SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsA single exploit that affects every iOS device made over an approximately 5-year period is massive.
WARNING: To be clear, the instructions below could result in bricking your device. Jailbreaking always carries risks and it is up to you to weigh the risk vs reward. Be sure to test these instructions on an exemplar device prior to an exhibit but bear in mind that just because it works once does not guarantee success on another device. Proceed at your own risk! You should read ALL instructions first BEFORE starting out. Missing or typing even one small instruction incorrectly will cause the task to fail. |
By Ian Whiffin (iwhiffin@gmail.com @blakdouble) and Shafik G. Punja (shafghp@gmail.com @qubytelogic)
There are already so many great articles on the web that detail this process that it feels unnecessary. What we will try to do differently from other articles is to bring as much information as possible into one place. It is not feasible to cover all eventualities, but this article will attempt to walk you through all the steps required to go from a fresh MacOS install and an uncompromised iOS Device, to having a Full File System (FFS) extraction from a freshly jailbroken device.
This is part 1 of a 4-part blog series that will cover the entire process from setup of the examiner machine, through to the analysis of the extraction.
Since its release back in September 2019, the iOS Exploit Checkm8 has seemingly taken the world by storm, and it's easy to see why. A single exploit that affects every iOS device made over an approximately 5-year period is massive. So much so that it has the attention of some of the biggest name vendors in forensics who are taking advantage of the exploit in their tools to extract full filesystems; something that only agencies with deep pockets could previously do.
I should state pretty early on for anyone who isn't familiar:
Tools such as those by Elcomsoft iOS Forensic Toolkit (EIFT) and Oxygen Forensic Detective (OFD) both produce FFS extractions of devices that are vulnerable to the checkRa1n jailbreak. Our testing has shown that the resulting TAR file is usable by ArtEx in exactly the same way that GK Extractions are.
The method we are going to focus on however is the method by fellow forensicator Mattia Epifani available at: https://github.com/RealityNet/ios_bfu_triage
This is a free and awesome tool that is pretty straightforward to use to obtain an FFS of a checkra1ned iOS device.
Apple computer (Some of these steps will also work on Linux but this is outside of the scope of this article).
Target iOS device must be vulnerable to Checkm8 and CheckRa1n.
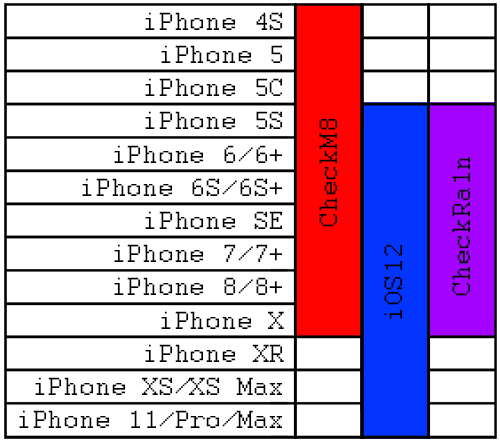
To add more clarity here, the exploit 'Checkm8' runs on any iOS device from an iPhone 4S up to and including an iPhone X. However, the jailbreak 'checkra1n' only works on devices running iOS 12.3 and above.
This means that there are some devices that are vulnerable to Checkm8 (such as the iPhone 4S and 5) but not checkra1n, because they cannot run iOS12 or above. There are also devices (such as the iPhone XR or XS) that will run iOS12 but are not vulnerable to Checkm8.
This leaves a sweet spot (in Purple in the table below) of around 7 generations of device that are vulnerable to the exploit (in Red in the table below) and are capable of running a supported version of iOS (in Blue in the table below).
In preparation for extracting a phone, there are a few pieces of software you need to install on your computer. Do these in the order they appear, as some of the tools are dependent on others. The following information with screenshots was compiled using MacOS 10.15.4 Catalina.
Download and Install Checkra1n on Mac
Download checkra1n from this location: https://checkra.in/. It is currently only supported on Mac and Linux in both GUI (Graphical User Interface) and CLI (Command Line Interface). The CLI also denotes the Terminal application on the Mac. In this article only the GUI Mac version will be shown.
