SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact Us
Hex editors allow examining and modifying a file at the low-level of bytes and bits, usually representing the file's contents in hexadecimal form. Some editors distinguish themselves at helping the user derive meaning from the examined file, extracting ASCII and Unicode contents, searching for patterns, recognizing common structures, and so on. There are lots of hex editors out there; I want to mention a few that I find particularly useful for analyzing malware and examining malicious document files.
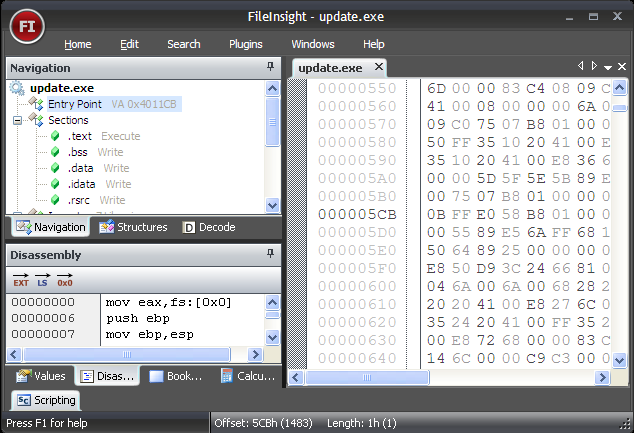
FileInsight is a free hex editor from McAfee Labs that runs on Microsoft Windows (download zip file). As expected, it can perform standard hex editor duties, such as viewing and editing file contents in a hex form, but it also does more than that.
FileInsight is able to parse the structure of compiled Windows executables (PE files) and binary Microsoft Office (OLE) documents. Furthermore, the tool has a built-in x86 disassembler: simply point the cursor at the area of the file you want to treat as code, and the tools will show you the corresponding assembly instructions. The disassembler is especially helpful when looking at shellcode embedded in malicious files.
FileInsight includes numerous other analyst-friendly features, such as the ability to import data structure declarations, HTML syntax highlighting, and tools for decoding various data obfuscation methods (xor, add, shift, Base64, etc.). FileInsight also allows you to automate actions using JavaScript and Python.
The tool's biggest weakness is, perhaps, its inability to open very large files. For instance, when attempting to load a 512MB file, FileInsight produced a "Failed to open document" error. Also, FileInsight does not support searching for Unicode-encoded strings that look like ASCII strings.
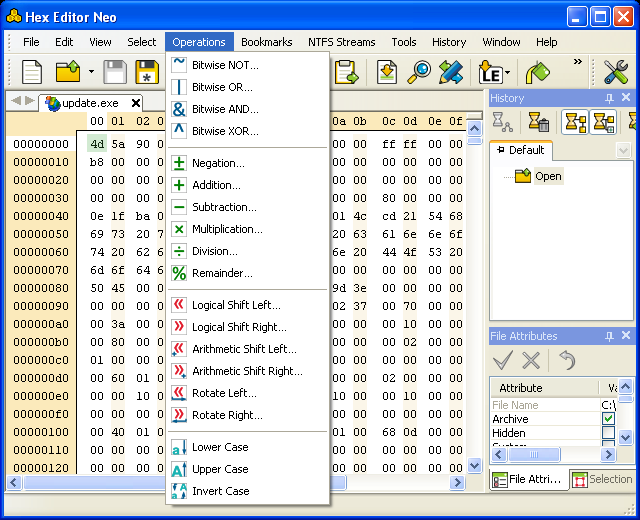
Hex Editor Neo is available as free and commercial versions for Microsoft Windows from HDD Software. Its freeware version provides typical hex editor features in a friendly and highly-customizable interface, but is not particularly impressive. However, unlike FileInsight, all versions of Hex Editor Neo can open very large files and allows user to look for ASCII and Unicode-encoded strings.
The features of Hex Editor Neo relevant to malware analysis are present in its commercial versions (see version comparison). For instance, the Standard version introduces the support for handling data manipulations, such as decoding, encrypting and deobfuscating using common algorithms. (Notably, these features are included for free in FileInsight.) The Professional version introduces support for viewing and editing local resources, such as NTFS streams, local disks, process memory and physical RAM. The Ultimate version includes scripting support and built-in disassemblers for x86, x64 and .NET code.
