SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsFeeble Security Culture Disconnected from Business Objectives

This is Part 3 of 4. Read the other parts here:
In the fall of 2020 SANS published a series of blog posts about an incident at the fictional company Rekt Casino. SANS then hosted a series of webcasts on lessons learned from the incident from a strategy, technology and culture perspective and how you can apply the lessons learned to your own organization. This blog post is an extension of those webcasts with a focus on security culture and how you can improve and leverage your security culture based on lessons from Rekt Casino and the SANS MGT521 Security Culture course.
Some background. Rekt Casino has been in business for approximately 20 years, to date they have invested only in the most basic security needs. Security has never been at the forefront. From a compliance perspective, they are subject to MICS under the Nevada Gaming Control Board. MICS is the Minimum Internal Control Standards for Casino technology. Rekt has a small IT team of 3 people that serve as help desk, network administration, and server administration. The team tries to secure these systems as they are deployed. The Ransomware attack initiated as a phishing attack and was successful due to no spam filtering, phishing or malware protections on the email server or any active awareness training.
From a cultural perspective we learned that Rekt Casino had no real security culture. By security culture we mean the attitudes, perceptions and beliefs people have about security and the security team. A strong security culture is important, as it not only helps ensure a far more secure workforce, but a strong security culture will enable far more of your security initiatives to succeed. You can have the best strategy in the world, but if you have a toxic or dysfunctional culture you will not succeed. A huge number of security initiatives, such as vulnerability management, DevSecOps, or a EDR or SSO rollout fail not because of technology but because of human issues. So what does a strong security culture look like? Indicators of a strong security culture include
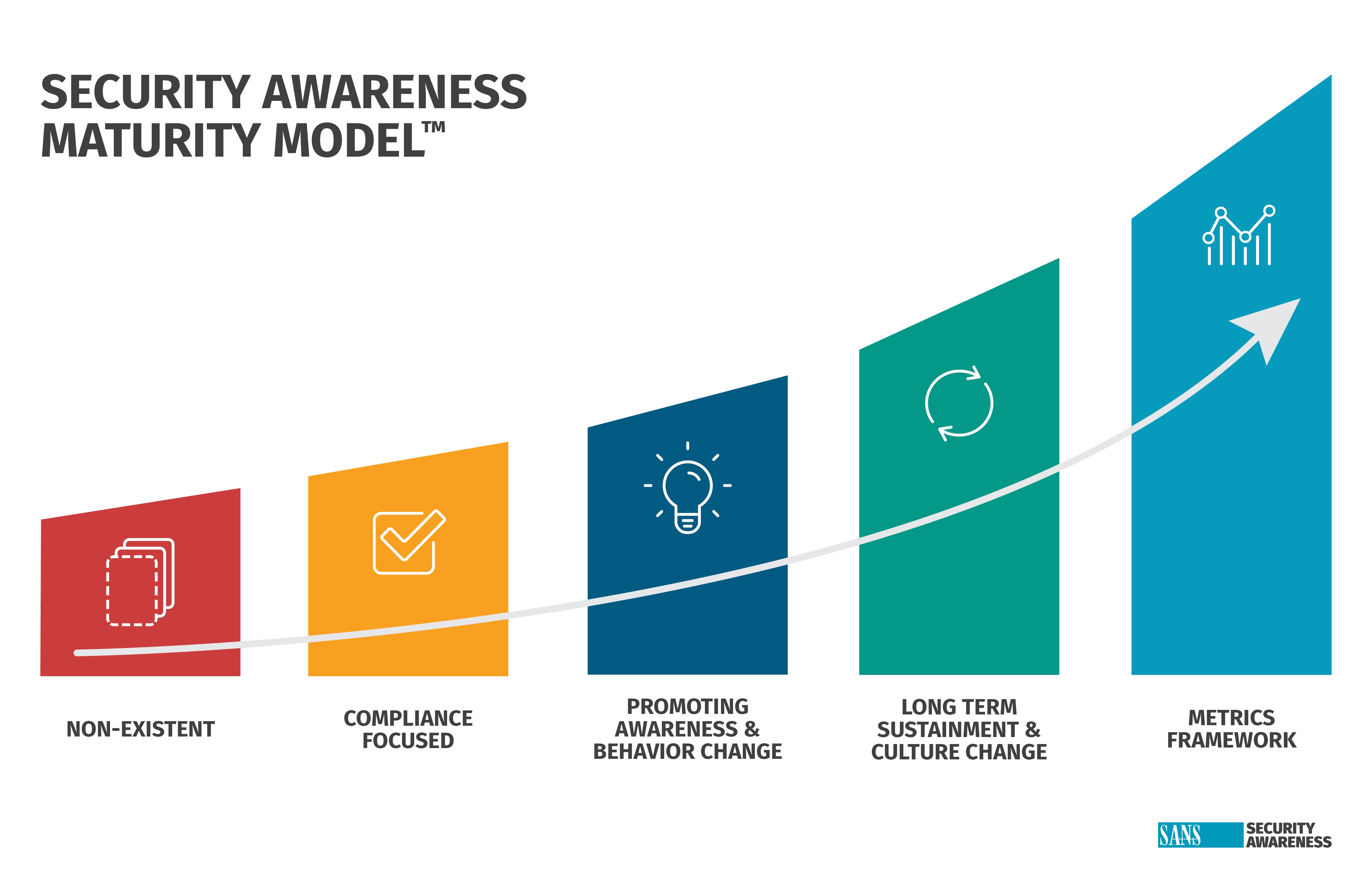
The problem was in the case of Rekt Casino, there was no security culture. Very few people had any thoughts about security because they had no interaction with the security team and to date had received very little if any communication or training about security. As such, they were not aware of any security policies, nor aware they were responsible for security or how their actions could impact security. This is a big reason why the Ransomware incident happened at Rekt. The non-existent security culture was confirmed by a security culture survey that was conducted after the event, where we asked questions such as
To address this we can start improving Rekt Casino’s security culture using models and lessons learned from the world of organizational change. This is a highly developed field of study that has hundreds of case studies, articles, books and research in how organizations can build a strong culture. While models like Kotter’s 8 Steps and ADKAR provide highly structured process, in the SANS MGT521 Security Culture course we build on and simplify them by focusing on Motivation and Ability.
