SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsHow to Stay Current to Best Assess Your Cyber Applicants

Opening up a job description to the public can be a blessing and a curse. It is a great sign that your job requisition is approved and one step closer to being filled, but it also opened up the next stage of the ‘perfect applicant” search. Resumes upon resumes fly into the door, awaiting your review. “Overwhelming” does not begin to describe how many feel when there are 250 + resumes to review and find the perfect candidate for.
Drawing down from a list of 250+ to about 4-6 candidates can look daunting when many of the same attributes are present on each resume. Luckily, there are both industry agnostic and industry specific assessments to help you fish through the sea of text on a resume.
Myers-Briggs: Allows a candidate to take a questionnaire on their own that indicates psychological preferences in how they see the world. It also may distill out how they make the decisions they do. Once the candidate completes the test, they are assigned four categories: introversion or extraversion, sensing or intuition, thinking or feeling, judging or perceiving. One letter from each category is taken to produce a four-letter test result, such as "INFP".
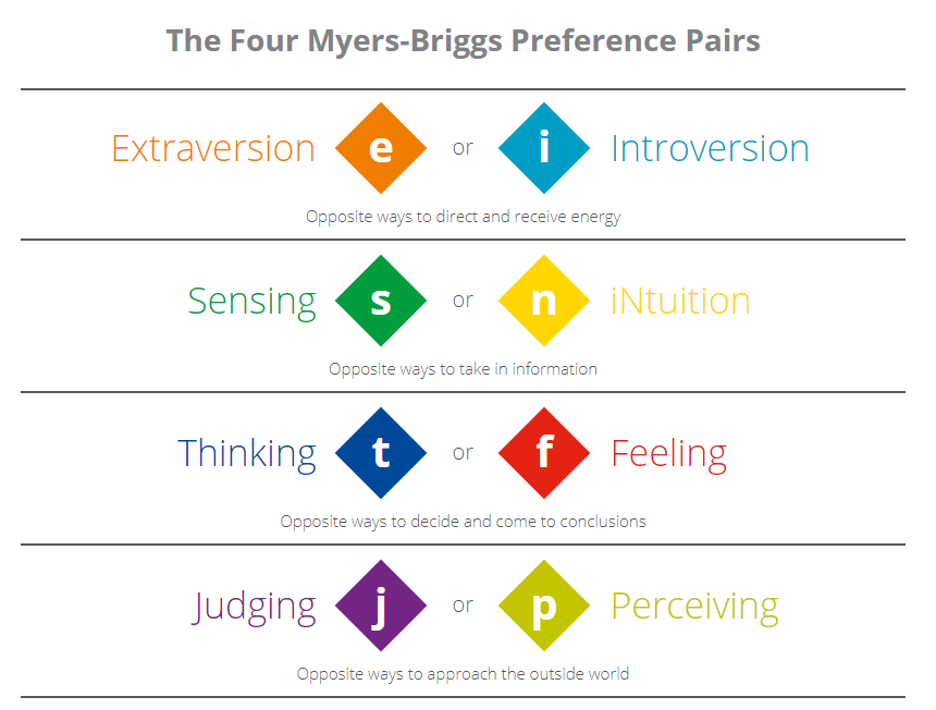
One of the best benefits of this test is one size does not fit all roles when reviewing results from Myers Briggs. Each decision maker throughout the interview process can use the results to compare to what they feel would be the best fit for a role. For example, all of the hiring decisions makers may come to a collective agreement that an individual who would best fit a security analyst role in their organization would be similar to an “ENTJ”, or a “Extraversion, Intuition, Thinking, and Judging” personality type. Personality types are very hard to capture in most resumes and an industry agnostic test like Myers Briggs gives you an opportunity to see through the hard skills and experience that are presented through most resumes. It also gives you a view into a candidate’s potential thought processes as they strategic and every day problems through their job.
