SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsTake a look at some of the most significant findings on the role of humans in breaches.

The Verizon Data Breach Incident Report (VZ DBIR) is one of the industry’s most respected annual security reports. For over fifteen years, the Verizon team has been publishing its data-driven report on the top risks organizations face around the world. What makes this report so valuable is its vendor-neutral approach, global data set, and the way in which the report analyzes all aspects of risk, to including not only deliberate cyber threat actors but other risks such as physical and human error.
The DBIR is unique in how it breaks down and categorizes risks, including by threat actors and their actions. This is a highly actionable document that I recommend everyone make part of their reading lists. With that said, let’s dive in and see what the 2023 report has to offer us. As always, I will be looking at this report from the human perspective.
.jpg)
I always like to start with summarizing the findings. For this year we see in Figure 6 that 74% of all breaches involve the human element, demonstrating that people continue to play a key role in the security of organizations. However, this percentage has dropped almost 10% from last year. Several possible reasons for this drop include that we, the security community, are getting better at securing the human element and / or cyber threat actors are starting to exploit technical vulnerabilities more actively (perhaps a combination of both). In addition, the technical exploit vulnerability category may have been skewed this year by the active exploitation of the Log4j vulnerability (which the report calls out). In any case, people continue to play a huge role in breaches, and the security of organizations, globally.
In Figure 7, we see the top three ways cyber threat actors are getting into organizations: credentials, phishing and vulnerability exploiting. Notably, these are the same top findings from the past three years. However, I’m intrigued to see that Phishing seems to be much lower percentage-wise compared to credential / account takeover.
After chatting with the DBIR team at Verizon they explained to me that a huge percentage of credential stealing indeed happens through phishing, but the DBIR team often cannot prove how cyber threat actors obtain the credentials in the first place.
Long story short, just as in the past three years, when it comes to human security, focus on:
Strong authentication: Long, unique passwords and MFA
Phishing: I would throw Vishing / Smishing in there also
Patched systems: for individuals, enable automatic updating
These are the same top risks, and behaviors, for the past four years.
The vast majority of breaches are driven by external threat actors (83%) as opposed to internal threat actors. In addition, the bulk of those threat actors are financially motivated, primarily organized crime.
Phishing continues to be one of the biggest drivers of breaches, but what I found interesting in this year’s data set is that almost 50% of successful phishing incidents were BEC (Business Email Compromise) / CEO fraud imposter attacks. These types of email attacks have no malicious link or infected email attachment. Instead, these attacks are most often financially motivated and aim to trick people into approving invoices, payments, or change of bank account information. Their goal is purely to steal money. The reason I emphasize this is we often hear of ransomware in the news, since organizations are required to go public when a ransomware incident happens, but we almost never hear about BEC / CEO fraud incidents in the news since the same requirement does not exist in those cases. You must go public when your data is breached, you do not need to go public when your money is stolen.
BEC / CEO fraud emails are often the most difficult for automated security tools or people to detect, as these emails are often highly customized and have far fewer indicators in the email. In addition, recent advances in artificial intelligence have made creating these customized email attacks easier, and in almost any language the cyber attacker wants. This is why it is critical that employees strictly adhere to and follow all policies related to the approving, invoicing, and transferring of money, or modifying related financial accounts.
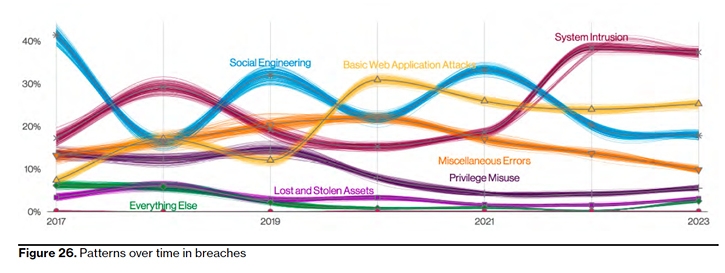
Human error accounted for roughly 10% of all breaches in this edition of the report (Figure 26). What is interesting here is the vast majority of those errors were not caused by the typical end-user worker, but rather by technical roles, specifically IT admins and developers. These are the individuals that are often working in the most technically confusing environments (including the cloud), which increases the probability of mistakes. In addition, when they do make a mistake, the impact is often far greater, as these individuals handle highly sensitive data sets. This highlights the need for more technical skills-based security training for these specialized roles. SANS Security Awareness, as an example, has for the last several years been investing in this type of training for the two audiences mentioned, Developers and IT Admins. Our recent partnership with Microsoft aims to help organizations train IT Admins at scale to address the Human Error problem.
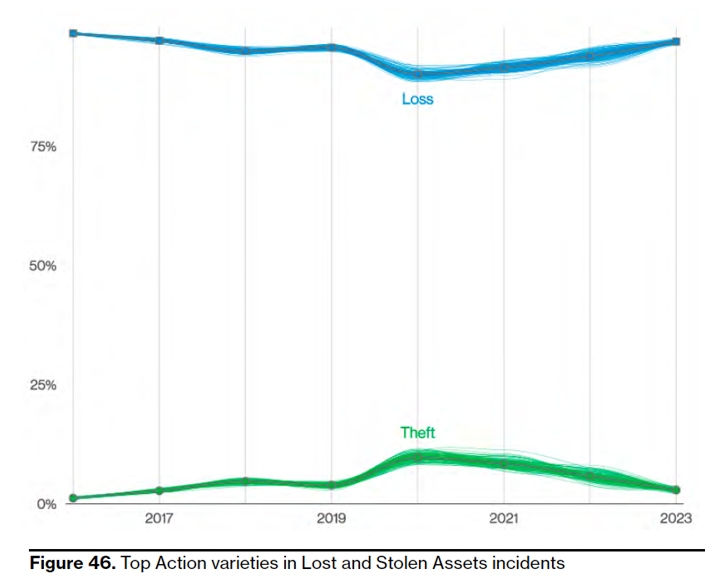
https://images.contentstack.io/v3/assets/blt36c2e63521272fdc/bltb654d6177c79e9fd/648248d4ee6549b073ccc620/SANS_-_Blog_-_Parsing_the_2023_VZ_DBIR_-_Images_-_43.jpgOne data point I always find interesting is the tracking of lost and stolen devices. While we often don’t think of this as a risk, when we lose control of a mobile device, the data on that device is at risk. This is why controls such as screen locks, encryption, and remote tracking / wiping are so important. Your mobile device is far more likely to be lost or stolen than it is to be hacked (it’s actually quite difficult to hack an actively patched and maintained mobile device). In Figure 46, we see a wonderful statistic that has been constant for years: You are ten times more likely to lose a device than have one stolen. So, when it comes to physical security, it is not the thief we should be concerned about, but the absent-minded, overwhelmed employee who is traveling.
These are by no means the only interesting or important findings in the report; these are just the ones I found most interesting. Please take the time to read this amazing resource yourself. It is easy to consume and packed full of actionable information, including many areas I have not covered in this blog, such as a breakdown of risks by industry.
To learn more about managing human risk, consider the three-day SANS LDR433 Managing Human Risk course.


Lance revolutionized cyber defense by founding the Honeynet Project. At SANS, he has empowered over 350 organizations worldwide to build resilient security cultures, transforming human risk management into a cornerstone of modern cybersecurity.
Read more about Lance Spitzner