SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsTo address NIS2 requirements, organizations must ensure they can detect and respond faster and quicker.

This is Part 4 of a multi-blog series on the new NIS2 Directive.
Organizations have for too long only focused on protecting the perimeter and the detection of compromises inside their environment. Network and Information Security Directive (NIS2) will shift the paradigm to enhanced detection of malicious activity before it becomes an incident. “Security Operations Center (SOC) leads should see the new directive as their ally,” said SANS Certified Instructor Maxim Deweerdt.
Deweerdt has taught cyber defense courses at SANS for almost ten years, both from a technical and management perspective. He specializes in building a SOC operation and has advised many organizations on this topic. He thinks the new European Union (EU) directive is good news from a SOC perspective. “The directive strengthens cybersecurity risk management measures, imposes reporting and incident reporting obligations, and outlines the potential sanctions in case of non-compliance. Those implications on liability at the board level mean there will be more attention and focus on cybersecurity and detection in particular,” said Deweerdt. “Organizations must ensure they can detect and respond faster and quicker. Hopefully, this will mean a bigger budget for SOC environments.”
SOC leads and organizations that have already started risk management programs, fall under the preceding NIS directive or are compliant with other standards and frameworks like ISO27001, shouldn’t worry too much about the implications of the NIS2 directive. “This directive is a good thing,” Deweerdt reassured. “We have been advocating cybersecurity attention on the board level for a long time. The NIS2 regulation now explicitly gives a sense of urgency to the board in the form of direct liability if they do not follow up on their responsibilities. This means that they will have to be a lot better informed.”
The strict NIS2 reporting requirements will significantly impact organizations. The requirements provide for more information sharing across a country and Europe as a whole. However, the strict prerequisites require far better detection of threats. “Under NIS2, you should be able to report any incident in your environment within 24 hours and then follow up with a more detailed report in 72 hours,” Deweerdt explained. “The faster a possible threat is detected, the better an organization can anticipate complying with the regulatory reporting requirement if it evolves into an incident.”
The directive's scope is defined in Directive (EU) 2022/2555 of the European Parliament and of the Council of 14 December 2022. NIS2 is aimed at harmonizing a common cybersecurity standard across all member states to ensure there are no weak links in the EU’s cybersecurity defenses, especially in the critical sectors where disruption could negatively impact any citizen’s life. “The objective of increasing cooperation on cybersecurity between different organizations and entities across the EU, especially within the same sector, can only contribute to a better overall cybersecurity posture,” said Deweerdt.
Any organization that conducts operations within a sector or service type specified in the directive’s annexes and meets a particular size criterium (see the Which Organizations Are Essential or Important? section below) must comply with the new rules. “Essential entities will be subject to proactive controls by authorities, with regular compliance checks and audits regardless of whether any significant incident has occurred. Important entities should only face limited reactive supervision and therefore should not face direct supervision from regulators and authorities unless a significant incident or report occurs.”
NIS2 can have some serious implications for smaller, very specialized organizations that, because of the sector in which they are active or the type of service they deliver, suddenly fall under NIS2. “They will have to go from having some cybersecurity in their environment to being in the heaviest category of NIS2. That will absolutely be a big challenge for those organizations,” stressed Deweerdt.
Not every organization, especially the smaller ones, has a SOC. “For those with a SOC, NIS2 will further double down into what they need to do anyway. For the organizations that don’t have a SOC yet, this will be an opportunity to do an evaluation on whether they already have or want to build the in-house expertise. Or they will look for partners that can take over some of these functions, like managed service providers. That is something we see quite a lot.”
NIS2 will be an ally for SOC leads, hopes Deweerdt. “To reassure all the SOC leads reading this: you’re not expected to increase your daily coffee intake," he said smiling. “If you’re a SOC lead in an organization that falls under the new regulation, then hopefully, it should be easier to pinpoint any of the visibility gaps you still have and raise them to management's attention. It should also most certainly help with focus, as the SOC is usually supposed to do a million things, even though, in essence, they should be primarily focused on detection and response. The NIS2 gives SOC leads a solid reason to ensure they can comply with the directive and have their primary job prevail again.”
