SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsIn part three of this mini-series on phishing benchmarks, we'll focus on internal benchmarking through comparison analysis.
Part three of this series will focus on internal benchmarking, performed by comparing different entities within your company or enterprise. Typically, the goal of internal benchmarking is to gain a better understanding of those entities in your company that are doing well and vice versa. With phishing simulations, you’re able to analyze the results to see which groups or teams are responding well to phishing simulations, and which may need additional opportunities to boost awareness. Internal benchmarking will be dependent on your company structure, the layout of your organization, departments, business units, regions, teleworking, access to awareness and training materials, and even time in band.
Internal benchmarking may seem easier to tackle at first brush, with a common set of characteristics that are most likely similar throughout the company. This allows us to plan accordingly:
Other factors and tactical aspects of internal benchmarking may require thought, strategic planning, and historical trending (if available). Consider:
As with external benchmarking, comparing “apples to apples” is important when validating the results. The last blog on benchmarking addressed tiering, ensuring the validity of benchmarks by comparing “apples to apples.” The difficulty of the phish, how many indicators present themselves, how hard to distinguish and isolate as a phish—these should all be considered when utilizing benchmarks as an analytic tool providing just one evaluation of your phishing program.
Based on this tiering concept laid out below, we can see how one simulation might fit all employees within the company, but a more advanced simulation may not.
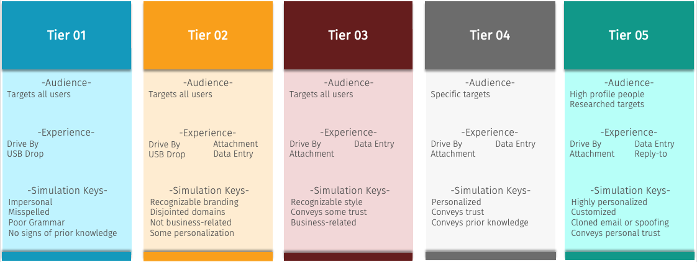
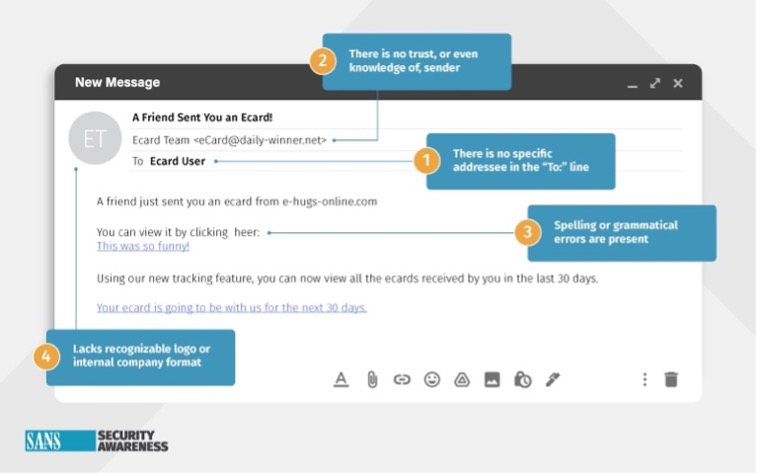
A Tier 1 or 2 would be appropriate for the entire workforce, as these are typically not business-, role-, or skill-related as in the example below.
A Tier 3 or 4 on the other hand, might not be appropriate for the entire workforce. These more sophisticated options may only apply to specific groups or roles across the organization and are more business-related while often conveying trust or prior knowledge. The sanitized example below would be appropriate for those with company-issued laptops, possibly resulting in a higher undesired action rate than those employees with no company-issued devices (and would hopefully result in a higher report rate).
