SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
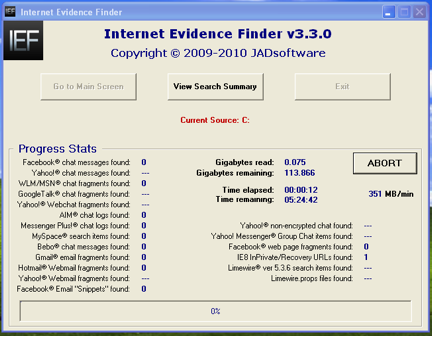
Contact UsI had an opportunity earlier this year to interview Jad Saliba of JadSoftware.com discussing his Internet Evidence Finder tool. You can view that interview here. Hopefully, SANS Computer Forensic Blog readers enjoyed the 15% discount that Jad offered exclusively to SANS CF blog readers and have taken the time to implement this tool into your forensic toolkit. This post is part of a series and will introduce functionality of IEF v3.3. You can download the most recent version (v3.5.1 at time of this article) from JadSoftware.com. Just a brief recap of what IEF will search for on a mounted drive/folder. Facebook chat, Yahoo! chat (IEF must have chat username to decode), Windows Live Messenger chat, Google Talk chat, AIM logs, hotmail webmail fragments, yahoo! webmail fragments, etc. For a full listing of supported artifacts and limitations visit here
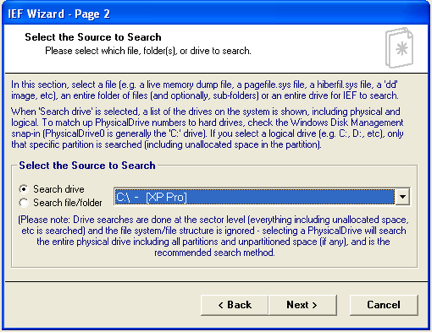
IEF has a nice step-by-step wizard to guide you through the process of selecting your source drive/file, your output folder, other options, etc. The great thing about IEF is that if you only have a live memory dump, the hiberfil.sys or the pagefile.sys you can use it as your source file to search for that forensic nugget. If your forensic image is an .E01 you will need a mount image utility (i.e. Mount Image Pro) to mount the forensic image and then point IEF to that drive letter.
We can view the results in the directory
C:\Documents and Settings\CF\Desktop\IEF Output\IEF Output\IEF — March 19 2010 192620\
03/19/2010 07:26 PM <DIR> .
03/19/2010 07:26 PM <DIR> ..
03/19/2010 07:26 PM <DIR> AIM chat
03/19/2010 07:26 PM <DIR> Bebo Chat
03/19/2010 07:26 PM <DIR> Facebook Email Snippets
03/19/2010 08:52 PM <DIR> Facebook Live Chat
03/19/2010 07:26 PM <DIR> Facebook Pages
03/19/2010 07:26 PM <DIR> Gmail
03/19/2010 08:52 PM <DIR> Hotmail Webmail
03/19/2010 07:26 PM <DIR> IE8 InPrivate and Recovery URLs
03/19/2010 11:54 PM 1,335 IEF - Log.txt
03/19/2010 08:52 PM <DIR> Messenger Plus! chat
03/19/2010 07:26 PM <DIR> MySpace Chat
03/19/2010 07:26 PM <DIR> Windows Live Messenger Chat
1 File(s) 1,335 bytes
13 Dir(s) 93,659,459,584 bytes free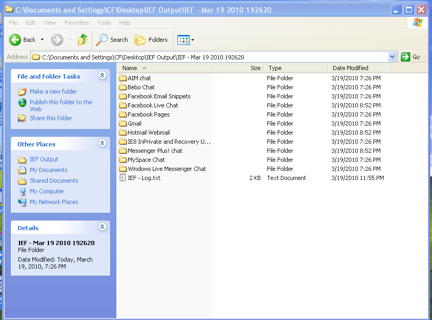
IEF also creates a text log file that shows what items were searched and a brief summary of the results once IEF is complete. You will notice in the log start and abort times. (Author's Note: Process aborted for demonstration purposes)
Start time: Mar 19, 2010 19:26:20
Aborted at: Mar 19, 2010 23:54:53
— Start of log —
Internet Evidence Finder v3.3.0 Copyright © 2009 JADsoftware
Search items selected:
Hotmail® Webmail fragments
Messenger Plus!® chat logs
AIM® chat logs
Bebo® chat
MySpace® chat
Gmail® email fragments
Windows Live Messenger® chat
Facebook® chat
Facebook® Email "Snippets"
Facebook® web page fragments
IE8® InPrivate/Recovery URLs
Search options selected:
Save Windows Live Messenger/MSN® chat logs to a CSV/TSV report file
Selected Source:
C:\ - [XP Pro]
Output folder:
C:\Documents and Settings\CF\Desktop\IEF Output\IEF - Mar 19 2010 192620\
Start time: Mar 19, 2010 19:26:20
Final results of search:
Facebook chat messages found: 2
Facebook Webpage fragments found: 0
Windows Live Messenger/MSN chat messages found: 0
Gmail email fragments found: 0
IE8 InPrivate/Recover URLs found: 38
AIM chat logs found: 0
Messenger Plus! chat logs found: 1
MySpace chat messages found: 0
Bebo chat messages found: 0
Hotmail Webmail fragments found: 1
Facebook Email "Snippets" found: 0
Aborted at: Mar 19, 2010 23:54:53
———————————
— End of log —
Let's take a look at the output: C:\Documents and Settings\CF\Desktop\IEF Output\IEF - Mar 19 2010 192620\IE8 InPrivate and Recovery URLs\ IE8 InPrivate and Recovery URLs Report.csv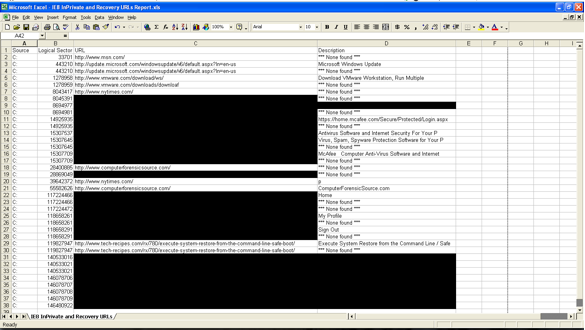
Let's take a closer look at row# 30: C: 119827947 http://www.tech-recipes.com/rx... *** None found **
Using your favorite hex editor let's take a look at sector 119827947 and we see the IE 8 InPrivate Browsing URL.
