SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals
Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsThe memorandum outlined findings and recommendations for improving perceived deficiencies with one of its information sharing programs.

Note: We intentionally held off on publishing this blog until we felt adequate time had passed where we would not influence potential US Government cybersecurity policy discourse.
In late September 2024, the U.S. Department of Homeland Security's (DHS) Office of the Inspector General (OIG) released a memorandum to the Cybersecurity and Infrastructure Security Agency (CISA) Director Jen Easterly. The memorandum outlined findings and recommendations for improving perceived deficiencies with one of its information sharing programs surrounding the "Automated Indicator Sharing (AIS) 2.0 capability."
For context, CISA created the AIS program in 2016 to enable real-time exchange of machine-readable cyber threat indicators (CTIs) – referred to as Indicators of Compromise (IOCs) by the cyber security community – and defensive measures. The program aims to help protect the networks belonging to AIS community participants. In March 2022, CISA upgraded the system to AIS 2.0.
The OIG reported a decline in participation in the AIS program, attributing it to CISA's inability to identify specific program costs and audit expenditure. The report suggested that these financial management issues hindered AIS’s effectiveness in facilitating real-time cyber threat sharing. However, the report erroneously represented AIS as CISA’s sole mechanism for real-time cyber threat information sharing with the private sector, ignoring CISA’s broader efforts to enhance this capability against threats from hostile nation-state and ransomware actors. The report did not evaluate the program’s impact on threat prevention or mitigation; according to the appendix, CISA is in the process of providing such information to the OIG for review.
To its credit, the OIG may focused its evaluation solely on machine-to-machine shared IOCs rather than higher-quality indicators containing surrounding threat activity specific context. The focus on "real-time" machine-to-machine data appeared to largely be evaluated on throughput rather than more useful metrics, as noted above. The report acknowledges that this was just one of many information-sharing capabilities encapsulated in the $31M and $35M expenditures in 2021 and 2022, respectively. It also acknowledges a longer-term vision under the department’s Threat Intelligence Enterprise Services (TIES) strategy. At least one other information sharing capability—CISA’s Enhanced Cybersecurity Services—was identified as an information sharing capability designed to share sensitive and classified cyber threat information with accredited commercial service providers to detect and block malicious cyber activity.
The Cybersecurity Act of 2015 established a voluntary process for public and private-sector entities to share cyber threat information with each other. The Act requires the Director of National Intelligence (DNI), secretaries of DHS and the Department of Defense (DoD), and the Attorney General (AG) to devise a process to facilitate and promote sharing classified and unclassified CTIs, defensive measures (DMs), and best practices to mitigate cyber threats to the Federal Government and private sector.
In 2016, CISA established the AIS as a solution promised by the Cybersecurity Act of 2015, allowing for real-time exchange of machine-readable IOCs and defensive measures. The AIS program was designed as a mechanism to share information at no cost to participants while allowing them to voluntarily share and receive unclassified cyber threat information. In March 2022, CISA improved its submission process and interface in what is referred to as "AIS 2.0." In a lot of ways, this model was designed as a national-level Information Sharing and Analysis Centers (ISAC) lite model as a central entity to push and pull related information on cyber threats. This is the fourth report issued by the OIG since AIS's inception, taking place on a biannual cadence with the findings of the previous three available in OIG-22-59, OIG-20-74, and OIG-18-10.
AIS is composed of three different IOC collections, represented as Structured Threat Information eXpression (STIX) objects shared via Trusted Automated eXchange of Indicator Information (TAXII):
The AIS capability shares machine-readable STIX objects from various CISA-published products to include its indicator bulletins, activity alerts, and analysis reports.
The OIG's assertion that the cyber threat information sharing vis-a-vi the AIS sharing program hinges on two data points raised primarily in its executive summary:
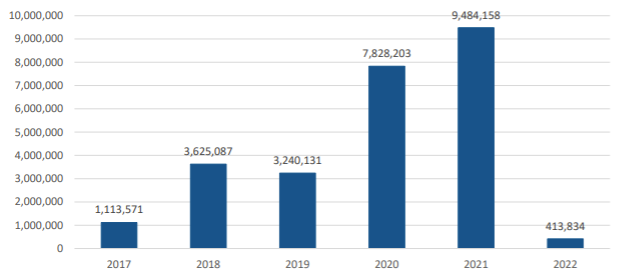
Yet, as we dig into the body of the report, it is hard to argue with the orders of magnitude drop off in indicators shared after the program changed hands to an unspecified government entity due to requirements in the National Defense Authorization Act. Specifically, in 2021, the outgoing Federal partner shared approximately 9 million indicators through AIS whereas in 2022, after the incoming Federal partner took ownership of the system, this number fell to 16,697, representing a decrease of more than 99 percent.
Technically, using their identified highly scoped criteria to evaluate the effectiveness of AIS, they sufficiently answered the mail. Where the analysis, presentation, and recommendations fall short are in a few areas:
For a deeper understanding of the cyber threat landscape and information sharing measures enacted by the government, check out the FOR578TM: Cyber Threat IntelligenceTM course. This course is designed to equip you and your organization with the level of tactical, operational, and strategic cyber threat intelligence required to better understand the ever-evolving threat landscape and how to effectively counter those threats. Ready to take the next step? Register today or request a demo to see this course in action!


John has over sixteen years of experience working in Cyber Threat Intelligence, Digital Forensics, Cyber Policy, and Security Awareness and Education.
Read more about John Doyle