SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsLearn how to import the REMnux virtual appliance into VMware or VirtualBox to set up a powerful system for malware analysis.

The REMnux project provides a Linux distribution for analyzing malicious software. The distro is available as a virtual appliance file, which you can run in your favorite hypervisor. REMnux is used my many malware analysts and is incorporated into FOR610: Reverse-Engineering Malware course at SANS. This article explains how you can import the REMnux virtual appliance into VMware and VirtualBox. You can use other hypervisors and even run REMnux as a Docker container, but this is outside the scope of this post.
If you don't already have a VMware hypervisor, get the tool of your choice, be it the free Player version or the commercial Pro version. The biggest difference between the two is that Player doesn't support snapshots, which are usually very useful when using analyzing malware. VMware Workstation Pro or VMware Fusion Pro is probably the best option for most REMnux users. For a headless setup, you might prefer VMware ESXi.
Next, follow the instructions on the REMnux documentation site to download and import prebuilt REMnux virtual appliance. For VMware, download the REMnux virtual appliance file using the "General OVA Link." Note that some browsers change the extension of the OVA file after downloading it; if that happens, rename the file so it has the .ova extension.
After validating that the SHA-256 hash of the downloaded file matches the one on the REMnux documentation site, load the OVA file into VMware. One way to do this is to double-click the OVA file. Alternatively, open VMware and select Open or Import (depending on your VMware product) from the File menu. (See VMware instructions for Workstation and Fusion.)
VMware will ask you where to save the imported virtual machine, then begin importing it.
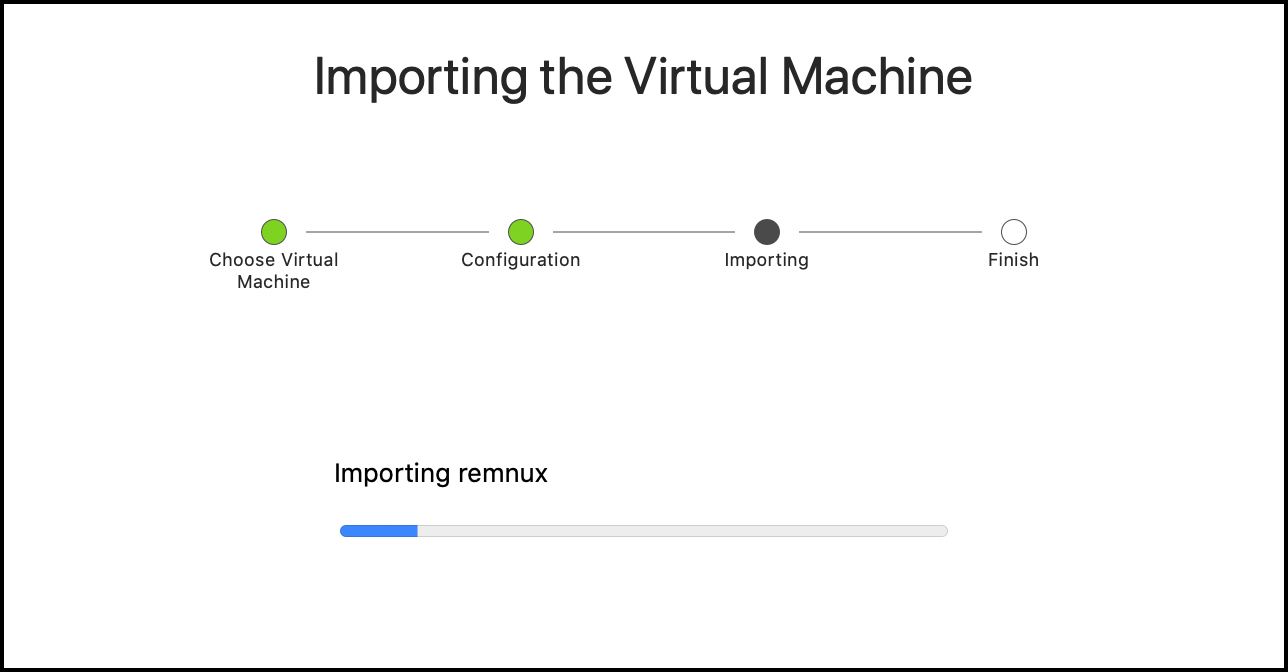
VMware will create the REMnux virtual machine in the designated location. Once this is done, you can delete the OVA file that you've downloaded.
