Make a Difference in the Cyber Community
This year, SANS is fortunate enough to partner with the Blind Institute of Technology to make a difference in the cyber community. Currently, 81% of people with disabilities are unemployed. The Blind Institute of Technology (BIT) Academy is committed to changing these statistics by working diligently with their candidates and their corporate partners to place people with disabilities in meaningful careers with a clear path for growth. The services offered through the BIT Academy are complimentary for all of their candidates with disabilities. However, it costs BIT $5,400 for each candidate to go through their 16 week Salesforce and Cisco certification classes. As a 501(c)(3) non-profit organization, they are highly dependent on corporate donations, individual donations, and grants. With a retention rate of 93% of its candidates that are placed in meaningful careers, every $5,400 raised enables them to change a person's life forever.
SANS and BIT would greatly welcome and appreciate your financial support to help them continue to change the lives of people with disabilities.
Attendee Information
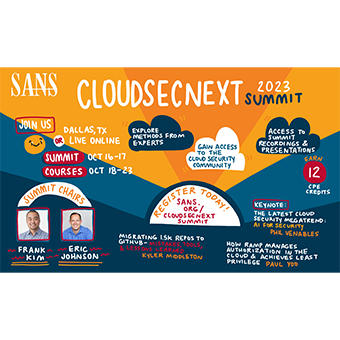
Rub virtual shoulders with professionals in your field and zero-in on the most relevant cyber solutions by registering for one of our four topic tracks. This event will bring together cyber security professionals of all experience levels from around the world for this two-day immersion into the latest cyber solutions, tools, and techniques to combat today’s threats.
Take a sneak peek of what you can expect from the experts themselves, when you join us to elevate your cyber skills and solutions know-how.
Continuing Professional Education (CPE) Credits are earned by participation in the event!
- 6 CPEs are earned each day for attending Cyber Solutions Fest 2022
- Yes, that's correct. You will earn 12 CPEs total for spending October 13th and 14th with us!
Agenda | October 14, 2022 | 8:30AM - 5:00PM
Timeline (EDT) | Session Details |
|---|---|
8:30 AM | Kickoff & WelcomeDave Shackleford, Senior Instructor, SANS Institute |
8:45 AM | Nudge and Sludge: Rethinking Cloud Access ManagementWe must secure our organization’s processes regardless of what tech they run on. Originally, security leaders had leverage. We controlled the horizontal. We controlled the vertical. And if people wanted to work, they needed to follow our rules to access corporate apps and services. But then came Cloud apps, and BYOD, and consumerization, pushing security beyond our outer limits. Security happens where psychology and technology intersect. The everyday decisions of employees increase or decrease an organization’s risk. Employees don’t need us. And by employee, I mean more than end-users. This is a broader conversation; including software developers, IT engineers, DevOps practitioners, and more. To get people to opt in and follow secure practices, IT security leaders must offer them a compelling experience. Come learn how. J Wolfgang Goerlich, Advisory CISO, Cisco Secure |
9:25 AM | Cloud Adoption Disrupts Threat Detection and ResponseAre your security monitoring capabilities sufficient for quickly detecting and responding threats to cloud and cloud-native environments? Organizations are increasingly building or hosting applications using cloud services, container technology stacks, and serverless abstractions. Traditional security approaches often fail to maintain visibility across all environment types in runtime, struggle to analyze the high volumes of signals, or can’t contend with ephemeral workloads that are common in modern architectures. Attend this session to understand:
Michael Isbitski, Director of Cybersecurity Strategy, Sysdig |
10:05 AM | Break |
10:20 AM | Attacking the Cloud: the Full Identity Kill ChainHow are attackers exploiting vulnerabilities in your cloud? This presentation will visually demonstrate a hypothetical attack on a company fully deployed in AWS, enabling you to prepare for them in your own company. Our team will take you through the whole kill chain, starting with privilege escalation techniques. Then expand the attack on an EC2 instance or S3 bucket. Using the identity’s role, we will permission chain our way through the AWS services to escalate privileges to admin. Finally, we’ll demonstrate various techniques for exfiltrating data from the AWS environment. Knowing how bad actors move through trust relationships arms you with best practices to prevent and remediate attacks. Rob Cobbins, Principal Solutions Architect, Sonrai Security |
10:50 AM | Unblock Your Cloud Transformation or Business Growth Initiatives with Confidential ComputingMany organizations wish to embrace the cloud to modernize operations or develop new business opportunities but are blocked by regulations or internal security mandates for securing and ensuring the privacy of data. Hear about these business challenges and learn how a breakthrough in security called Confidential Computing can unblock them. Mark Bower, VP Product, Anjuna |
11:20 AM | Converged NetOps and SecOps – A United Force to Protect the Integrity of the Hybrid CloudCybercriminals are working smarter, not harder. Naturally, they are going to find the weaknesses in an organization and exploit them wherever possible – and it’s not a matter of if, but when, most organizations will experience a breach. One of the key areas they are attacking is in the hybrid cloud. As wonderful as the cloud is in terms of cost savings and scaling your business, it also introduces new challenges and complexities. In fact, managing your network is not as simple as it used to be. You can no longer assume that network or cloud performance issues are related to some bad configuration or a failing hardware device – we now often see cyberattacks driving latency or jitter issues. Security-driven performance issues have also complicated problem detection and incident response. Because of this, NetOps and SecOps can no longer act as independent teams. They must collaborate closely together and leverage solutions that are closely integrated, providing a single platform for both performance and security. There is growing mindshare and adoption of a converged network and security operations model. Michael Bacon, Director of Enterprise Solution’s Marketing, Accedian |
