SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsDefining what Industrial Control Systems are, why they are vital, and the unique challenges of securing them.

Welcome to the first part in a multi-part series on the cybersecurity of Industrial Control Systems (ICS): Introduction to ICS Security. In this first blog entry, we’ll introduce you to what these systems are, explain why they are vital, and outline the unique challenges of securing ICS.
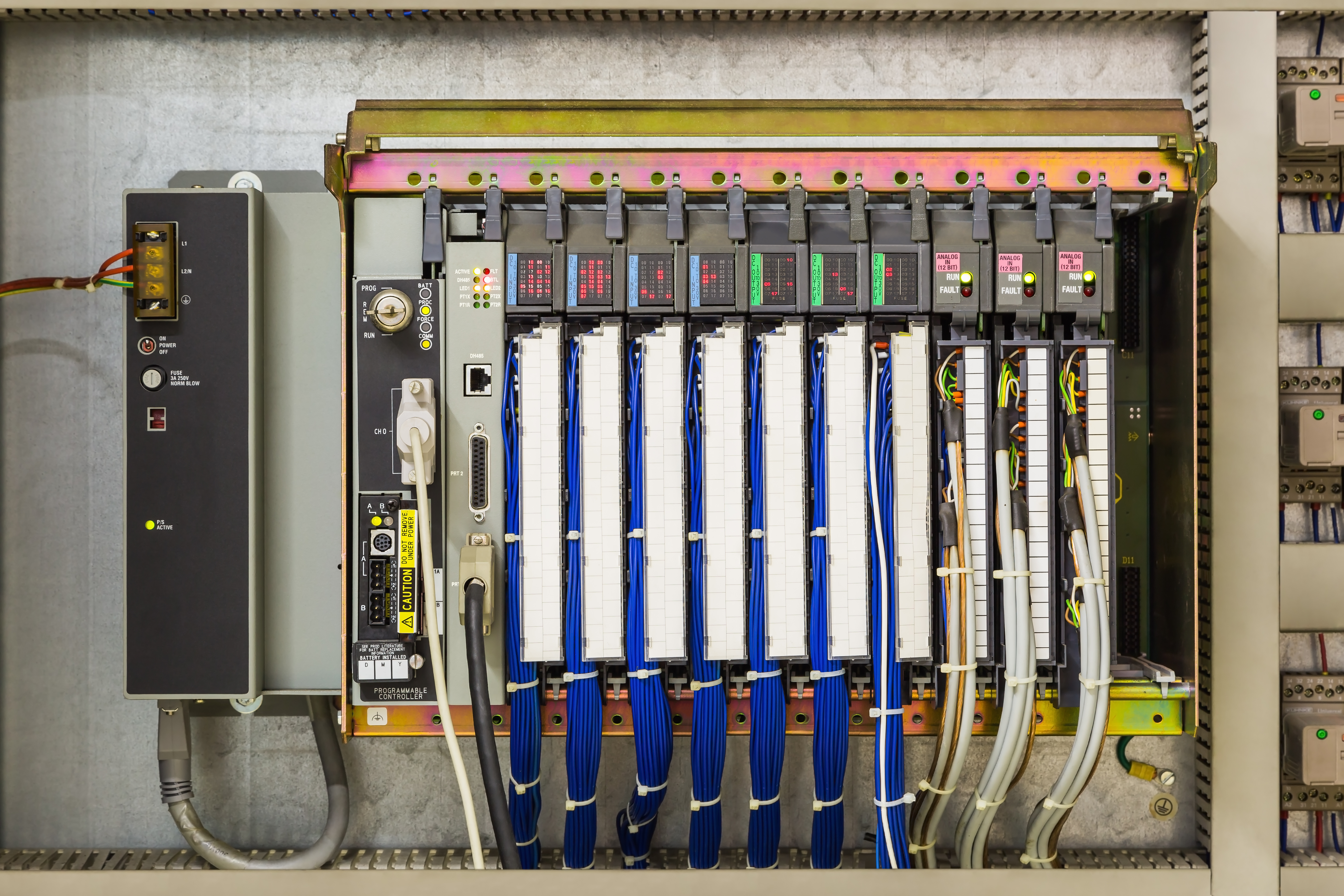
Industrial control systems are used for managing, directing, and regulating the behavior of automated industrial processes. ICS is a term that encompass several types of control systems, but all these systems have some basic traits in common. Their job is to produce a desired outcome, typically maintaining a target state or performing a certain task in an industrial environment. They carry out this function using sensors to gather real-world information. They then compare this data with desired set points, and compute and execute command functions to control processes through final control elements, such as control valves, to maintain desired states or complete tasks.
