SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
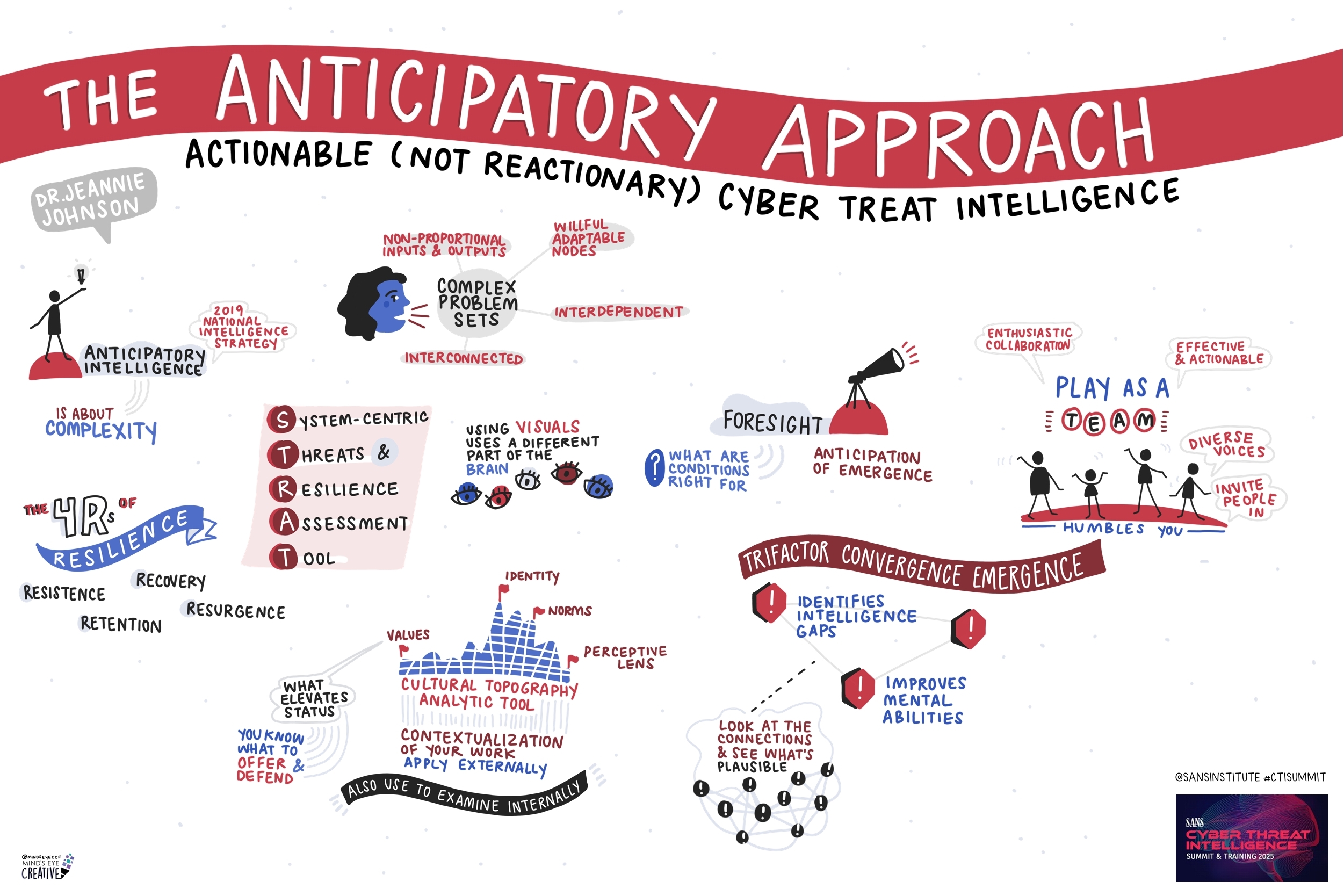
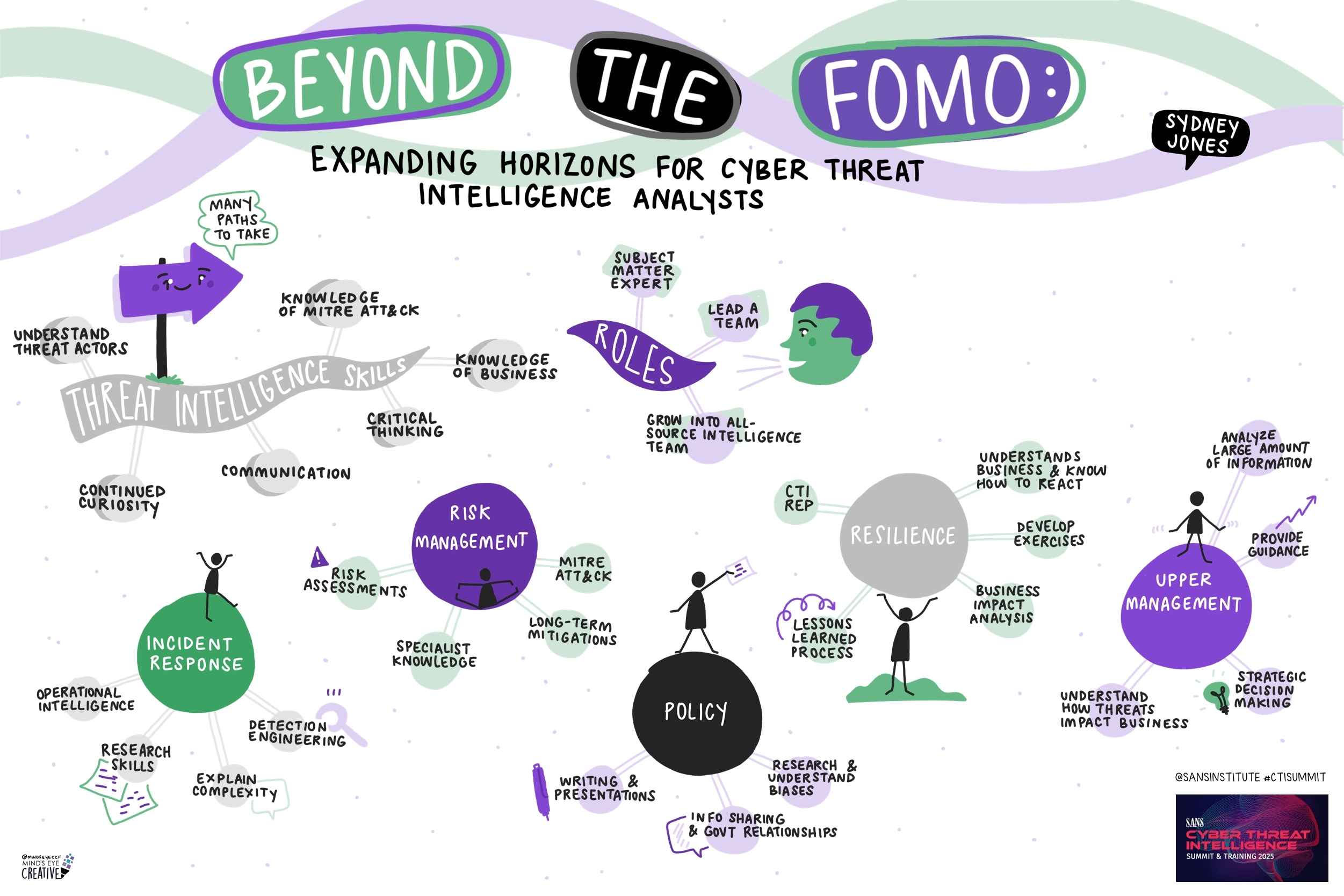
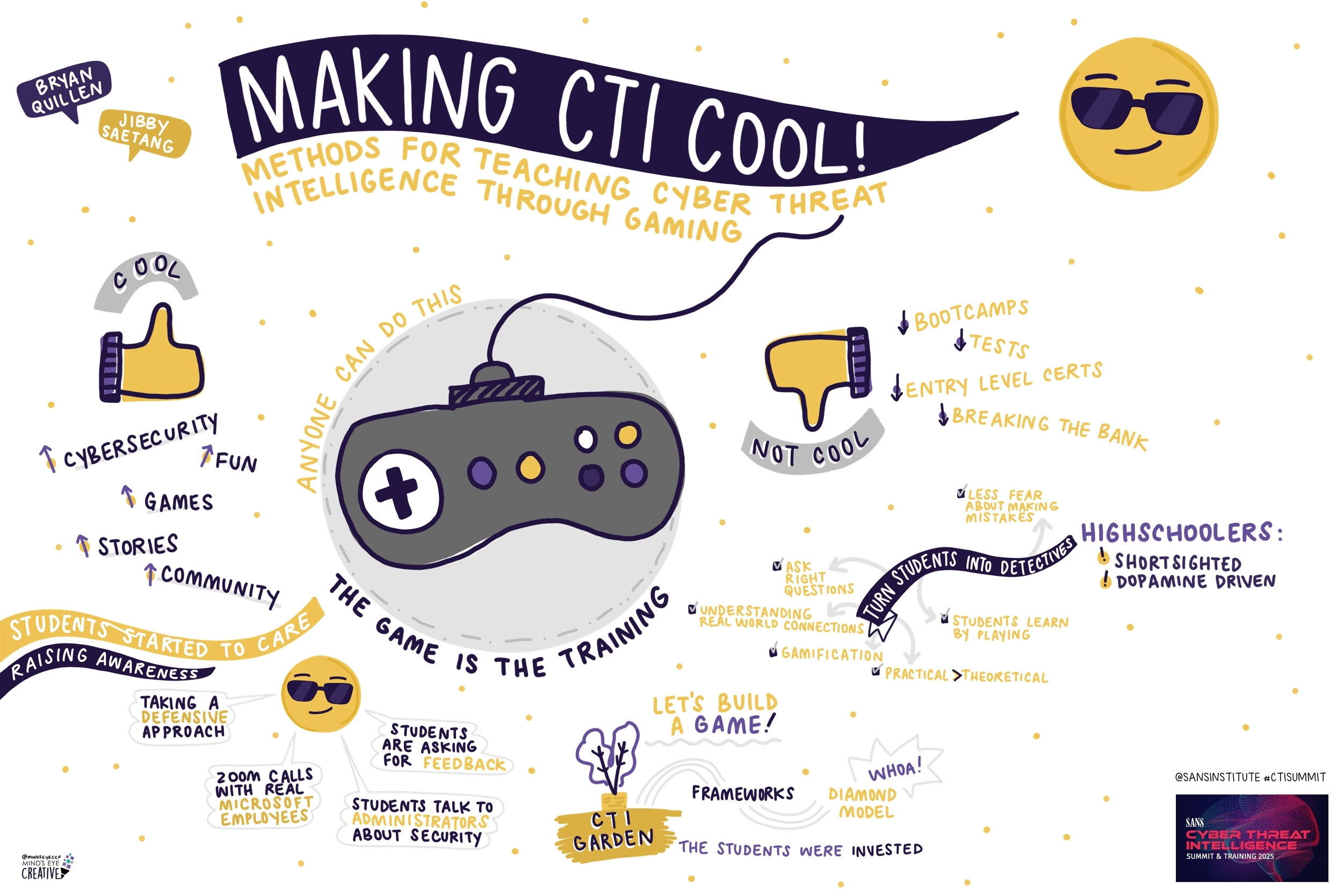
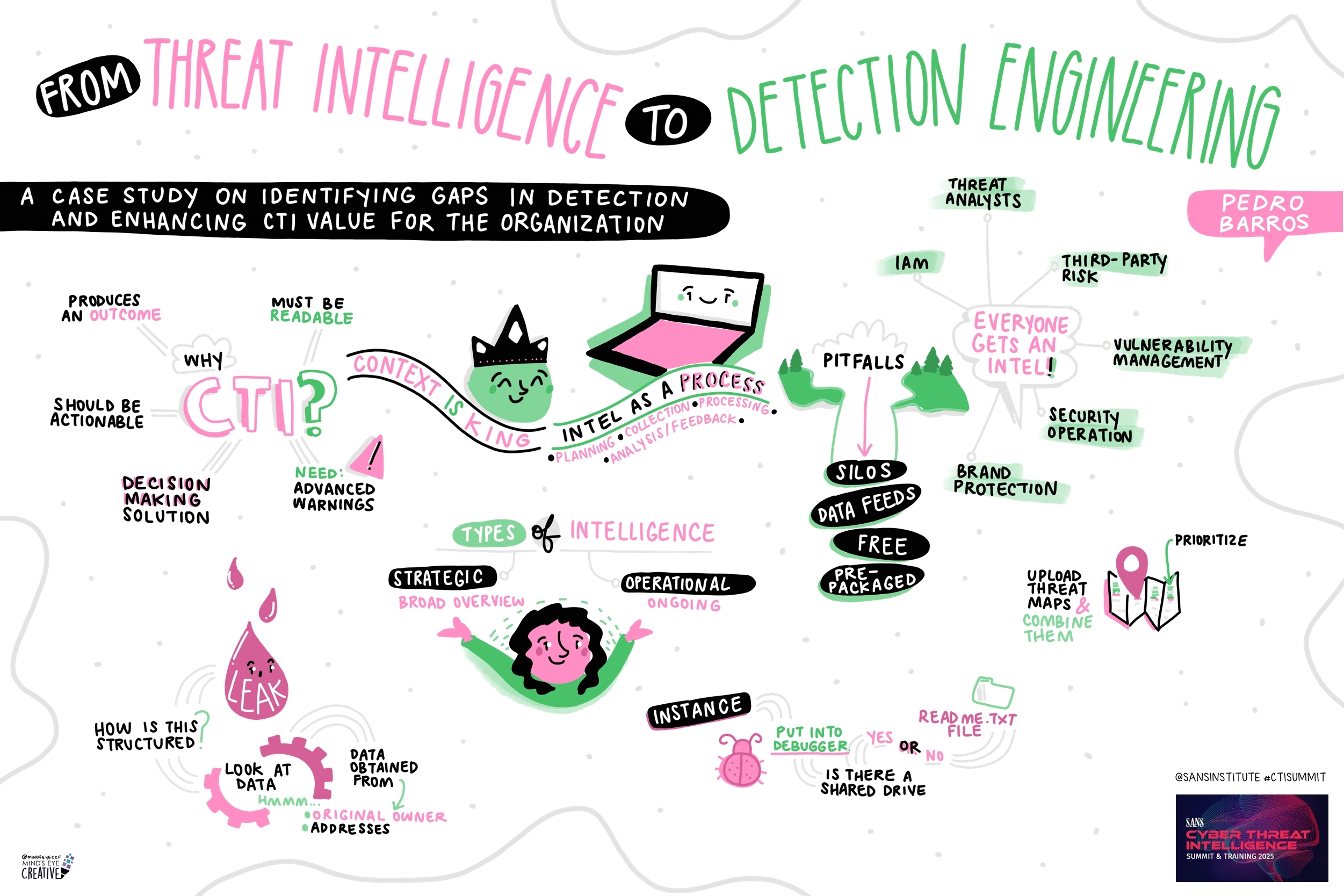
