SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact Us
Shodan is a search engine that takes a distinct departure from most Internet search engines. Instead of searching through content intentionally served up and delivered to web browsers, Shodan allows us to search for Internet-connected devices. Created by John Matherly, Shodan uses distributed scanners throughout the world to randomly select target IP addresses and identify listening TCP and UDP ports. Listening ports are further enumerated to gather protocol banners, web pages, and other service data. All of this data is then added to an enormous, searchable database that describes the "what" of Internet devices.
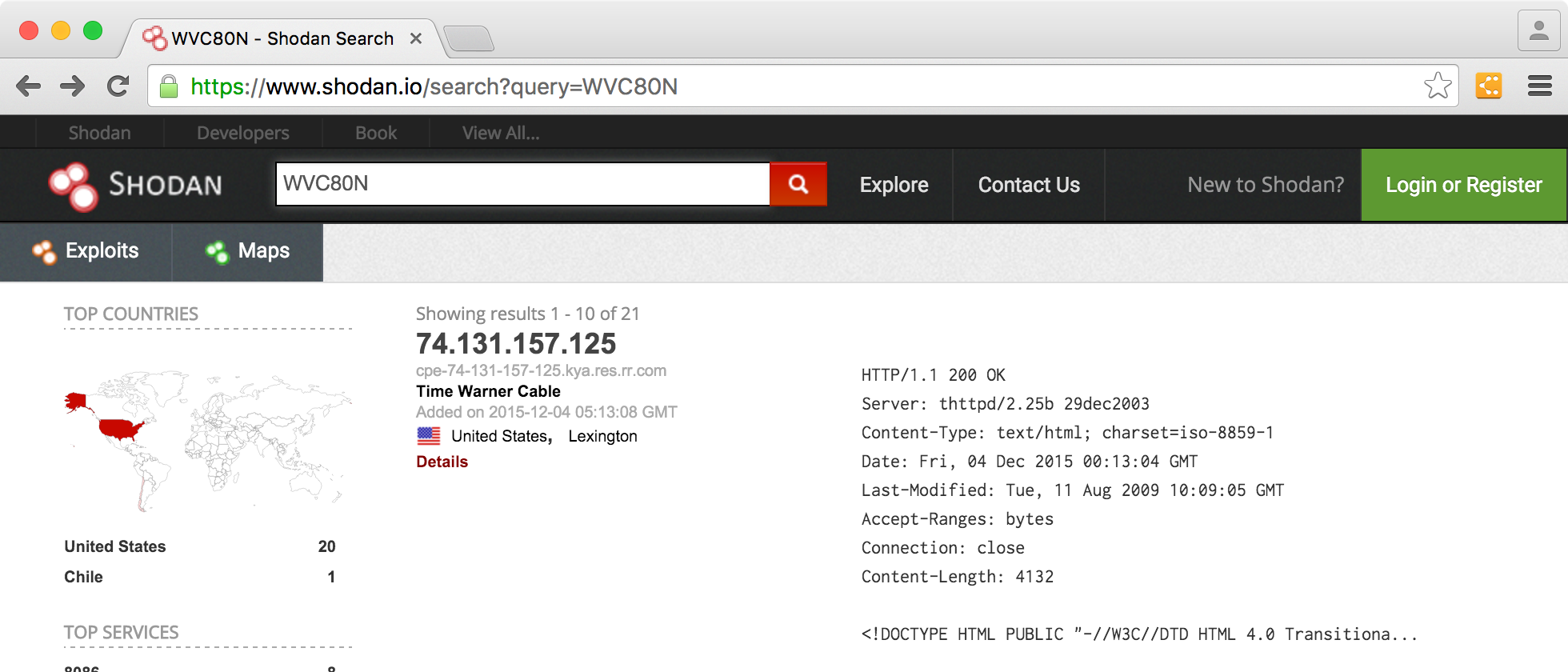
Shodan's search feature is powerful, allowing us to specify generic terms such as "camera" or even a specific part number such as "WVC80N" and quickly identify the devices that match.
