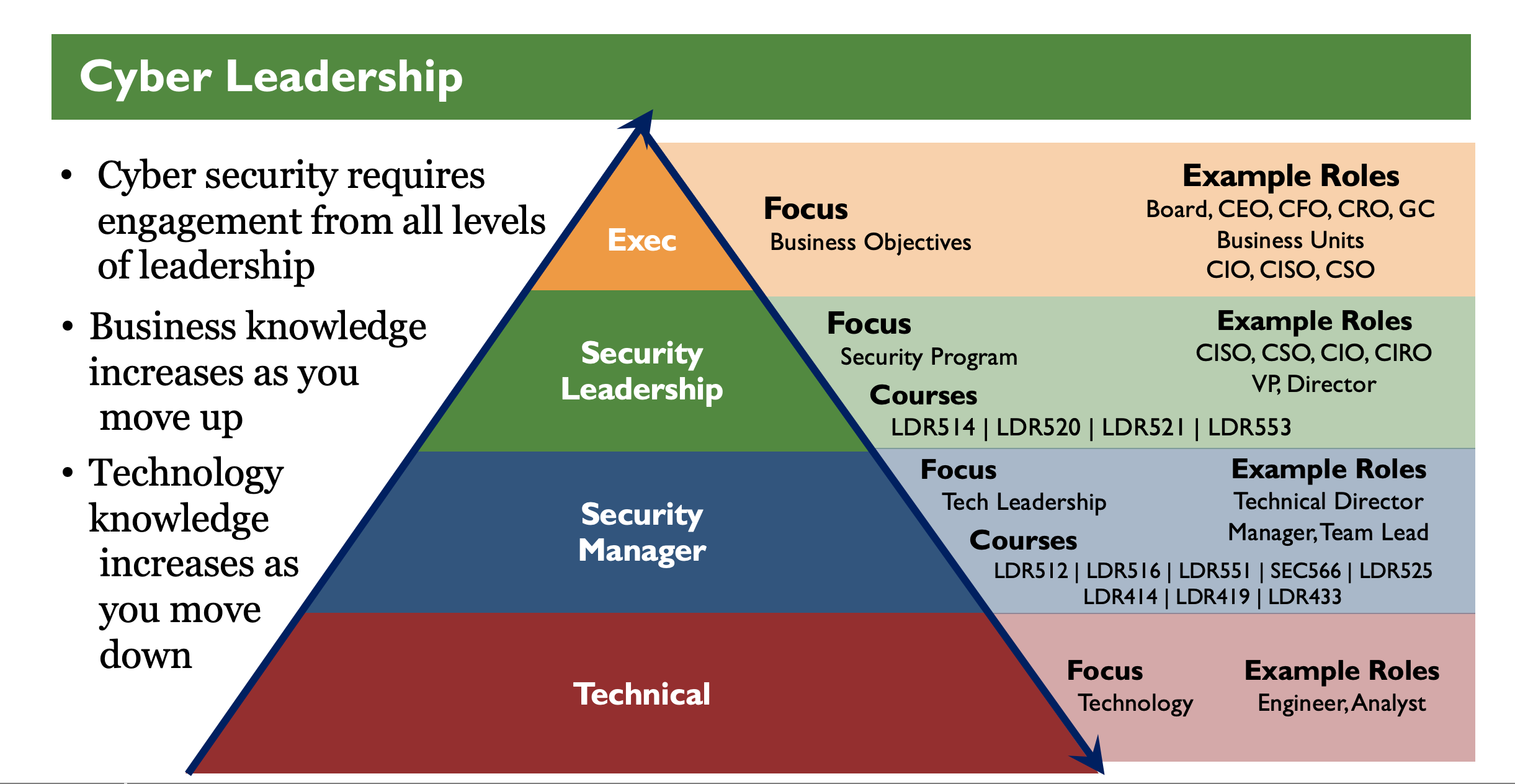
Cybersecurity requires engagement from all levels of leadership throughout an organization. The key differentiator between these various levels is the amount of technical knowledge and business knowledge that is required to succeed. Technology knowledge is invariably greater as you move down the pyramid while business knowledge increases as you move up the pyramid with increasingly more responsibility. Roles and titles will vary across organizations of different sizes and industries but the amount of technical knowledge that an engineer or analyst requires is vastly different from that which a CISO or even a VP of Security requires.