11:50 AM | Break |
12:00 PM | In the Trenches with Top Cyber ExpertsDuring this keynote, SANS’ John Pescatore and several SANS instructors and leaders of the cybersecurity community will share their experiences with from times in their careers where they were brought in by companies and government agencies on cybersecurity incidents, audits/test or other critical business/mission areas. Join this fascinating discussion where they will dive into some breaches and stories of their experiences in the cyber trenches – and maybe also in corporate boardrooms. Moderator: |
1:00PM | Afternoon Kick-offDave Shackleford, Senior Instructor, SANS Institute |
1:10 PM | Cloud Purple Teaming ProcessesCisco Talos has performed four cloud purple teaming engagements, developing an intelligence-led adversary emulation process to test the efficacy of our products and outline detection gaps that we can then solve. Our research allows us to continually devise new ways to detect suspicious behavior and keeps us ahead of threat actors. Darin Smith, Cloud Security Researcher, Cisco Talos |
1:30 PM | Boosting your TDR with Cloud Detection and ResponseCloud and container adoption are disruptive forces for threat detection & response (TDR). Organizations must contend with multiple workload types, high volumes of containers, short workload lifetimes, and ineffectiveness of traditional endpoint controls. These impacts drive the need for improved TDR capabilities for modern environments so that practitioners can quickly detect and respond to threats.
Nigel Douglas, Technical Marketing Manager, Detect and Response, Sysdig |
1:50 PM | The Future is Faster: Accelerating Patching From Months to HoursDespite dramatic shifts across nearly every aspect of IT and security, patching remains a holdout for organizations shifting to cloud infrastructure. Adversaries continue to cut the time to weaponize a vulnerability from months to weeks to days while the average time to patch a vulnerability continues to climb. Today, we are faced with a worldwide average of over 200 days to patch a vulnerability while our adversaries are accelerating. It's time to flip the script and take patching from months to hours, closing the door, and securing our infrastructure. Jay Goodman, Product Marketing, Automox |
2:20 PM | Eliminate Security Blind Spots: How to Get 100% Cloud VisibilityYou cannot protect what you can’t see. So why are so many organizations still using legacy cloud security solutions that rely on agent deployments and come with many blind spots? Attend this session to learn: - How to get 100% wide and deep visibility into your cloud assets and risks - How only a true consolidated platform has the contextual intelligence to accurately prioritize risk - How alert fatigue and missed critical alerts can be avoided with attack path analysis and scoring - Which 4 'Cs' every cloud security platform should be built on Deborah Galea, Director, Product Marketing, Orca Security |
2:50 PM | Improving Cloud Security posture with Attack Surface ManagementAs your organization continues to rely on the cloud to centralize its business operations, new challenges arise when new cyber assets are added to your environment — extending your attack surface, unbeknownst to your IT and security teams. In this session, Cara Seely, Senior Solutions Architect at JupiterOne, will discuss how maintaining a continuous inventory of your cyber assets – well beyond endpoints, IP addresses, users, and devices – is critical to understanding the scope of your attack surface. Find out how you can use this information to optimize cloud configurations, ascertain your cloud security posture management, enhance your SecOps workflows, address compliance, and more. Cara Seely, Senior Solutions Architect, JupiterOne |
3:20 PM | Break |
3:35 PM | Why Data Protection Strategies MUST Include API SecurityData security initiatives have traditionally focused on structured and unstructured data, data loss prevention (DLP) solutions and other tools that focus primarily on the network to prevent sensitive data exfiltration. However, the majority of sensitive data now flows through APIs. We need to start looking beyond traditional methods of protecting data and realize that APIs are the top vector at play, and have already caused massive data breaches and operational downtime for several different industries. In this session, learn the different ways that APIs are hacked, what specifically to look for in potential API threats, and what you can start doing today, in order to detect and stop API threats in your environment. We will cover how building baselines of sensitive data usage by the standard user population vis a vis suspicious users, API call flow, inter API time intervals, as well as device fingerprinting, can help prevent sensitive data exfiltration via APIs. The talk will include real-life examples of how a range of API abuse patterns have been detected using this approach. Sudeep Padiyar, Director, Product Management, Traceable AI |
4:05 PM | Panel: Are We There Yet? A Discussion on the State of Cloud SecurityAs the relentless march to cloud continues on, organizations are realizing that there are numerous strategic and tactical decisions that need to be made, many dependent on the types of cloud deployments in flight (lift and shift, cloud native services, serverless, etc.) as well as the use cases for cloud access and configuration. With more remote users accessing the cloud directly, how can enterprise security protect them? How can cloud configuration management and security posture be measured and maintained? In this panel, we’ll touch on a variety of current real-world topics, also highlighting some critical lessons learned from organizations that have made the journey and discovered some of the challenges they faced along the way. Join our panelists in a free flowing discussion that will touch on these cloud security topics and more. Moderator: Panelists: |
4:55 PM | Wrap-UpDave Shackleford, Senior Instructor, SANS Institute |




.png)