Prior to starting the virtual machine, consider modifying its properties, perhaps allocating more RAM to it.
VMware sometimes conflicts with the Ubuntu graphical environment, which by default uses Wayland display protocol. The problems manifest themselves through the VM being unresponsive to keyboard and mouse; clipboard sharing and copy-and-paste VMware features might not be working, too. If this happens to you, follow REMnux documentation instructions to switch your REMnux VM from Wayland to Xorg.
If you prefer to use VirtualBox for your REMnux virtual machine, install the latest version of the tool.
Next, follow the instructions on the REMnux documentation site to download and import prebuilt REMnux virtual appliance. For VirtualBox, download the REMnux virtual appliance file using the "VirtualBox OVA Link." Note that some browsers change the extension of the OVA file after downloading it; if that happens, rename the file so it has the .ova extension.
While you could use the "General OVA" version, importing it into VirtualBox would require you to reinitialize the network interface details inside your REMnux virtual machine; you'd also need to install Guest Additions. The VirtualBox-specific version of the OVA file eliminates these steps.
After validating that the SHA-256 hash of the downloaded file matches the one on the REMnux documentation site, load the OVA file into VirtualBox. One way to do this is to double-click the OVA file. Alternatively, open VirtualBox and select File > Import Appliance... (See VirtualBox instructions for doing this.)
VirtualBox will give you a chance to customize properties of the VM you're about to generate based on the supplied OVA file. You can change the location of the VM, if you wish. You can also modify other aspects of the virtual machine, including allocating extra RAM or other resources.
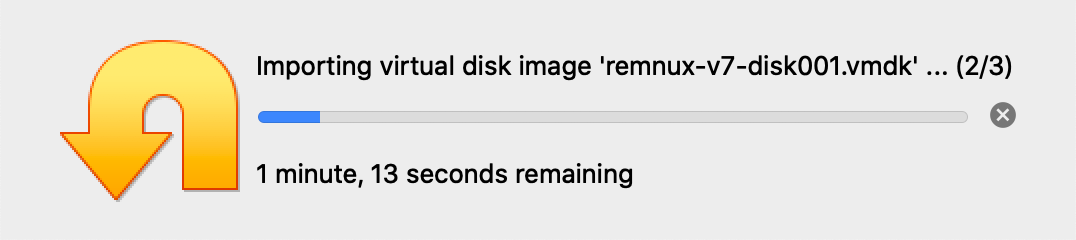
VirtualBox will import the OVA and create the REMnux virtual machine in the designated location. Once this is done, you can delete the OVA file that you've downloaded.
If you're running VirtualBox on Windows 10, before starting your REMnux VM, be sure to disable Hyper-V using the following command:
bcdedit /set hypervisorlaunchtype off
Do this even if Hyper-V appears disabled in the Windows Features listing. If you don't, you are likely to run into problems downloading files and updating REMnux.
If your REMnux window is too small when you boot it up the system in VirtualBox, activate the Scaling Mode for the VM via the VirtualBox menu View > Scaling Mode.
Click Start to power up your REMnux virtual machine, then run the following command on REMnux to update its software
remnux upgradeThis will allow you to benefit from any enhancements introduced after the virtual appliance has been packaged. Your system needs to have Internet access for this to work.
For more information about REMnux, including the detailed listing of the tools available as part of the project, see the REMnux documentation site.
Lenny Zeltser teaches at SANS Institute. He is active on Twitter and writes a security blog.


Lenny Zeltser is a leader in developing resilient security programs. His invaluable tools, like REMnux, a widely used Linux distribution for malware analysis, have become industry standards in combating malicious software.
Read more about Lenny Zeltser