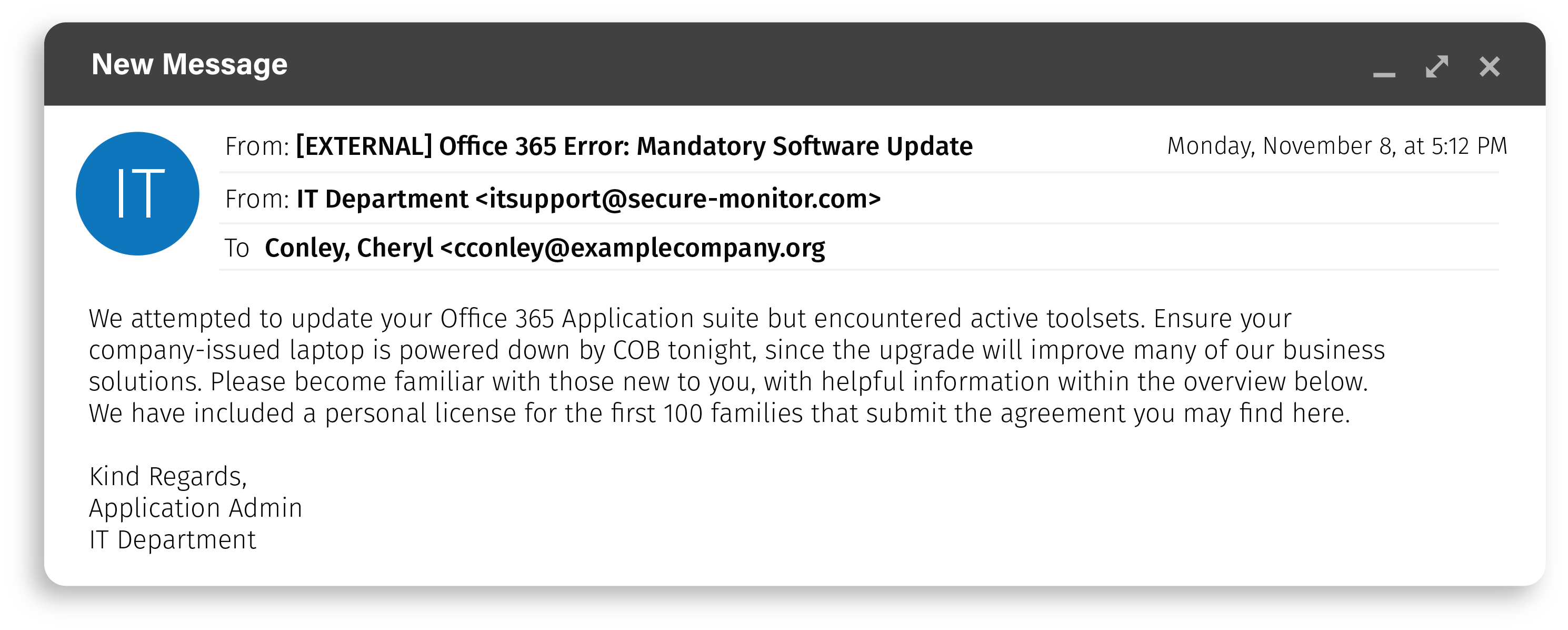
In all cases, it’s imperative for the workforce to have had exposure to awareness and training materials. This would not be appropriate if this group had many new employees, who were just issued a new device and have yet to have availability of awareness materials.