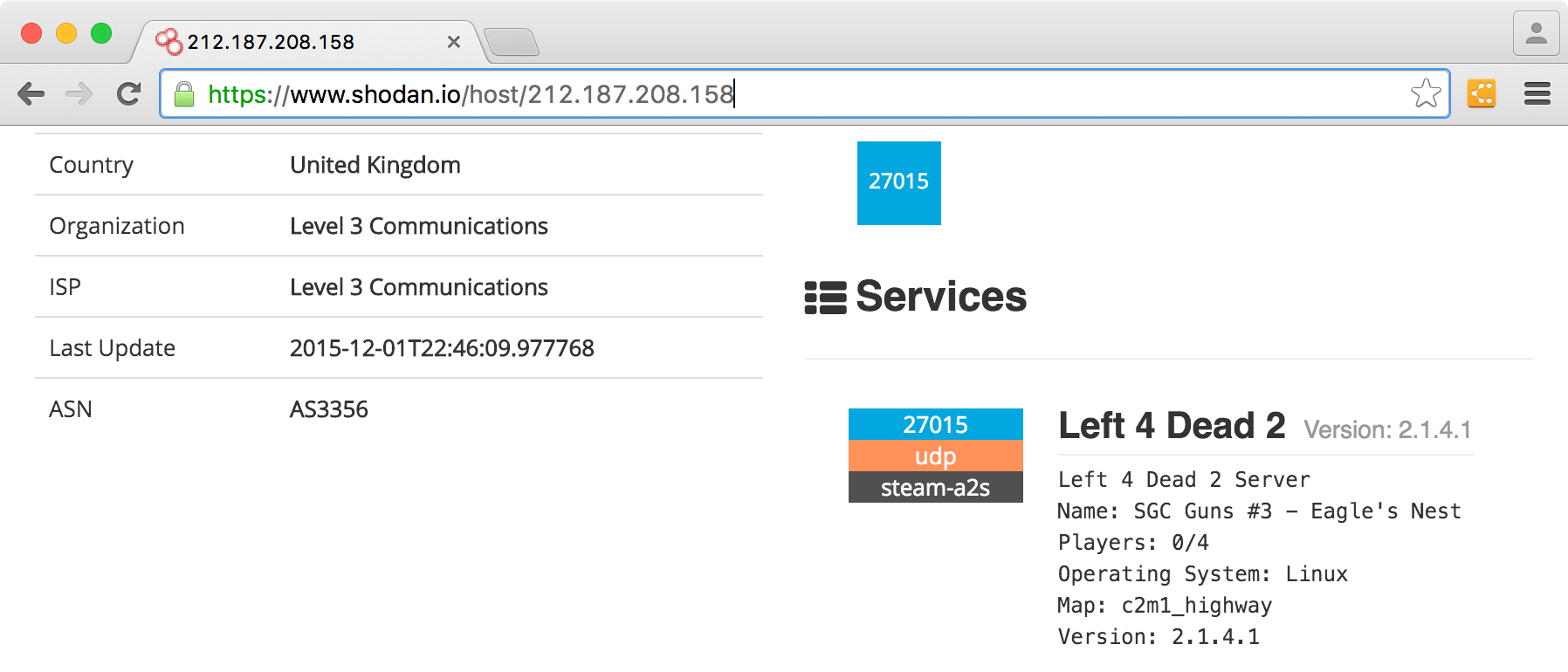
Beyond the web interface, Shodan offers a full-featured API and command-line tools to search and parse the Internet-device results. In this article we'll focus on using the web interface for effective device searches, as well as tips to use Shodan in your next penetration test.
By default, Shodan's website search feature will use a search term as an exact expression in a string match. Shodan does not do incomplete word matching (e.g. "WVC80" will not return matches against "WVC80N"), and will treat multiple words as a logical AND expression. Common words (a, and, by, the, is, on, it) are ignored.
The basic search will perform string matching against server banner information without searching through additional protocol metadata that is also gathered about the discovered devices. The Shodan documentation doesn't disclose exactly what protocol data is used in the default search, but empirical analysis indicates that it includes at least the following:
Metadata about a service is not searched by default. This list includes:
To perform more advanced searches using Shodan, we can apply search operators. Search operators are only available to registered users. It's free to create an account, which will also give you an API key for use with Shodan's command-line tool.
Once you are logged-in, you can apply additional search modifiers to focus your search. Search operators include:
Some filters allow multiple values, such as "postal:97201,97202".