Strength-Finders (CliftonStrengths) :
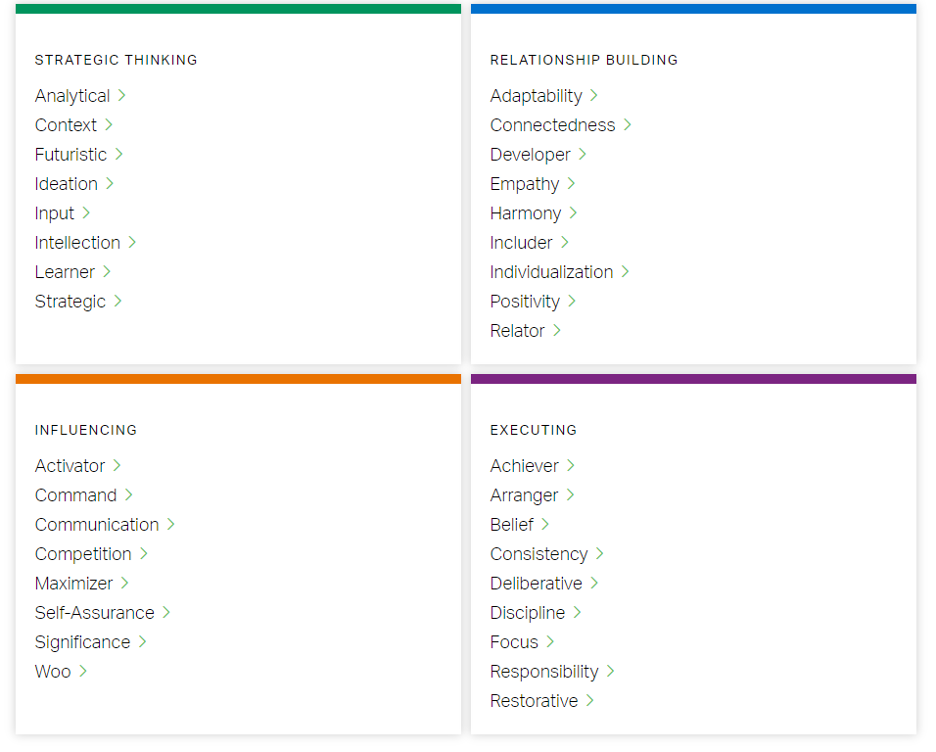
Both Myers Briggs and Strength Finders require the hiring decision makers to come to an agreement on the best strengths for the role. These tools can be utilized for any role and do a great job showcasing the strengths of a candidate outside of a resume.
Commercial Cyber Aptitude Test – This industry specific test created by IBM allows hiring decision makers to “assess behavioral attributes and cognitive aptitude to acquire the technical knowledge required in a cyber role”. (www.worktest.co/wp-content/uploads/2018/10/Commercial-Cyber-Aptitude-Test.pdf) Importantly, the purpose of this test is to figure out what a candidate’s ability is to pick up the technical knowledge required for a role. This is a critical bridge between those who do not have the technical experience on a resume but may have the necessary skills to not only do a specific cyber security job well but also pick up the required technical knowledge when needed.
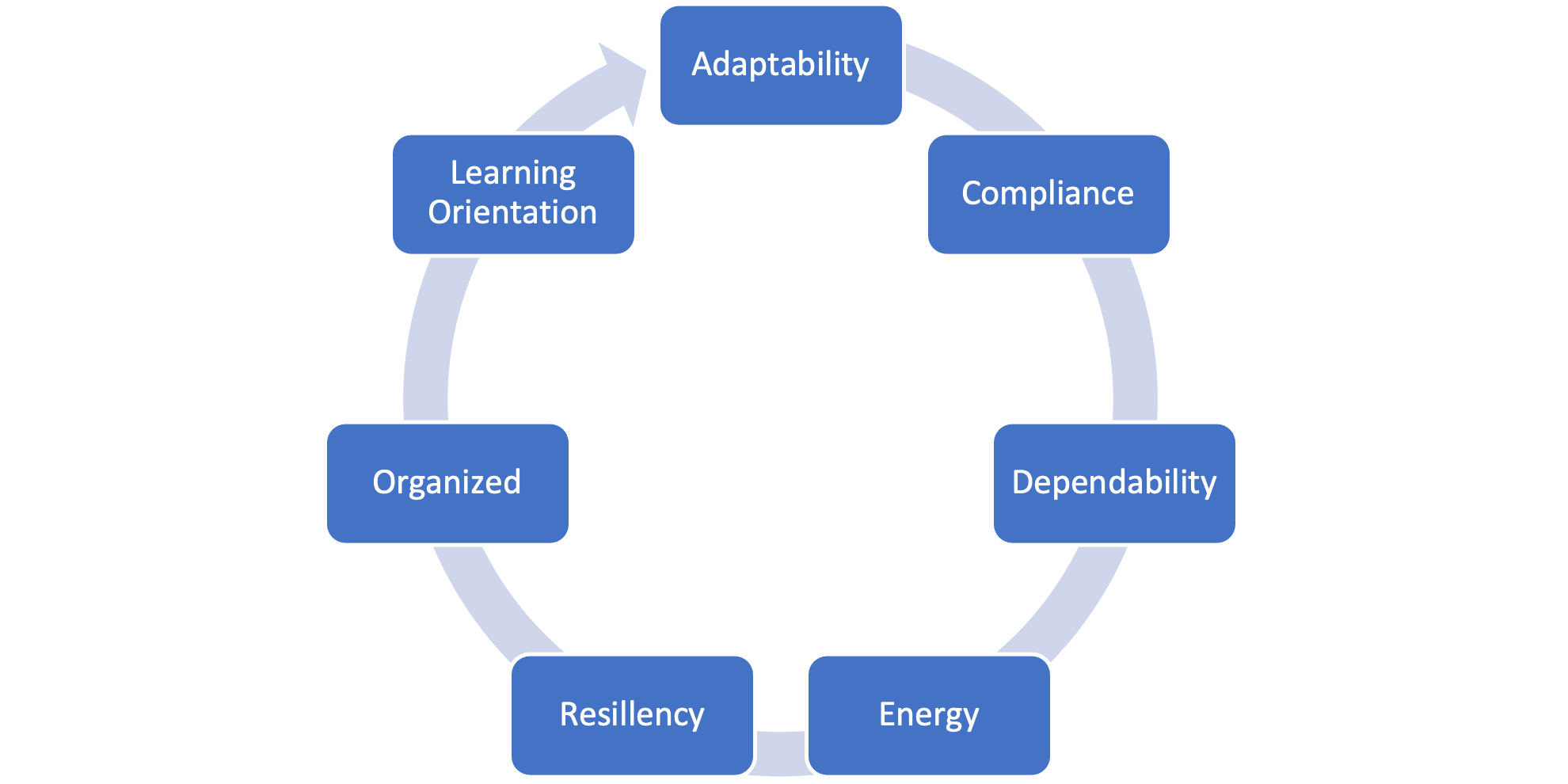
The Commercial Cyber Aptitude Test is well situated to help assess a junior or transitioning cyber security hire and looks for the below behavioral traits for cyber roles:
SANS CyberTalent
SANS CyberTalent is a full program developed by the SANS Institute to provided targeted training and for employers to:
Being able to focus on identifying talent during recruitment is an area where SANS CyberTalent shines as it looks at both soft and hard skills that are required for a successful candidate. Following the theme of many of the other industry agnostic and industry specific assessments that were referenced earlier, SANS CyberTalent starts off assessments from a non-technical level. This is done through an “Aptitude” assessment and gauges the candidate’s skills to become successful in their cyber security role. This assessment may be best suited for those who are just joining the cyber security industry and may not have some of the technical expertise just yet.
