SEC536: Adversarial AI - Penetration Testing AI Systems


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact Us38% of compromises to ICS environments in 2023 come from IT networks that allow threats to traverse into ICS networks.


Read the previous blogs in this series:
With my firm ICS Defense Force, I perform industrial control system (ICS) security assessments, incident response tasks, and incident response tabletop exercises across multiple critical infrastructure sectors, globally. In fact, I’ve recently conducted these projects for the oil and gas, water management, and electric power sectors in the Gulf region. This practical field experience allows me to meet with security teams, engineering staff, and those leading the charge of cybersecurity risk management and defense. Getting to go onsite also reminds everybody that while in the field, safety is number one. Cybersecurity supports safety.
Teaching cybersecurity best practices for industrial safety instrumented systems commonly found in the Gulf region’s oil and gas sector. Safety is always first in ICS environments. Security supports safety, not the other way around.
25% of survey respondents from the 2023 SANS ICS Cybersecurity survey consider the current cybersecurity threats against ICS as severe/critical. Proactive control system cyber defense requires dedicated ICS tactical security teams with engineering knowledge to preserve safety of ICS and operational technology (OT) operations. Details of the ICS threat landscape in the Gulf region and common ICS security challenges, can be further reviewed in Blog #1 - Industrial Control System Cyber Threats and the Gulf Region.
38% of compromises to ICS environments in 2023 come from compromises in IT networks that allow threats to traverse into ICS networks for engineering system specific attacks. Such attacks can lead to losing view and control of engineering operations. ICS cybersecurity practitioners in the Gulf region are reminded to focus on proper ICS network segmentation by adding security to the Purdue aligned with the SANS ICS410 SCADA network architecture. Additional focus on the deployment of ICS network visibility and specific location for ICS network traffic is also required. Further details on this topic can be found here.
This blog focuses on those leading the change in managing ICS/OT cybersecurity risk and leading the ICS cybersecurity practitioners in the region.
Organizations relying exclusively on reactive strategies experience a significant delay in safeguarding critical infrastructure against adversaries equipped with the technical capability and motives to disrupt and introduce safety risks in engineering environments. A reactive ICS cybersecurity program poses an obvious potential threat to individual safety, particularly when adversaries employ sophisticated techniques like living off the land attacks.

To reduce such high risk, ICS/OT risk managers should request their technical teams thoroughly examine all access routes from IT network(s) and the Internet into/out of the ICS networks at all segments or Purdue Levels. This assessment can be carried out by scrutinizing access control lists on ICS perimeter firewalls and monitoring for all remote connections both entering and exiting the ICS. As part of this risk reduction effort, it is critical to ensure multi factor authentication (MFA) is enabled and strictly enforced on all network pathways, including access from any vendor support and IT network into the ICS network(s).
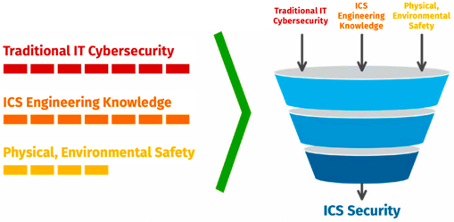
The fundamental differences between IT and ICS/OT are the driving force behind varied cybersecurity design, approaches to security assessments, understanding of risk surfaces, safety protocols, strategic considerations, support systems, tactical defense controls, and practices in responding to cyber incidents. It is crucial to recognize that employing standard cyber incident remediation actions developed for IT business systems may prove ineffective and even lead to disastrous outcomes when applied to ICS cyber incidents. This emphasizes the need for prior thoughtful planning tailored to operational ICS scenarios and using dedicated skillsets and tools.
Trained ICS cybersecurity staff understand the nuances between traditional IT and ICS/OT security, risk, and controls. As ICS risk leaders work to build their ICS security teams, they will do well to ensure their team has training and experience in the following skills:
As cybersecurity leaders in the Gulf region know, the initial tier of the comprehensive defense in depth approach for ICSs is comprised of policies, procedures, and awareness. Here, ICS-specific awareness denotes the cultivation of a cybersecurity-conscious culture within ICS operators, engineers, and facility stakeholders, that puts safety first. The significance of ICS security awareness and prioritization of safety cannot be overstated as it plays a pivotal role in protecting vital infrastructure across various ICS sectors and regions. It forms the foundation of an effective defense in depth strategy for ICS which ICS cybersecurity leaders are expected and responsible to deploy, maintain, and mature. This alignment strengthens resilience against a spectrum of risks, encompassing not only physical accidents but also the evolving landscape of digital threats in industrial environments, all while prioritizing the safety of people above all.
Those responsible for ICS/OT cybersecurity in the Gulf region can have their technical teams leverage the SANS Five ICS Cybersecurity Critical Controls, listed below.
1. ICS-Specific Incident Response
2. Defensible Control System Network Architecture
3. ICS Network Visibility and Monitoring
4. Secure Remote Access
5. Risk Based Vulnerability Management
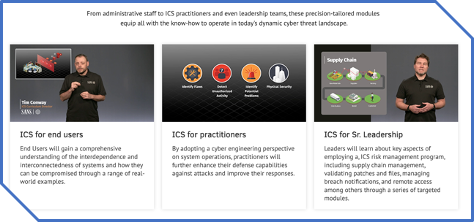
ICS418: ICS Security Essentials for Managers helps build critical infrastructure teams and leaders. This course empowers those stepping into an ICS leadership role for the first time, those leading IT security now also tasked with ICS security, and those stepping up to take the charge to manage cybersecurity risk from inside engineering departments.
The ICS threat landscape continues to rapidly change with brazen attempts by adversaries to cause disruption, destruction, and impacts to safety. This is evident with the discovery of increased targeting of critical infrastructure with ransomware like the recent ICS-specific scalable attack framework known as PIPEDREAM and attacks on Gulf region-specific oil and gas safety systems using the TRISIS ICS malware.
Mature facilities are embracing the differences in IT and ICS/OT. They do so by deploying specific ICS-aware technology for ICS-protocol aware network detections and investing in a continued effort to train their cybersecurity defenders in ICS/OT skills. They position their security and engineering teams to ensure they are prepared for active defense and ready to perform industrial-grade incident response to maintain the safety and reliability of their critical infrastructure.


Dean Parsons, CEO of ICS Defense Force, teaches ICS515 and co-authors ICS418, emphasizing ICS-specific detection, incident response, and security programs that support OT operations—aligning practitioners and leaders on clear, defensible action.
Read more about Dean Parsons