Tags:
SEC540: Cloud Security and DevSecOps Automation has released another major update that will help you in your efforts to build cloud infrastructure with Terraform, deploy resources to the Azure Cloud, and better understand the Container Security Lifecycle. Since the inception of SEC540, the lab environment has had a heavy focus on deploying and securing resources in the AWS Cloud. At the end of every class, I always ask students for feedback about their experience and how we can improve the course. By far, the most common feedback was:
- The AWS labs are very exciting and challenging, but I wish we could do the labs in Azure.
- I’d love to get more hands-on experience with Terraform!
To my past students, we heard you! In the spirit of continuous improvement, the SEC540 author team set a goal in the 2021 update to go multicloud, build full support for deploying the lab environment in Azure, and bring in security tooling for equivalent Azure analysis. This required a tremendous amount of engineering effort, documentation, and support from SANS. We are all proud to announce that SEC540’s lab environment now supports a dual path option for students to choose AWS or Azure as their cloud infrastructure provider!
Microsoft Azure Lab Environment
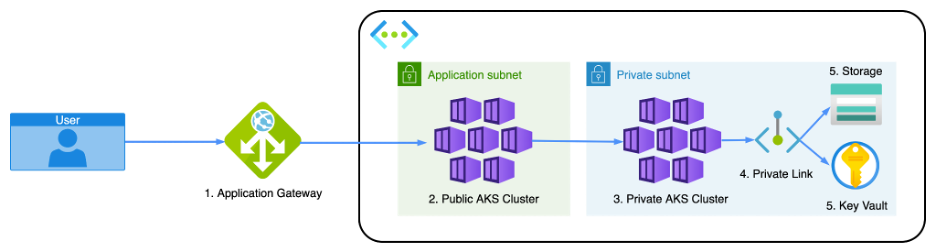
Students choosing the Azure Lab environment will experience a different toolchain, with a few common tools where possible:
- Azure deploys using over 2,000 lines of Terraform configuration code
- Virtual machine gold images build with Packer and the Azure Resource Manager Builder
- Checkov scans the Terraform configuration and identifies misconfigurations
- Azure DevOps pipelines build the lab environment’s container images and store images in the Azure Container Registry (ACR)
- Azure Kubernetes Service (AKS) manages the lab environment’s container runtime
- Azure Application Gateway routes traffic to Kubernetes, manages blue green deployments, and enforces Web Application Firewall (WAF) policies
- Azure Log Analytics, Container Insights, and Rule Alerts manage application telemetry and notifications
- Azure API Management hosts APIs and Azure Functions perform custom JSON Web Token (JWT) validation
- Microsoft Defender for Cloud monitors resource configuration and Workload Protection performs threat detection
- Cloud Custodian Azure Policies provide a cloud-agnostic way to auto-remediate misconfigured resources
Read more details below on the section-by-section updates.
SEC540: Cloud Security and DevSecOps Automation
SEC540.1: DevOps Security Automation
- CI / CD security misconfigurations, GitHub Actions security, and best practices for hardening CI / CD pipelines.
SEC540.2: Cloud Infrastructure Security
- Cloud Infrastructure as Code: In depth walk through of the HashiCorp language, Terraform configuration, Terraform Modules. Detailed command line examples for applying Terraform configuration and managing Terraform state.
- Container Security Lifecycle: Refreshed content focusing on the Container Security Lifecycle:
- Pre-commit: hadolint, trusted image suppliers, conftest policies, distroless images, multi-stage builds, docker secrets, and docker scan
- Version Control / CI CD: Scanning images with Trivy and signing images with Project Sigstore Cosign
- Container Registry: Enabling cloud native image scanning, immutable tag policies, and registry role-based access control policies
- Container Orchestration: Enforcing security policy with admission controller, validating cosign signatures, and runtime protection with Falco
SEC540.3: Cloud Security Operations
- Cloud Workload Security review for Azure Application Gateway, Azure Kubernetes Service, and Azure Storage Accounts
- Running OWASP Dependency Check in Azure Devops pipelines for Software Composition Analysis (SCA) / Supply chain scanning
- Using Azure Monitor Log Analytics, Container Insights, and Kusto Query Language (KQL) queries for detecting alerts and sending notifications
SEC540.4: Cloud Security as a Service
- Blue / Green deployments with Azure Application Gateway
- Azure CDN Token Authentication, Symmetric Keys, and Policies
- Azure API Management, Endpoints, and Authorization Policies
- Building and Deploying Azure Functions with Terraform
SEC540.5: Compliance as Code
- Creating Policy as Code with InSpec, AWS Service Control Policies, and Azure Policy
- Azure Application Gateway WAF configuration and custom rules
- Continuous compliance, detection, and automated remediation with Azure Event Grid, AWS Event Bridge, AWS Security Hub Automated Response & Remediation, and Cloud Custodian Azure Policy
DevOps is the set of cultural and technical practices that enable teams to deliver value to their stakeholders quickly, securely and reliably. Take SEC540: Cloud Security and DevSecOps Automation and let us teach you how. Read the full course description here.