SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsVulnerabilities don’t matter! Patching is terrible! Prove me wrong!

Hyperbole aside, in this blog we will discuss some of the most common pitfalls in enterprise vulnerability management programs. Essentially, we spend too much time focusing on the wrong issues. This is a serious problem given that information security teams are almost always under- resourced.
Let’s start with a level set.
Vulnerability management is the continuous and repeatable process that provides an organization with an understanding of its weaknesses so that a plan can be developed to address them. It’s the process by which an organization identifies, analyzes, and manages IT and cybersecurity vulnerabilities, and it is key in planning for and choosing the controls that best address and manage risk.
When conducting vulnerability management, organizations should describe their current cybersecurity posture and targeted future state, identify and prioritize opportunities for improvement, assess progress toward the future state, and communicate risk to stakeholders.
Vulnerability management outcomes should include a vulnerability analysis and resolution strategy and a vulnerability management plan. The plan should include a vulnerability discovery process, detail vulnerability management activities, and provide a strategy for managing exposure to risk.
An organization must have robust vulnerability management practices in place to effectively respond to a vulnerability.
In today's rapidly evolving digital landscape, organizations face an ever-growing number of cybersecurity threats. Ensuring the security and integrity of critical systems and data is a top priority for businesses and government agencies alike. Vulnerability assessments play a crucial role in identifying and addressing potential weaknesses in an organization's security posture.
However, the current state of vulnerability assessment practices often falls short of providing organizations with a comprehensive understanding of their security posture. Many teams neglect critical components of a successful vulnerability assessment strategy, such as Threat Modeling and Validation. As a result, they may leave their networks exposed to potential threats, leading to costly data breaches and reputational damage.
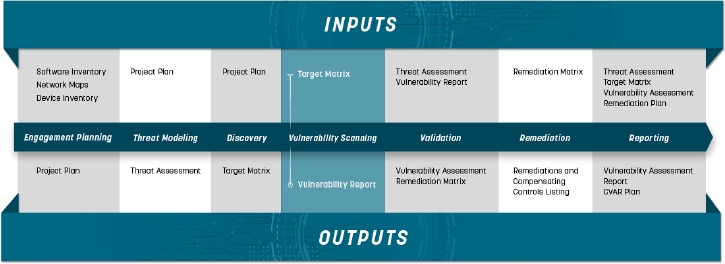
The SANS Institute Seven Phase Vulnerability Assessment Framework aims to address these issues by providing a structured, repeatable methodology for organizations to effectively assess and remediate potential security vulnerabilities. By implementing this framework, organizations can unlock the transformative potential of vulnerability assessment in enhancing their information security posture.
By understanding and leveraging each step of this comprehensive framework, organizations can ensure they are making the most of their vulnerability assessment efforts and truly safeguarding their digital assets.
The Vulnerability Assessment Framework consists of seven interconnected phases, each playing a critical role in building a robust security posture for an organization. By following these phases, organizations can ensure a thorough and efficient vulnerability assessment process that uncovers potential weaknesses and recommends appropriate remediation strategies. Here's a high-level overview of the seven phases:
By following these seven phases, organizations can create a comprehensive and effective vulnerability assessment process that uncovers potential security weaknesses and recommends appropriate remediation actions. This structured approach helps organizations strengthen their security defenses and mitigate the risk of cyber threats.
In 2022, a staggering 26,448 unique common vulnerability and exposures (CVEs) were reported. But did cyber adversaries really adopt over 26,000 new techniques in a single year? Absolutely not. This realization forces us to confront an uncomfortable truth: many vulnerabilities simply don't matter.
The fact is, if an attacker doesn't exploit a vulnerability, and we invest significant time and effort into discovering, remediating, and resolving these issues, we're ultimately wasting valuable resources. In an era where organizational security is of utmost importance, efficiency is crucial.
To maximize the security benefits for our organizations, we must be extremely efficient in our vulnerability management efforts. That's where modern risk calculation mechanisms like EPSS (Exploit Prediction Scoring System) come into play. EPSS helps us identify the likelihood that a threat actor might exploit a given vulnerability, enabling us to prioritize and focus on the vulnerabilities that truly matter.

This approach combines both threat intelligence and vulnerability intelligence, which are essentially the factors that influence an attacker's decision to exploit a specific vulnerability. By understanding these factors, we can concentrate our efforts on the vulnerabilities that are most likely to be targeted by cyber adversaries, rather than getting bogged down by the sheer number of CVEs reported.