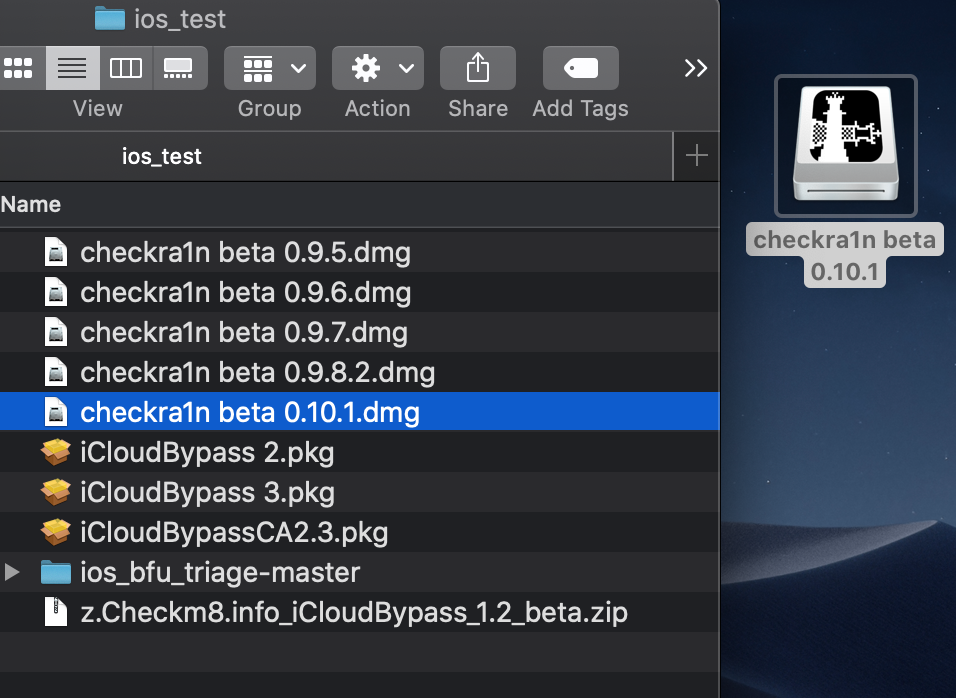
At the time of writing, the latest version was noted as 0.10.1 beta. The older releases of checkra1n based on a quick perusal, shows they are all beta previews. Review of the change log for the latest release 0.10.1 beta shows added support of iOS 13.4 and 13.4.1.
Once checkra1n is downloaded (on your Mac), in the location you selected, please install it.
This is done by double clicking the DMG file, which will mount and open the DMG (Mac disk image) on the desktop. This screenshot shows the checkra1n beta 0.10.1 DMG file mounted on the desktop.
Drag this file over top the shortcut icon of the Applications folder. This screenshot is showing the contents of the mounted checkra1n beta 0.10.1 DMG file on the desktop.
