SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsThe NICE Workforce Framework for Cybersecurity defines the roles, skills, and knowledge needed across the industry. It’s designed to help you identify the right training and certifications for your current or desired role, mapped directly to SANS courses and GIAC certifications.

The NICE Framework (National Initiative for Cybersecurity Education Cybersecurity Workforce Framework) is a fundamental reference for describing and sharing information about cybersecurity work.
The Framework is designed to help you identify the right training and certifications for your current or desired cybersecurity role.
For more information on this framework and how it can assist you in finding the right cybersecurity training for you or your organisation, speak to a SANS representative.
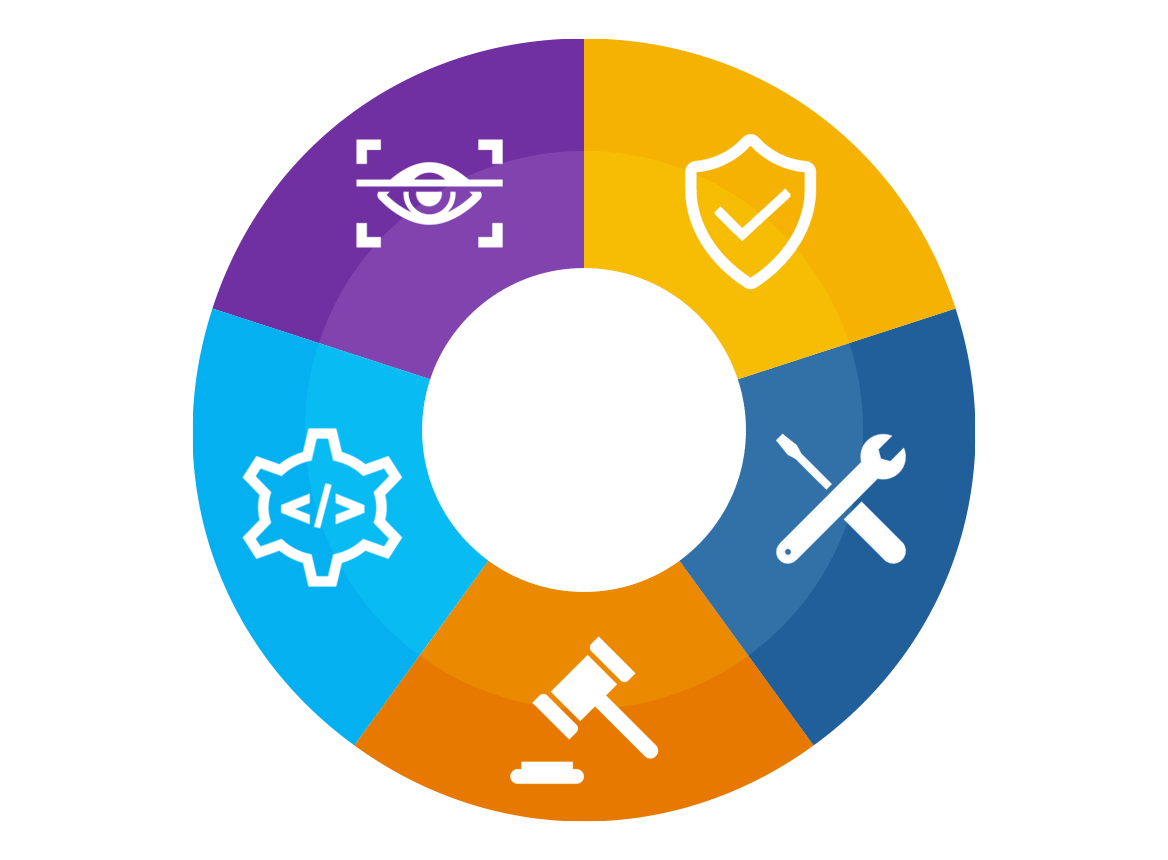
Provides leadership, management, direction, and advocacy so the organization may effectively manage cybersecurity-related risks to the enterprise and conduct cybersecurity work.
Conducts research, conceptualizes, designs, develops, and tests secure technology systems, including on perimeter and cloud-based networks.
Provides implementation, administration, configuration, operation, and maintenance to ensure effective and efficient technology system performance and security.
Protects against, identifies, and analyzes risks to technology systems or networks. Includes investigation of cybersecurity events or crimes related to technology systems and networks.
Conducts national cybersecurity and cybercrime investigations, including the collection, management, and analysis of digital evidence.