SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsThis blog post discussed techniques implemented across the kill chain, from initial access to lateral movement to impact.

On 8 August 2023, cybersecurity vendor CrowdStrike released their annual Threat Hunting Report. It shared the trending tactics, techniques, and procedures (TTPs) leveraged by adversaries against victim organizations observed by the CrowdStrike Threat Hunting team over the last 12 months. One of the focuses of the report was the rise of cloud exploitation, with a 95% increase in cloud exploitation and 3x increase in cases involving cloud-conscious threat actors. Some of the key takeaways from this report are:
In this blog post, we’ll dive deeper into these key takeaways and how organizations can leverage these insights to better protect themselves.
Identity and access management (IAM) is the cornerstone of every organization’s cloud security. IAM provides the framework for defining who can access what through the use of roles, policies, and permissions. As such, IAM is a key focus of threat actors when trying to gain initial access, escalate privileges, or move laterally in victim environments. This fact is backed up by CrowdStrike’s finding that among interactive attacks (both cloud and on-premise), 62% of intrusions involved the abuse of valid accounts. Additionally, the use of valid accounts was one of the top initial access methods observed in cloud attacks.
There are many ways a threat actor can obtain and abuse valid cloud accounts. Traditional methods such as phishing attacks may lead to the disclosure of credentials by users, while reconnaissance tools can be used to uncover improperly secured cloud credentials on endpoints or in code repositories. Even if the account has limited privileges, this becomes a stepping stone for the attacker to reach their ultimate objective.
As mentioned, initial access is not the only place in which abuse of IAM credentials is observed. Once in a cloud environment, observed threat actors primarily focused their discovery activities on cloud accounts. If they were able to compromise a cloud endpoint, they typically targeted credentials left in files on the system, although the abuse of cloud provider’s instance metadata services (IMDSs) gained prevalence, with a 160% increase in attempts to gather credentials from the service’s API. SANS Cloud Security author Ryan Nicholson recently updated his blog post documenting this tactic along with defense mechanisms. Additional credentials obtained post-compromise were the primary method through which the actors escalated privileges and moved laterally.
When it came to initial access, besides leveraging valid accounts, exploiting public-facing applications was another popular technique. Organizations may be under the misconception that with their applications hosted in the cloud, responsibility is shifted to the cloud provider to provide some level of security for their applications. This, however, is not the case when we look at the shared responsibility model, specifically for IaaS and PaaS services. Amazon provides a great explanation of what responsibility falls onto the customer vs. themselves in their shared responsibility model graphic, found in their documentation here and shown in Figure 1 below.
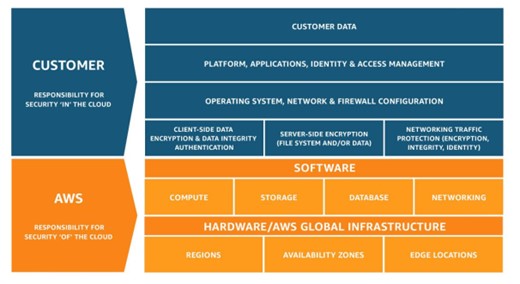
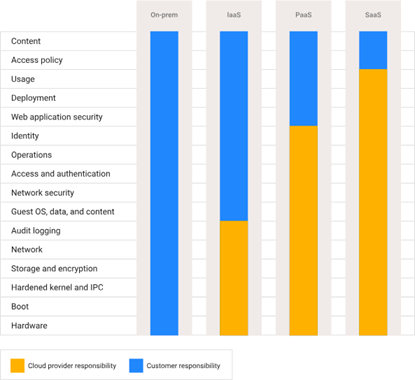
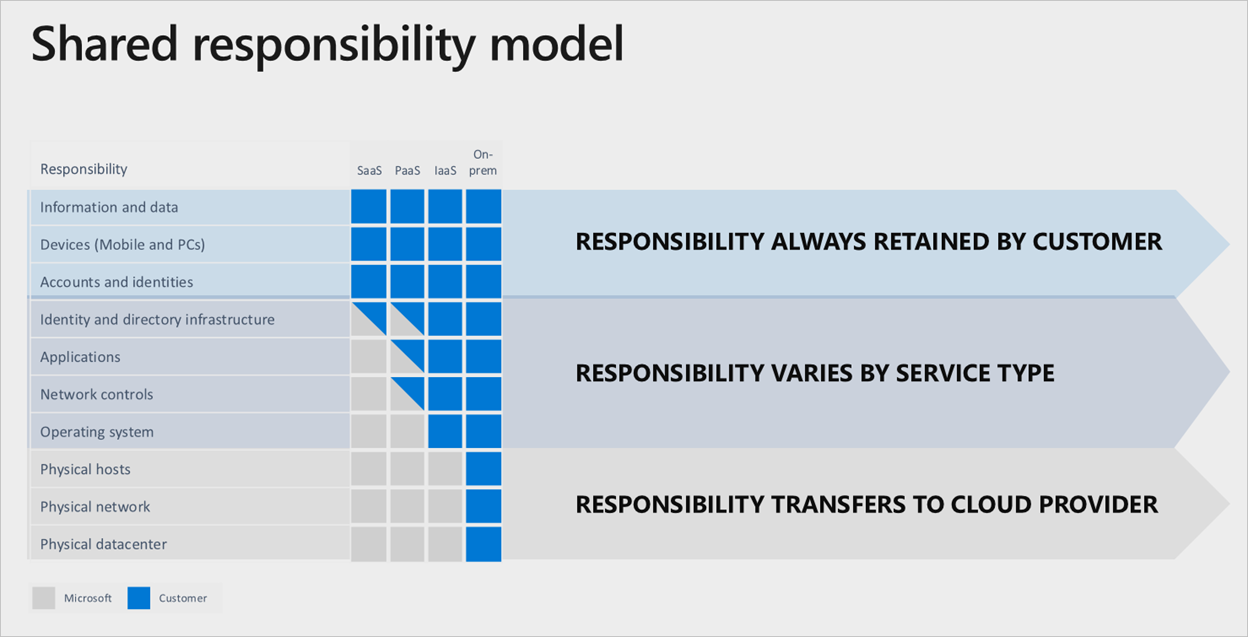
AWS itself takes responsibility for the security of the cloud. This means that the security of the infrastructure, such as the physical data centers and the hardware inside, as well as the actual services provided, such as the software providing EC2, S3, and all their other services, is their responsibility. The customer, however, is responsible for security in the cloud. Whatever the customer builds on top of the cloud infrastructure and services provided by Amazon falls must be secured by the customer, not Amazon. Google Cloud and Microsoft Azure have similar shared responsibility models, as shown in Figures 2 and 3.