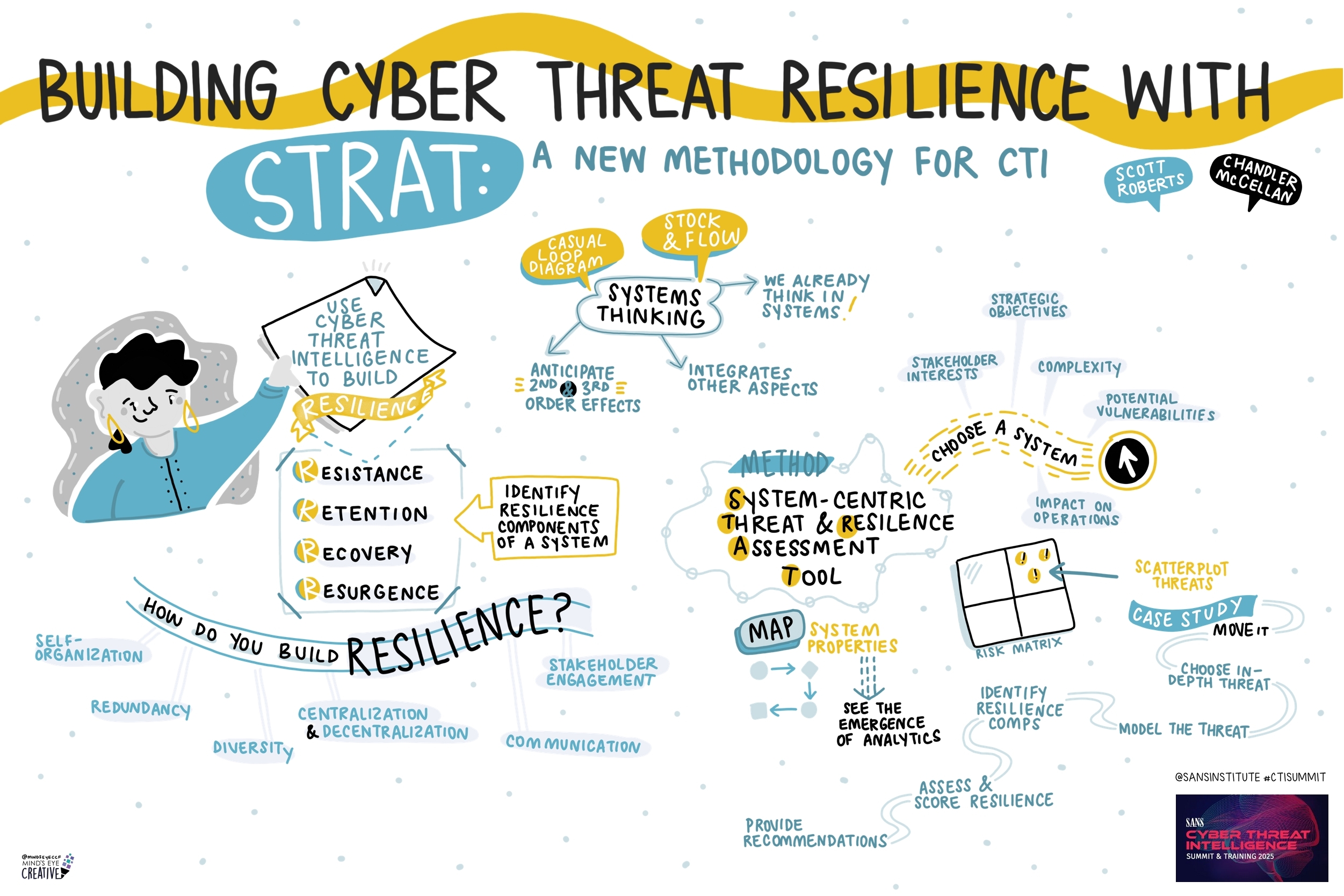
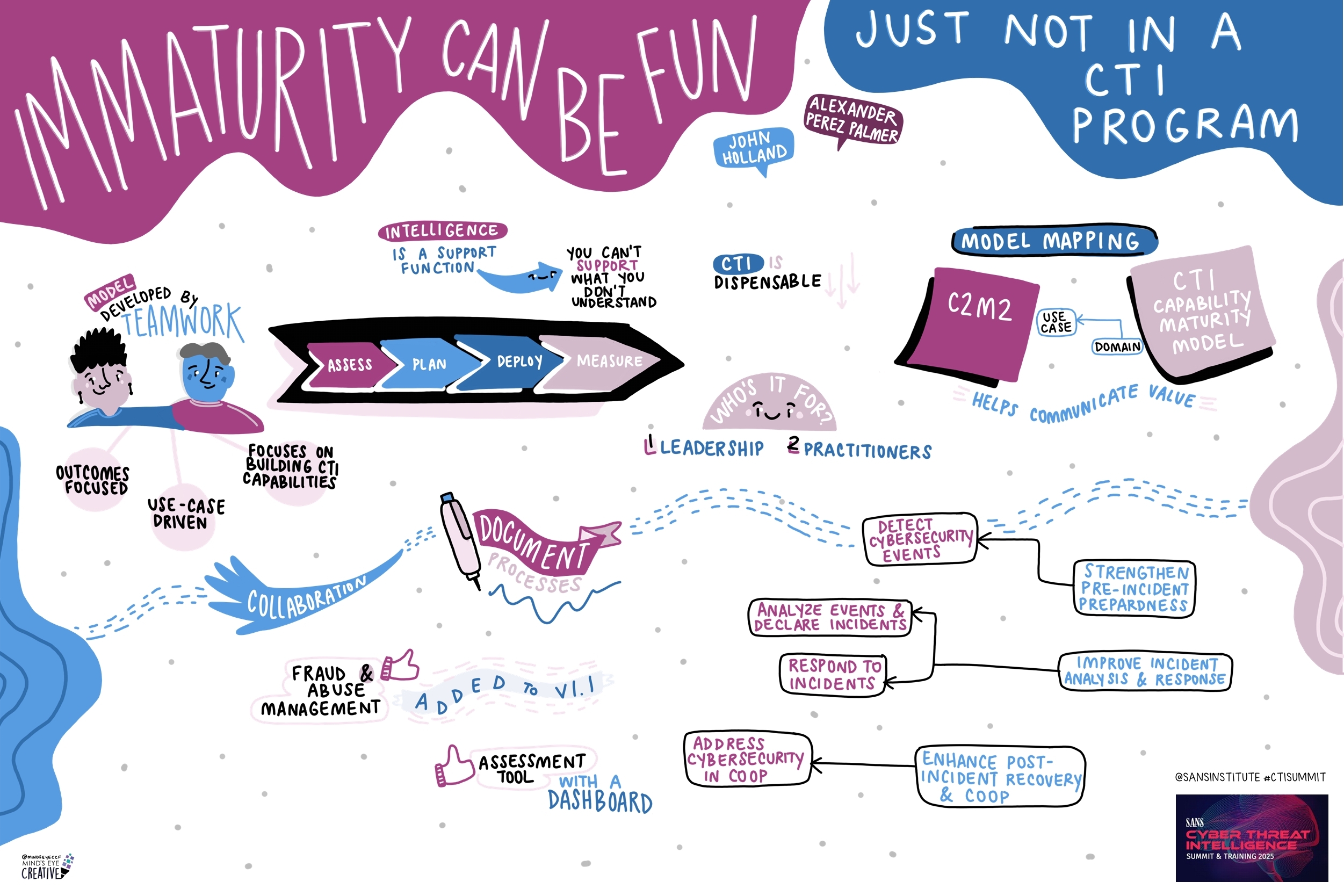
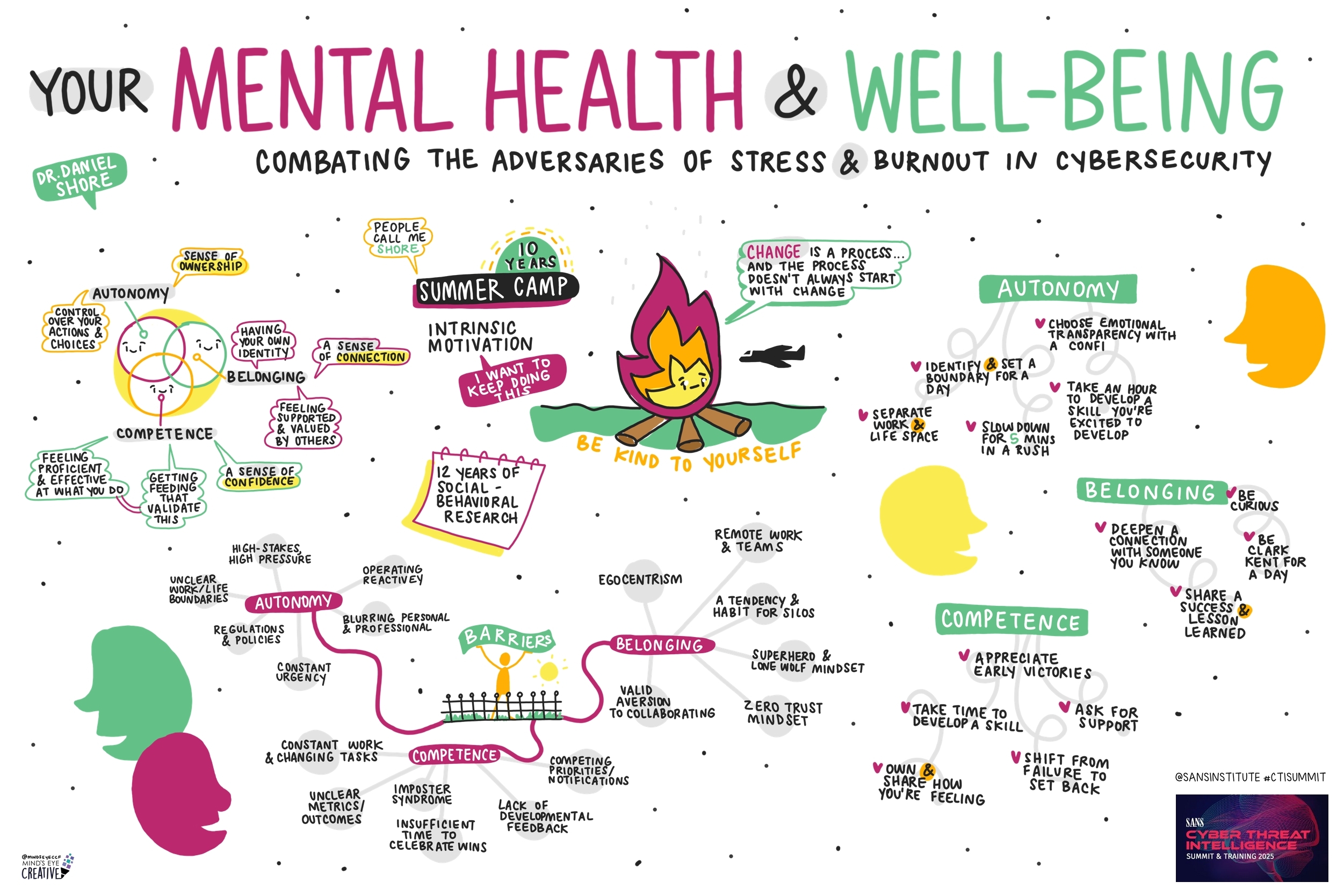
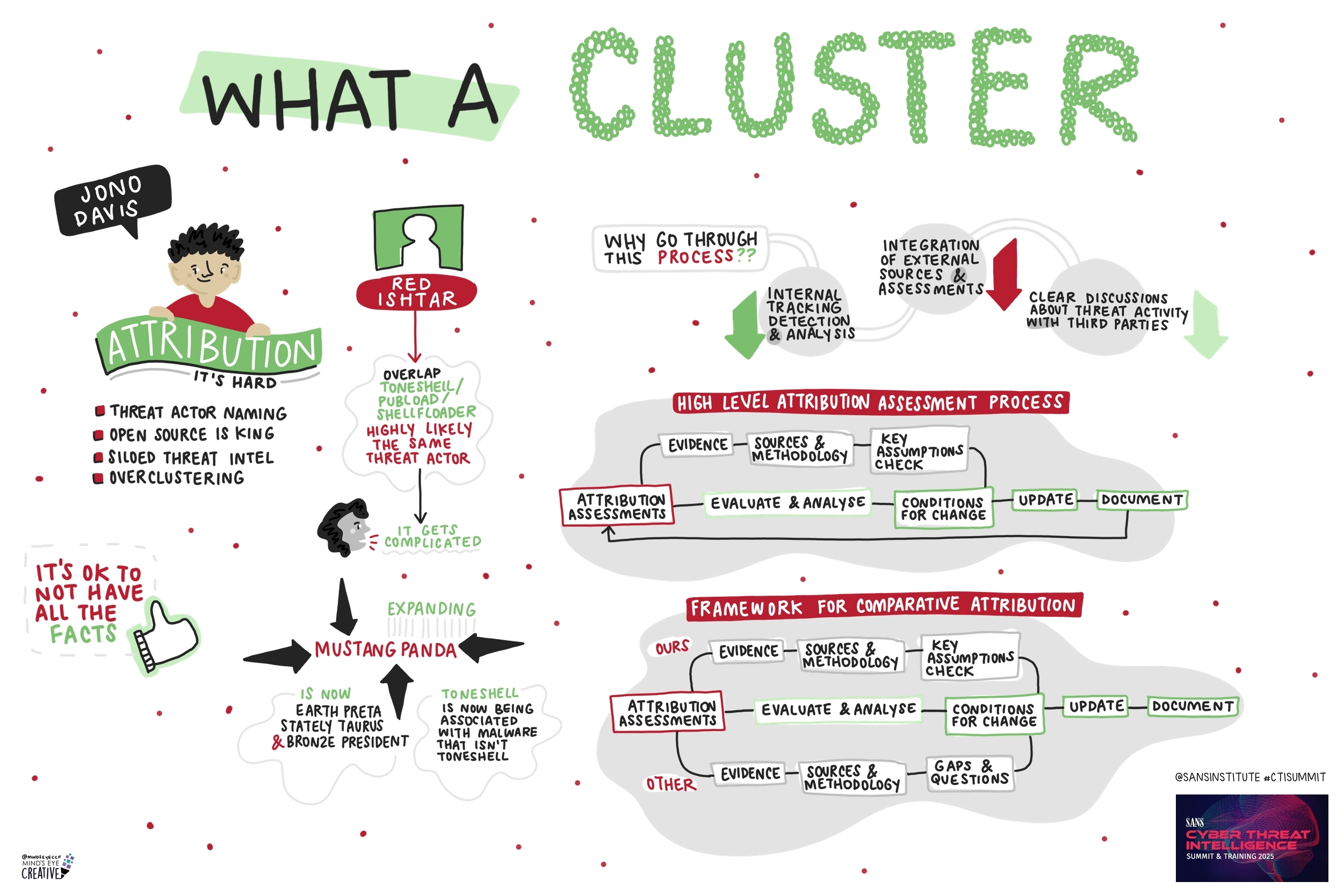
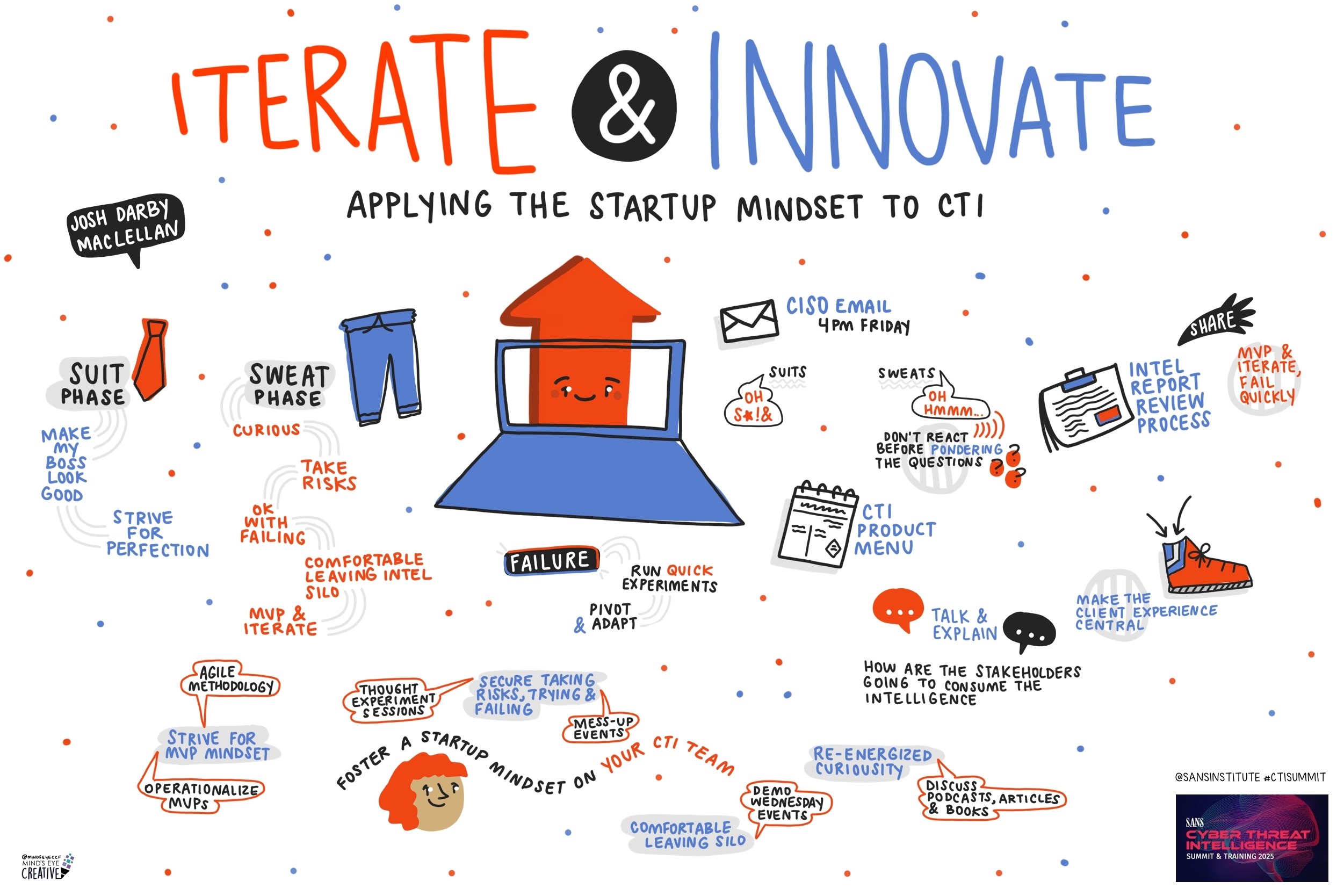
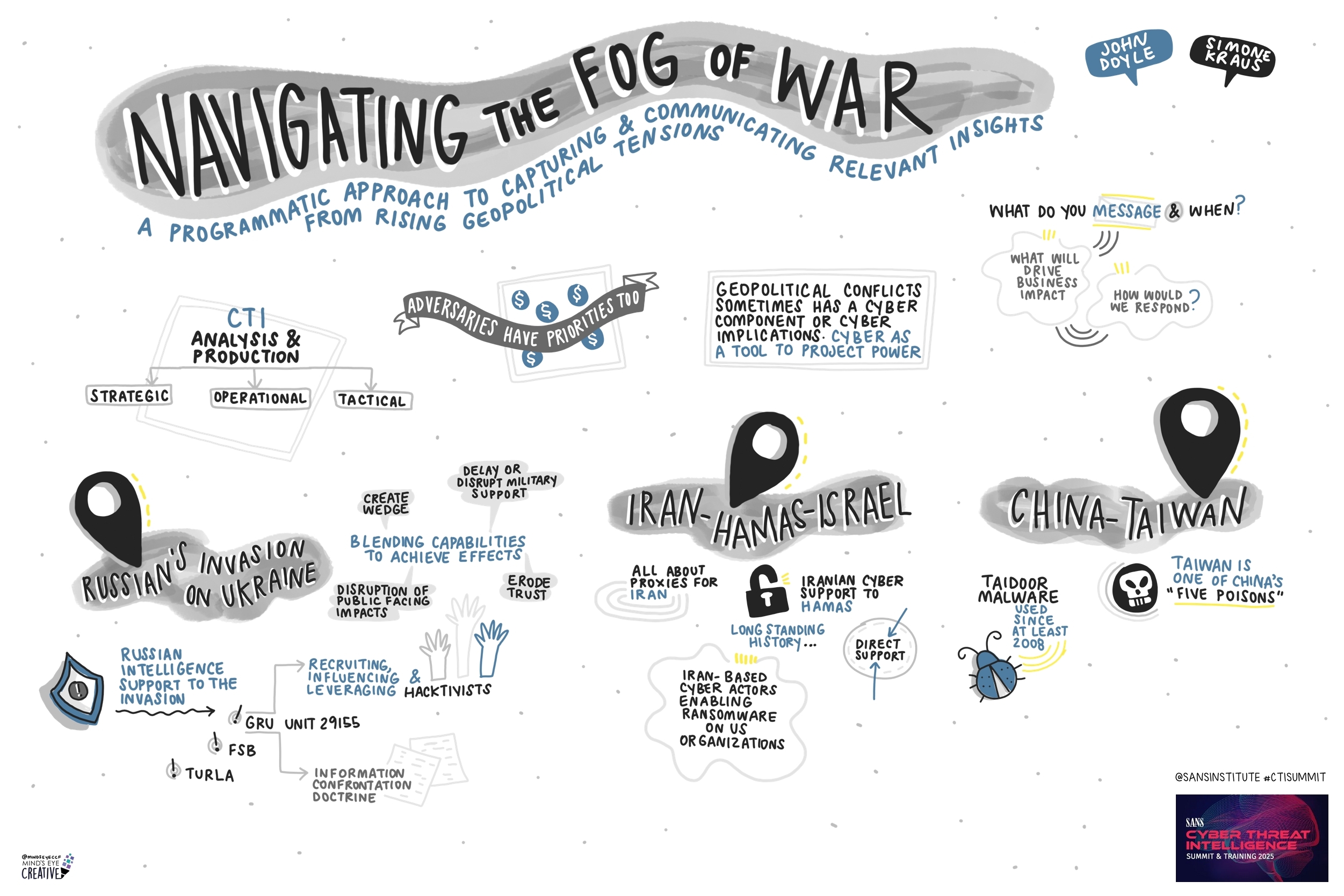