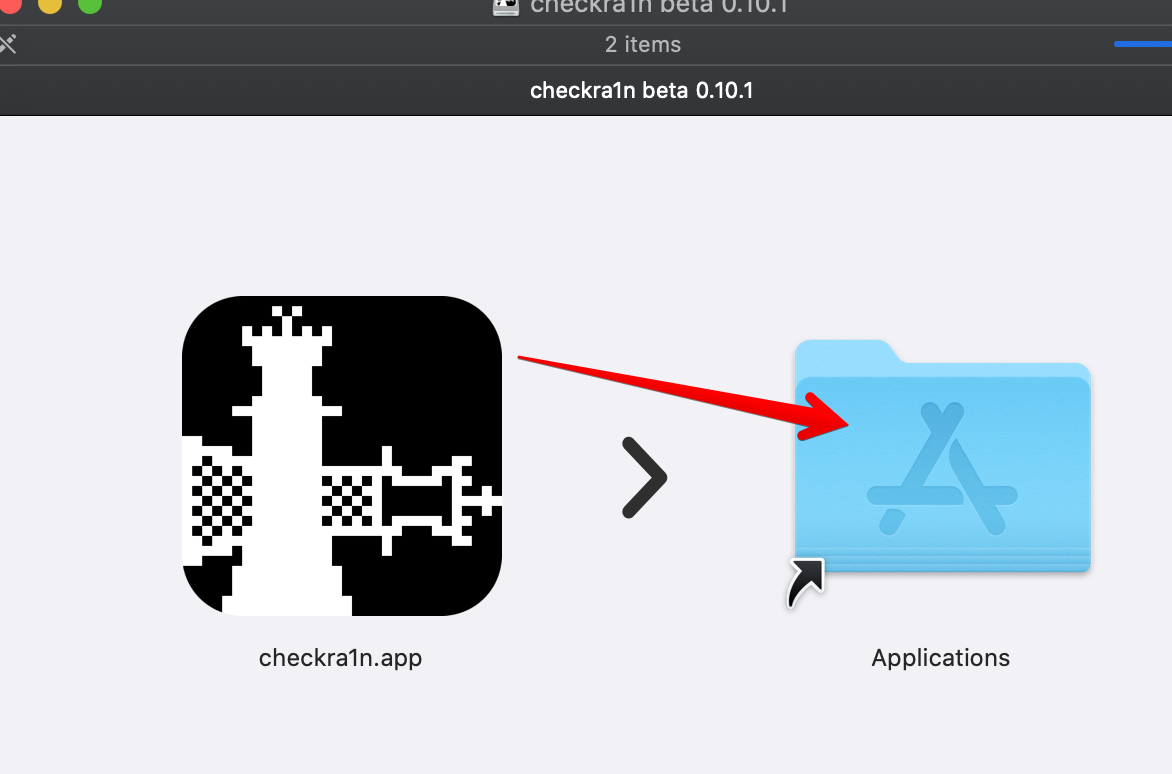
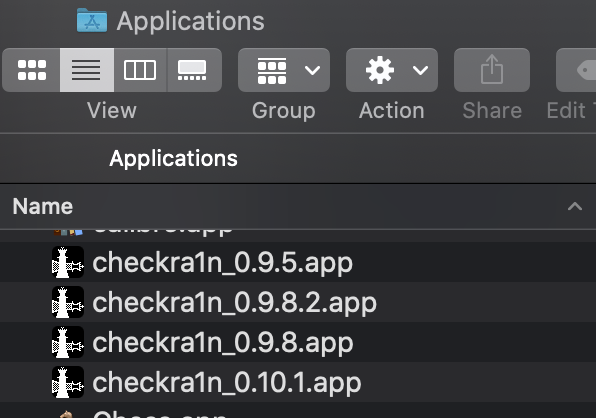
The Application folder now shows the checkra1n app installed. In this case it was renamed to checkra1n_0.10.1.app in order to distinguish it from other versions of checkra1n.
Why are we going on these side quests and installing more software tools? Because they are required for properly running the iOS BFU triage script. The iOS BFU triage script is named by the author. After the device is checkra1ned, this script has the ability to perform either a BFU extraction, which obtains a limited amount of data if the device is locked, or a complete full file system (FFS) extraction if the device is unlocked. Hence the reason for installing these tools now, so that you are ready to perform the extraction after the device is jailbroken with checkra1n. If you skip this part and try to run the iOS BFU triage script, you will fail at your task of obtaining an FFS.
The iOS BFU triage script instructions will be discussed in Part 3 of this blog post.
Install Xcode Command Line tools (CLT)
Xcode is the Apple Integrated Design Environment (IDE) used to create Apple Mac OS and iOS Applications. Typically, the IDE is a graphical interface and is available from the Mac OS App Store. However, for this process, you will need the Command Line Tools which do not get installed with the App Store version of Xcode. I typically install both, but the Command Line Tools should install without the need for Xcode.