However, as a security leader or manager we are in a difficult situation. We need to have enough technical acumen to understand our team, resolve technical disagreements, and weigh in on appropriate technical direction. At the same time, we must have enough business understanding to convey technical security topics in ways that non-technical leaders can understand and translate business drivers to our teams in ways that they in turn can understand.
That is the focus of this curriculum. To give security leaders both the technical knowledge and management skills to gain the respect of technical team members, understand what technical staff are actually doing, and appropriately plan and manage security projects and initiatives.
CISO Training | Cybersecurity Leadership Triads
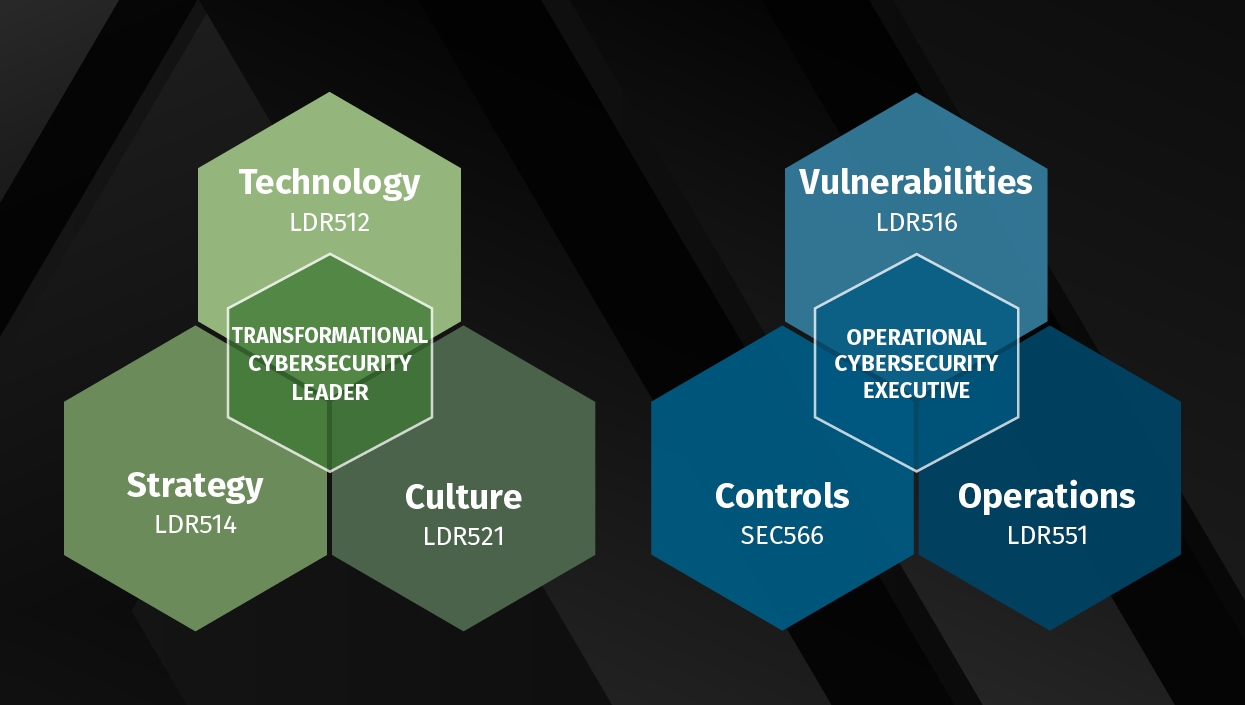
In an effort to help our students find the right path, SANS Cybersecurity Leadership Curriculum has created two triads of courses and certifications that align to help create stronger, more well-rounded cybersecurity leaders. This entire landing page is dedicated to describing these triads in detail as well as providing a series of related resources.
