SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsPulling It All Together

This is Part 4 of 4 of our Rekt Casino Operational Leadership series, which itself is a sequel to our Transformation Series dealing with the same case study. You can read the other parts of the Operational Leadership series here:
If you haven’t been following the Rekt Casino webcast series, let’s get you up to speed: Rekt Casino suffered a breach due to a ransomware attack. The Casino did not have an operational security capability in place to help it resist intrusions, maintain awareness of its weaknesses, or identify and respond to attacks.
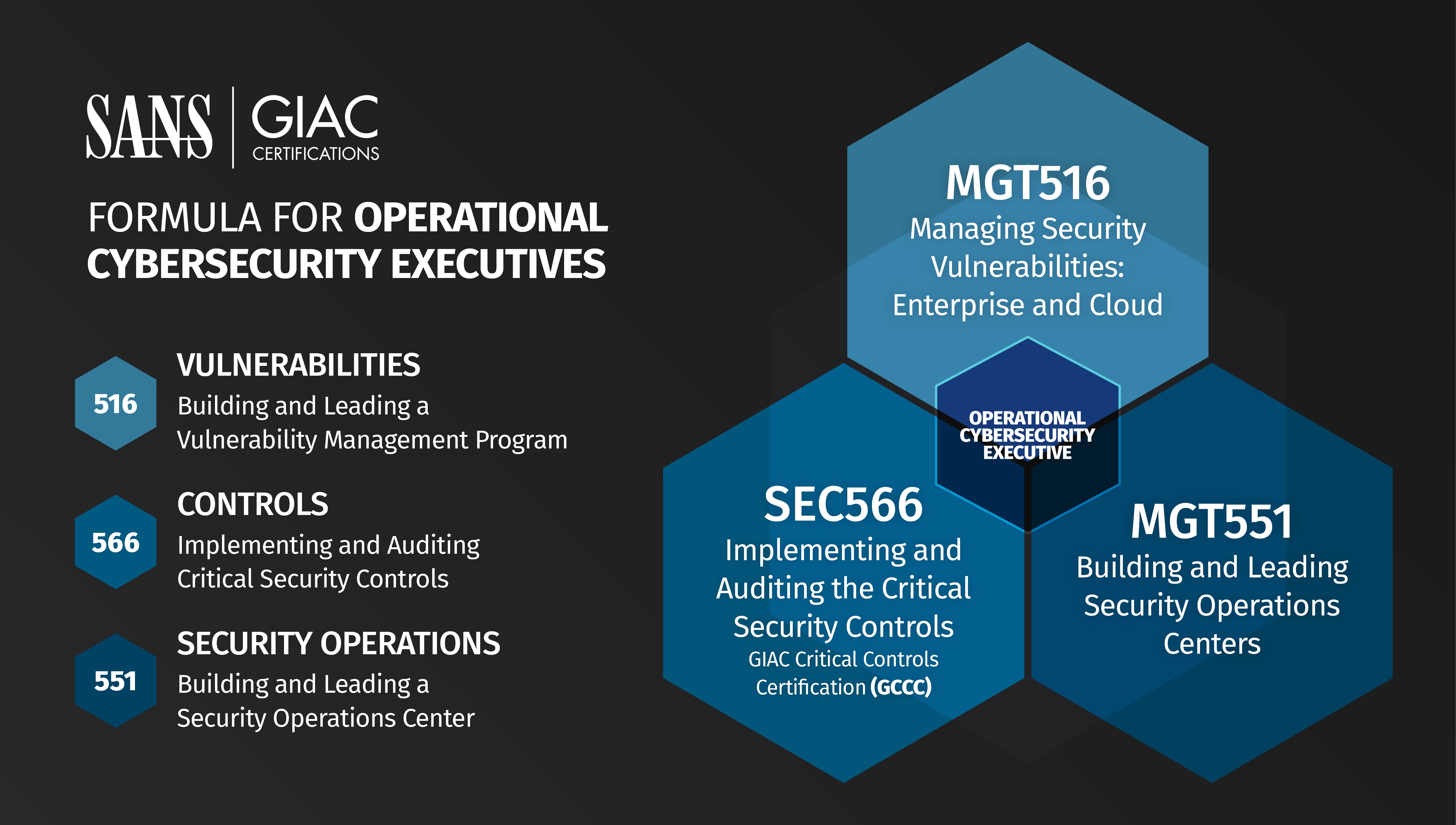
In our fourth and final webcast of our series, we talked about how the three disciplines in the Operational Leadership Series – the Critical Security Controls, Vulnerability Management, and Security Operations- can come together to get Rekt on the path to a stronger, more proactive defense. These disciplines are part of the SANS Operational Leadership Triad:
As we’ll see in this post, each of these disciplines provides a key element of the kind of defense that Rekt must now build in the aftermath of a major breach. We will also see that while each discipline represents a potentially massive undertaking in terms of time and investment, there are things we can do to build out basic capabilities we can expand and improve as Rekt’s new security program matures.