While far from complex, a thermostat is an example of a simple control system that most people are familiar with. It monitors the temperature in an enclosed space and turns on a heating or cooling device to maintain the desired temperature.
On the other end of the spectrum are large-scale, complex environments requiring several different systems working in concert to automate the functions of industrial equipment. The widely used Purdue reference architecture model segments ICS into multiple levels that we will cover in more detail in a subsequent blog post in this series. For the time being, we will summarize the components of ICS as follows:

Industrial control systems are basically everywhere. The water you drink, the traffic lights that tell you when to stop and go, and the electricity powering the device you’re using to read this blog all come from services that cannot function without the automated processes enabled by ICS. These systems are also a matter of national security. The US Department of Homeland Security lists 16 critical infrastructure sectors whose assets and functions are considered vital to the country’s national economic security and public health or safety, and every sector listed is heavily reliant on ICS:
|
|
In each of these critical infrastructure sectors, different industrial control systems are continuously at work regulating flow rates, opening and closing breakers, monitoring temperature levels, and performing many other functions. Vaccine production, for example, is currently a major global priority and the batch control functions of the ICS used in this process are critical to pharmaceutical companies’ mass production efforts. Disruptions of ICS in any one of these sectors can have major consequences. In workplaces where front-line staff must handle explosive or toxic materials, a system failure can result in serious injury or death.
It is easy to understand why industrial control systems are among the highest value targets for cyber-attacks by well-organized threat actors. The goals of these groups can vary from theft of intellectual property to intentional infliction of damage by hostile nation-states, but the importance of ICS systems to the daily functioning of any industrialized nation makes them an ideal target for any group looking to inflict a maximum level of disruption for a relatively low resource cost.
Attacks on major utilities can severely impact large populations, as in the case of the 2015 cyber-attack on three energy distribution companies in the Ukraine that temporarily cut off electricity to over 200,000 customers for over three hours in the heart of winter. Since 2016, there have also been three publicly disclosed attacks on water systems that posed direct risks to the health of their customers. These attacks followed in the wake of 25 cybersecurity incidents in the U.S. water and wastewater sector in 2015 alone.
Compounding the problem are the limited budgets of utilities, particularly those operated by smaller municipalities. Rural utilities frequently lack the budget to employ even a single IT person, leaving them poorly equipped to handle most types of cyber threats.
There are some key characteristics of industrial control systems that make them inherently more challenging to secure than IT environments. For one, these are deterministic devices that must operate precisely in real time, and layers of security can potentially impede their performance. If ICS devices must measure an electrical current at precise intervals of 1/60th of a second, they cannot tolerate the potential latency created by security software running in the background. Secondly, some components of ICS are essentially running all the time, and their continuous operation may be integral to organizational drivers (e.g., driving profits or maintaining health & safety). Any downtime incurred by making changes or installing updates to these systems must be meticulously planned to ensure the absolute minimum level of service disruption.
While they may deal with complex industrial applications, there’s an inherent simplicity to industrial control systems: they control the processes for which they were designed, and nothing more. These systems have improved considerably over time, yet they have evolved along a different path than IT, and their security capabilities have not received as much attention as security practitioners would like.
The first industrial control systems were customized for the requirements of the different sectors in which they operated. For example, the early days of plant floor automation relied on racks of industrial relays, pneumatic plunger timers, and electromagnetic counters to start and stop motors. There were no terminals or network connections at all, and programming changes were conducted by electrical engineers on the plant floor making program changes by physically changing electrical circuits. These systems were predefined, inflexible, and stagnant by nature, and implementing any changes or performing maintenance on them was extremely difficult.