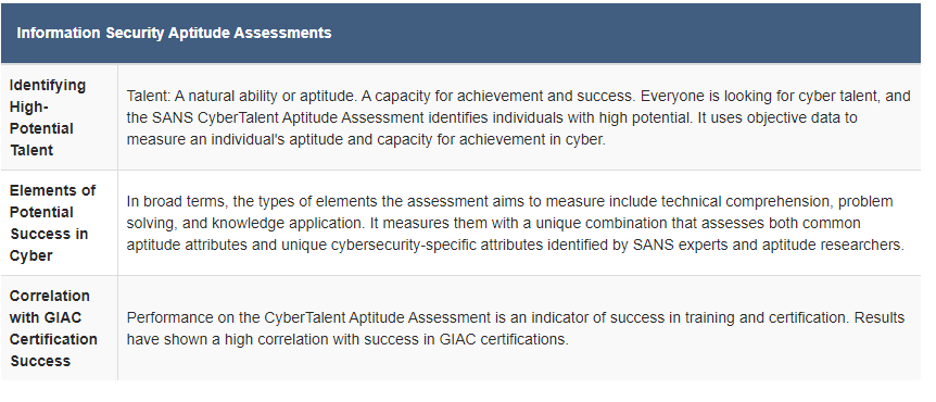
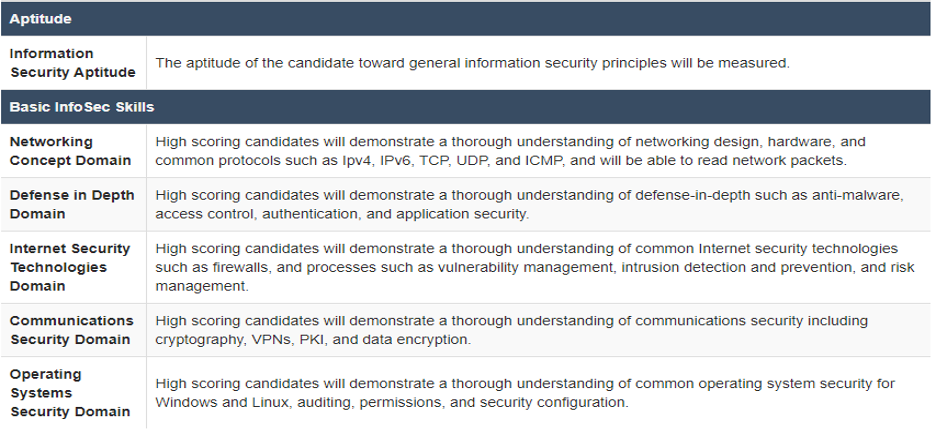
The CyberTalent Enhanced Assessment under the SANS CyberTalent Assessment program goes one step further and begins to assess some of the technical knowledge that a non junior role would expect to have. Importantly, the Aptitude test is still given so hiring decision makers can make an assessment of the candidate’s potential of not only being successful in the role but also to gauge their non technical capabilities. These basic information security domains that are assessed include network concepts, defense in depth, internet security technology, communications security and operating systems.
The other assessments aim to ascertain the knowledge on specific cyber security skillsets. These assessments may be best aligned to experienced roles or roles to fill a specific need in a cyber security organization such as incident response:
CYBRScore
CYBRScore aims to have a candidate use a lab environment to test and prove their technical cyber security skills. Available labs include a range of cyber concepts from basic firewall configuration, to incident analysis, and coding. This allows the candidate to showcase their hands to keyboard knowledge of many cyber security topics that may have a hard time being shown through a plain old resume. It also may be a great way of finding out from your final list of candidates what tier of knowledge you can expect from the hire. Additionally, CYBRScore’s grading and scoring component interacts with lab systems to monitor changes, responses, and actions performed and inputted by the user. This assessment would best fit a candidate who has hand on experience to bring to an open role or a potentially a candidate who has prior IT experience but less direct cyber security experience. Being flexible on an assessment such as CYBRScore allows everyone in the hiring process to have confidence in the level of technical knowledge a candidate brings.
