Tags:
This article looks at how Amazon Web Services (AWS) and Microsoft Azure have modified their services to gain entry to the cloud market space in China and compares their service offerings to local Chinese cloud service providers. We will cover specific considerations for foreign companies using cloud services in China. The Chinese company, Alibaba Cloud, is the fourth largest global Infrastructure-as-a-Service provider following AWS, Azure, and Google Cloud Platform. We end with a discussion of why this CSP should be on your watchlist.
It is important to understand Cloud Computing in China for these reasons.
- Extremely large market opportunities.
- US – China trade war and COVID19 Fallout
- Intellectual property protections
- China is a nation-state threat actor
In addition to the above reasons, many international companies either have a presence in China or plan to establish one. Even though the current US-China relationship is unstable, it is reasonable to expect Cloud Security Professionals to have an increasing need to understand the “cloud-scape” in China.
The Chinese Cloud Market
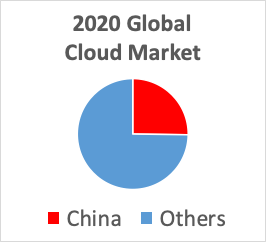
Without a doubt, everyone has their eyes on the Chinese Cloud Services market. A 2017 report [1] forecasted the China market to grow to 686.6 billion yuan (about $103.6 billion) in 2020. This is a quarter of the projected worldwide market of $411 billion.
One indicator of the keen interest in the cloud in China is the 120,000 attendees that gathered at Alibaba’s 2018 cloud conference. For reference, the attendance at AWS re: Invent (the largest US conference) was 50,000 that same year [2]. NOTE: No attendance numbers available for the 2019 Alibaba Cloud Computing Conference.
While the opportunities are great, so are the challenges. Chinese companies' biggest concerns with moving to the cloud are focused on the costs and difficulties of moving to the cloud followed closely with concerns around security, according to the 2018 McKinsey China Cloud Survey [3].
Cloud Computing Market by Region
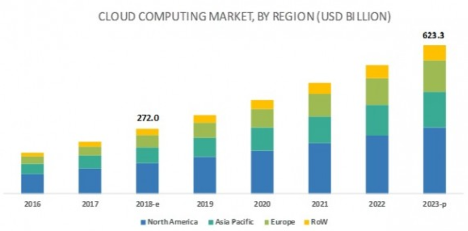
According to a September 2019 report, the global market for cloud computing is expected to exceed $623 Billion US Dollars by 2023 [4,5]. The chart above breaks down the growth by region of the world.
Market Data on the Growth of Public Cloud Computing
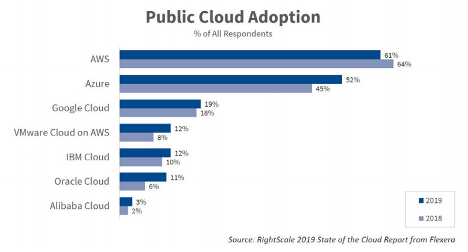
The slide above shows data from the RightScale 2019 State of the Cloud Report [6]. Interestingly, in 2017 AWS had 57% adoption, Azure had 34%, and GCP had 15%. This 2019 survey found that 84% of respondents had a multi-cloud strategy and were running applications in an average of 3.4 clouds and experimenting with 1.8 more for a total average of 4.9 clouds!
This above slide shows which cloud service providers are being used, while the following slide on the next page shows how much each provider is being used.
Iaas + Paas Market Shares
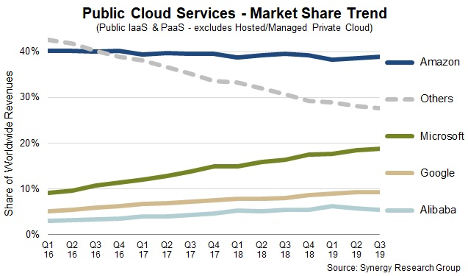
According to the Synergy Research Group [7], Amazon is still the market leader by a significant margin. Microsoft is aggressively ramping up its cloud campaign in terms of maturing its cloud offerings as well as its and marketing efforts.
Google is definitely a player with solid cloud products and loyal customers, however it has made a strategic decision not to compete in China. Alibaba will be certainly important to track as well, particularly as they expand their footprint outside of China.