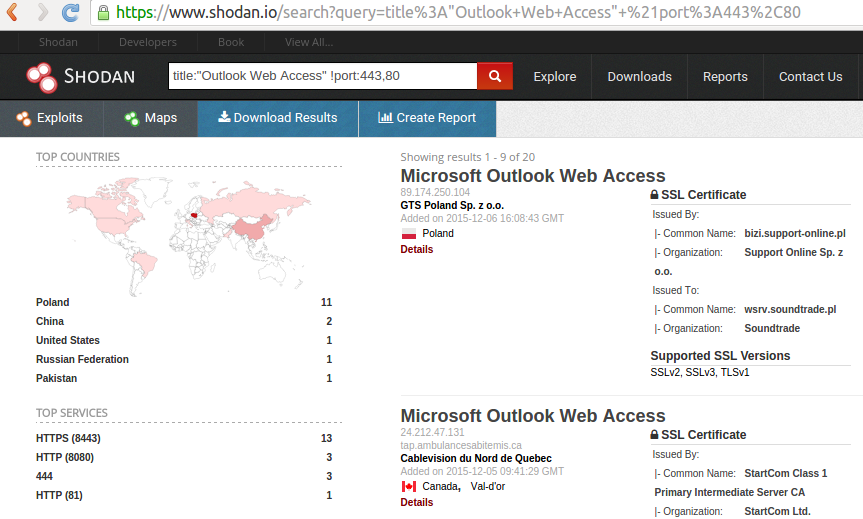
By default, multiple search terms are treated as Boolean AND expressions. You can also negate a particular prefix with the "!" character at the beginning of the search operator. For example, to search for machines running Outlook Web Access on ports other than 80 and 443, you can combine the title and port operators as follows:
It's easy to disregard Shodan as offering functionality to find vulnerable devices: an opportunistic attack tool. However, to do so is to overlook the benefits that Shodan can offer you and your customers in a penetration test.
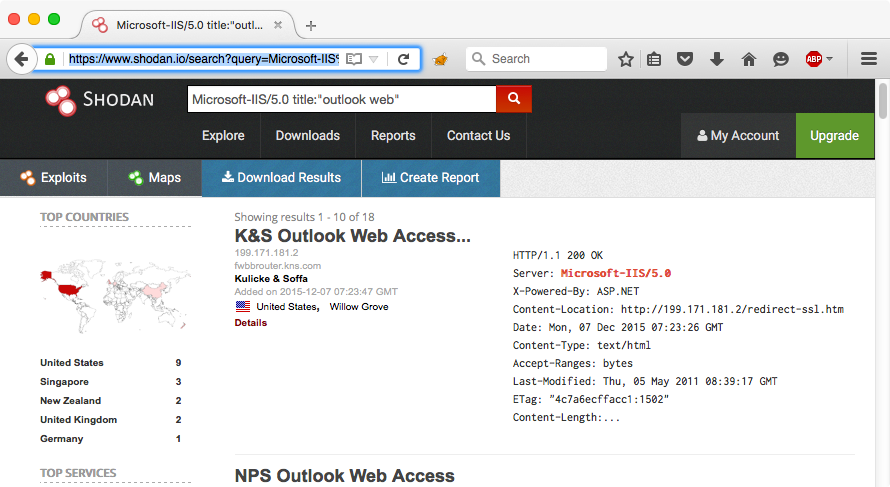
Answering Questions About Similar Vulnerabilities When putting together a report for a customer, I try to answer the inevitable question "How many others are similarly vulnerable?" Sometimes this question is in an attempt to justify a vulnerable configuration as commonplace or industry standard, or as a defensive mechanism for explaining why they continue to run Outlook Web Access on an IIS 5.0 server.
Using Shodan, you can quickly use the search criteria described in this article to answer that question. At the time of this writing, there appear to be no fewer than 18 publicly accessible IIS/5.0 servers running Outlook Web Access. Adding this level of detail to a penetration test report can help your customer to better understand the nature of the risk in the context of other similar configurations.
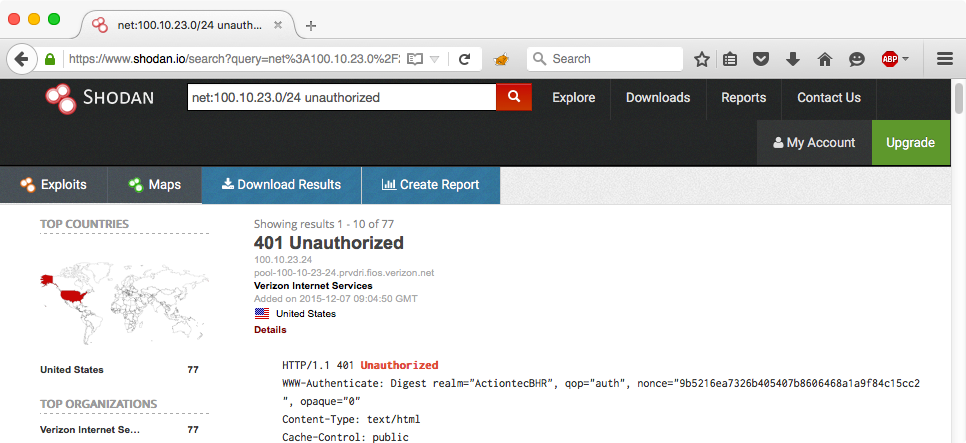
Shodan can quickly disclose information about target devices scoped to a specific range of IP addresses. This can be useful for helping to get a quick understanding of your customer's assets and the services on those assets as known to Shodan.
