SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsCheck out the new Cyber42 Security Leadership Simulation game used in SANS MGT512: Security Leadership Essentials for Managers! Can you win??

An updated blog about Cyber42 can be found here, incorporates all the new uses of the game. and will be kept up-to-date.
I’ve been teaching for SANS for over a decade and we’ve learned a lot building out the Management Curriculum. We have great authors and instructors who have created amazing content, labs, and exercises. These include hands-on technical labs, case scenarios, group discussions, and longer business case studies like the ones from Harvard Business School.
Recently, we added something new to the mix for students in the MGT512: Security Leadership Essentials for Managers course. We call it the Cyber42 Security Leadership Simulation. The goal of this continuous tabletop exercise is to improve the state of security for your organization and more effectively manage risk. As you might experience at work, the actions you choose to take can have uncertain outcomes and even unintended consequences.
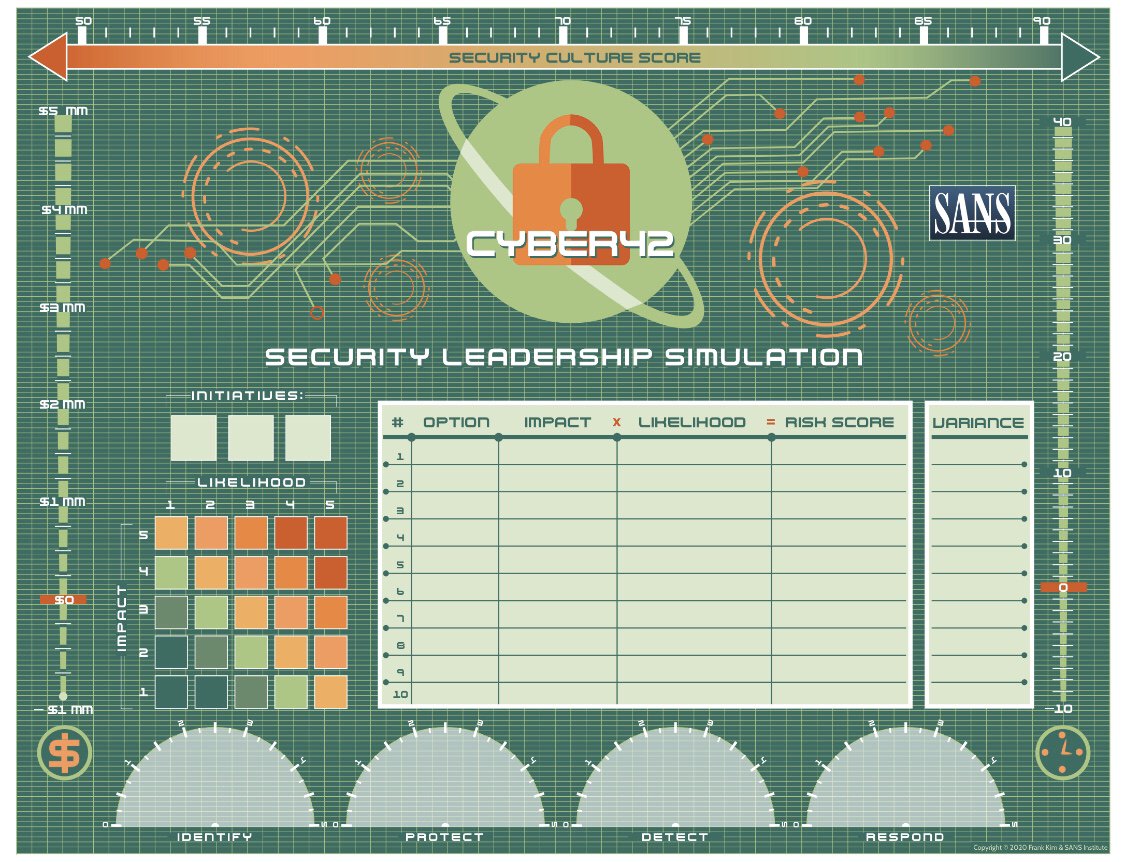
Teams play to improve security culture at a fictional organization. What does that mean in more detail? Just as in real life, any program has constraints, such as time, money, and resources. Students are required to manage the security program budget even amongst changing tides and requirements within the organization. They must capitalize on the schedule and available resources to accomplish necessary tasks in a timely and effective manner. Team members interact with one another throughout class in order to maximize the results of their program. This type of interactive simulation puts students in real-world scenarios that spur discussion, critical thinking of situations, and melding of different points of view and personalities that they will encounter at work.
As students progress in the game, they choose different initiatives to implement. These initiatives are larger, strategic activities that drive change for the organization. By the end of the game three different initiatives are implemented.
Just like in the real world, however, unexpected events can arise that delay or even possibly derail teams’ planned strategic initiatives. In the game there are ten events to which teams will respond. The decisions that are made in response to these events will alter teams’ budget, time, level of security functions, and ultimately the security culture score.
Students keep track of their security progress using the dials at the bottom of the game board. These dials for Identify, Protect, Detect, and Respond represent how much your team has implemented for each of these areas.
Winning the game is simple. A team needs to have the highest security culture score, which is represented by the tracker at the top of the game board. This represents how well your organization has incorporated security as part of the its culture. It’s not just about implementing security controls, it’s about changing behaviors and culture to create lasting security improvement.
If you are taking the class in OnDemand, we did a special studio recording of the Cyber42 game and all of the labs in the class so you don’t miss out on the fun!
We’re really excited about the game and are glad that students are as well.
“I am learning a lot from the Cyber42 Security Event games.”
– Crystal Chatam, EY
“Really loving the game aspect, keeps it very interactive.”
– MGT512 Student, SANS2020
“I thought that the game was very good. A different way of looking at things that apply to today’s scenarios.”
– Ed Moore, Moore Consulting
“MGT512 course material was perfect, and the Cyber42 game was fun. I loved the challenge coin aspect as well.”
– Mike Melo, LifeLabs
Did you say challenge coin? Yes! If you are taking the class live (either in-person or live online) the members of the winning team get the new MGT512 challenge coin. Shout out to Derek Hill for providing the inspiration for the cool slogan.
Look forward to seeing you in MGT512!

About the author: Frank Kim leads the management and cloud security curricula for SANS, developing courses on strategic planning, leadership, DevSecOps and cloud security. He is also a SANS certified instructor and author of MGT512, MGT514, and SEC540. Previously, Frank served as CISO at the SANS Institute, leading its information risk function, and was executive director of cybersecurity at Kaiser Permanente, where he built an innovative security program to serve one of the nation's largest not-for-profit health plans and integrated healthcare provider. Currently, as founder of ThinkSec, a security consulting and CISO advisory firm, Frank helps leaders develop business-driven security programs.


SANS Fellow Frank Kim helps to develop the next generation of CISOs and cyber leaders while teaching LDR512 and LDR514.
Read more about Frank Kim