Cloud Service Providers in China
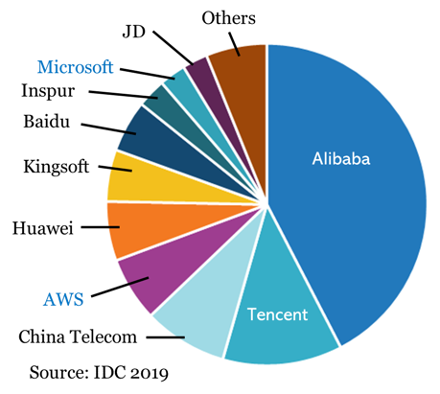
Alibaba Cloud is the largest provider in China, but there are several domestic CSP’s including Tencent (the creator of WeChat) and Kingsoft Cloud. [8,9]. According to a 2015 report [10], AWS is the sixth largest provider in China, with about 4.3% market share. This same report put IBM in the 11th position at 0.1% market share. Oracle and VMWare are referenced in [10] but no market data is provided.
At the present time, Google does not have a cloud service offering in China. Google has had a troubled relationship with China from the Operation Aurora Attack [11] to its attempt to offer a search engine that complies with China’s censorship requirements [12].
Iaas Vendors Market Share in China – 2019H1
Alibaba, Tencent, China Telecom, AWS and Huawei are the top five vendors, and together control 75.3% of the market. [13], [14]
Operational Requirements - Cloud Service Providers
China is the only country in the world that does not permit foreign cloud service providers to own and operate their own data centers in the country. To operate a data center in China, a locally registered company that has less than 50% foreign investment must obtain a value-added telecom permit. This permit requirement is a point of contention in the US-China trade war as the US has taken the position that it gives Chinese companies and unfair competitive advantage [15]. The local partners own the physical infrastructure and are the “seller of record,” although the foreign cloud service providers retain their intellectual property rights and trademarks [16]. These local partners in China control the relationships between the CSP’s suppliers and customers [16].
Some experts believe that the deep cultural and technical links that the local companies have with the Chinese government create nearly insurmountable advantages, especially when it comes to regulations and requirements around cybersecurity and data protection [16].
Operational Requirements - Cloud Customers
Telecom and Cloud Service Providers:
- “Must ask users to provide authentic identity information and verify it when settling access service formalities for users.”
- “Cannot offer services for access to entities or individuals if they fail to obtain an operating license or to complete the non-operating Internet information service filing formalities in accordance with the law.”
All licensed operators must indicate the number of their operating license in a prominent position in their main premises, website homepage and business promotion brochures.
In accordance with Chinese law and regulations, the State subjects non-commercial internet information services to a record-filing system and commercial internet information services to a permit system. No one may engage in the provision of internet information services without having carried out record-filing procedures or obtained permission [22].
Companies that want to register for a cloud account need to provide a valid Chinese business license issued by the Bureau of Industry and Commerce and valid contact information [23].
Internet Content Providers
Internet content providers (ICPs) must apply to the China Ministry of Industry and Information Technology (MIIT) via their hosting provider.
- Commercial ICP services require an ICP license
- Non-commercial ICP services must submit an ICP filing.
Without an ICP license or ICP filing record, the domain and the website will be blocked.
AWS China
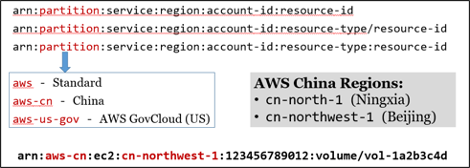
AWS China has two separate regions:
- Beijing Region (Beijing Sinnet Technology Co., Ltd.)
- Ningxia Region (Ningxia Western Cloud Data Technology Co., Ltd.)
AWS China is a separate partition (Just like GovCloud)
- AWS Global credentials cannot access other partitions
Not all AWS services are available in China
It is also interesting to note that tenants do not get the root credentials for the AWS accounts created in the China partition and that there is not a free tier.
All objects in AWS are referenced using a globally unique Amazon Resource Naming (ARN) convention. The following diagram shows an example ARN of an Elastic Block Storage (EBS) volume in the Ningxia region of the AWS China partition.
