SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsHow to approach, research, and develop analytic assessments on emerging technologies and threat trends (Part 1)

“The human mind tends to see what it expects to see and to overlook the unexpected.
Change often happens so gradually that we do not see it or we rationalize it as not being of fundamental importance until it is too obvious to ignore.
Identification of indicators, signposts, and scenarios create an awareness that prepares the mind to recognize change.”
–The Dutton Institute
Introduction
Cyber Threat Intelligence (CTI) analysts are all too familiar with receiving daunting, perhaps un-scoped or seemingly irrelevant requests from their leadership team. These questions usually take some variation of the question, “I just read/saw on the news/was told about X. Should we care about this?”. X could represent a breaking cyber event; a vendor’s newly published assessment on FUZZYSNUGGLYDUCK; a new technology, trend, security advancement; government policy decisions; or some other flavor du jour. The sheer range of topics this question could cover and the breadth of subject matter expertise required to provide a satisfactory answer makes this cringe-worthy when analysts hear the start of the question…”Hey, I just read this article and was just wondering if…”
However, underpinning this ask is often a sincere inquiry and your leadership team’s implicit endorsement in the caliber of the CTI team, its members, expertise, agility, and adaptability. Part of this is also the unspoken expectation that the CTI team will understand how to answer the should we care about this question, which requires a fair degree of business acumen and understanding organizational priorities. Distilled to its most basic parts, its leadership’s desire to understand whether X would shift the organization’s overall risk posture; whether existing security controls are sufficient to control the risk; what we are doing about X; or if additional investment is required in people, processes, or technologies. One of the trickier topics analysts sometimes struggle to provide adequate answers to is when this question focuses on emerging technologies, advancements, or general adversary trends.
This two-part blog series will focus on assisting CTI analysts in how to approach, research, and develop analytic assessments on emerging technologies and threat trends. This first blog post covers systems analytic thinking to understand the multiple dimensions in which there could be implications for the business to incur additional risk as a result of a new technological advancement or general threat trend. The second blog post will examine a handful of “cyber” advancements over the past decade, how we can use mental models and Structured Analytic Techniques (SATs) to help us frame our response, and other considerations when crafting future oriented analytic assessments.
Emerging Technology Asks are Complex
Emerging technologies are of foremost interest to organizational leadership, but they often realize that they are not the experts on the topic or its implications, so they seek your counsel as the big brains more familiar with the topic. Cyber security leadership, the executive team, the board of directors, and risk management expect that we will provide our opinions on how this X will impact business operations moving forward, change the risk posture and organization's present security or threat model, require additional levels of investment, or otherwise will provide efficiency gains to existing workflows.
The challenge when trying to answer this type of request on any sort of new advancement is that it requires a steep knowledge base not only in cyber security and understanding cyber threat actor tradecraft and trends therein, but also having at least a cursory understanding of broader, multidimensional effects, too. On a micro level, we would call this type of thinking “systems analysis” whereby we seek to understand the various dimensions of a series of systems, the interconnections, dependencies, and relationships between them all. Yet, this systems analytic thinking also acts as a way to help us ground and structure our thoughts. I’ll use the rest of this blog post to provide a perspective on how to begin to answer these types of questions from our leadership team that includes various considerations we should be mindful of like timing the analysis to align with business priorities and how to craft a message that resonates with consumers.
A Common Understanding
Organizations strive to make informed decisions on technology integration, human capital, organizational structure, internal processes, and many other areas to drive down risk to an acceptable level that empowers the organization to pursue its defined mission, vision, and goals. While a fulsome dissection of risk management is outside the scope of this blog post, we provide a high-level understanding in this section to introduce the drivers behind why security operations and cyber threat intelligence exist in the construct of an organization's hierarchy.

