SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsDavid is an author and instructor for LDR516: Building and Leading Vulnerability Management Programs.
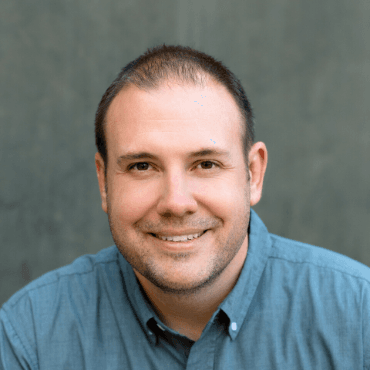
David is a security consultant based in Salt Lake City, Utah focused on vulnerability management, application security, cloud security, and DevOps. David has 20+ years of broad, deep technical experience gained from a variety of hands-on roles serving the financial, healthcare, and technology industries. In his many roles, including 3 years with a top security consulting firm, he has focused on helping integrate and automate security testing and other important security controls into both on-premise and cloud environments. He has also developed and led technical security training initiatives at many of the companies he has worked for, is an instructor for and contributor to SEC540: Cloud Security and DevOps Automation, and a co-author and instructor for LDR516: Building and Leading Vulnerability Management Programs. David holds a BS in Information Systems and a Master’s of Information Systems Management from Brigham Young University along with numerous other technical and security certifications
David Hazar: I was working for a local municipality and they dragged me into a Payment Card Industry Data Security Standard assessment for the Energy Department, which was accepting credit card payments through its website. They also had me replace their firewalls and improve their network security. After I became more established in security, I got sucked into application security because of my development background.
David Hazar: I have participated in a wide variety of IT functions throughout my career – everything from developer to server admin, network admin, domain admin, telephony admin, database admin/developer, security engineer, risk manager, and AppSec engineer. I have also worked in a wide variety of environments from startups to large enterprises and consulting. This broad range of experience enables me to understand technology from many different angles and to relate to my students regardless of their technology or company background. I also have a unique perspective on vulnerability management because most people only get to see the problems associated with vulnerability management (VM) for a handful of companies. I have worked with numerous organizations to help them understand why they are failing and what they can do to solve their problems. I integrate these stories and experiences throughout the courses I teach.
David Hazar: While vulnerability management is not the sexiest security topic, it is easily one of the most important. In fact, it’s the basis for all that we do in security. Think of how much less important such areas as penetration testing, threat hunting, and war gaming would be if we could truly solve this one problem. I love digging into VM datasets to identify root cause issues for the companies I am working with so that they truly understand what needs to change in order to succeed. I also enjoy aggregating and analyzing data in order to make more meaningful, targeted reports. Finally, automating solutions to common problems with common solutions is a big part of what I like about vulnerability management. This is what I love about Cloud it makes automating solutions so much easier.
David Hazar: Come prepared, that is, read the course prerequisites and laptop requirements, especially if you are attending SEC540; research the event ahead of time to see what SANS@Night talks and events are available; and reach out to your network to see who’s attending. Also, don’t forget to do some research on the best places to eat while you’re there!
David Hazar: It is always rewarding to see all the people who I have trained over the years, both for companies I’ve worked for and with SANS, move on to bigger and better things. One recent highlight was helping a company reduce its vulnerability count from over 12 million vulnerabilities to less than 5 million after overcoming some particularly challenging technical debt. It was not a short or painless process, but it was achieved by meaningfully highlighting the issue in order to convince the business to fund and implement the necessary changes.
David Hazar: With respect to VM and AppSec, there has not been too much change, and that’s part of the problem. While the security side of VM and AppSec has remained relatively stagnant, the IT and development landscape has shifted many times and will continue to shift in the foreseeable future. Think agile, DevOps, virtualization, containers, cloud, serverless, etc. As we move to a world where almost everything is defined in code, the traditional infrastructure VM processes and procedures will hopefully be automated out of existence. On the application security side, certain types of testing will become less meaningful and new technologies will have to emerge and mature. We are already seeing some of this with interactive application security testing and runtime application self-protection technologies.
David Hazar: I enjoy skiing and snowboarding with my family (when they agree to be seen with me!), watching my daughter play high school basketball, cooking/eating, and reading.
David Hazar: “I don't talk to myself because I'm crazy." "No?" "I do it because I'm awesome.” - Brandon Sanderson, Words of Radiance
Read more about David Hazar.
Learn more about LDR516: Building and Leading Vulnerability Management Programs
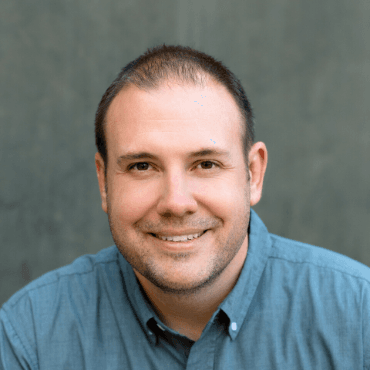
David has 20+ years of experience in vulnerability management, application security, and DevOps. He's developed technical security training initiatives, and believes vulnerability management is one of the most important foundations of cybersecurity.
Read more about David Hazar