However, there will also be challenges, said Deweerdt. Especially in the area of operational technology (OT) as these industrial control systems have been out of the scope of IT security teams up until now. NIS2 compliance is organization-wide and thus comprises both IT and OT security. “SOCs need to find a way to protect the operational environment or at least be able to detect when something happens there. This scope extension is not an easy one. First, IT and OT are completely different worlds. So, it’s difficult to find a governance model that works so IT people can try to detect and bring their cybersecurity knowledge into the OT space. There needs to be a knowledge transfer from the OT people on how these environments work and ensure we don’t impact any operations. I see that as a big challenge for most IT SOC environments to understand and cope with.”
Organizations need to switch their mindset when it comes to continuous monitoring. Instead of focusing too much on the perimeter, they must focus on catching adversaries before they reach their objectives, whatever those may be. “NIS2 is pushing organizations to have better detection in place,” said Deweerdt. He advises organizations to conduct a comprehensive cybersecurity gap assessment with an expert to prepare for the new directive.
“If your entity is in a country where no information has yet been published, we recommend starting to work with either the ISO27000 framework, the NIST CSF framework, or country-specific guidelines, as these can help identify your gaps against the regulatory obligations. Pay special attention to the supply chain and risk management pieces of each framework, as they are key NIS2 focuses. You should implement incident reporting mechanisms which allow you to meet reporting obligations. Most importantly, you should refer to your CISO, legal team, or any NIS2 expert to stay informed about how your country transposes the directive into national law. Preparation is key to achieving compliance by the due date and will also increase your resilience against cyber threats. It is better to start sooner than later,” Deweerdt stressed.
What Deweerdt most wishes to impresses upon his students when it comes to preparing for NIS2 is the importance of developing a personal relationship with someone at their local cybersecurity authority. “Use all the advice and information those centers have been putting out there to your advantage to get more knowledge about what the local authority expects from you if you fall under the scope of NIS2,” Deweerdt said. “Next, have a look at all the areas that it covers. Maybe you already know about gaps towards certain other security standards, so you can prioritize those and devise a plan to address them.” As a last remark, Deweerdt advised the SOC leads in his classes to know exactly what weaknesses are in their software environment and make those visible to the management. “Don’t just say you need more budget but show the gaps and possible consequences when they’re not addressed.”
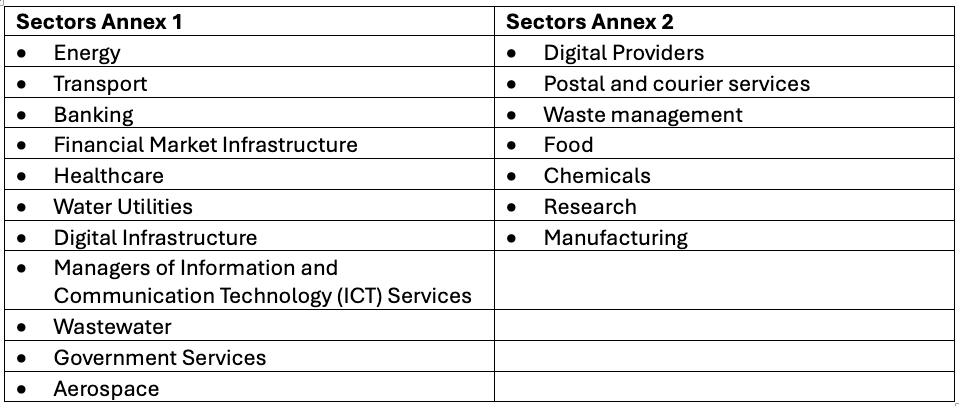
Essential entities: Large organizations operating in a sector from Annex 1 of the NIS2 Directive
Key entities: Medium-sized organizations operating in an Annex 1 sector and medium and large organizations operating in an Annex 2 sector.
An organization is considered large based on the following criteria:
An organization is considered medium-sized based on the following criteria:
In this series on NIS2, we highlight the new directive from different angles so CISOs and their organizations can gain insight into how to deal with NIS2.
Are you ready to turn NIS2 compliance from a challenge into an opportunity? Connect with SANS here for access to expertly crafted learning materials that will empower your team and ensure compliance.
As SANS maps out industry preparedness for the new EU Commission's NIS2 Directive, your insights are invaluable. Please take a moment to complete the NIS2 survey to contribute to our research. Your feedback will help us provide the guidance and resources needed for this and future directives.


With over 10 years of experience in cyber defense, Max has garnered insights spanning risk and compliance, threat hunting, incident response, and SOC operations. As a trusted advisor, he has served governments, large corporations, and businesses.
Read more about Maxim Deweerdt