SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact Us
For the past few years I've been invited to speak at the SANS HackFest conference. This is a great opportunity for me to present new research and useful pen testing techniques to a hungry audience.
It's also a highly competitive event among speakers. Each year my stuff needs to be bigger and better than the year before.
Over the summer, my daughter and I watched a show about a haunted house, and the reenactor used an Android app to communicate with ghosts. I saw two excellent opportunities:
My budget-manager-for-crazy-projects and I agreed that I would spend $200 on Android apps that claim to detect ghosts. I excluded anything that was free, marked as entertainment, or otherwise admitted that they did not actually detect real ghosts. Instead I focused on apps that were labeled professional use, that claim to meet or exceed the capabilities of commercial ghost detection tools, and claim to perform genuine ghost detection.
The apps I chose ranged from $0.99 to $29.99 in price, and are generally categorized as including one or more of 4 ghost detection capabilities:
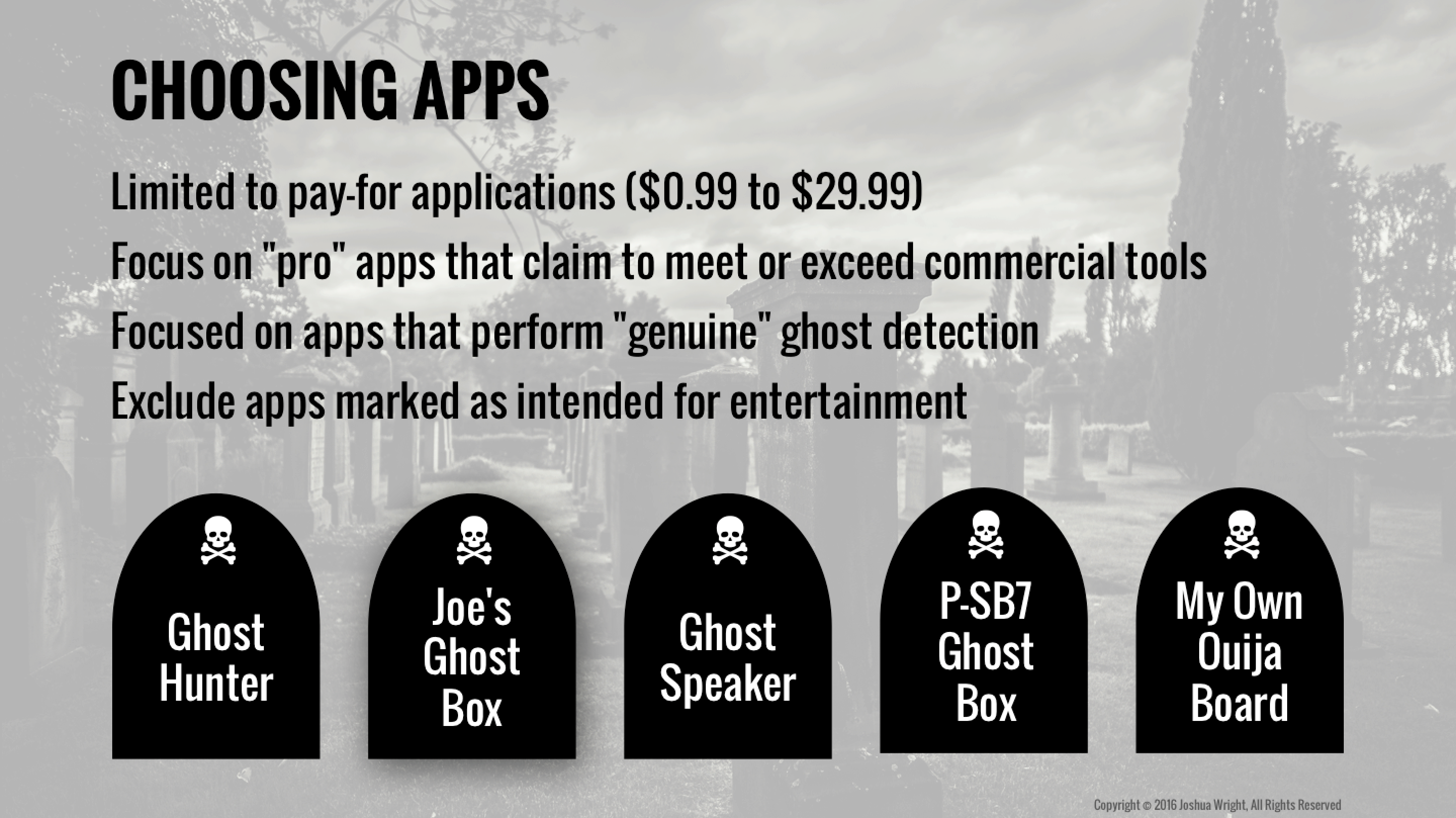
I evaluated 20 Android ghost detection apps in total, and at HackFest I revealed my analysis results for 5 apps:
My work primarily consisted of dynamic analysis (install the app, capture network traffic, monitor the filesystem, and look at logging messages) followed by static analysis (unzip the Android APK file, examine the embedded resources, decompile and analyze the source code). Somewhat unsurprisingly, I found my usual cache of tried-and-true tools served me well:
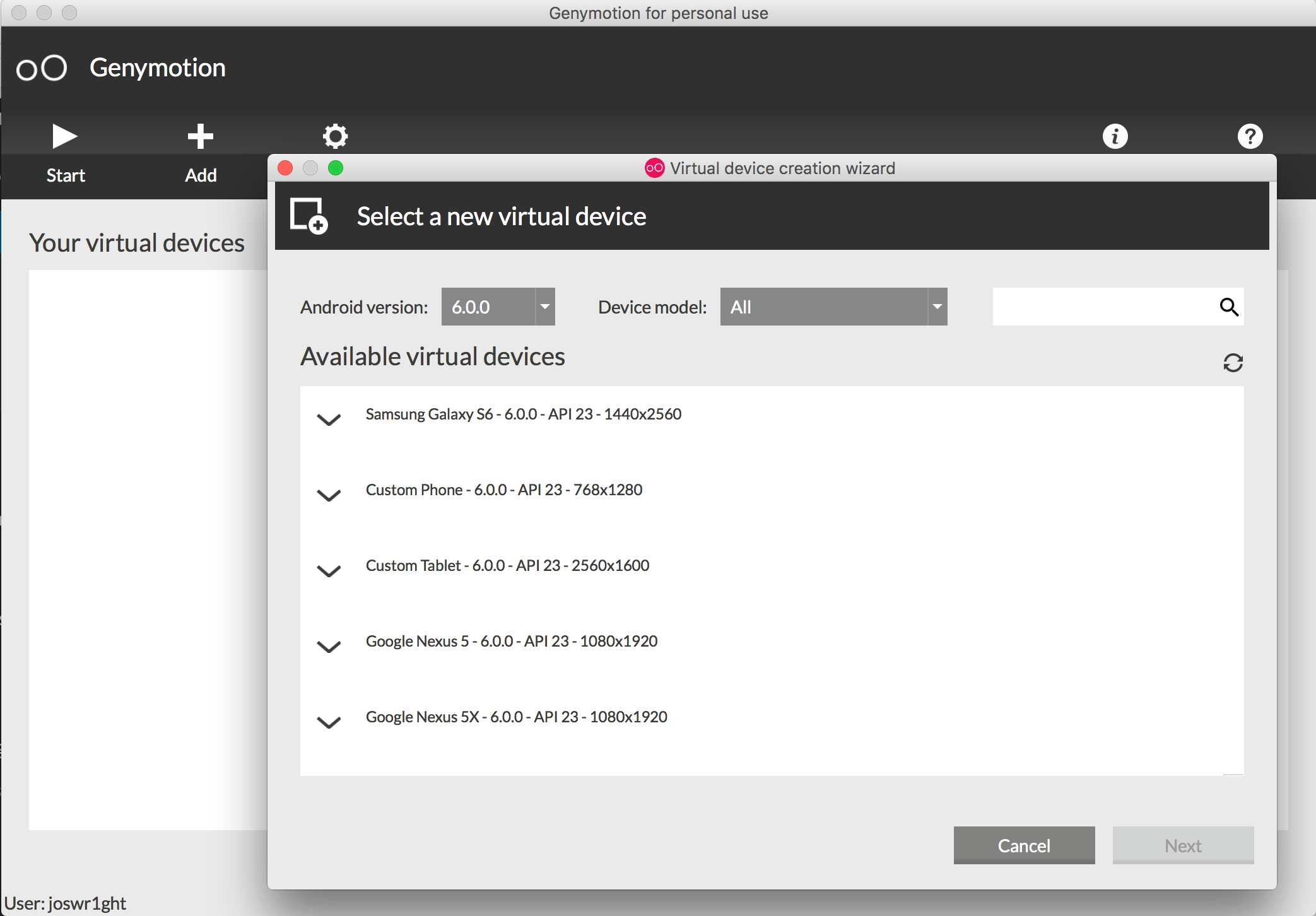
In particular, I started using Genymotion as my go-to emulator for runtime analysis of Android applications. Genymotion uses VirtualBox as the behind-the-scenes hypervisor to emulate Android devices, but it does so with a very simple user interface. Free for personal use, it's quick and easy to download and install Genymotion on Windows, Mac OS X, Linux.
