SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsBusiness Security Strategy, Policy, and Leadership Gone Wrong

This is Part 1 of 4. Read the other parts here:
In the Fall of 2020, I wrote a 3-part blog post about how to build a security program in a post breach scenario in a fictional organization called Rekt Casino. You can read those posts starting here. This blog post is based on the REKT Casino Hack Assessment: Transformational webcast series, which you can view starting here.

To summarize what happened: Rekt Casino suffered a ransomware attack that resulted in a breach. The Ransomware came in over email due to no spam filtering, phishing or malware protections on the email server.
The initial malware was able to beacon out to the attackers because there were no outbound firewall rules. Memory dumps showed the attackers were using PSEXEC, PowerShell and an unknown executable. RDP connection were observed taking place on the network using the domain admin account – domain admin had been compromised.
Things were going really wrong at Rekt Casino. This post is about how the breach could have prevented by utilizing the tools and techniques covered in MGT514 Security Strategic Planning, Policy, and Leadership if a security program was in place before the ransomware incident.
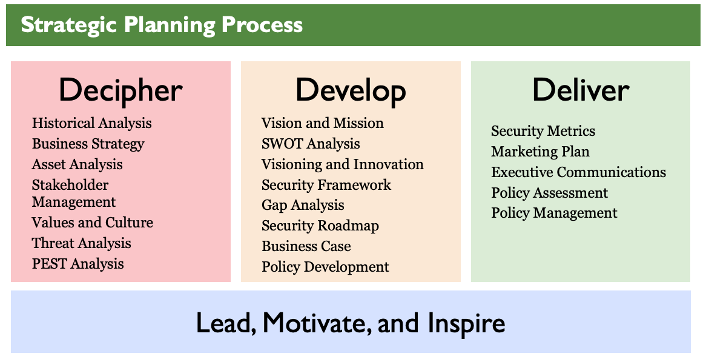
If you look at the tools and techniques, I used in the Rekt Casino blog series, the same approach can be used to build a security program before you experience a breach. Tools like the PEST Analysis, SWOT Analysis, Gap Analysis, and Security Roadmap are all activities you should be engaging in as you build your strategic plan for security. I’m not going to cover those again in this blog post.
What I’ll cover in this blog post is what goes into the strategic planning process when you aren’t forced into a reactive approach to security. This involves the new school approach to security which takes a more wholistic approach and includes IT Security, regulatory, compliance legal, privacy, and risk management. This requires a security leader to be business savvy and understand enterprise risk management and not just the technology aspect of security.
I’ll approach this blog post as if I were the newly hired CISO (Chief Executive Security Officer) to build a security program at Rekt Casino long before the ransomware incident and resulting breach.
These stakeholders and business leaders at Rekt Casino have strategic business objectives that I need to understand. One of the most important parts of creating a strategic plan for security is understanding the business objectives and business strategy.
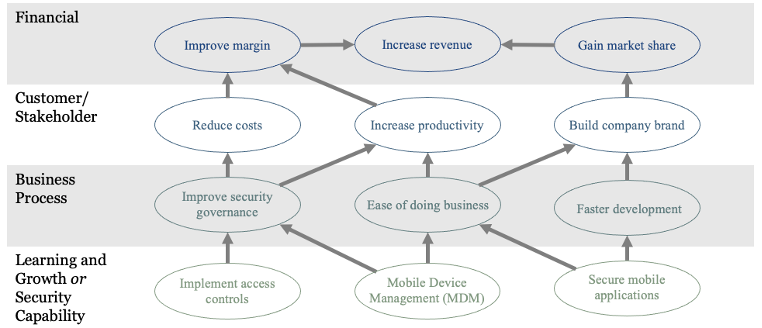
I can visualize that with a slide like the image above. This slide shows how security contributes to and enables the strategic business objectives. This is an approach that executives can understand. Let’s assume that Rekt casino has a strategic objective to roll out a mobile application for clients to interact with the casino.
At the bottom of the diagram, they can see what security does for the organization. Those actions contribute to the business processes, which in turn affect customer and stakeholder satisfaction, and ultimately impact the financial objectives of the organization. That top line is what the executives and business leaders are concerned about in a for profit organization.

The previous blog post series didn’t talk about how important it is to have a visioning and innovation mind set during the strategic planning process.
Security needs to be an innovator for the business. I need to think about what the business and security might look like in the future. For example, the casino of the future might be all virtual. What security challenges will we face? How will security be implemented? What legal, compliance, and regulatory changes will be in place? How can security be a differentiator for the business from that perspective?
Security has a short shelf life. We can’t just maintain what we are doing today and expect it to be as effective in a year or longer. We need to look for ways to get more from what we have, scale out as the business grows, and imagine what security will look like in the future.
Without that visioning and innovation mind set, we most likely build a tactical plan and not a strategic plan.

