SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsIt is crucial that ICS/OT cyber defenders embrace the differences between IT and ICS.


With my firm ICS Defense Force, I perform industrial control system (ICS) security assessments, incident response tasks, and incident response tabletop exercises across multiple critical infrastructure sectors, globally. In fact, I recently conducted these tasks for oil and gas and electric power sectors in the Gulf region. It is important to describe my practical field work in this context. It allows me to meet with security teams, engineering staff, and those leading the charge of cybersecurity risk management and defense. This includes the decision makers seeking technical solutions and tactical training to address their identified cybersecurity challenges.
In part 1 of this blog series, I noted that 25% of survey respondents from the 2023 SANS ICS/OT Cybersecurity survey consider the current cybersecurity threats against ICS as severe/critical. This aligns, as modern adversaries again and again illustrate the brazen steps they take to defeat traditional security controls and impact safety and engineering reliability. Proactive control system cyber defense requires dedicated ICS tactical security teams with engineering knowledge to preserve the safety of ICS and operational technology (OT) operations. Details of the ICS threat landscape in the Gulf region and common ICS security challenges, can be further reviewed in Part 1.
For part 2 of this ICS blog post series, I want to focus on ICS/OT environments by protecting their networks. Let’s jump into this topic, below.
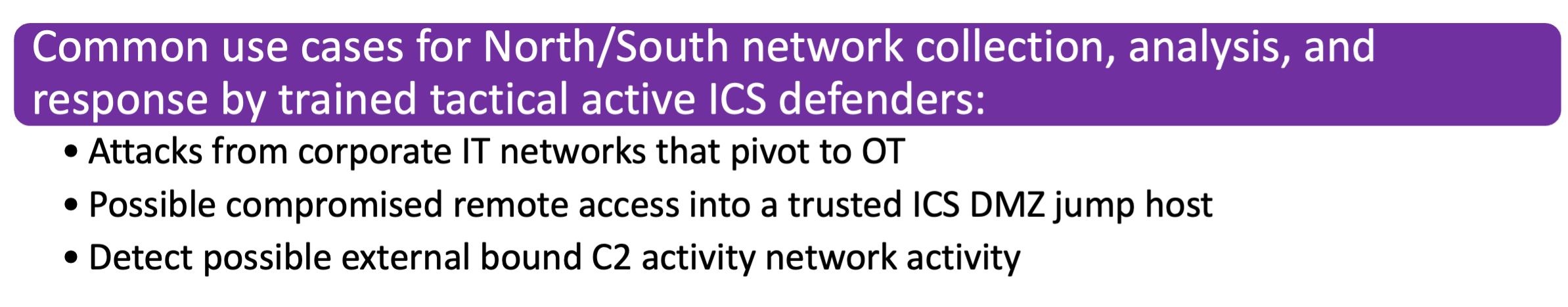
A common ICS attack technique is pivoting from IT networks into ICS environments through trusted network paths or trusted assets between these networks. In fact, 38% of compromises to ICS environments in 2023 come from compromises in IT networks that allow threats to traverse into ICS networks for engineering system specific attacks. Such attacks could lead to the loss of view, control, or the manipulation of control of engineering operations.
From a defense perspective, we know performing safe, tactical ICS network perimeter assessments can inform us of targeted pathways and weak points between IT and ICS networks. The scope of such assessments should extend to all access, including remote access into the ICS, those deemed to have multi-factor authentication, and vender connections.
There are, however, major differences in assessments and penetration tests, specifically, their purposes, i.e., their effects and related remediation actions when gaps are found. Penetration testing brings the inherent risk of introducing unintentional system inconsistencies during scanning or active system interaction. This holds true especially for legacy engineering devices and can result in system loss, unavailability, engineering system downtime, and may also introduce safety impacts. As such, passive assessments promote greater safety and reliability than penetration testing and are the recommended assessment approach for ICS/OT environments.
Tactical teams should take advantage of the benefits of architecting and segmenting the ICS network properly by aligning their strategy with the Purdue Model. Then, add security to the Purdue using the SANS ICS410 SCADA network architecture. This architecture naturally provides incident response capabilities and network traffic collection points that aid in effective ICS network visibility. Once in place, an assessment of this effective ICS network architecture is recommended.
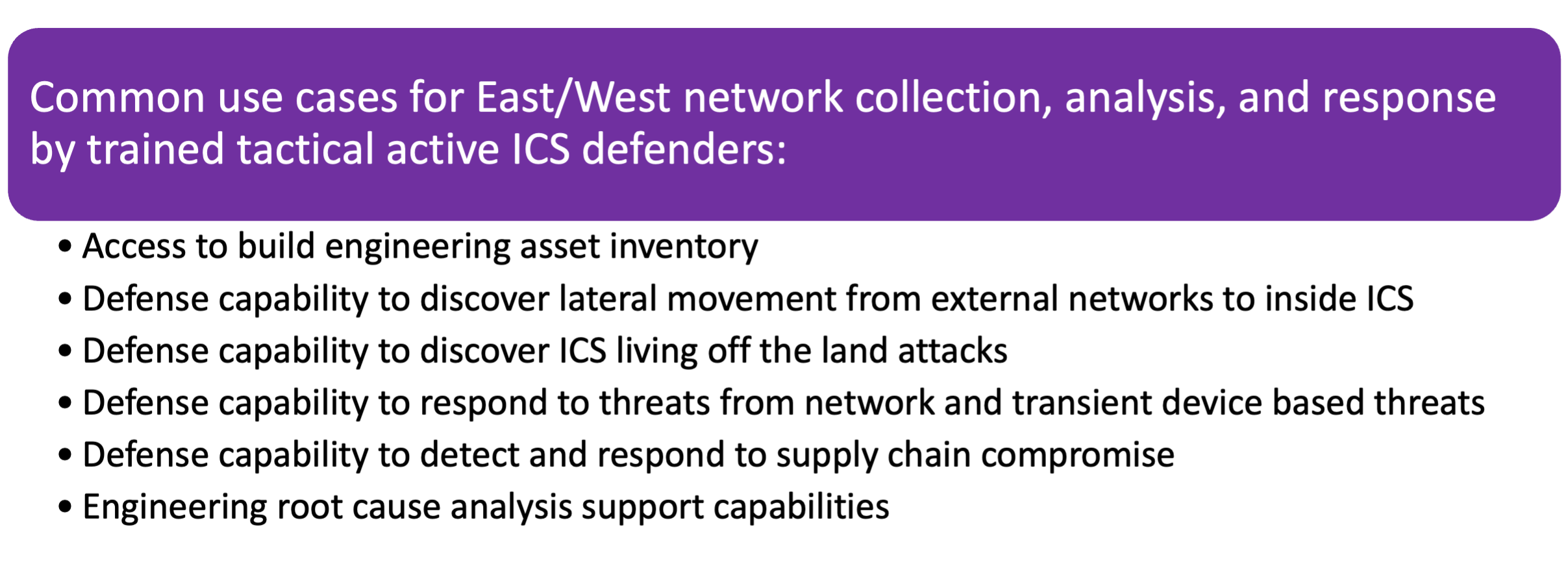
ICS network visibility is achieved when specific, ICS-protocol aware network intrusion detection systems (IDSs) are deployed at strategic positions inside the control system network. These IDSs monitor and alert on anomalous engineering network activity, such as the abuse of ICS protocols.
Mature ICS facilities have either deployed ICS network visibility tools and processes or they are planning to do so in the near future. According to the recent 2023 SANS ICS/OT Cybersecurity survey data, respondents said that deploying ICS specific network visibility technology and the dedicated ICS/OT trained defenders who leverage it ranked #1 in importance and planned to implement this strategy within the next 18 months.