For example, this author's office Internet access uses IP addresses in 100.10.23.0/24 block through Verizon FIOS. I can ask Shodan how many people with IP addresses in my network also have their routers available for remote authentication and access. Apparently, it's far too many.
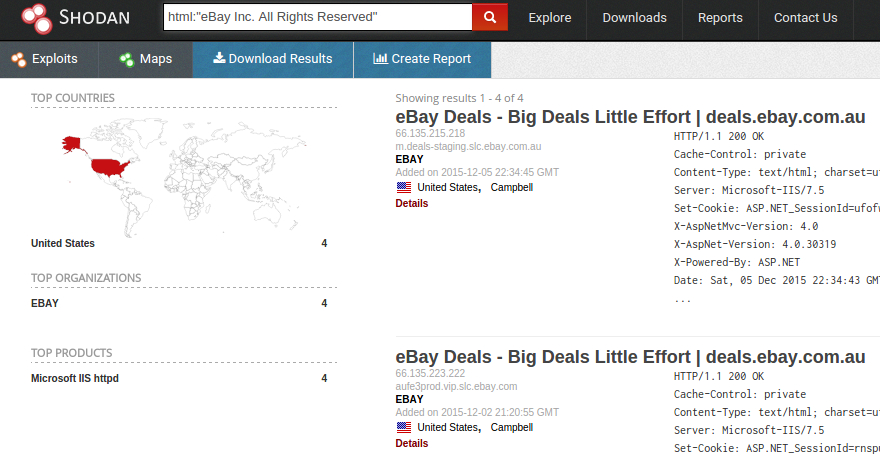
Sometimes the point of contact you are working with to scope your penetration test might not be aware of the company's entire web presence. By searching for identifying features of the website (such as the copyright notice), you may be able to find lesser-known sites for a given organization.
As a penetration tester, identifying targets that are owned by an organization that they don't know allows you to clearly demonstrate your value and usefulness as a security analyst.
For example, a search for html:"eBay Inc. All Rights Reserved" shows a small number of sites (eBay has excluded a lot of their web properties from Shodan) that may not be as well known:
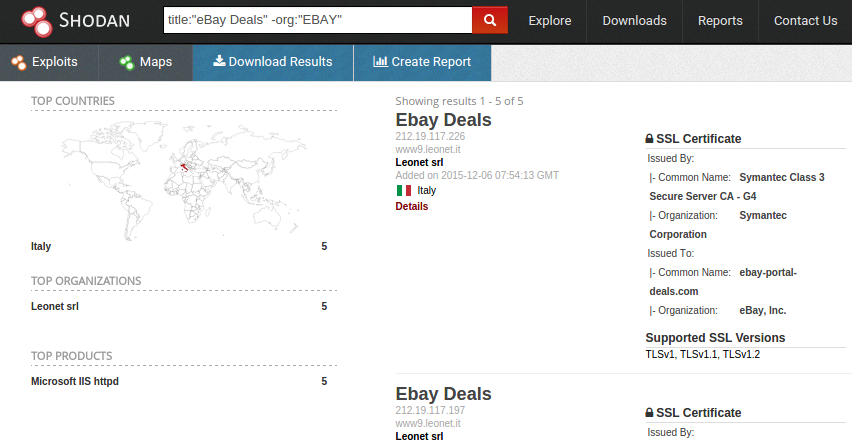
If your target is large enough to have Regional Internet Registry allocations (where the WHOIS information reflects the organization name), you can combine negative searches to exclude the known ranges with the html filter (searching for copyright or other unique strings) or the "org" filter.
Using the power of Shodan and some creative thinking, you can provide additional value to your penetration tests. Use some of these ideas in your next pen test and see if you can find some targets that were supposed be in scope, but weren't! Above all, have fun discovering new things on the Internet and providing more value to target system personnel.


Joshua Wright, Senior Technical Director at Counter Hack Challenges and author of SEC504, has spent over two decades teaching and building tools that help defenders identify and counter real-world cyber threats through practical, hands-on learning.
Read more about Joshua Wright