Transformational Cybersecurity Leader - 1 page flyer
Operational Cybersecurity Leader - 1 page flyer
GIAC Cybersecurity Leadership Certifications

In addition to courses, we offer eight GIAC certifications, one SSA certification.
- GSLC: GIAC Security Leadership Certification
- GSTRT: GIAC Strategic Planning, Policy, and Leadership
- GCCC: GIAC Critical Controls Certification
- GSOM: GIAC Security Operations Manager
- GCPM: GIAC Certified Project Manager
- GISP: GIAC Information Security Professional
SSAP: SANS Security Awareness Professional: Managing Human Risk
- GLEG: GIAC Law of Data Security & Investigations
- GSNA: GIAC Systems Network Auditor
Leadership Challenge Coins

Hundreds of SANS Institute students have stepped up to the challenge and conquered. They’ve mastered the concepts and skills, beat out their classmates, and proven their prowess. These are the elite, the recipients of a SANS Challenge Coin, an award given to a select portion of the thousands of students that have taken any of the SANS courses.
SANS Technology Institute | Graduate Certificate in Cybersecurity Leadership
Designed for working information security professionals, the 16-credit-hour graduate certificate in Cybersecurity Leadership prepares you to build and execute strategic plans that resonate with business executives, create effective information security policy, design and deploy information security environments, and lead, inspire, and motivate cybersecurity teams. You'll learn from some of the world's top cybersecurity experts, gain hands-on technical and leadership experience you can apply immediately on the job, and emerge with 5 industry-recognized GIAC certifications. A 100% online option is available.
Applications are accepted monthly. Learn more.
SANS CyberTalent Assessments
Whether you are looking to hire new employees for cybersecurity positions or creating opportunities for your existing talent, SANS CyberTalent can help ensure you find the right skills match for the job. According to the U.S. Department of Labor, the cost of a bad hire is at least 30 percent of the employee's first-year earnings - for a security analyst, that's $27,000+. You can't afford to get hiring wrong at a time when talent is increasingly difficult to find. SANS CyberTalent Assessments measure the aptitude and skills of cybersecurity professionals, allowing employers to create professional development and retention programs for existing employees or test and rank the skill sets of candidates to fill open positions.
Learn more about Cybersecurity Leadership Assessments here.
Access Our Free Resources
- Cybersecurity Leadership Website
- Recommended Reading List
- Cybersecurity Leadership Webcasts
- Blogs
- Whitepapers
- Posters
Free Cybersecurity Leadership Course Demos
SANS offers free course demos for all courses available on the SANS OnDemand platform. Browse them here.
Join Us On Social
- X - @SecLeadership
- LinkedIn - SANS Security Leadership
- SANS YouTube - Cybersecurity Leadership Playlist
- Discord - SANS Cybersecurity Leadership

Purchase SANS Cybersecurity Leadership Gear here.
Complete Cybersecurity Leadership Curriculum
- LDR414: SANS Training Program for the CISSP® Certification | 6 days | GISP
- LDR419: Performing a Cybersecurity Risk Assessment | 2 days
- LDR433: Managing Human Risk | 3 Days | SSAP
- LDR512: Security Leadership Essentials for Managers | 5 Days | GSLC
- LDR514: Security Strategic Planning, Policy, and Leadership | 5 Days | GSTRT
- LDR516: Building and Leading Vulnerability Management Programs | 5 Days
- LDR520: Cloud Security for Leaders | 5 Days
- LDR521: Security Culture for Leader | 5 Days
- LDR525: Managing Cybersecurity Initiatives and Effective Communication | 5 Days | GCPM
- LDR551: Building and Leading Security Operations Centers | 5 Days | GSOM
- LDR553: Cyber Incident Response | 5 Days
- AUD507: Auditing Systems, Applications, and the Cloud | 6 Days | GSNA
- SEC566: Implementing and Auditing CIS Controls | 5 Days | GCCC