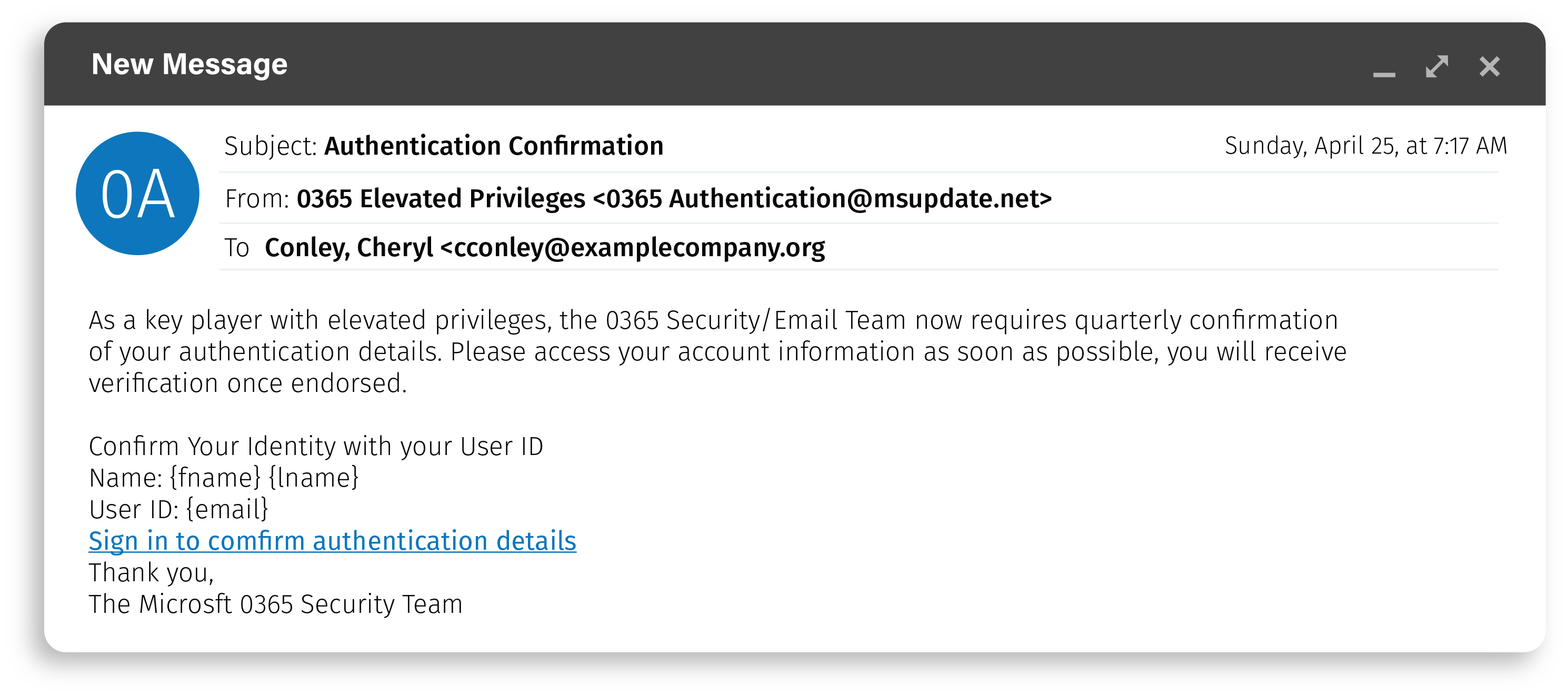
While the above example was based on a situation, the phish below is aimed at a specific role. The employees targeted here hold elevated and advanced credentials or authorizations.
Another factor to consider is the diversification and distribution of awareness and training materials. If you have a wide range of demographics, ensure that your teachable moments are meaningful and understandable across your workforce. We all learn and consume information in different ways; some by print, others by video or interactive options. Also consider, if applicable, the localization and varying cultures of your benchmark groups, along with the physical location. On-site availability of awareness and training resources might be more diverse than for your remote workforce or even those with a hybrid setup. Your benchmark data will be more valid if you’ve incorporated diverse awareness and training methodologies.
How your stakeholder, management, and leadership teams handle security awareness is also a factor to consider when assessing internal benchmarking data. While we hope that all levels of managers and stakeholders—such as HR, Communications, or IT—understand the importance of improving cyber security and social engineering skills. Often, a leader's background, priorities, and limited resources impact that focus. A remote field supervisor might feel differently about proper cyber behavior than an IT leader, and a dedicated program manager missing schedule dates may not promote security awareness as much as they should.
Internal benchmarking is a valuable tool, as comparing metrics allows you to leverage those findings to entice the workforce into being more aware while developing the skills to recognize and report a phish attempt. Some options to compare include:
Your security teams can also provide suggestions on target groups to benchmark, and they often have the resources to pinpoint the most vulnerable employees. In addition, your phishing program historical data can uncover weak departments, teams, and other areas that would benefit from additional training opportunities.
Cheryl Conley is a phishing and security awareness SME, with the CISSP (Certified Information Systems Security Professional) and SSAP (SANS Security Awareness Professional (SSAP) certifications, along with a Master’s degree specializing in Information Security.
Read more about Cheryl Conley