As the CISO at Rekt Casino, my job is to enact change. Policy is one of the most powerful tools I have at my disposal to steer the organization in a certain direction. Enacting change is not a fast process – every organization has a pace at which it accepts change.
As I decipher the organization, I’m going to be meeting with department managers, business leaders, executives, and many of their direct reports. All these meetings and discussion will help me identify what security changes need to take place at Rekt Casino. CISO is very much a social role as much as it is a security leadership and technical role.
There’s no security program here and there’s a lot of change that needs to take place. I’m not going to be able to change everything I want in the first year, the second year, or maybe even the third year. Changing culture is slow process and can take a number of years to accomplish. Policy is going to be one of my main approaches to laying the foundation for the strategic plan for security.
Policy is the best security no money can buy.
Let me explain:
Policy is a preventive administrative control that can be more effective than technical controls in some cases. Policies start with risk assessments to determine what polices you need in place.
Cost: The time it takes to risk assess and create the appropriate policies.
I need policies in order to enact change. I also need the appropriate technical controls, staff, and hardware, and that takes budget.
I’m a new CISO, I might not get that budget at first. The executives aren’t going to give me the keys to the kingdom, a blank check, or start throwing money at me when I walk in the door on my first day. I’ll have to earn the trust and confidence of the executive team and business leaders before I can expect a larger budget allocation.
Until then, policy is the tool I’m going to start the groundwork with. I’m not going to wait until bad things happen to start creating the corresponding policies. By using the risk assessment approach combined with tabletop exercises, I can identify what policies and procedures the organization is deficient in.
For example, this risk assessment for Cloud Computing Services in Rekt Casino to illustrate the point:
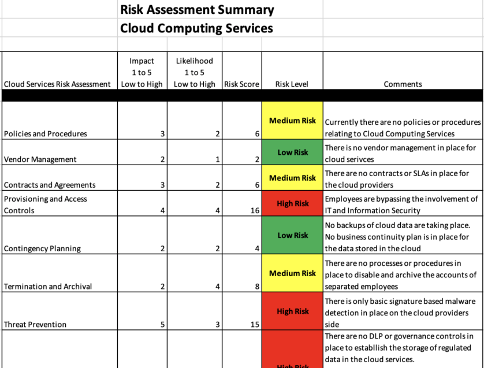
Just glancing at this I can immediately determine that Rekt Casino needs an Access Control and Threat Prevention policy for cloud services. (the numbers are example data and not intended to be precise in this fictional scenario).
My approach to creating policies is with security and compliance baked in by design.
All the policies I create will include the regulations, laws, and compliance frameworks that Rekt Casino is subject to. I’ll also include any SLAs we must meet, and any contractual obligations we have.
In this case I know about MICS (Minimum Internal Control Standards), but then there's PCI, GPDR, and any associated laws that casinos must follow.
As an information security leader, I can't possibly keep up with all these laws and regulations and that's why it's important to work with the organizations' risk and legal department as these policies are created.
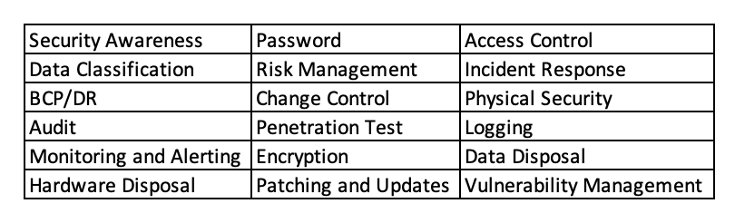
This image about is an example of baseline of policies for a typical organization.
I might start here before starting the risk assessment process just as a reminder of what I should be looking for. The next challenge is: Which policies do I implement first? That’s an easy question to answer, I’ll implement the policies that reduce the most risk first.
Keep in mind that I won’t just sit down at my desk and start creating these policies – that’s the wrong approach. I’ll meet with other business leaders in the organization to understand the impact and context for each needed policy.
Another approach is to create a policy steering committee where these policies can be discussed and developed for final approval. The next step is to socialize these new policies with the organization. That can be done through newsletters, company meetings, annual policy reviews, posters, and over email. There are many ways I can socialize the policies within the organization.
In the blog post series, I didn’t talk about the importance of security metrics.
Delivering on the strategic plan for security means that I have to communicate the state of the security to the executives, business leaders, and other stakeholders in a language they can understand. Metrics is a universally understood language from this perspective.
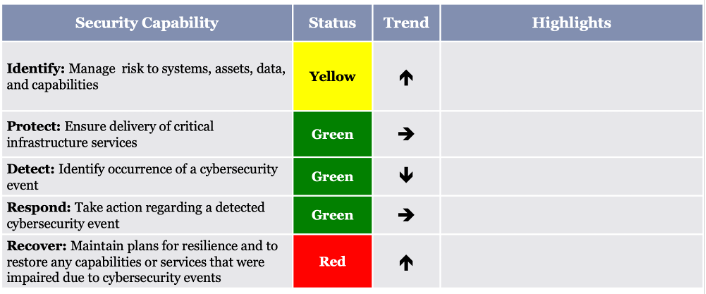
Metrics programs can’t be built in a few weeks or even a few months. This process may take a few years. Since this is the early stage of the program, I need a simple metrics dashboard that’s easy to understand and communicates the state of security.
This dashboard maps the 5 functions (Identify, Detect, Respond, and Recover) of the NIST CSF (NIST Cyber Security Framework) to three status measures, Red, Yellow, and Green, and shows the trend for that function.
Over time as the metrics program matures, KPIs, balanced score cards, and metrics dashboard will be implemented and socialized with the organization.