Know that when you look through a sea of 250 + resumes for one open job description, it is no longer impossible find who the top tier candidates are for your organization. Both the industry agnostic and industry specific methods that were covered above provide another tool for hiring decision makers to use to find the best candidate. While the assessments and methods provide an extra data point, try and make sure that every decision maker is in agreement on what they feel will make a candidate successful in a role. In an entry level or job transition type role, the candidate’s non technical aptitude and willingness to continue to learn may hold more weight in a decision than their technical acumen. As the technical demands of a more experienced role expand, other more technical assessment may be better suited to assist in the decision making process. No one assessment is going to be clairvoyant enough to determine the future success of a candidate. However, with these assessments, you can increase your confidence level that you and all the hiring decision makers are making a sound next choice for the next joiner to your team .
1. Listen to the corresponding webcast here.
2. Read the rest of the Blog series here:
Kevin Garvey is the US IT Security Manager for an international bank responsible for overseeing incident response, vulnerability management, cyber threat intelligence, as well as the security operations center (SOC). Previously, he worked at New York Power Authority, JP Morgan and WarnerMedia (formerly Time Warner). Kevin has always had a passion to hunt down the adversary and has loved tackling the risk and threat challenges his responsibilities have thrown at him. Kevin teaches SANS MGT512: Security Leadership Essentials for Managers. Read Kevin's full profile here.


Kevin is the IT Security Manager for an international bank, responsible for overseeing incident response, vulnerability management, cyber threat intelligence, as well as the SOC. He has worked at New York Power Authority, JP Morgan and WarnerMedia.
Read more about Kevin Garvey