The Command Line Tools (CLT) includes a module called GNU Compiler Collection (GCC) which includes libraries for various languages and is necessary for this extraction process to work.
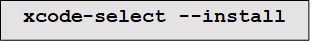
To Install Command Line Tools, start the MacOS Terminal and type:
Once installation has finished, you can type the following to ensure installation worked.
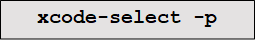
Which should return: /Applications/Xcode.app/Contents/Developer
You can also confirm that GCC is installed by typing:

Terminal Tips: *Sometimes, copying and pasting from website into terminal can include characters that cause issues. If any errors occur, try typing the command instead of copy/paste to see if the issue is resolved.
If this is the first time installing CLT for Xcode, and if you are on Mac OS Catalina, then the following reference is a good guide with screenshots:
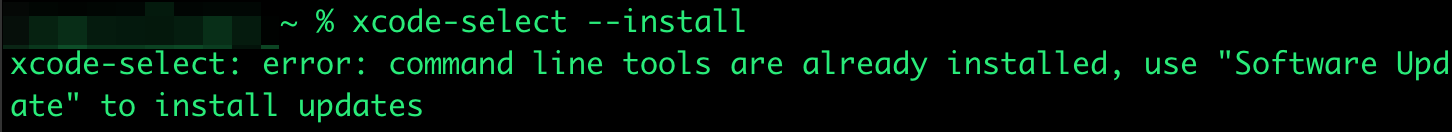
If you have previously installed Xcode, then you will see a different response from the Terminal. For example, in the terminal window shown below, the copy/paste did not work correctly due to extra characters from the HTML coding. As a workaround, we typed the command: xcode-select --install. The reply shows that CLT for Xcode is already installed.
Install Homebrew (brew)
HomeBrew is a free package management tool for MacOS. It makes it easy to install software from outside of the Apple ecosystem.
More information about HomeBrew can be found at https://brew.sh/
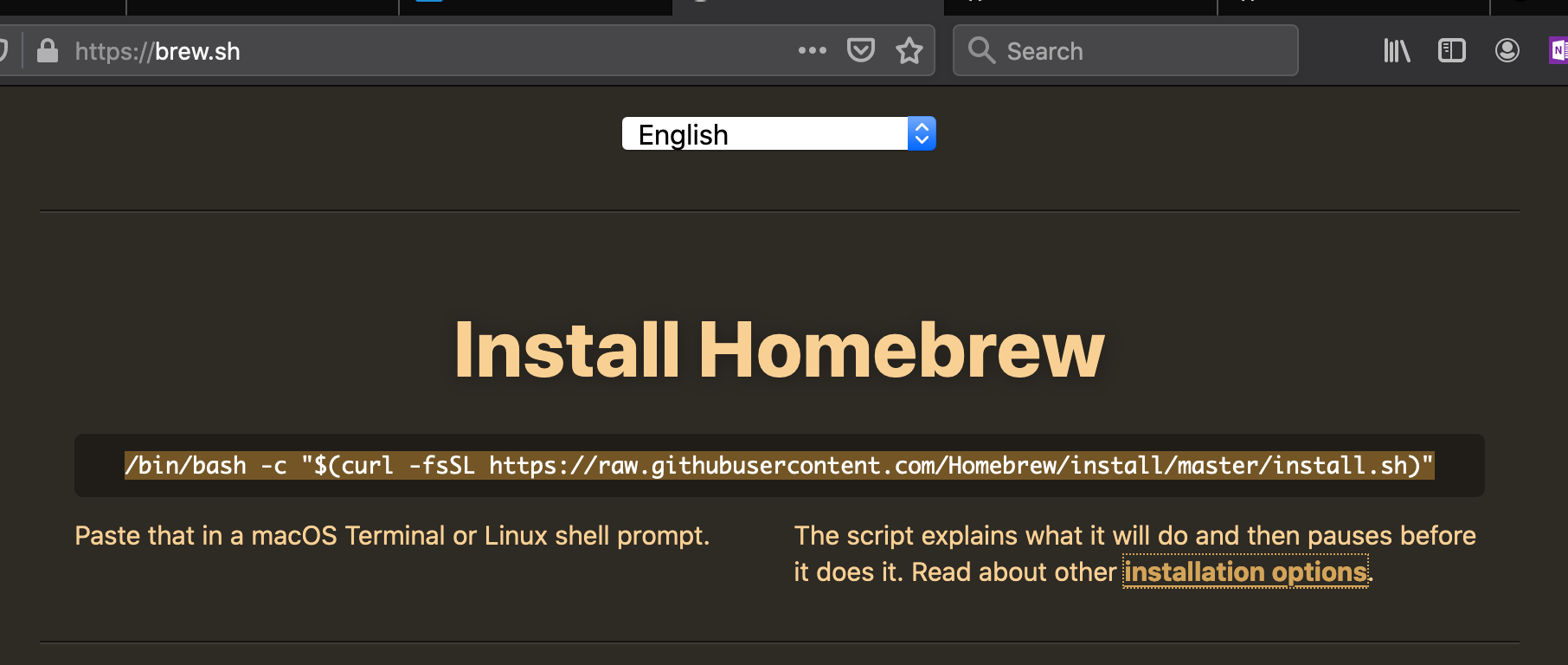
To install, enter the MacOS Terminal and type (or copy and paste) the following command and then press ENTER:
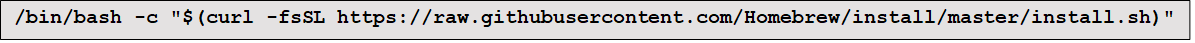
The terminal should respond by identifying what will be installed, and where brew will be installed to.
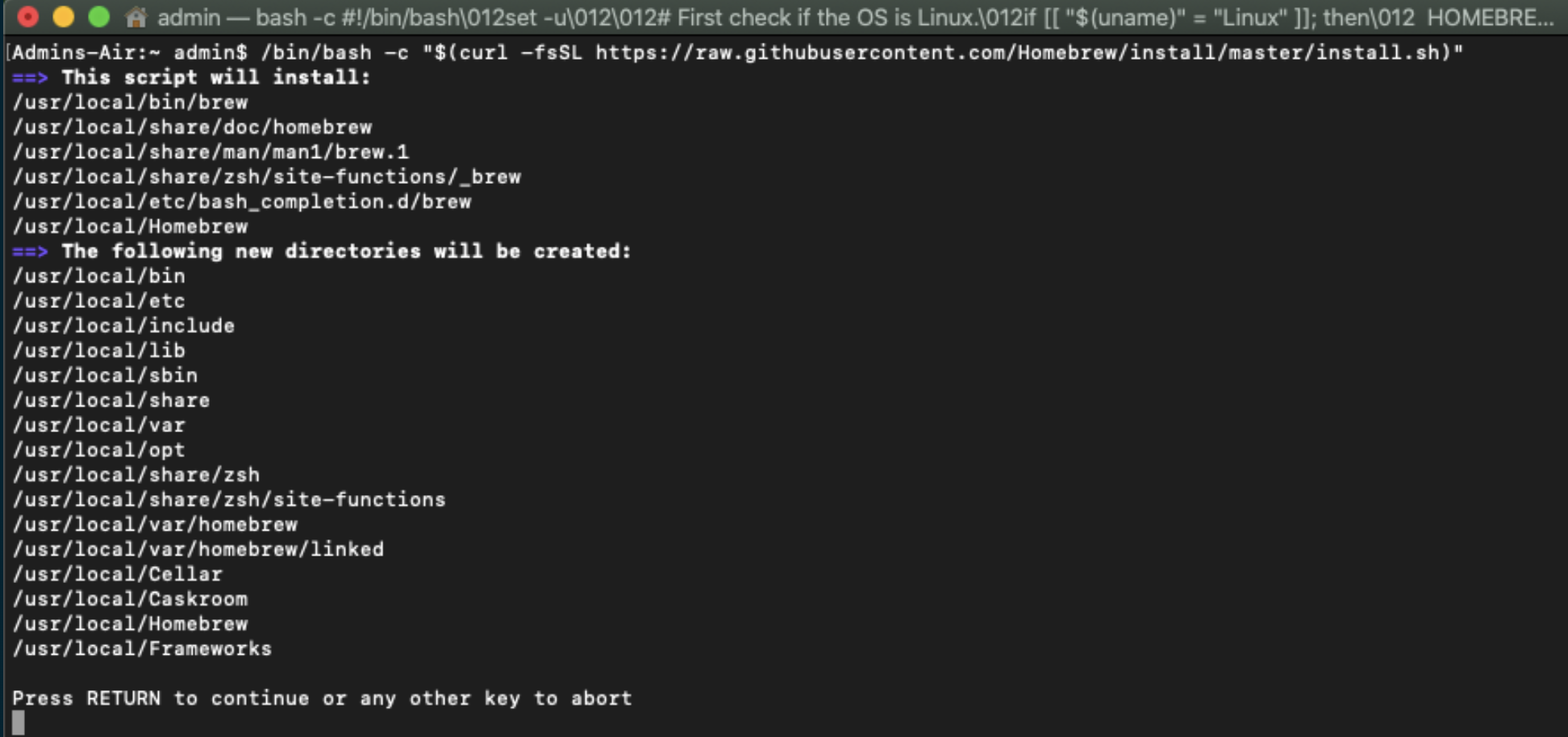
Press RETURN to start the installation.
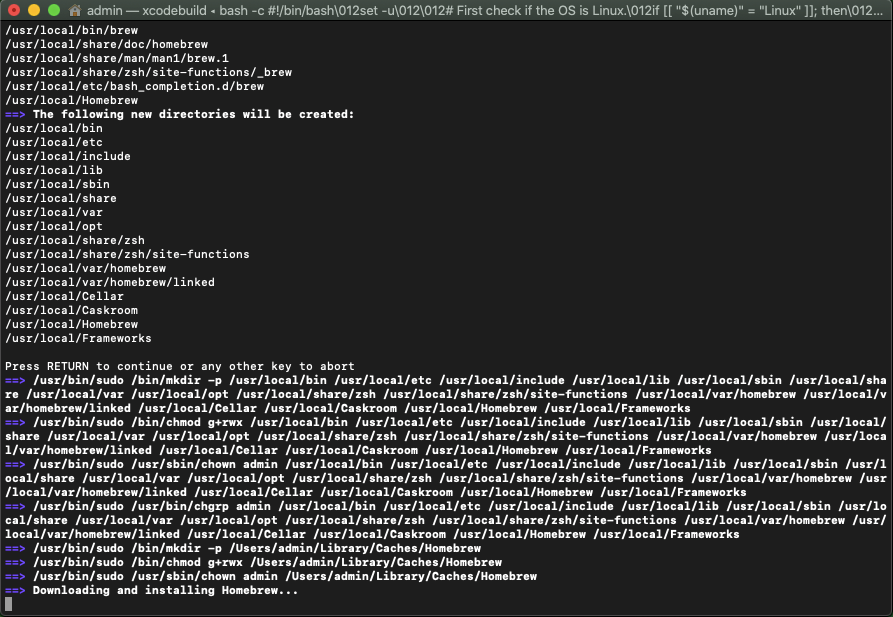
This process can take a good few minutes. Use that time to go make yourself a brew. :)
Install libimobiledevice
Information on libimobiledevice can be found at: https://www.libimobiledevice.org/
Basically, libimobiledevice is a cross platform protocol tool for speaking to iOS devices, and is installed via HomeBrew from the MacOS Terminal. To install libimobiledevice, type the command shown below in terminal and press ENTER.
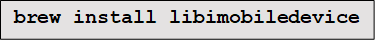
The terminal should respond with messages stating it is installing dependencies.