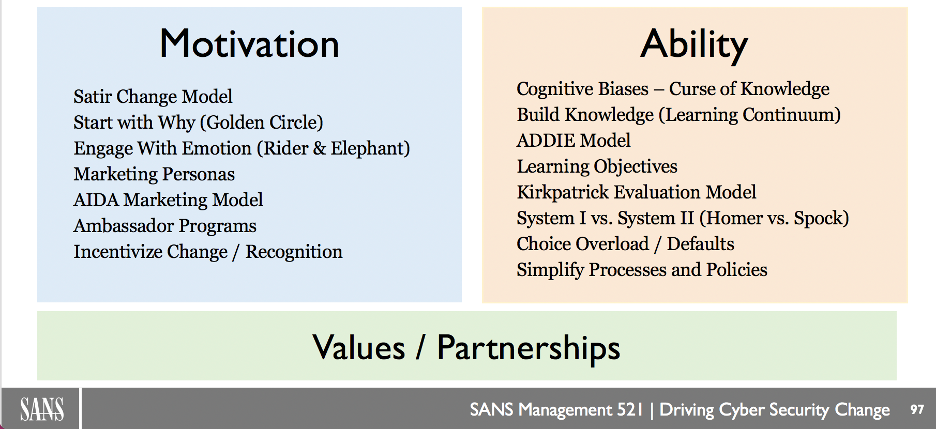
The key to building a strong security culture is applying both of these to all of your security initiatives and outreach efforts. Motivation is ultimately about explaining the WHY of any security initiative, policy or effort. To truly engage and motivate people we need to first explain the why of security from a personal perspective, how people benefit. Simone Sinek explains the logic of this using his Golden Circle, one of the highest rated Ted Talks ever published. The book Switch compares the need for a personal, emotional hook to the rider and the elephant.
However, ability in many ways is where we can have an even greater impact building a strong security culture. Far too often what we the security community communicate or require of people we perceive as simple. What we don’t realize is for the vast majority of the world security is confusing, scary and intimidating. This cognitive bias is known as Curse of Knowledge, the more of an expert you are at something the worse you are at communicating it. There are numerous ways to simplify security, such as reviewing and simplifying complex or confusing policies (hint: passwords), teaching people in fun and engaging ways (hint: involve marketing) and architecting an environment where it’s much easier for people to exhibit the behaviors we want. Ultimately, ability is all about making security simple for people - instead of fighting human nature we work with it.
Rekt Casino is in the perfect position to start building a strong security culture as there is no culture at this point, they are starting with a clean slate. By following the key principles of Motivation and Ability, not only will they have a far more secure workforce, but their new security strategy and initiatives will be far more likely to succeed. Learn more in the new five day SANS MGT521 Security Culture course, part of the SANS Leadership Triad.
Lance Spitzner has over 20 years of security experience in cyber threat research, security architecture and awareness training and is a SANS Senior Instructor. He helped pioneer the fields of deception and cyber intelligence with his creation of honeynets and founding of The Honeynet Project. In addition, Lance has published three security books, consulted in over 25 countries, and helped over 350 organizations build awareness programs to manage their human risk. He is also on the Board of Advisors for Attivo Networks. Lance is the author and an instructor for MGT433: Managing Human Risk: Mature Security Awareness Programs, and MGT521: Leading Cybersecurity Change: Building A Security-Based Culture, and built the SANS Security Awareness business unit from the ground up over the past 10 years. With the catalyst of COVID-19, Lance created multiple resources for securing humans from home, from those working remotely for the first time or managing newly remote teams, to children learning and playing online. Read more about Lance here.


Lance revolutionized cyber defense by founding the Honeynet Project. At SANS, he has empowered over 350 organizations worldwide to build resilient security cultures, transforming human risk management into a cornerstone of modern cybersecurity.
Read more about Lance Spitzner