A major leap forward took place in 1975 with the release of the Modicon 184, the first programmable logic controller (PLC). This device could be programmed from a personal computer running vendor programming software via proprietary media and protocols. The predominant communication protocol used to program first-generation PLCs was Modbus (over a serial interface), introduced in 1979. Modbus is now open-source, and it proved so reliable and easy to use that it remains in use to this day, with developers having adapted it to work over TCP/IP networks. Unfortunately, this presents a significant security problem, because Modbus request and response packets are sent unencrypted and without authentication, and they are easy to intercept, modify, and replay using established methods. While several other protocols are currently used in modern ICS, many of them share similar vulnerabilities.
Security deficiencies inherent in ICS devices go beyond communication protocols, however. Devices that have proven the most easy-to-use and durable over time are paradoxically among the most problematic from a security perspective because they have extremely long service lives and, as a result, they lack the hardware, horsepower, or programming required to implement security features.
There is also a vast number of different, often proprietary systems comprising today’s ICS environments due to the wide variety of real-world applications for ICS. Most IT organizations use well-known operating systems like Windows, for which it is easy to find experienced administrators. The systems, protocols, and programming methods used in ICS are more diverse, a result of vendors adhering to proprietary technologies for their respective product lines. Consequently, each ICS environment is often unique and may feature several different systems run by operators with differing priorities and specialized skill sets.
In conclusion, it is important to note that ICS practitioners have historically placed a premium on reliability and interoperability. This is because industrial control systems are typically subject to continuous use, providing critical functions over long service lifetimes in multi-vendor environments. As a result, security practices were not commonplace when many of those environments were first commissioned and security features and practices have only started being integrated into ICS systems in recent years.
As organizations everywhere have exposed more ICS functions to their corporate networks and the cloud to improve business and operational efficiencies, they have unwittingly opened up new potential attack vectors into their industrial control systems. Malicious actors frequently succeed at accessing corporate networks and have, in many documented cases, gained access to the ICS environment and caused a variety of disruptions ranging in impact from trivial to life-threatening.

While the problems stated here are significant, their convergence with other socio-economic factors, including the contraction of the oil & gas industry, presents opportunities for individuals considering career transitions. Those with experience working with ICS in industrial settings possess a solid foundation to become ICS security practitioners. In a keynote speech at the 2021 SANS ICS Summit, Anne Neuberger, the Deputy National Security Advisor for Cyber and Emerging Technology on the US National Security Council, expressed the importance of engaging people with this background:
"I had a couple of people on my team in my last job who came in from the utility sector and they were hugely value and pulled into every discussion because folks kept saying 'this is useful.'"
Along with the different set of tools used in ICS comes a different mindset among its experts, borne of a different mission, culture, and apprehension of the unique risks to ICS environments. Those with hands-on experience with ICS bring a wealth of knowledge that can help develop the informed approach required to secure our industrial infrastructure.
IT security analysts who are willing to apply their expertise to the field of ICS can also greatly help to improve the state of ICS cybersecurity. While ICS vendors are beginning to incorporate more security into their products and technologies, people with a solid grasp of IT security best practices are crucial to protecting ICS environments right now. All ICS protocols, for example, will eventually be hardened and secured, just as FTP and TELNET were gradually replaced in the IT realm by SFTP and SSH. Until these types of improvements come about, however, proven IT security practices can be adapted to protect ICS: network segmentation coupled with strong perimeter protections and robust monitoring, detection, and response.
In our next installment in this series, we’ll delve further into the current state of ICS cybersecurity, examining best practices and architecture standards, while reviewing the valuable lessons learned from recent attacks on ICS infrastructure.
Introduction to ICS Security Blog Series
Read Part 2 here.
Read Part 3 here.
Sources
Ackerman, Pascal (October 2017). Industrial Cybersecurity.
https://subscription.packtpub....
Barrett, Brian (April 2, 2021). Wired. The Threat to the Water Supply is Real - and Only Getting Worse.
https://www.wired.com/story/th...
About Stephen Mathezer
See Stephen's bio and ICS contributions here.
Learn more about SANS Course ICS410: ICS/SCADA Security Essentials here


With more than 25 years of experience in IT and OT security, Stephen Matezar has led major security initiatives, including the re-architecting of OT networks for a multi-billion-dollar oil and gas company.
Read more about Stephen Mathezer