From a public-facing perspective, an application looks the same whether it’s deployed on-premise or in the cloud. In the same way, to an attacker, a target application is the same deployed on-premise or in the cloud. The application has the same vulnerabilities no matter where it is hosted. Amongst the confusion of the shared responsibility model and all the moving parts involved in a cloud migration, however, the organization might lose sight of the need to move their vulnerability management procedures to the cloud too. CrowdStrike’s observations show that vulnerable applications continue to be available for exploitation, regardless of the move to the cloud.
Especially when it comes to advanced persistent threats (APTs), the confidence threat actors have in pivoting in hybrid environments is growing, with CrowdStrike sharing three in-the-wild incidents where threat actors pivoted from on-premise to cloud or vice versa. Many organizations remain in a hybrid format, where some of their resources have been migrated to the cloud while on-premises assets, especially user endpoints, still exist. Due to the need for these environments to be connected to some extent, there are pathways through which attackers can pivot between the environments depending on their motives.
We already mentioned when discussing IAM how cloud credentials can often be found in files. When endpoints or their users are interacting with the cloud from an on-premise host, credentials may be saved to the system in some way. Not surprisingly, CrowdStrike found threat actors identifying these credentials during reconnaissance and using them to connect to the cloud. In the other direction, threat actors have been observed using cloud management tools to execute commands from cloud environments to user endpoints in order to install malicious software.
It is important that, while assessing cloud security, organizations take into account the risks that their hybrid infrastructure may introduce. When looking at the two environments as separate entities, organizations may unknowingly be ignoring a bridge that could allow threats to propagate further.
A major motive of threat actors since the beginning of cloud exploitation has been resource hijacking. One of the most common uses of these resources is crypto-mining. Research has shown that crypto-mining is not a profitable activity when hosted in the cloud. Threat actors, however, are happy to let an organization foot the bill for resource utilization while mining cryptocurrency into their own wallets. The attacker simply needs the ability to create a virtual machine or container, or the ability to install software on an existing machine or container. From that point, the miner will do its job until the organization becomes aware and is able to remediate.
While public reporting has continued to claim that this is the most common impact technique used even through 2022, CrowdStrike’s observations told a different story. In their findings, the biggest impact technique was actually destructive behavior. The specific actions taken included removing access to accounts, terminating services, destroying data, and deleting resources. The motives here can range from simply wreaking havoc on the target organization and its reputation to financial gain through extortion campaigns. We have, in fact, observed the start of so-called “ransomware in the cloud” where threat actors steal files found in cloud storage, delete the files, and leave behind a ransom note demanding a ransom in exchange for the return of the stolen data.
This change in primary motive from resource utilization to destructive attacks is significant. An organization may take a financial hit paying for the resource utilized in a crypto-hijacking campaign, but the risk is much higher when actors instead start deleting data, locking accounts, and terminating services that are potentially critical to operations.
In an ideal world, all organizations will fully secure their environment and not fall victim to cloud-conscious threat actors. In reality, however, this is not feasible. Even with mitigating controls in place, threat actors will evolve and find new ways to evade defenses. That is the reason for the creation of SANS FOR509. The goal of this course is to prepare incident responders for the inevitable rise of cloud compromises and teach them how to investigate cloud-specific evidence.
This blog post discussed techniques implemented across the kill chain, from initial access to lateral movement to impact. One of the goals of FOR509 is to teach responders how to look into all these different aspects of cloud attacks, including investigating IAM logs, analyzing service-specific actions being taken, and understanding resource-level activity in logs.
https://images.contentstack.io/v3/assets/blt36c2e63521272fdc/blt7681227400dbbb3b/64de3c584eb700227af7e9b4/FOR509_banner.png

Megan is a Senior Security Engineer at Datadog, SANS DFIR faculty, and co-author of FOR509. She holds two master’s degrees, serves as CFO of Mental Health Hackers, and is a strong advocate for hands-on cloud forensics training and mental wellness.
Read more about Megan Roddie-Fonseca