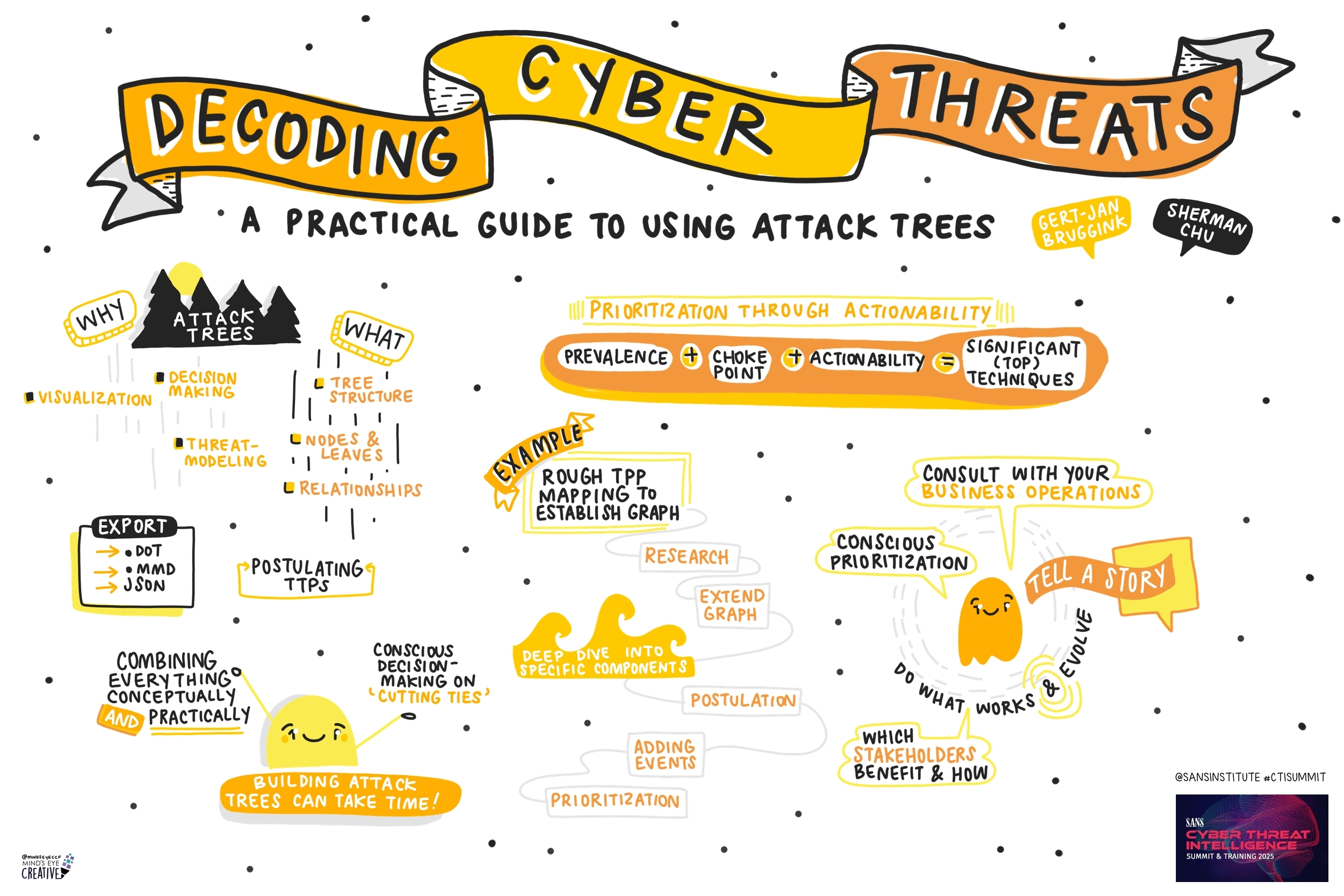
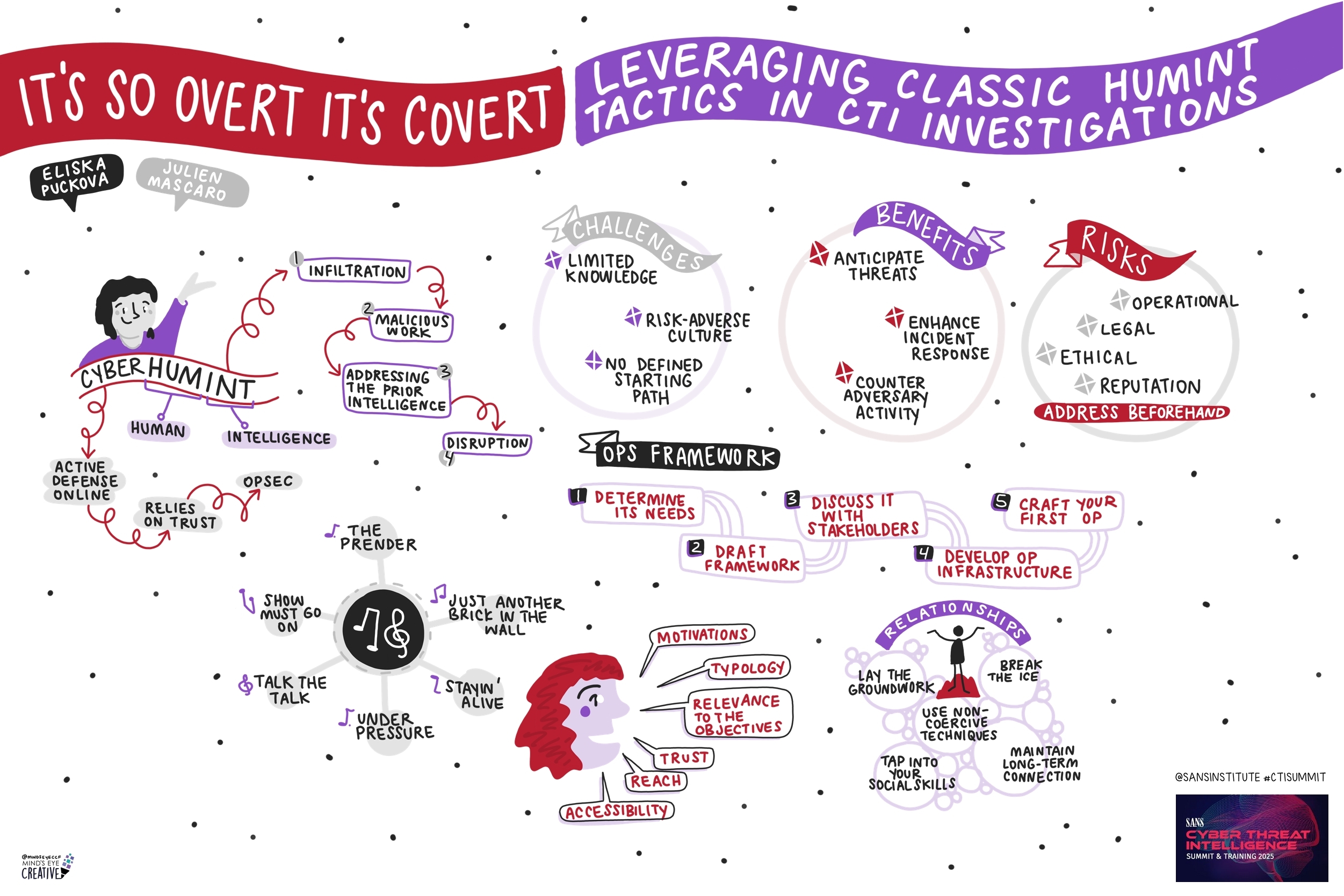
Contact UsCheck out these graphic recordings created in real-time throughout the event for SANS CTI Summit 2025

On Jan 27-28, attendees joined us in Alexandria, VA or tuned in Live Online for the SANS CTI Summit!
We invited Ashton Rodenhiser of Mind's Eye Creative to create graphic recordings of our Summit presentations. If you missed a talk or are looking to view the Summit through a visual lens, take a look at the recordings below.
*If you registered for the Summit, video recordings are available on your Summit Access page in your SANS Portal.

Jibby Saetang, Security Researcher , Microsoft (GHOST) & KC7Cyber
Lior Rochberger, Senior Threat Researcher, Palo Alto Networks

Chandler McClellan, Student, Intrusion Analyst Intern, Utah State University, CrowdStrike
Alexander Perez Palma, Lead Threat Intelligence, Workday
Simone Kraus, Senior CSIRT, Orange Cyberdefense

Julien Mascaro, Security & Forensic Investigator, Ubisoft
If you'd like to check out our other upcoming Summits, you can view the latest listing here.


Launched in 1989 as a cooperative for information security thought leadership, it is SANS’ ongoing mission to empower cybersecurity professionals with the practical skills and knowledge they need to make our world a safer place.
Read more about SANS Institute