Brandon Evans
Senior InstructorPartner at Cyverity
Specialities
Cloud Security

Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsCloud Security
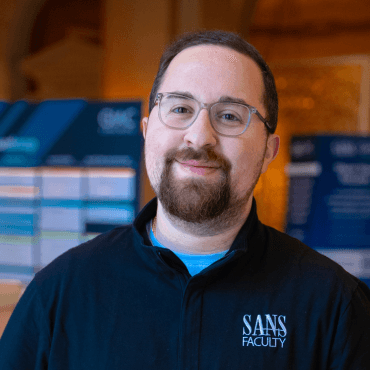
Brandon is a Partner at Cyverity and Senior Instructor at the SANS Institute. As a consultant, he specializes in securing applications and workloads in multicloud and hybrid environments through assessments, decision support, and security consultation services. Previously, he led the secure development training program at Zoom Video Communications. He began his career in software engineering, where he contributed to core product development for both emerging startups and large-scale enterprises. Brandon is the lead author of SEC510: Cloud Security Engineering and Controls and contributed to SEC540: Cloud Native Security and DevSecOps Automation. He has also been the host of the Cloud Ace podcast, Season 1, an analyst for various SANS surveys, and a multi-year RSA Conference presenter.
Well spoken, had down to earth, applicable stories that made it crystal clear why certain vulnerabilities were dangerous and why we need to protect against them.
He has been fantastic. No words. Brilliant! Such energy and wisdom.
It is so difficult to find the right balance of people skills, nerdiness, and ability to translate difficult concepts. Brandon is fantastic.
Here are upcoming opportunities to train with this expert instructor.
Explore content featuring this instructor’s insights and expertise.
In 2026, the Cloud Security Track at the SANS Spring Cyber Solutions Fest will once again assemble leading experts and practitioners to examine the evolving challenges of cloud environments — now further complicated by the rapid adoption of AI-native workloads, multi-cloud architectures, and hybrid on-premise/cloud deployments.

Many organizations have progressed to increasingly cloud heavy infrastructures, changing the game for security professionals of all stripes. While identity attacks have existed for a long time, it was primarily used as the first step in the path to initial access into a secured network.

This event will provide you with practical solutions to these challenges from some of the world’s leading experts. We will deliver the latest tools, techniques, and procedures for cloud, multicloud, and hybrid environments.

This webcast is built on insights from one of our most anticipated cybersecurity surveys of the year—offering an in-depth look at how the community is adopting, adapting to, and defending against artificial intelligence in all its forms.

Prepare for the Next Era of Cloud Security.

Implementing cloud security controls is hard. Implementing them at scale is harder.

Cloud enthusiasts often tout how using a public cloud service provider helps mitigate ransomware attacks. Unfortunately, this is not true by default. Regardless of where files are stored, an attacker can download them, make them inaccessible to the target organization, and demand a payment for restoring their mission-critical data.

In Part 4: Evolving Cloud Security with a Modern ApproachIn this session, we'll explore how organizations can adapt their security practices to fit the dynamic nature of cloud infrastructure.
Join Brandon as he discusses widespread issues with cross-cloud integrations, this specific critical vulnerability in Microsoft Defender for Cloud, and how to proactively protect your organization from this class of vulnerabilities.
As demonstrated in the last workshop in the Aviata Cloud series, public cloud resources pose a major risk. One mitigation, Private Endpoints, allows users and workloads to connect to cloud services without internet access.

The presentation will include case studies of real cloud security breaches that were made much worse due to a lack of defense-in-depth. Learn how to prevent real attacks with controls that matter.

This study takes a fresh look at multicloud adoption trends, in the face of a looming recession, tech layoffs, and the excitement about the advancements of artificial technologies.
This talk will shed light on the modern practices and strategies essential for safeguarding cloud environments against configuration missteps and network vulnerabilities.

Organizations are becoming multicloud by choice or by chance. Many of them integrate their multiple clouds with one another to improve Availability, support Disaster Recovery, and leverage the services from each provider that best fits their needs.

Does a single set of Terraform code securely configure all cloud provides? No, it is practically impossible for any tool to work this way. Learn the real, more difficult techniques required to consistently apply security controls across CSPs using Terraform.

Review relevant educational resources made with contribution from this instructor.