In the world of cybersecurity, it's crucial to recognize that not all vulnerabilities are equal. Focusing on every single CVE that pops up on a vulnerability scanner is not only inefficient but can also detract from addressing the vulnerabilities that genuinely pose a threat to our organizations.
By leveraging modern risk calculation mechanisms like EPSS, we can better prioritize our vulnerability management efforts and focus on the vulnerabilities that matter most to threat actors. This approach ultimately allows us to strengthen our security defenses and better protect our organizations from potential cyber threats.
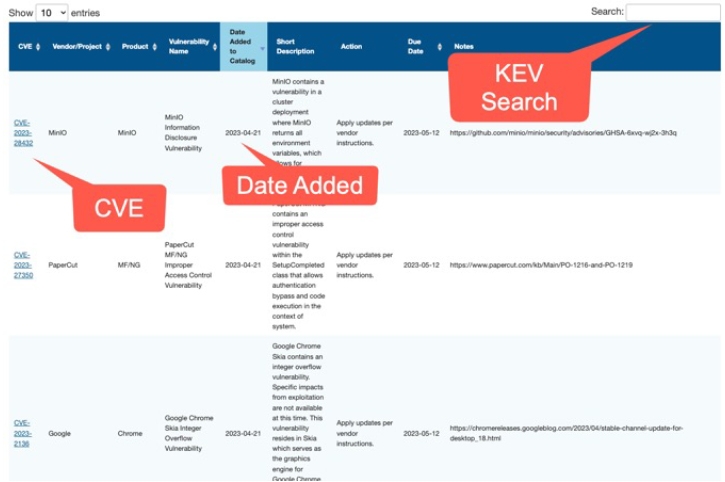
A great place to start with Vulnerability Intelligence sources is the Known Exploited Vulnerabilities (KEV) catalog by the Cybersecurity and Infrastructure Security Agency (CISA).
So, while it might be tempting to chase down every single CVE, it's essential to remember that many vulnerabilities simply don't matter. Instead, focus on what truly matters by prioritizing your efforts and addressing the vulnerabilities that pose the greatest risk to your organization.
One might assume that patching is the easiest and most effective way to remediate vulnerabilities. However, the reality is that patching is not always the best solution. In fact, it can sometimes be the worst option holistically. In this section, we'll explore the limitations of patching and the advantages of alternative approaches like compensating controls.
On June 29, 2021, a critical remote code execution (RCE) vulnerability was discovered in the Windows print spooler service. Microsoft promptly released out-of-band patches, some dating back to Windows 7. However, the initial patch was ineffective.
The first variant of the patch focused on print driver permissions, intending to prevent remote non-administrators from installing printer drivers on the system. However, multiple workarounds bypassed this "fix". Furthermore, PrintNightmare was published either in error or due to poor communication with Microsoft. As a result, the Sangfor group released a proof-of-concept exploit on a public GitHub repository before a patch was available.
Given that this vulnerability affected nearly all Windows domain controllers, which typically do not need to print documents, one of the most effective solutions was to simply disable the printer service or remove the spooler binary (spoolsv.exe). In this case, a fantastic patch could have been an excellent solution, but a simpler alternative provided better results.
The PrintNightmare case demonstrates that relying on patches alone may not always be the most effective approach to remediate vulnerabilities. In some cases, alternative controls may not only prove more effective but also require less time and effort to implement. The critical lesson here is that organizations must be prepared to consider various options for addressing vulnerabilities, rather than merely waiting for and relying on vendor patches.
Patches can sometimes be flawed or even destructive in nature. For instance, the Spectre and Meltdown patches were known to cause systems to blue screen, become unstable, and often require a complete rebuild and reimage. This demonstrates that patches can sometimes create more problems than they solve.
In many cases, compensating controls can offer a more effective solution than patching. These alternative solutions can provide better results, often with less time and effort. Below, we explore several examples of compensating controls that have proven to be valuable in securing organizations' systems.
Server Message Block (SMB) is a network file-sharing protocol that allows applications to read and write to files and request services from server programs. SMB version 1 (SMBv1) is an older, insecure version of the protocol that has been exploited by various high-profile cyberattacks, such as WannaCry and NotPetya. Instead of relying on patches to secure systems running SMBv1, organizations could have disabled the protocol entirely to eliminate the risk associated with it. By doing so, they can protect their networks from a range of vulnerabilities and exploits both past, present, and future that target the legacy protocol.
