SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsGIAC Response and Industrial Defense (GRID) is a must-have certification for ICS/SCADA/OT professionals.


One of our main goals as SANS Certified Instructors is to deliver course content in a way that ensures maximum retention of knowledge and inject as much real-world experience as possible. This makes the content even more applicable to what’s happening in the industry right now, providing practical security takeaways that are immediately actionable.
Beyond those core goals, it is critical to prepare students for the GIAC Certification associated with ICS515. This helps professionals demonstrate their knowledge and gives confidence to team supervisors that they have team members with the appropriate skillsets to carry out security and defensive tasks with confidence.
When teaching the Industrial Control Systems Security course ICS515: ICS Visibility, Detection, and Response, one of the most frequently asked questions I get is: “Should I take the GIAC exam and become GRID-certified?”
GIAC Response and Industrial Defense (GRID) is a must-have certification for ICS/SCADA/OT professionals who want to demonstrate their knowledge of Active Cyber Defense strategies specific to industrial control system (ICS) networks and environments. It is common for professionals working or looking to work or consult in these areas to earn their GRID certification. The graph below shows some of the critical roles supported by the GRID.

ICS Incident Response Team Leads, Members - Those who know the control systems and directly execute the specific ICS incident response steps, which go beyond traditional IT cyber security incident response steps.
ICS and Operations Technology Security Personnel - Engineering or other staff who design control network architecture and integrate systems into the control environment for secure industrial protocol communications, with appropriate network segmentation and reliability.
IT Security Professionals - Those responsible for or contributing to the safety and reliability of control system operations through security efforts focusing on the traditional components of the industrial environment.
Security Operations Center (SOC) Team Leads and Analysts - Leaders and technical analysts in control system security operations that directly review, triage and respond to cyber threats within an industrial control system network.
ICS Red Team and Penetration Testers - Those who discover the ICS risk surface and attack vectors with the purpose of identification of vulnerabilities, attack paths, and providing solutions to minimizing those cyber risks, while supporting the safety and reliability of engineering system operations.