Azure China
Azure China is a separate instance of Azure in China. It is independently operated by Shanghai Blue Cloud Technology Co., Ltd., a wholly owned subsidiary of Beijing 21Vianet Broadband Data Center Co., Ltd. Azure China has datacenters in eastern and northern China, with >1000-kilometer separation between the regions.
Like AWS, Azure China has a feature parity gap, so it is important to monitor the updates from each CSP for change announcements. As with AWS, the Azure Portal & CLI can be accessed/used anywhere on Internet.
The Greatest Firewall of China
Regardless of which cloud service provider you use in China, traffic from outside China must traverse the Great Firewall of China which increases latency by an average factor of three times the latency of traffic that is internal to China. The Azure China Playbook [27] states:
“The network latency between China and the rest of the world is inevitable, because of the intermediary technologies that regulate cross-border internet traffic. Website users and administrators might experience slow performance.” –Azure
The Great Firewall of China uses a variety of techniques [28, 29, 30, 31] to inspect, manipulate and block traffic that cloud customers should be aware of:
- DNS spoofing, filtering & redirection
- URL filtering using transparent proxies
- Quality of Service (QOS) filtering
- Packet forging & TCP reset attacks
- TLS Man-in-the-Middle (MITM) attacks with Chinese Root CA certificates
- Black holes for IP Ranges
- Active probing
However, as evidenced by Azure’s tactful statement above, most companies accept this reality and make their decisions accordingly. It is possible to set up a VPN into China provided you obtain approval by the Ministry of Industry and Information Technology (MIIT) of the Chinese government. This is facilitated by your CSP [27] and should not be expected to protect you from interception by the Chinese Government.
Conclusion
In conclusion, I encourage you to explore the Chinese Cloud Service Providers. Don’t think of the Chinese Cloud as an impenetrable “black box,” like any other cloud service provider, they are open to the public and welcome your service fees. In fact, the more different cloud services that you can explore, the better foundation you have for comparison. That includes the various Chinese cloud service providers.
Embrace the hacker ethic but stay inside the law. Discover what’s inside that black box, how it works, and what makes each different from the others. However, if you are going to use cloud services in China, you should be aware of China’s cybersecurity laws [32].
Resources:
[1] http://usa.chinadaily.com.cn/a/201711/08/WS5a0d20c5a31061a738408eb8.html
[5] https://www.marketsandmarkets.com/Market-Reports/cloud-computing-market-234.html
[8] https://chinatechscope.com/2018/10/04/10-chinese-internet-cloud-providers/
[9] https://www.idc.com/getdoc.jsp?containerId=prCHE45761819
[10] https://www.lexology.com/library/detail.aspx?g=998fe1a0-6634-41e7-a670-19ca406709e5
[11] https://www.wired.com/2010/01/operation-aurora/
[12] https://www.popularmechanics.com/technology/a28434395/project-dragonfly-dead/
[13] https://www.idc.com/getdoc.jsp?containerId=prCHE45761819
[17] http://usa.chinadaily.com.cn/a/201711/08/WS5a0d20c5a31061a738408eb8.html
[20] https://uk.practicallaw.thomsonreuters.com/w-013-7289
[2]1 https://www.alibabacloud.com/help/doc-detail/52595.htm
[22] https://www.amazonaws.cn/en/about-aws/china/
[23] https://www.amazonaws.cn/en/about-aws/china/faqs/
[24] https://www.amazonaws.cn/en/about-aws/china/
[26] https://docs.microsoft.com/en-us/azure/china/
[27] https://docs.microsoft.com/en-us/azure/china/concepts-performance-and-connectivity
[28] http://pcwizardpro.com/how-to-unblock-websites-in-china/
[29] https://www.usenix.org/system/files/conference/foci14/foci14-anonymous.pdf
[30] https://www.eecs.yorku.ca/course_archive/2014-15/W/3482/Team13_presentation.pdf
[31] https://www.theguardian.com/technology/2012/dec/14/china-tightens-great-firewall-internet-control
[32] https://www.dezshira.com/library/legal/cyber-security-law-china-8013.html