FileInsight is probably a better match than Hex Editor Neo for regular malware analysis use. However, Hex Editor Neo's commercial versions add value to the toolkit by supporting very large files, x64 and .NET disassembly, local resource editing, searching for Unicode strings and extensive customization support of its user interface.
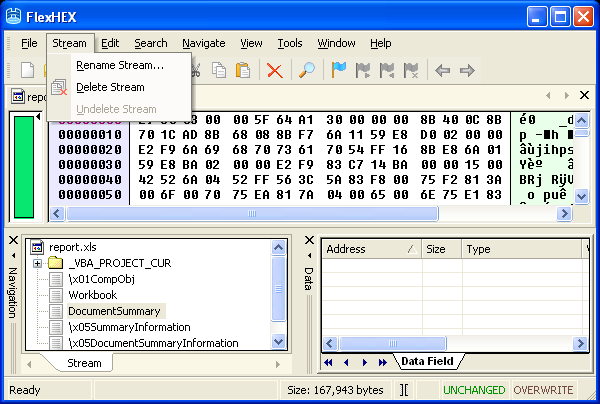
FlexHex is a powerful commercial hex editor from Heaventools Software that includes many features comparable to commercial versions of Hex Editor Neo, though FlexHex does not support scripting.
FlexHex only stands out from Hex Editor Neo in its ability to parse binary Microsoft Office (OLE) documents. However, FlexHex might get confused when attempting to parse some malicious OLE files, presenting a "The docfile has been corrupted" error. Overall, this is probably the weakest editor of those examined here from the perspective of a malware analyst.
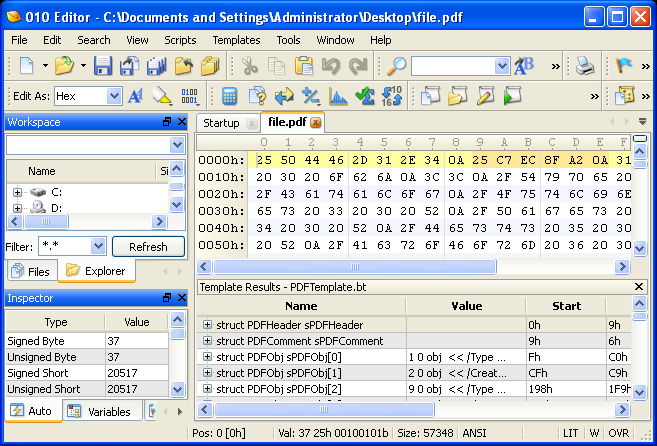
010 Editor is a commercial hex editor for Microsoft Windows from SweetScape Software. Its core features are comparable to those of the commercial versions of Hex Editor Neo and FileHex: support for very large files, data manipulation, local resource editing, and so on. Like Hex Editor Neo, 010 Editor also supports scripting.
010 Editor shines in its ability to parse various file formats by using a large library of user-contributed templates. This makes it easier for the analyst to navigate various file formats, including Windows executables (PE files), Windows shortcut (LNK) files, Zip archives, Java Class files, and many more. Malware analysts will particularly appreciate the template for parsing PDF files that Didier Stevens created for 010 Editor. You can also download several user-submitted 010 Editor scripts from its website.
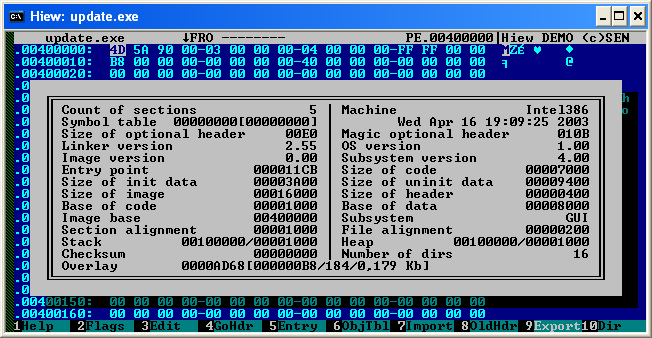
Hiew is a commercial hex editor by Eugene Suslikov for Microsoft Windows. It is a favorite among many malware researchers due to the powerful features for examining and editing the structure and contents of Windows executables (PE files) and Linux binaries (ELF files). Another very useful feature for reverse-engineering malicious programs is the tool's ability to disassemble and assemble x86 and x64. Hiew's disassembler even supports the ARM instruction set. Hiew can handle very large files and edit local logical and physical drives. It supports macros, scripts and even has an API set for additional extension and automation.