After starting Genymotion, you'll have the option to create new Android virtual devices, choosing from different Android versions and hardware configurations. From there, it's easy to start the Android device, scale the window, and install or copy files to the virtual device with drag-and-drop.
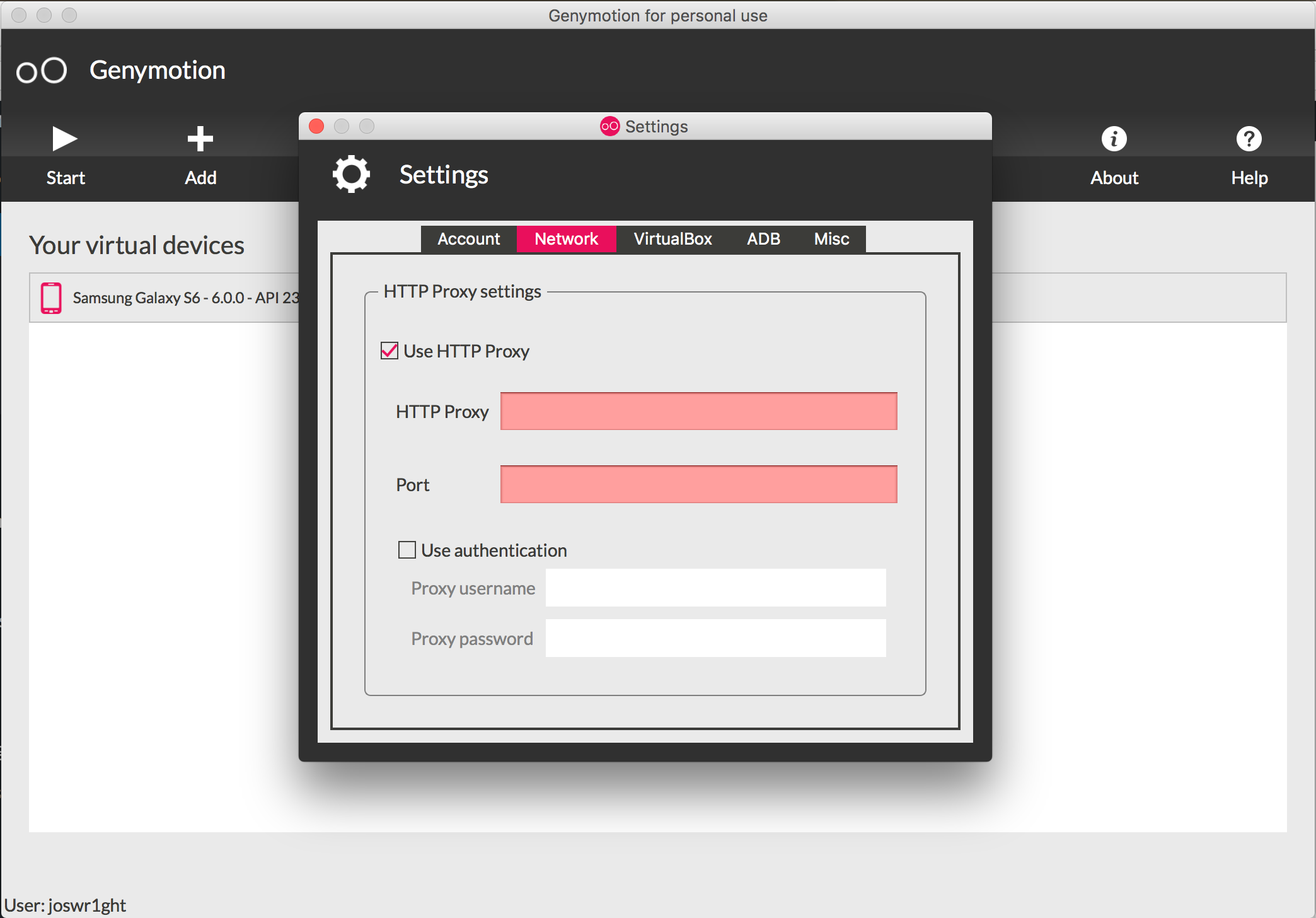
Although Genymotion lacks the "-tcpdump" and "-http-proxy" features that come with the official Android Emulator and the Qemu hypervisor, it's easy enough to capture Genymotion network traffic from your guest using Wireshark. HTTP proxy settings can be configured using the Genymotion virtual WiFi interface, or though the Genymotion settings before starting the virtual device.
The apps were pretty lame.

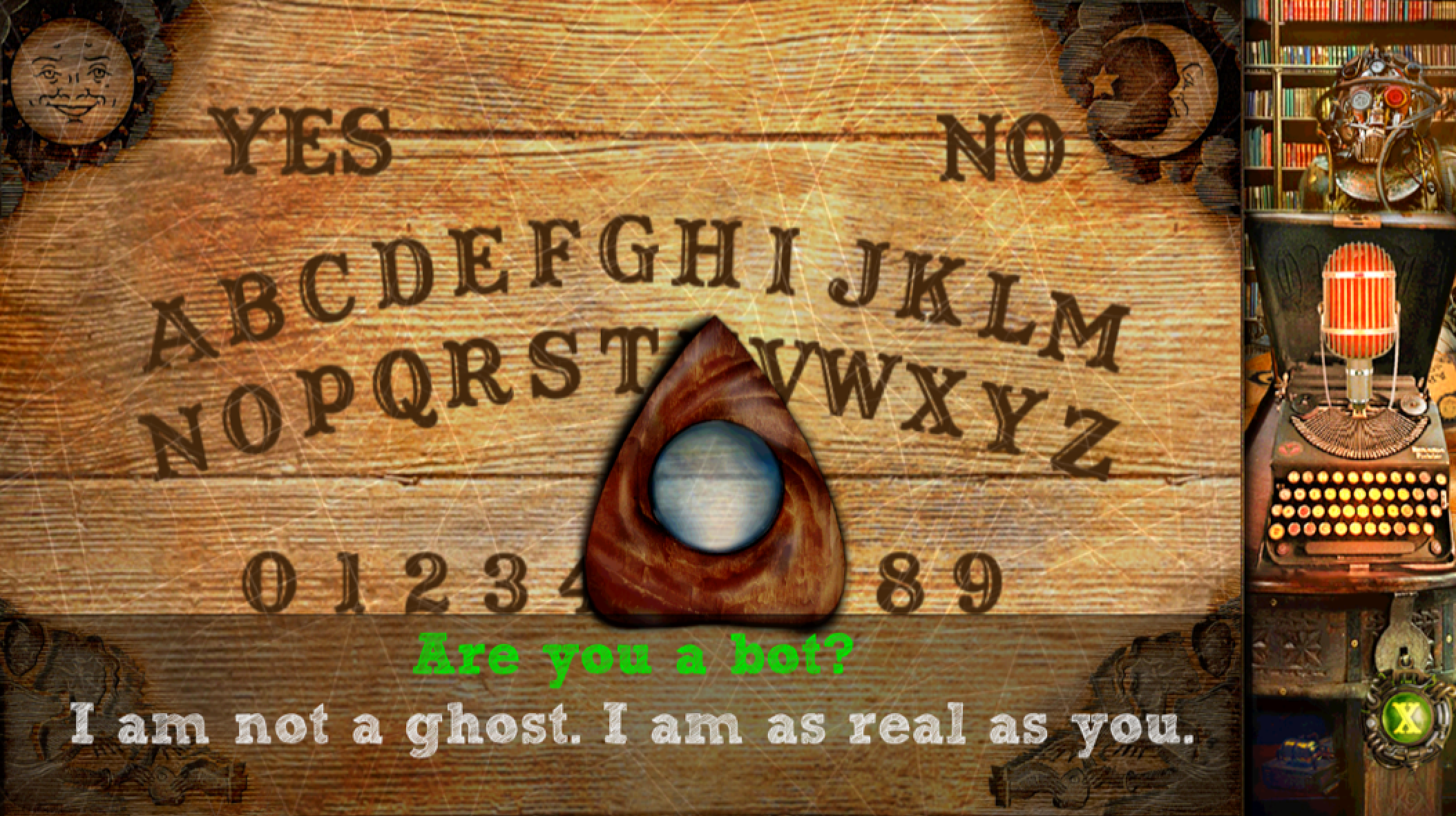
Several of the apps used a random number generator to "detect" ghosts at various intervals, using static images to populate "radar" systems, or to serve up "ghostly" audio clips. Other apps used static wordlists to spook the user into