SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact Us
It's going to happen sooner or later...sooner probably. You're going to be asked about your company's mobile app or a mobile app your company wants to install across all mobile devices. They'll put the request in the "yet another duty as assigned" (YADAA) category/bucket. You look at the network traffic; it's using TLS so you can't see the content. Cool, right? Maybe, maybe not. Can an attacker get man in the middle position by tricking users, or by attacking the very root of trust (well, one of the 100 or so root CAs) that is used to sign a TLS server cert? It is a complicated situation and requires a thorough understanding of several systems and protocols to address. I want you to be smart on the subject, so when that YADAA comes your way, you can answer the question knowledgeably and authoritatively. So here you go...read on.
The first installment of this two-part blog post will provide some background on TLS (Transport Layer Security) certificates so you can understand why your mobile apps should implement certificate pinning. In the second part, I'll discuss a tool that was released recently, called TrustKit, that makes it easy for iOS developers to implement certificate pinning with no change to the iOS app. (No change presumes the URLs to be protected are requested by TLS already). No analogous project exists for Android yet.
TLS provides transport encryption to protect data while in transit over a network, providing confidentiality and integrity protection against untrusted and unknown network nodes. This is a mainstay in our protection of information in transit. In addition to recent attacks against implementations in TLS/SSL, (iOS/OSX goto fail; Heartbleed; Poodle) there are fundamental trust issues within the implementation of TLS. A trusted Certification Authority (CA) is trusted to issue certificates for any resource.
The TLS handshake involves a client verification of the certificate the server provides, then an optional server validation of client certs. In practice, there is no server validation of client certificates, but the spec allows for it.
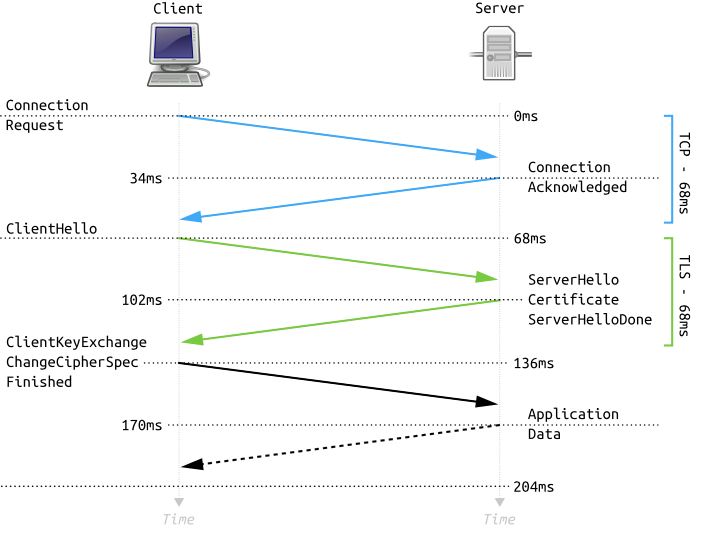
Diagram Source here
There are 5 basic items that the client validates during the assessment of the server presented certificate.
To put this in perspective, iOS 9 trusts 218 CA's:
$ curl -s https://support.apple.com/en-us/HT205205 | grep '</tr><tr><td>' | wc -l
218We've seen some attacks in the past related to certificate manipulation. We've seen scenarios of complete CA compromises that were used to issue unauthorized certs. We've seen CAs tricked into handing out certs. We've seen users fail to protect the CA-issued private keys which resulted in unauthorized certificates being issues. Below I cite two reported instances (India CCA and TURKTRUST Inc) where government organizations have issued certificates for servers in an unauthorized fashion. These two are not really a big deal, just for google.com host certificates. Also, many organizations using HTTP proxies will configure CA certs on the client end points, allowing for the transparent interception of HTTPS communication.
We've seen theoretical and in the wild attacks against TLS and its related certificate authority infrastructure and organizations. Why, there's even an RFC "Summarizing Known Attacks on Transport Layer Security (TLS) and Datagram TLS (DTLS)"
Some of my favorite failures are below. I like studying failure; it helps us to improve.
In many of the cases listed above, there was some fundamental component of the protocol or the implementation that undermined integrity of the security. Several of the attacks were entirely fraudulent certificates. You can't have endpoint protection when there is a broken implementation on the endpoint (like in the Apple goto fail;) or in the server OS (like in Heartbleed). But, we can address the frequent (2001, 2009, 2011, 2013, 2014, 2015) scenario of fraudulent certificates used in networks by requiring our mobile applications to only trust specific certificates we intend for use.
Certificate pinning is the application-specific requirement that some specific certificate or CA be required for a TLS connection, rather than accommodating any of the CAs the phone trusts. This can also be used to remove the user from the negotiation. Certificate pinning is most effective when the user is unable to override it.
For protecting your data, this is a useful thing. Is it foolproof? Certainly not. For example, there's a tweak available for jailbroken iPhones called SSLKillSwitch (https://github.com/iSECPartners/ios-ssl-kill-switch) which is a "Blackbox tool to disable SSL certificate validation - including certificate pinning - within iOS Apps." Instead of falling victim to the perfect solution fallacy, I recommend developers use certificate pinning to minimize the likelihood of data interception, while acknowledging the reality that a jailbroken or rooted endpoint is not going to provide the same data protection as a non-rooted device.
Cert pinning provides your application with a layer of certificate control that allows you to specify which certificates you'll accept, substantially limiting the likelihood of unauthorized information disclosure or alteration during network transmission. Another scenario where this may be undesirable is if your organization uses a privately issued CA to introduce a man-in-the-middle (MITM) TLS scenario for data loss protection. Google implements one of the largest certificate pinning instances in the world via its Chrome browser. It addresses this nuance by allowing the private trust store CAs to override pinning, while prohibiting the public trust store to violate pinning. Read more here.
Here's a simple example of how certificate pinning could help you to protect your organization's data. A user, alibo, reported to Google Groups that there was a cert error reported by Google Chrome. As it turns out, Google used certificate pinning capability in the Chrome browser to identify unexpected certificates signing certificates for servers in the google.com domain. Read more here.
That is a public example of detecting the DigiNotar compromise.
In my next blog installment I'll discuss the specific implementation of certificate pinning in iOS applications using TrustKit. Let me know if you found this useful on twitter @CCrowMontance.
P.S. If you like this kind of thing, you really should consider joining me for the SANS Security 575 course on mobile device penetration testing and security in New Orleans in January. We call the event SANS Security East, and it's gonna be an awesome event full of great strategies, tactics, techniques, and practical advice on securing your organizations mobile devices! I hope you can make it!


Chris Crowley, SANS Senior Instructor and SOC consultant, combines 25 years of cyber operations leadership and AI expertise to train defenders to detect, analyze, and respond to modern threats with clarity, confidence, and hands-on precision.
Read more about Christopher Crowley