SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact Us
Whether you are a systems administrator performing regular threat hunting on your network, or you are an analyst examining a system after the smoke of an incident has cleared, Windows Defender’s DetectionHistory logs give an excellent look into what (and who) has been marked as potentially malicious. DetectionHistory Parser, or DHParser, takes data which previously only had limited availability on live systems, into an expanded dataset available for offline viewing.
A Quick Rundown on Windows DetectionHistory Logging
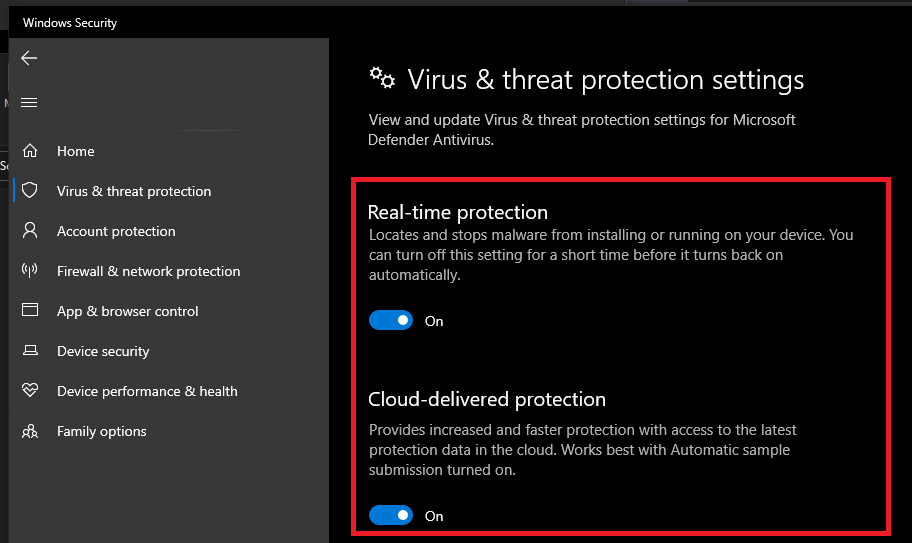
DetectionHistory files may be created and found on, at the very least, Windows 10 systems. The creation of these files is an after-product of Windows Defender's real-time protection (RTP) blocking threats, such as Potentially Unwanted Applications (PUAs), viruses, worms, trojans, etc. To block threats and generate DetectionHistory files, RTP must be turned on in the Windows Security app, under Windows Security > Virus and Threat Protection > Virus and Threat Protection Settings:
When a threat is detected, the user is presented first with a notification that Windows Defender has received a hit. A sample notification of what one would see is provided below:
The user’s decision to run this .exe or not has no impact on the creation of the DetectionHistory file. At this point, Windows Defender places a DetectionHistory binary file under [root]\ProgramData\Microsoft\Windows Defender\Scans\History\Service\ DetectionHistory\[numbered folder]\, where the name of the file is Windows’ generated DetectionID of the event. As long as the file exists in this directory, Windows Security recognizes it, and displays a few details in the "Protection History" tab. This can be found under Windows Security > Virus and Threat Protection > Current Threats/Protection History. If this DetectionHistory file shown here is deleted, the Windows Security blurb disappears along with it:
A great resource for attempting to generate these notifications on your own system can be found here. Included are benign PUA and malware files designed to set off antivirus software as a test.
DHParser Collections: How Is This Helpful?
As DFIR professionals, there are more resources at our disposal than ever before to deliver case findings to clients. However, there is more still that is obscured in mystery by binary files scattered across Windows, whose structure remains unknown. DetectionHistory files take this form as well, containing loads of unencrypted data about threats that once existed (or still exist) on a network. Because a binary file’s structure is generally unique to its purpose, specialized tools such as DHParser are created to iterate over the file structure and return its contents as human readable data.
Typical usage of dhparser.exe
Not only does DHParser return meaningful, analysis-ready JSON data, but it can also recursively search a directory on your system for DetectionHistory files, processing each one found in the same manner. Getting results takes only a few seconds, and the various data points could be easily linked to other indicators of compromise in your investigations.
Since DHParser’s capabilities are fully offline, running the tool against a mounted logical image as part of a forensic triage becomes trivial. DHParser requires read access to the directory being searched for DetectionHistory files, as other file parsing applications do. As [root]\ProgramData\Microsoft\Windows Defender\ often is protected, you can ensure DHParser has access by copying the DetectionHistory directory out of your image or live system, onto your desktop.
Example of a collection generated by dhparser.exe
As you can see, not only are we given the threat name (Trojan/ThreatTrackingThreatName), malicious file location (file), and detection timestamp (ThreatTrackingStartTime), but even file hashes for the malicious file (ThreatTrackingSha256, ThreatTrackingMD5), and the parent process (SpawningProcessName) responsible for spinning up the threat in question. The given hashes could be run against a list of known bad file hashes, for a quick win in discovering which detections from Windows Defender are truly malicious. This list of fields above is not exhaustive, as other threat types include more types of data, including registry keys (regkey, uninstall) for potentially malicious applications (PUAs).
DetectionHistory files also update as the given user responds to the threat (quarantines, removes, allows, etc.) with a ThreatStatusID. In certain cases, especially those involving insider threats, a ThreatStatus showing that a user allowed (or restored) a system threat would be critical to the timeline of an incident. More information is available for each ThreatStatus on Microsoft's MSFT_MpThreatDetection class documentation.
Conclusion
DHParser is an excellent way to gather more complete information on the nature of threats picked up by Windows’ native AV software. Hopefully, the brief introduction to the DetectionHistory artifact has inspired you to dig deeper into what data Windows Defender’s logs can offer to DFIR professionals. If you are interested in the more technical aspects of the DetectionHistory binary file structure, I’ve included a deeper dive on the GitHub repo for DHParser. Happy Hunting!


Launched in 1989 as a cooperative for information security thought leadership, it is SANS’ ongoing mission to empower cybersecurity professionals with the practical skills and knowledge they need to make our world a safer place.
Read more about SANS Institute