SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsGo, Pokémon Go! I admit it. I was anxious to play Pokémon Go, the hot new "augmented reality" app. Not because I follow the newest styles and trends.

This post was originally posted on Murphy's Law Blog authored by SANS Certified Instructor Cindy Murphy
UPDATED 7/22/16 — Thanks to Warren Raquel (@warquel) a Senior Security Engineer at the National Center for Supercomputing Applications, Android location information has been SOLVED! See the Android Location Information section below.
"Some trainers have no fear. To them this is just one more challenge. They follow their hearts. That is what sets them apart, and will make them Pokémon Masters." — Miranda, Pokémon: The First Movie Pokemon Go Gameplay
Go, Pokémon Go!

I admit it. I was anxious to play Pokémon Go, the hot new "augmented reality" app. Not because I follow the newest styles and trends. Not because I spend a lot of time playing games on my phone. Not because I wanted to join zombie-like hoards in blind pursuit of invisible pocket monsters. I was anxious to play after reading about the application's Gmail privacy issues. I really wanted to see what the app stores on the phone it's installed on.
And for that, I needed test phone data!
I installed the app on a test iPhone and Android devices, created a "Trainer" account with a test Gmail account, and went to work?. er, play. Sometimes it turns out that work and play are one and the same. In the name of science.
Shortly after installation, I found myself in position to capture a blue, swirly, Poliwag near a curb. A few seconds later, "Gotcha!" Less than a minute later, up popped a Pidgey, in the middle of the road. So I stopped to grab him too, fully aware that I was in the middle of the road. I quickly gained insight into how this game could get dangerous.
"Gotcha!"

Things got strange pretty quickly. As I walked down towards the Wisconsin National Guard, Pokémon Go alerted me that there was a Pokestop and two Pokémon to be captured — behind the fence. Restricted AreaI decided not to go there. And as I swung my cell phone camera towards the secured area, I wondered if the images I might capture were going anywhere. And if so, where? Hundreds and thousands of Trainers running around the world photographing every nook and cranny in the name of capturing imaginary creatures? Conspiracy theorists will be having a field day. Gate guards will be having headaches!
I returned to the Gillware offices to find that my research was generating interest and enthusiasm. Or maybe it's that I'm working with like-minded people. Either way, the Gillware gang was also busy gathering data for research purposes (and fun, too), and they were anxious to share what they were finding with me. So, we sat down at lunch and geeked out over the forensic possibilities. Here's a little bit of what we found:
Pokémon Go on iOS The iOS test phone data I used contained data for a level 20 Pokémon Go trainer (that's a lot of research, right?). I performed a file system extraction using Cellebrite Physical Analyzer, and examined the data using a variety of mobile forensic tools — Physical Analyzer, Oxygen Forensics Suite 2015, and Magnet Axiom. The basic file system for the Pokémon Go app looks like this on iOS:

Forensic Artifacts — iOS
Much of the data we're interested in from a forensics standpoint on the iOS version of Pokémon Go is located in .plist files and .sqlite database files within the app. In fact, a number of the .sqlite database files located within the app contain embedded .plist files.
The com.nianticlabs.pokemongo.plist file contains the plain text Pokémon Go trainer user name and device information including the iPhone model number and iOS version, carrier information, and related data, and a hashed device ID.

iOS Date and Time Stamps
The data stored in the "bundles" directory was not in human readable format, and is encoded or encrypted. The date and time stamp for each of the blob-like files corresponds to when the game was being played. For now though, I have yet to answer the question about where those pictures are going, and also about how and if geo-location data related to user activity is stored within the app. If it is, it's likely in those mysterious "bundles," or maybe in the "com_upsight" folder.
The "com_upsight" sub directory in the Application Support folder contains three SQLite database files, each of which has multiple .plist formatted entries. A Google search shows that Upsight is a marketing and analytics platform for web & mobile application developers that assists in improving engagement and tracking user behavior. I'm still working on the .plist files stored there. Their dates and times also correspond with user activity. From a forensics standpoint, date and time stamps from these files can help us determine whether the game was being played when a particular incident happened.
Pokémon Go on Android The Android test phone data I used contained data for a level 5 Pokémon Go trainer. I performed a file system extraction using Cellebrite Physical Analyzer, and examined the data using Physical Analyzer, Oxygen Forensics Suite 2015, and Magnet Axiom. The basic file system layout for the Pokémon Go app looks like this on Android:

The com.nianticlabs.pokemongo.PREFS.xml file contains the account name for the user in plain text:

Android Date and Time Stamps
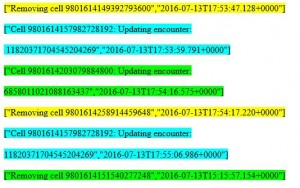
Inside the app data for the Android device there are a variety of Pokémon Go "encounter" dates and times logged in the com.crittercism folder in the subdirectory named "f". Crittercism (now known as Apteligent) is an Application Performance Management system. I don't know at this point in my research whether all events are logged or only events related to errors. Either way, there are a large number of individual files with the naming format 1.1468422937026.00000000X (where X is a sequentially progressing number) which contain really interesting data.
When these files are sorted by date/time, the sequential nature of the file names is clearly noted.
Date and time information is contained in text within the file in the format "YYYY-MM-DDTHH:MM:SS.MMM+00000", in addition to specific information about the event being logged. I noted a 5 hour offset in the time stamp. For example, the time stamp "2016-07-13T17:55:06.986+0000" corresponds to a file dated 7/13/2016 at 10:55 PM.
Sequential log filesLogged events appear to include:
Application errors Application loads Session starts Session finishes Wild Pokémon encounters Pokémon captures Encounter updates Successful encounters of wild Pokémon Additions of wild Pokémon Attempted encounters Caught Pokémon Cell removals This is good for forensic examiners. If we need to know whether someone was playing Pokémon Go at the time of a particular incident — say for example an armed robbery or a traffic accident, these Android based application files will be of great assistance.
Each of these files is a logged event in plain text that gives a short explanation of the event being logged and the time stamp. Location Information appears to be identified as "cells" with a long numeric number. It seems logical that these cells are likely mapped to GPS coordinates, but I'm still researching this.
Android Location Information -UPDATED 7/22/16
Collaboration is an amazing and rewarding thing. Thanks to Warren Raquel (@warquel) a Senior Security Engineer at the National Center for Supercomputing Applications, the Android cell location mystery has been SOLVED! Warren somehow came across this post and reached out to me shortly after it was published to tell me he had some theories about the location cell identifiers I had described above. He asked for some test data to work with.
I was exceptionally happy to have a new member of team Pokémon Go Forensics, and obliged. I sent him six examples of various cell identifiers from different Crittercism log files. Here's what the data I sent him looked like:
crittercism cell logs
Warren theorized that the 19 digit cell ID number could be two concatenated numbers which, when divided by 1e6 resulted in lat/long information. I found this post, and thought he was likely onto something.We both went to work (or is it play?).
Warren took the cell ID numbers and played with them in various ways. Shortly later, he emailed me and sent me the cell numbers converted to Hex:
Int -> HEX
9801614157982728192->8806542540000000 9801614149392793600->8806542340000000 9801614203079884800->8806542fc0000000 9801614258914459648->8806543cc0000000 9801614157982728192->8806542540000000 9801614151540277248->88065423c0000000 And he apologized (yes, really!). He'd been wrong and messed up the conversions. It didn't work. He said he hoped he'd been of some small help. Are you kidding me? Every little bit helps. Knowing the wrong answers gets us closer to the right ones. That's science. Warren made some guesses (let's call these alternate theories) and we both went back to the drawing board.
"Gotcha!!!"
Warren emailed me this morning to let me know he'd had a Pokémon Go "Gotcha!" moment. He captured this difficult artifact with a great deal of persistence and diligence. The cell numbers refer to Google's representation of the global map in a Hilbert Curve. He used the s2 library in order to convert one of my example cell ids (8806542340000000). Here's the output:
>>> import s2 >>> str(s2.S2CellId_FromToken("8806542340000000").ToLatLng()) ?[43.1182500, -89.3309966]\x00' >>> s2.S2CellId_FromToken("8806542340000000").level() 15 Yep! That's right in the Gillware neighborhood! Here's what that location looks like on a map:

As far as the 19 digit encounter ID is concerned, Warren and I both think that it's likely a 64bit representation of a particular Pokémon that contains bits to represent characteristics like type of Pokémon, strength, and that sort of thing. I'll be looking into my Pokédex to make some comparisons, for sure. Thanks again, Warren (@warquel) for the time and effort you took researching this location artifact and figuring out the cell location mystery. Nicely done!
The Android App I used the tools and tips from last week's HummingBad post to peek into the Pokémon Go app. There's a lot there to get through, but it gives some insight into some of what we see stored on the phone itself, and potentially about the way data is stored on the device and where it might go. Here's what the layout of the apps classes looks like in Dex2Jar:
App Structure

That's the way forensics goes most of the time, and part of why it's such an adventure. Anything you dig into can potentially send you down another interesting path in pursuit of forensic artifacts. And digging into an app like Pokémon Go is just as much fun (if not more) than playing the game itself.
CLASSROOM TRAINING
SANS Virginia Beach 2016 Virginia Beach, VA | Aug 22 - Sept 2
SANS Network Security 2016 Las Vegas, NV | Sept 12 - 17 (Simulcast option)
Community SANS Madison FOR585 Madison, WI | Sept 19 - 24
SANS Baltimore 2016 Baltimore, MD | Oct 10 - 15
ONLINE TRAINING
Learn at your own pace with four months of online access:
Cindy Murphy served in law enforcement for more than thirty years, serving as a detective and a certified digital forensics examiner.
Read more about Cindy Murphy