I need to market for the security program. The reason for this is that security is competing with all the other departments in the organization for time, attention and budget – Security needs a way to stand out.
Part of the marketing strategy for security is build brand visibility. The brand for security at Rekt Casino consists of security’s capabilities, products, services, and initiatives.
For example, raising awareness within the organization that the security team at Rekt Casino can provide secure email and cloud storage, helps those in the organization realize they have access to these services without seeking them out on their own. That marketing effort helps prevent Shadow IT in the organization.
Security also needs to market for initiatives they are undertaking to raise organizational awareness about upcoming changes they might be impacted by. Security also needs to market for employee retention, recruiting, to create and maintain relationships with customers, vendors, and those within the organization.

Leadership and Management Competencies in MGT514 gets into:
Leading teams and people are one of the biggest challenges we have in my opinion.
We have all these tools for deciphering and understanding security like PEST, SWOT, risk assessments, and roadmaps, but none of these tools help you figure out people or your team.
You can’t get leadership and management competencies from a vendor, or event take a class and walk away a leader afterwards. Leadership and management competencies are developed over time and take conscious and consistent effort.
It’s important for me to keep the team engaged and stay engaged with the team.
Some of the tools that I can use to do this is include personality assessments, team building exercises, management training for the team members, and make sure that they have a good work/life balance.
I also need to allow my team to have input for the strategic plan – this makes them feel valued, heard, and gives them a stake in the organization's security. I’m just coming in as a new CISO to Rekt Casino, they’ve been here longer, and their input is going to be valuable to the success of the program.
At this point I need to keep a few leadership concepts in mind:

With the strategic plan for security in place and now having an effective security program, what happens when that ransomware email comes in?
Security is now a priority, we have policies and procedures, technical controls are implemented, and incident response is operationalized.
That ransomware email is identified due to the security awareness program, and in fact it was forwarded to the security team for analysis and confirmation. What’s the value of this to the organization?
Many security programs do this every day, and nothing is ever mentioned.
If this is your security program, you are missing out on an opportunity.
When we block ransomware, phishing emails, and other malware, that has a value to it.
Security needs to start calling more attention to this and taking credit for when things go right.
To close out this post, there was a question in the webinar that I stated I would follow up on here:
Q: Can you elaborate the mapping between risk assessment, NIST-CSF, CIS Controls, Threat Modeling/PEST, CMMI, and deriving key strategic planning key metrics?
A: The mapping is going to depend on the state and maturity of security program. To break it down into the context of Rekt Casino, I would approach it like this:
1. Start with a PEST analysis to determine the threats to the business that security needs to be aware of.
2. Use the CMMI to determine where the security program is today and what changes are needed to mature the security program.
3. Adopt the NIST CSF and CIS Controls as the framework for building the security program.
4. Perform risk assessments (includes threat modeling) to develop the policies, policies, procedures, guidelines, and baselines.
The risk assessment process can also be used to determine which aspects of the NIST CSF and CIS Controls to implement in the early stages as well.
5. Periodically review the milestones of the security program to determine the state of maturity.
Images You can create metrics based on the state of the security program which shows progression and maturity. That would be a good metric for the security team executives and board members.
More strategic metrics can be collected to align with strategic business objectives. For example, Rekt Casino has a strategic plan to reduce the number of internet facing vulnerabilities. Metrics could be collected to show the remediation trend, number of critical business systems with vulnerabilities, and remediation velocity as a simple approach.
Joe Sullivan has over 20 years of experience in information security. Joe is Principal Consultant at Rural Sourcing in Oklahoma City where he manages and develops the security consulting services and the teams that provide them. Over his career Joe has worked in incident response, penetration testing, systems administration, network architecture, forensics, and is a private investigator specializing in computer crime investigations. Joe teaches MGT514: Security Strategic Planning, Policy, and Leadership. Learn more about Joe here.


Joe Sullivan has over 20 years of experience in information security and is a senior security consultant for TrustedSec. Joe teaches LDR514: Security Strategic Planning, Policy, and Leadership.
Read more about Joe Sullivan