Based on FOR526 Memory Forensics In Depth content
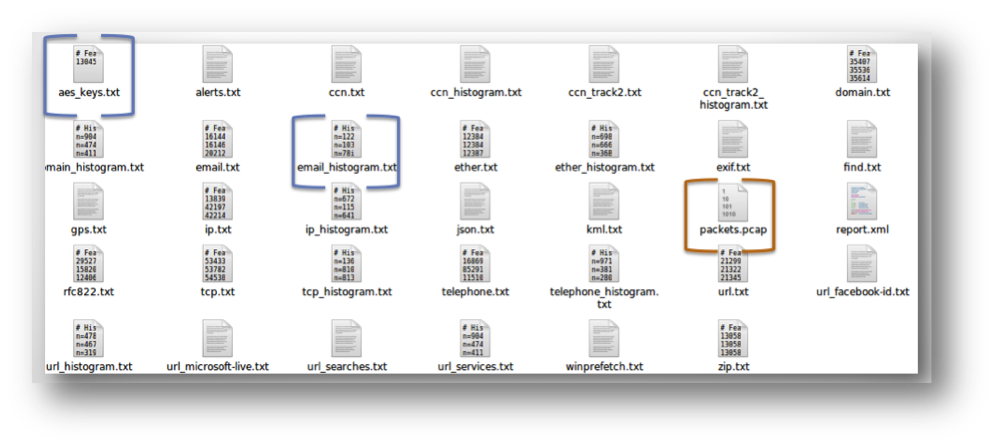
I recently worked an investigation that involved anomalous network traffic occurring inside a customer's network between a handful of workstations and the internal DNS server. I was given memory images collected by the customer from two of the offending systems. Following the memory analysis methodology we teach in FOR526, I was able to "rule out"* malicious code running on these systems. In addition to doing memory structure-based analysis, I parsed the image with a stream-based data carving tool, Bulk Extractor. This impressive free open-source parsing tool was written by Simson Garfinkel and in its most current release 1.4.0, carves for PE files, Prefetch, and MFT records in addition to its default scanners: urls, credit cards, email addresses, mac addresses and more (see Figure 1). Yet, one of my favorite features that Bulk Extractor offers is the ability to extract network packets out of memory. In my investigation, it successfully extracted network packets from the packet buffer in each of the memory images. Using WireShark to view one of the consolidated "packets.pcap" files from one system memory image acquired remotely, I noticed that almost all of the extracted packets were from the collection server, acknowledging the packets containing the memory image data being sent from the workstation. No evidence of the internal anomalous traffic was found in this "packets.pcap" file. The act of remotely acquiring the memory, in this case, had "stomped" all over the actual anomalous activity, giving me little to go on.
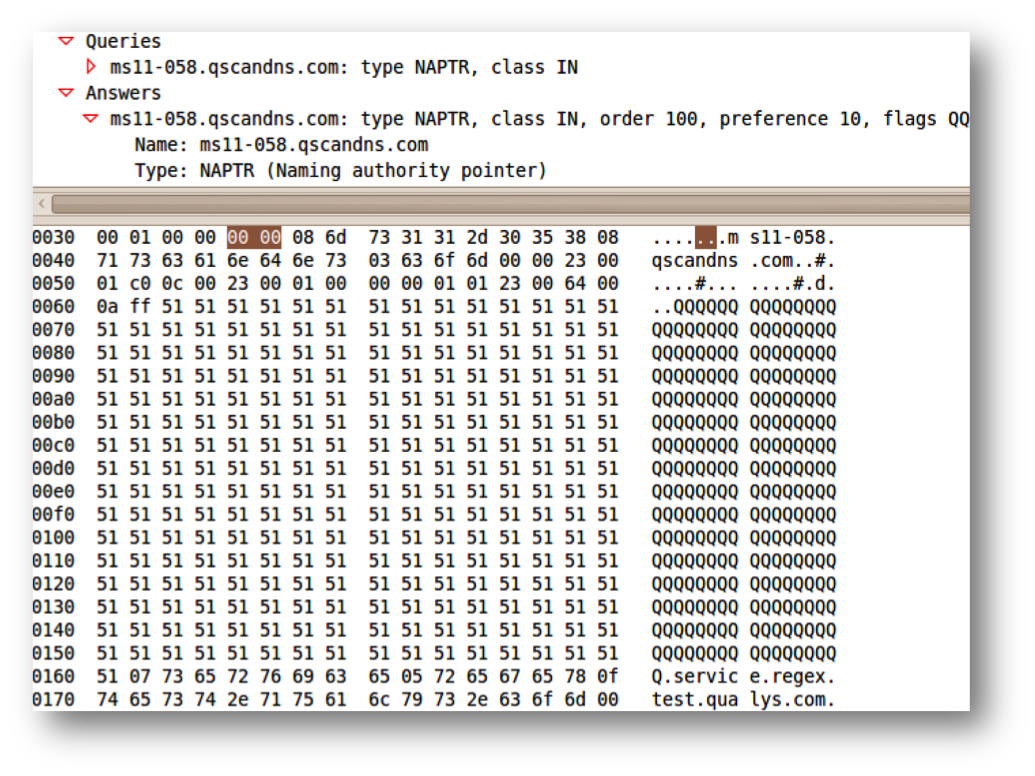
Fortunately, the memory of the other system was dumped locally. There was no "contamination" of the packet buffer on this system during the dumping process. When viewed in WireShark, the hundreds of responses from the internal DNS server were evident, as well as one packet that proved to be the "smoking gun". Seen in the extracted packets from this system was a DNS vulnerability scan run across the entire enterprise by the internal pentesting team (see Figure 3). This system had most likely received this packet on a listening port and forwarded it to its authoritative DNS server, creating a ricochet effect, resulting the anomalous traffic seen on the customer's network.
Bulk Extractor was the hero here and mine is just one of the stories amongst many that I have heard about the valuable use cases for this tool. To learn more about stream-based parsing tools to include Bulk Extractor, check out FOR526: Memory Forensics In Depth.
*Most experts in the field agree that there is never a 100% definitive rule out for malware on a system.