It works in a DOS-style console window and is generally unfriendly towards a new user, in comparison to the other hex editors I discussed so far. It's a powerful hex editor, but is not well-documented. For those who don't already know how to use it, it probably isn't the best tool to get started with, given the number of other powerful hex editors and disassemblers available.
Radare is a set of free tools for Unix platforms that include powerful hex editing capabilities. Radare's features are too numerous to list here, and include support for examining and tweaking Windows executables (PE files), Linux binaries (ELF files) and Java Class files, comparing binary files, as well as disassembling, reassembling and debugging code. The tool also includes shellcode generator, which is particularly relevant for those who analyze vulnerabilities and exploits. The capabilities of Radare are extensible and scriptable.
The drawback of Radare is that it is a command-line tool that is difficult to master. Fortunately, it includes rather extensive documentation. Radare is of particular interest for analysts who prefer working in Unix environments with command-line tools. (Radare is included in the REMnux distro for malware analysis.)
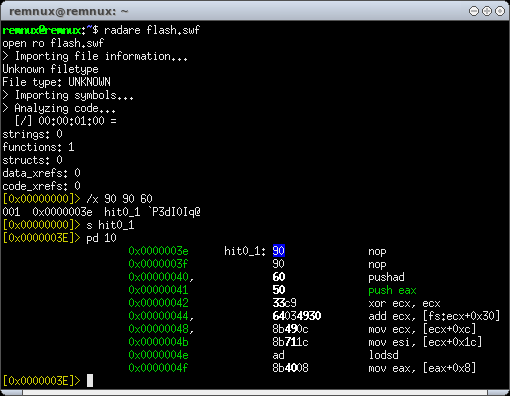
We looked at several powerful hex editors that included features useful for analyzing malicious software. Of these, FileInsight stood out for its overall feature set that malware analysts find useful on regular basis. 010 Editor provided a large number of templates for parsing file, including PDF documents, and was highly customizable. FlexHex included support for parsing some binary Microsoft Office (OLE) files, but otherwise did not stand out. Hex Editor Neo expanded the toolkit by being able to disassemble x86, x64 and .NET code. Radare offered comprehensive, but hard-to-use command-line capabilities for Unix platforms. Hiew included powerful features for tinkering with compiled executables, but was not-user friendly.
| Hex Editor | Highlighted Features | Highlighted Limitations |
| FileInsight | Built-in x86 disassembler Many data decoding methods Scriptable Parses PE and OLE formats Free | Cannot handle very large files |
| Hex Editor Neo | Built-in x86, x64, .NET disassembler Many data decoding methods Handles very large files Scriptable Highly-configurable interface | Advanced features in commerical version |
| FlexHex | Parses OLE format Handles large files Some data decoding methods | Not scriptable Commercial |
| 010 Editor | Parses many formats, including PE and PDF Support for custom parsing templates Many data decoding methods Handles very large files Scriptable | Commercial |
| Hiew | Built-in x86, x64, etc. disassembler Built-in reassembler Handles very large files Many data decoding methods | Commercial Hard to use Not well-documented |
| Radare | Built-in x86, x64, etc. disassembler Built-in reassembler Handles very large files Many data decoding methods Free | Hard to use |
Personally, FileInsight and 010 Editor offer the most value for my malware analysis work on Windows and Radare on Unix, leaving FlexHex, Hex Editor Neo and Hiew in the "nice-to-have" category. Of course, everyone has his or her own preferences. What's your favorite hex editor?
Lenny Zeltser focuses on safeguarding customers' IT operations at NCR Corporation. He also teaches how to analyze malware at SANS Institute. Lenny is active on Twitter and writes a security blog.


Lenny Zeltser, CISO at Axonius, is a leader in developing resilient security programs. His invaluable tools, like REMnux, a widely used Linux distribution for malware analysis, have become industry standards in combating malicious software.
Read more about Lenny Zeltser