E48DBD600 D6 00 14 00 1F 00 80 53 1C 87 A0 42 69 10 A2 EA Ö ?S ? Bi ¢ê
E48DBD610 08 00 2B 30 30 9D C0 00 61 80 00 00 00 00 68 00 +00À a? h
E48DBD620 74 00 74 00 70 00 3A 00 2F 00 2F 00 77 00 77 00 t t p : / / w w
E48DBD630 77 00 2E 00 74 00 65 00 63 00 68 00 2D 00 72 00 w . t e c h - r
E48DBD640 65 00 63 00 69 00 70 00 65 00 73 00 2E 00 63 00 e c i p e s . c
E48DBD650 6F 00 6D 00 2F 00 72 00 78 00 2F 00 37 00 38 00 o m / r x / 7 8
E48DBD660 30 00 2F 00 65 00 78 00 65 00 63 00 75 00 74 00 0 / e x e c u t
E48DBD670 65 00 2D 00 73 00 79 00 73 00 74 00 65 00 6D 00 e - s y s t e m
E48DBD680 2D 00 72 00 65 00 73 00 74 00 6F 00 72 00 65 00 - r e s t o r e
E48DBD690 2D 00 66 00 72 00 6F 00 6D 00 2D 00 74 00 68 00 - f r o m - t h
E48DBD6A0 65 00 2D 00 63 00 6F 00 6D 00 6D 00 61 00 6E 00 e - c o m m a n
E48DBD6B0 64 00 2D 00 6C 00 69 00 6E 00 65 00 2D 00 73 00 d - l i n e - s
E48DBD6C0 61 00 66 00 65 00 2D 00 62 00 6F 00 6F 00 74 00 a f e - b o o t
E48DBD6D0 2F 00 00 00 00 00 00 00 A2 00 00 00 45 00 78 00 / ¢ E x
E48DBD6E0 65 00 63 00 75 00 74 00 65 00 20 00 53 00 79 00 e c u t e S y
E48DBD6F0 73 00 74 00 65 00 6D 00 20 00 52 00 65 00 73 00 s t e m R e s
E48DBD700 74 00 6F 00 72 00 65 00 20 00 66 00 72 00 6F 00 t o r e f r o
E48DBD710 6D 00 20 00 74 00 68 00 65 00 20 00 43 00 6F 00 m t h e C o
E48DBD720 6D 00 6D 00 61 00 6E 00 64 00 20 00 4C 00 69 00 m m a n d L i
E48DBD730 6E 00 65 00 20 00 2F 00 20 00 53 00 61 00 66 00 n e / S a f
E48DBD740 65 00 20 00 42 00 6F 00 6F 00 74 00 20 00 7C 00 e B o o t |
E48DBD750 20 00 57 00 69 00 6E 00 64 00 6F 00 77 00 73 00 W i n d o w s
E48DBD760 20 00 7C 00 20 00 54 00 65 00 63 00 68 00 2D 00 | T e c h -
E48DBD770 52 00 65 00 63 00 69 00 70 00 65 00 73 00 01 00 R e c i p e s
E48DBD780 00 00 00 00 00 00 FF FF FF FF 00 00 00 00 00 00 ÿÿÿÿ
E48DBD790 00 00 00 00 00 00 00 00 00 00 C0 46 00 00 24 00 ÀF $
E48DBD7A0 00 00 02 00 00 00 00 00 00 00 FF FF FF FF 20 69 ÿÿÿÿ i
E48DBD7B0 33 25 F9 03 CF 11 8F D0 00 AA 00 68 6F 13 D6 00 3%ù Ï Ð ª ho Ö
E48DBD7C0 00 00 14 00 1F 00 80 53 1C 87 A0 42 69 10 A2 EA ?S ? Bi ¢ê
E48DBD7D0 08 00 2B 30 30 9D C0 00 61 80 00 00 00 00 68 00 +00À a? h
E48DBD7E0 74 00 74 00 70 00 3A 00 2F 00 2F 00 77 00 77 00 t t p : / / w w
E48DBD7F0 77 00 2E 00 74 00 65 00 63 00 68 00 2D 00 72 00 w . t e c h - rInternet Evidence Finder is a good, inexpensive forensic tool to assist the examiner/analyst with parsing internet artifacts that are an important piece of the computer forensic examination. If your examinations include searching for internet artifacts, IEF will help you streamline the process and give you a nice output for reporting and presentation purposes. In Part III of the IEF series, we'll take a closer look at artifacts of what IEF is reporting and how we validate our findings. Stay tuned...
Mr. Brad Garnett, CCE, GCFA is a law enforcement officer specializing in computer forensics. You can follow Brad on Twitter @bgarnett17 and his blog at www.computerforensicsource.com