Active Defenders - Cyber security resources who are proactively involved with control system security who preempt attacks to control networks through various vectors by understanding the control systems, protocols, and threat vectors. These resources utilize cyber threat intelligence for control systems to make changes to the environment prior to an attack or work to reduce the impact of an attack by quickly changing the nature of a threat, or the systems during an incident.
In ICS515, students will gain experience with a variety of tools specific to ICS environments, including Shodan, Security Onion, tcpdump, Wireshark, tshark, Snort, Bro, SGUIL, ELSA, Volatility, Redline, FTK Imager, PDF analyzers, and malware sandboxes, among others. Students will build a hardware Programmable Logic Controller (PLC) supplied in class, deconstruct Advanced Persistent Threat attacks through real-world scenarios from SANS Cyber City, and examine data from a Distributed Control System (DCS) environment infected with Malware. Students will be able to use the practical steps of ICS Active Cyber Defense Cycle they learn in the course as soon as they get back to work!
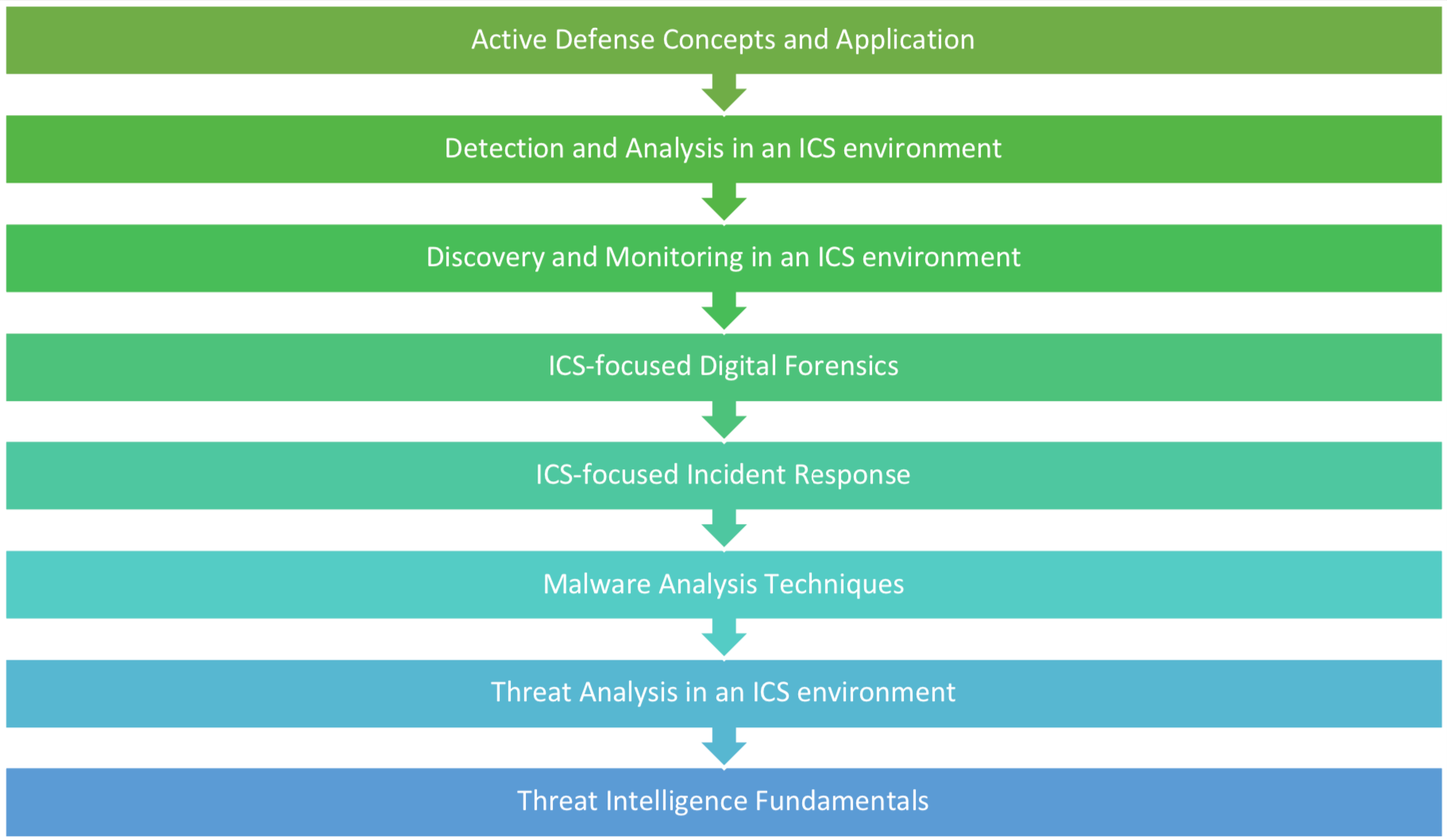
The class content will prepare students for the GRID exam. Once the course is completed, four months are allotted for additional study, including two practice exams provided through the SANS and GIAC portals. The main learning objectives of ICS515 include but are not limited to those highlighted in the graph below:
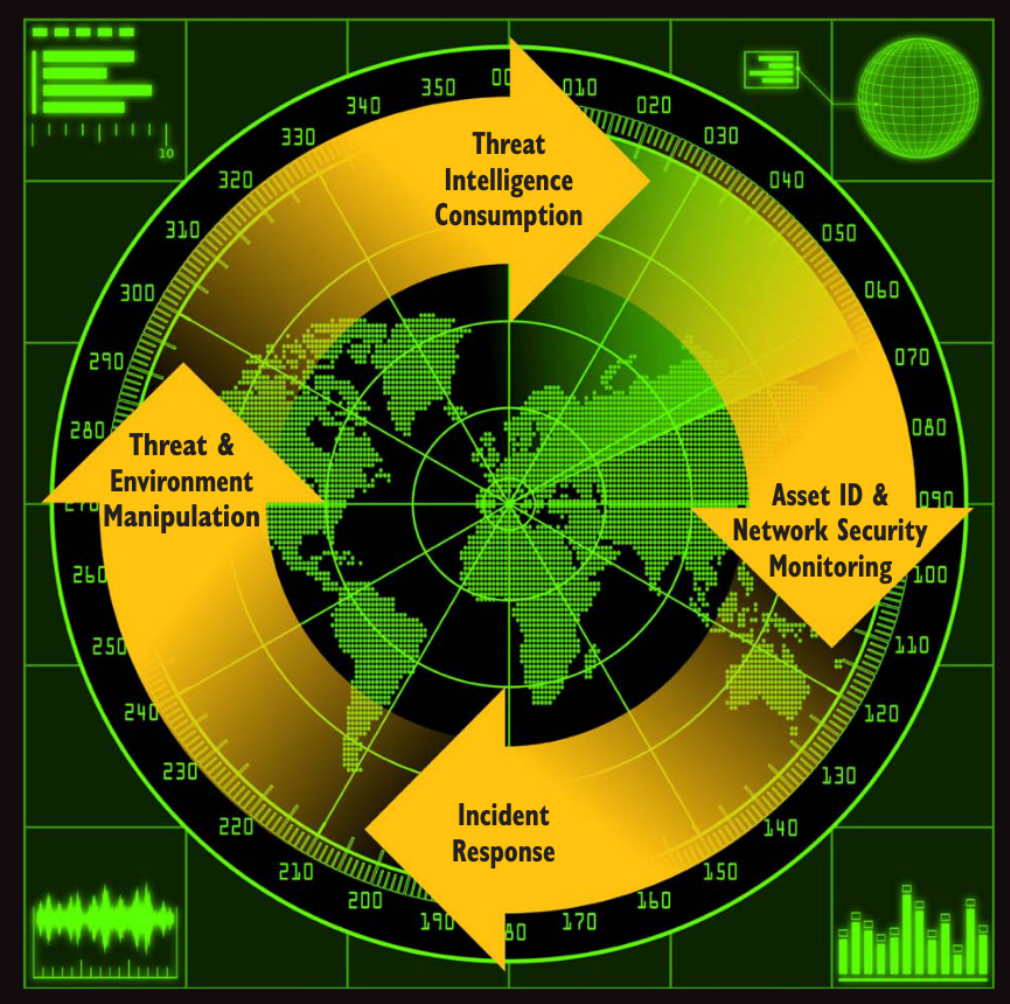
Considerable time is devoted executing and applying the phases of the ICS ACDC (Active Cyber Defense Cycle) throughout the course:
The skills obtained through ICS515 and by earning the GRID certification prepare professionals to prioritize safety when implementing active cyber defense and industrial incident response across all industrial control system sectors, including critical infrastructure, as outlined below.
Critical Infrastructure and Control System Sectors | |||
Chemical Sector | Commercial Facilities Sector | Communications Sector | Critical Manufacturing Sector |
Dams Sector | Defense Industrial Base Sector | Emergency Services Sector | Energy Sector |
Financial Services Sector | Food and Agriculture Sector | Government Facilities Sector | Healthcare and Public Health Sector |
Information Technology Sector | Nuclear Reactors, Materials, and Waste | Transportation Systems | Water and Wastewater Systems |