It is imperative this type of technology is detection-based rather than prevention-based to avoid false positives and disrupting critical engineering operations. This technology must be ICS protocol aware. It must know how to correctly interpret the industrial protocols running in the environment and related engineering commands on the network, including but not limited to Common Industrial Protocol (CIP), Distributed Network Protocol 3 (DNP3), EtherNet/IP, IEC61850, ModbusTCP, OPC, Profibus, PROFINET, S7, and BacNet, to name a few.
The exact placement of such an ICS dedicated network intrusion detection technology deployed in industrial network(s) is crucial to its effectiveness. Tactical teams should have technical discussions with faculty network architects on the exact locations for deployment within their environment. However, I will provide you with some suggestions and related use cases.
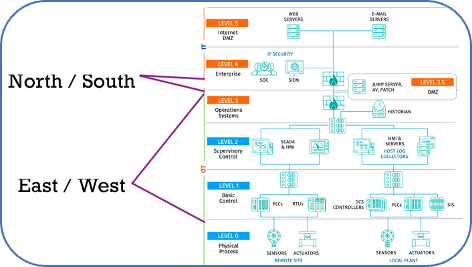
Ideally, tactical ICS security teams will work with engineering staff and lead the way to obtain both ICS network perimeter visibility (North/South traffic) and internal ICS network visibility (East/West traffic) as shown below as a guide.
Once the placement of the solution is complete (in either one or both selected placement locations), dedicated resources trained specifically in IT and ICS security and prioritizing safety, are required to operate an ICS network visibility tool.
The SANS course, ICS515: ICS Visibility, Detection, and Response meets several modern ICS security challenges with practical techniques and applied knowledge for effective ICS security to protect critical infrastructure. ICS515 teaches students how to perform tactical ICS incident response by leveraging hands-on labs. Labs include assembling and running a programmable logic controller (PLC) like you’d see on a plant floor. Students keep the PLC kit for continued learning after class is over. Students from IT, ICS, engineering, etc., will detect and defend against threats in several realistic ICS environments.
In conclusion, what works for IT business networks and assets will in many cases cause disruptive or disastrous consequences if applied to ICS/OT engineering systems and environments. So, it is crucial that tactical cybersecurity defenders focusing on ICS/OT ensure they embrace the differences between IT and ICS. They should never attempt to “copy and paste” the processes, technical controls, and policies from IT Security into ICS security environments.
The most effective way today to achieve practical, technical, and effective cyber defense of critical infrastructure is having technical teams specifically trained on ICS security, utilizing ICS specific security tools, and who understand; 1) IT security threats, 2) ICS/OT security threats, and 3) the engineering systems and work with a prioritization on safety first.
On behalf of myself and the EMEA team, thank you for taking the time to review this important topic geared towards tactical ICS/OT cybersecurity roles, as it relates to the protection of critical systems in the Gulf region. I look forward to teaching and speaking with you and your teams at the next SANS Gulf event.
Be safe from industrial incidents!
Best,


Dean Parsons, CEO of ICS Defense Force, teaches ICS515 and co-authors ICS418, emphasizing ICS-specific detection, incident response, and security programs that support OT operations—aligning practitioners and leaders on clear, defensible action.
Read more about Dean Parsons