Having discussed how each of these disciplines could have positioned Rekt Casino to defend itself more effectively, we can now look at how implementing all three in concert forms a more robust foundation upon which we can build a proactive defense.
From a SEC566 perspective, implementing the Critical Security Controls would have:
A strong defense starts with the right technical controls. The goal is to gain as much situational awareness as possible, prevent as many attacks as possible, and detect the things we cannot and did not prevent. The Critical Security Controls are an effective security framework because they are based on actual attacks launched regularly against networks. Priority is given to Controls that (1) mitigate known attacks (2) address a wide variety of attacks, and (3) identify and stop attackers early in the compromise cycle.
From a MGT516 perspective, enterprise vulnerability management would have:
By understanding common issues and how to solve them, Rekt Casino will be better prepared to meet the challenges ahead and guide its IT teams and the broader organization to successfully treat vulnerabilities. The approach taken in MGT516 aligns to other modernization efforts Rekt is likely to take in the near future as it evaluates expansion into the cloud or implementing new processes like DevOps.
From a MGT551 perspective, a security operations center would have:
Information technology is so tightly woven into the fabric of modern business that cyber risk has become business risk, and this has certainly proven true for Rekt Casino. A security operations team analyzing telemetry from across the environment that includes control data and vulnerability information can be the difference between a temporary disruption and a massive business loss.
Each of these disciplines represent significant investments Rekt Casino, or any other organization, must make to be more resistant to attack. But without some capability in each of these disciplines, our operational defense doesn’t have the whole picture. Strong operational leadership in each of these three key disciplines will provide a robust and flexible starting point for a more proactive defense. More importantly, that defense will be focused on Rekt’s unique business and risk profile with controls and monitoring that prioritizes the biggest gains first.
For critical security controls, there are many sources of inventory data and some of the basic capabilities within the control library. Use a spreadsheet or data warehouse, engage with your IT management teams, and maximize the data to which you already have access to make as much progress as possible before turning to more significant new investments.
In vulnerability management, getting as much coverage as possible is one of the earliest and most important goals, and the biggest challenge – using a combination of tools at the network and host layers, the right access, and the right technical analysis of the data, organizations like Rekt Casino can build complete inventories of both hardware and software. This effort isn’t wholly reliant on major commercial scanning tools and may be supplemented by configuration management and patch management efforts.
In security operations, use existing frameworks like MITRE’s ATT&CK matrix to define threats facing your organization in common terms and prioritize your preventative controls and monitoring accordingly. Revisit the profile you have built often to update it based on new controls, vulnerabilities, and attacks you have observed, and share those insights with the other security functions so that they too can adjust and improve. Look to the risk appetite of your organization to strike the right balance between preventative controls and more passive, detection-oriented controls. Strive for prevention but do not compromise on detection!
Once we deploy basic capabilities in each of these areas, we have a baseline on which to grow and improve. Security is a process, not a state of being, and as we have followed Rekt Casino on their journey from breach to recovery to improvement we can now look to our own organizations to undertake the same initiatives. The SANS Operational Leadership Triad provides three entry points for this journey, so pick the one that is right for you.
Mark Orlando is a SANS Associate Instructor, co-author MGT551: Building and Leading Security Operations Centers, instructor for SEC450: Blue Team Fundamentals: Security Operations and Analysis, and the Co-Founder and CEO of Bionic Cyber. Prior to Bionic, Mark built, assessed, and managed security teams at the Pentagon, the White House, the Department of Energy, and numerous Fortune 500 clients. Mark has presented on security operations and assessment at DefCon's Blue Team Village, the Institute for Applied Network Security (IANS) Forum, BSidesDC, and the RSA Conference and has been quoted in the New York Times, the Washington Post, Forbes, and many other publications. He holds a Bachelor's Degree in Advanced Information Technology from George Mason University and served in the US Marine Corps as an Artillery Non-Commissioned Officer.


Mark Orlando brings extensive cybersecurity leadership experience from the Pentagon, White House, and Fortune 500 sectors. As Bionic Cyber's CEO, he's a respected security operations expert with military and academic credentials.
Read more about Mark Orlando