Interacting with control systems is commonplace, whether by flipping on a light, pumping gas, or pouring water from a tap – all daily activities in the modern world that rely on industrial control and critical infrastructure systems. Increasingly, however, adversaries have been targeting these systems, with impacts that have serious safety and environmental risks.
If you are new to ICS/OT Security or already contributing to a program, the GRID certification is for you. In a world that is seeing increasingly sophisticated and impactful industrial incidents, the GRID helps level the playing field.
GRID-certified professionals have demonstrated they have the skills to help protect this critical infrastructure that modern society now relies upon. GRID gives ICS defenders the technical and strategic skills for the Active Defense of industrial control systems.
The GRID Certification requires students to complete a one on-book proctored exam with 75 multiply-choice questions within a two-hour time limit. The minimum passing score is 74 percent. More detailed information on the GRID can be found here: https://www.giac.org/certification/response-industrial-defense-grid
As a practitioner in the ICS security community, I enjoy helping people move forward with their careers and strengthen their skills and passion to protect ICS critical infrastructure. ICS515 features tons of hands-on and real-world technical exercises and scenarios. Students will collect data from an intrusion into SANS Cyber City as well as from a Distributed Control System infected with malware. And there’s more! Students will dissect network captures from a variety of ICS facilities, including a system they’ll build and run in the class. Spoiler alert – there will be attacks and malware affecting the ICS that will drive us to industrial incident response specific to ICS networks and systems.
Join me in class as I guide you through the content, help prepare you for your GRID Certification, and share key knowledge from the field drawing on experiences across electric power systems, oil & gas refining, storage, distribution, manufacturing, and ICS system assessments. We will deconstruct modern ICS cyber-attacks, identify and counter threats, and use ICS incident response procedures to maintain the safety and reliability of ICS operations.
I am a SANS Certified ICS Instructor and the sixth person in the world to earn the GIAC GRID – I am GRID Analyst #6.



Dean Parsons, CEO of ICS Defense Force, teaches ICS515 and co-authors ICS418, emphasizing ICS-specific detection, incident response, and security programs that support OT operations—aligning practitioners and leaders on clear, defensible action.
Read more about Dean Parsons