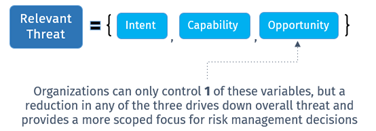
Due to the complexity of the topic, let’s focus on a primary component of risk—and the one that CTI analysts are typically most familiar with—threat. The idea being if we have a strong understanding of the composition of a threat, we can more easily rationalize how it fits into the broader risk context. We can then apply this understanding to advise leadership on various courses of actions it can take to drive threat reduction and ergo reduce risk in kind. So, a natural question arises: with the seemingly ever-increasing number of cyber threats that exist, how can an organization bound its focus to only those cyber threats that are relevant to it?
At its core, organizations can determine relevant cyber threats using a rather straightforward formula defined by three functional inputs: Intent, Capability, and Opportunity.
So where do emerging technologies fit into this equation? Both adversaries and organizations may elect to adopt a new technology into their existing workflows, sometimes for the same reason – to improve efficiency gains or otherwise support execution of an overall mission. Thus, when evaluating the risk of emerging technologies, organizations should consider how the technology presents as a potential adversary capability or increases its exposed attack surface.
Broadening Our Aperture
Let’s briefly revisit system analysis, which at its core is the process of studying how a system, institution, or business operates; identifying procedural elements; and what internal and external factors could impact the system, institution, or business' operations. This process is important because it helps organizations make decisions to streamline operations, increase efficiency, reduce costs, act on uncertainty (risk), and ultimately achieve their business objectives. Identifying the factors that influence systems analytic decisions, especially as it relates to risk, often leverage threat modeling to enumerate these factors. So where do we start when trying to model potential factors relating to emergent technologies? How can we assist in offering business justification for technological adoption, restricted use, or a decision to outright block usage within a corporate environment?
One approach could involve using existing mental models, templates, and prototypes as a known reference point. Most of us don’t have time to reinvent the wheel, so leveraging known-knowns help us bin, group, and organize relevant information. Threat modeling is no different.
Last month at the Forum of Incident Response and Security Teams (FIRST) CTI Symposium, Natalie Kilber gave a stellar keynote that used the NASA developed Technology Readiness Level framework to determine whether an emergent technology is over-hyped and the timescale in which an emergent technology may become commercially viable. In her talk, Natalie uncoupled technologies into three different categories based on their application—consumer, military, or dual-use—before providing a deeper examination on the quantum cryptography threat. Each of the categories has different development timelines, underlying funding streams, and market viability.
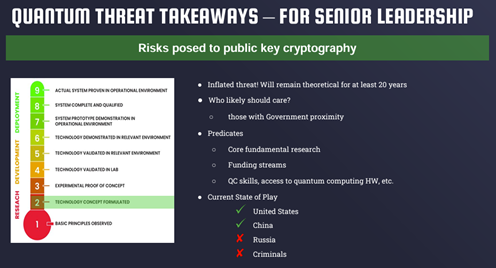
Figure 1: Natalie's Quantum Threats Assessment
If we perform a more fulsome examination on the categories Natalie identified, we quickly spot similarities and differences impacting drive to market. One additional consideration not noted explicitly thus far is technology refresh cycles and shifts in underpinning technologies. Wholesale shifts in military technology innovation like weapons systems occur at a much slower pace than commercial technology, at a rate of 5-10 years or longer versus magnanimous shifts in the cyber landscape which happen roughly every 2 years.
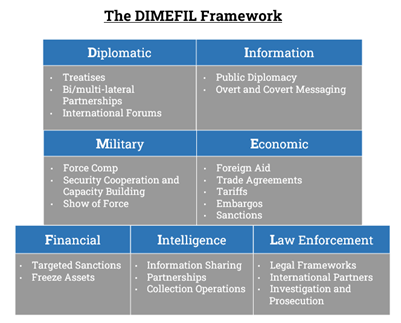
Figure 2: DIMEFIL Framework Overview
In late November, Robin Dimyanoglu published a blog post entitled "Geopolitical Cyber Risk: Going Beyond the Industry and Region" that used a DIMEFIL-like framework to create a threat model for a fictious organization. In it, Robin provides organizations with an understanding of how to assess relevant cyber threats using a forecasting system that maps to the motivations, intentions, mission mandate, and priorities of state-sponsored offensive cyber programs. Unto itself, it provides a blueprint that leverages mental models and frameworks to help organizations when creating their own organizational cyber threat profile. Also consider Scott Small and Tidal Cyber’s “Ultimate Guide to Cyber Threat Profiling Assets“ and ENISA’s “Cyber Threat Landscape Development Methodology” when developing an organizational cyber threat profile.
One final illustration I have found particularly handy when it comes to thinking about all the relevant categories to consider when building a threat model—and when communicating the inter-relations—is the following graphic we use in the FOR578 course before students begin a threat modeling lab:
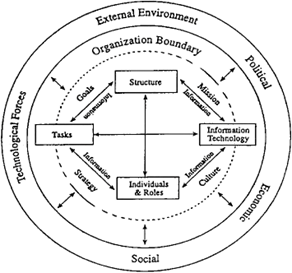
Figure 3: Illustrative Systems Analytic Categories
Conclusion and Path Forward
While there is no magic bullet solution on how to answer a question about emerging technologies and threat trends, this first blog post hopefully provided some insights and perhaps starting points on the various dimensions to consider when starting your research. The next blog post will examine a handful of shifts in the “cyber” landscape over the past decade, posit a framework for baselining, identify future oriented SATs that build on our systems analytic dimensions, and cover key considerations on when and how to write the analytic assessment on emerging technologies and threat trends.


John has over sixteen years of experience working in Cyber Threat Intelligence, Digital Forensics, Cyber Policy, and Security Awareness and Education.
Read more about John Doyle