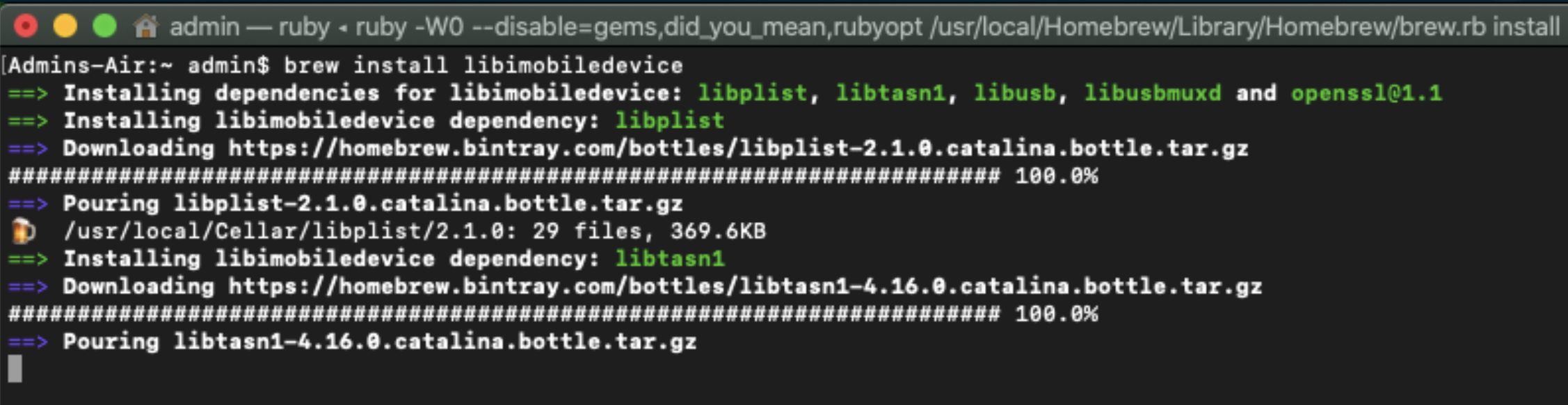
Install SSHPASS
Information on SSHPASS can be found at https://gist.github.com/arunoda/7790979
According to that page, SSHPASS is "a tiny utility, which allows you to provide the ssh password without using the prompt. This is very helpful for scripting." Again, we will use HomeBrew to install from the MacOS Terminal using the following command:
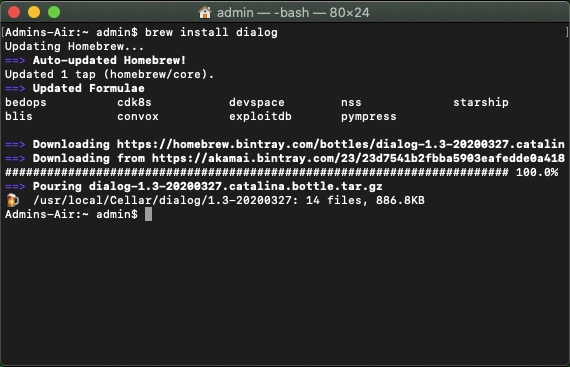
Install dialog
Dialog is little tool to make MacOS show user friendly dialog boxes from shell scripts. It is available from http://macappstore.org/dialog/
Again we will use HomeBrew to install from the MacOS Terminal using the following command:
We have now installed all the necessary tools and dependencies. In part 2 of this 4-part blog series, we will perform the actual jailbreak on a device.
The authors sincerely thank Kevin J. Ripa (@kevinripa) for taking the time to peer review this article. Kevin is a 25-year digital forensics veteran and Certified SANS instructor. He is one of the co-authors and instructors for SANS498: Battlefield Forensics & Data Acquisition, and also teaches the SANS SEC301, SEC401 and FOR500 courses.
Kevin Ripa has transformed the global cybersecurity landscape through decades of frontline digital forensics, assisting law enforcement, governments, and Fortune 500 companies in unraveling sophisticated cyberattacks and nation-state threats.
Read more about Kevin Ripa