thinking they could communicate with the dead, or otherwise hooked into cloud-based bot communication systems. One app overlaid a picture of a Ouija board with chat directly from cleverbot.com, changing each response of "bot" to "spirit", "ghost", "psyche", or "soul".
My budget-manager-for-crazy-projects asked me if the $200 and hundreds of hours spent analyzing Android ghost box apps was worth it.
Going into this, I hoped I would find evidence of ghost detection capabilities that would defy scientific understanding. Instead, I found developers using the compass as an RNG to graph "energy values that paranormal entities might be projecting". While that was mildly disappointing, I am well-pleased with this project.
Looking at all these apps forced me to improve my understanding of how the Android SDK works. I found bugs in some of my favorite tools, and figured out how to overcome them. I was able to optimize my workflow, to analyze an app in less time, and to produce better results. I was able to leverage Android Studio as a mechanism to aid my reverse engineering efforts, building a better understanding of how these apps work.
Going into this project, I was motivated to find out what I could about ghost box apps, and I wanted to build my skills as a mobile application security analyst. I had clearly defined goals and a strong motivation to keep working through the challenges that inevitably creep up in any project. At the end, I hadn't identified any ghosts, but I felt smarter and more capable to evaluate Android applications, a skill that I can apply in customer pen test engagements going forward.
In the meantime, if you come across a ghost box app that you think actually detects ghosts...then drop me a note in the comments section below.


Joshua Wright, Senior Technical Director at Counter Hack Challenges and author of SEC504, has spent over two decades teaching and building tools that help defenders identify and counter real-world cyber threats through practical, hands-on learning.
Read more about Joshua Wright