Removing extraneous and risky components of systems is a core component of Attack Surface Management.
Network segmentation is a compensating control that involves dividing a network into smaller, isolated segments. This approach helps to prevent unauthorized access and contain the spread of threats if a breach occurs. By implementing network segmentation, organizations can mitigate the risk posed by vulnerabilities in one part of the network without relying on patches. This can be especially useful when dealing with legacy systems that are difficult or impossible to patch.
Limiting access to systems degrades the adversary’s opportunity to attack systems further limiting the attack surface.
Multi-Factor Authentication (MFA) adds an extra layer of security by requiring users to provide at least two forms of identification to access a system or service. Implementing MFA can help mitigate the risk of unauthorized access resulting from vulnerabilities in authentication systems, such as weak or stolen credentials. By enforcing MFA, organizations can minimize the potential impact of vulnerabilities without relying solely on patching.
Single points of failure consistently lead to compromise. By looking beyond simple patches our security programs can prevent these conditions from arising in the first place.
The principle of least privilege dictates that users should only have access to the resources and permissions necessary to perform their job functions. By enforcing this principle, organizations can limit the potential damage that can result from exploited vulnerabilities. For example, if a vulnerability allows an attacker to escalate privileges, applying the principle of least privilege can prevent the attacker from gaining access to critical systems and data. This can be a more effective approach than waiting for a patch to fix the vulnerability.
Features are vulnerabilities too. The top two mechanisms for initial access are phishing and remote access tools such as RDP. Controlling user permissions through Identity Access Management (IAM), is the cornerstone of any mature Vulnerability Management program.
Compensating controls can also have a force-multiplicative effect, wherein a single solution might address multiple vulnerabilities at once or even protect against future, undiscovered vulnerabilities. This makes them a valuable tool for organizations looking to improve their security posture. By considering and implementing these alternative approaches, organizations can better protect their digital assets and mitigate the risk of costly data breaches and reputational damage.
While patching is often seen as the go-to solution for immediate remediation, it's essential to recognize its limitations and explore alternative mechanisms for addressing vulnerabilities. Compensating controls can often provide a more effective and comprehensive approach to securing systems, mitigating the risk of cyber threats.
It’s crucial for organizations to consider all available options when addressing vulnerabilities, rather than relying solely on patching. By exploring alternative solutions like compensating controls, organizations can better protect their digital assets and mitigate the risk of costly data breaches and reputational damage.
In today's rapidly evolving threat landscape, it's crucial for organizations to adopt a proactive and holistic approach to vulnerability management. The Vulnerability Assessment Framework (VAF) serves as a comprehensive roadmap that can guide businesses in addressing vulnerabilities more effectively.
By recognizing the limitations of traditional patching and exploring alternative solutions like compensating controls, organizations can better protect their digital assets and stay ahead of the curve. The VAF's seven-phase process ensures a thorough and efficient vulnerability assessment that uncovers potential weaknesses and recommends appropriate remediation strategies.
A successful vulnerability management program goes beyond just addressing CVEs and patching systems. It involves prioritizing vulnerabilities based on risk, implementing compensating controls, and continuously refining security practices. By embracing the VAF and integrating it into their vulnerability management strategy, organizations can optimize their security posture and safeguard against potential cyber threats.
Remember, the key to success lies in being agile and adaptable. By combining modern risk calculation mechanisms like EPSS with the VAF and alternative remediation strategies, businesses can create a resilient and robust security infrastructure that can withstand the challenges of the digital age.
It's time to shift our mindset and redefine vulnerability management. By leveraging the VAF and focusing on what truly matters, we can make better use of our resources, minimize the attack surface, and ultimately ensure the safety and security of our organizations in an increasingly interconnected world.
If you’re interested in learning a complete holistic vulnerability assessment methodology featuring hands-on experience in a full-scale enterprise range, consider joining me at SANS Security West San Diego 2023.



Launched in 1989 as a cooperative for information security thought leadership, it is SANS’ ongoing mission to empower cybersecurity professionals with the practical skills and knowledge they need to make our world a safer place.
Read more about SANS Institute