SEC595: Applied Data Science and AI/Machine Learning for Cybersecurity Professionals


Experience SANS training through course previews.
Learn MoreLet us help.
Contact usBecome a member for instant access to our free resources.
Sign UpWe're here to help.
Contact UsCloud security encompasses technologies, policies, and controls that protect data, applications, and infrastructure in cloud environments. Knowing how to safeguard sensitive information in cloud environments is crucial for preventing cyber threats, ensuring compliance, and maintaining business continuity.

Cloud security is business-critical, requiring cyber professionals to navigate evolving threats, secure cloud environments, and align security goals with business objectives. At SANS, we believe that effective cloud security training should be a business enabler that evolves as fast as the technology. It must equip practitioners with hands-on technical expertise, in-depth knowledge of multiple Cloud Service Providers (CSPs), and strategic insight to build sustainable security practices in an era where innovation outpaces workforce knowledge.
Learn to build secure, resilient cloud environments and align security frameworks with business strategy.
Develop the ability to monitor, detect, and respond to cloud-specific threats and security breaches.
Design and deploy automated security controls, IaC protections, and proactive defenses in cloud-native environments.
SANS is a world leader in Cloud Security for a reason. I'm never disappointed when I attend sessions, and I know I'm in for a torrent of incredibly useful information.


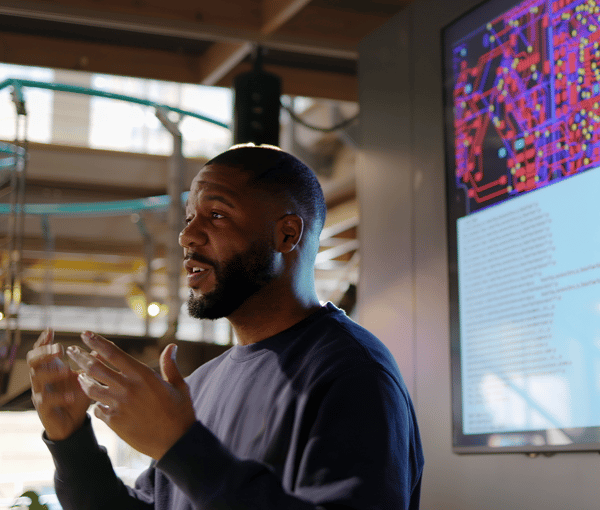
Ahmed AbuGharbia, SANS Instructor and SEC545 author, helps practitioners secure generative AI systems by identifying risks, understanding model behavior, and applying practical security controls.
Learn more
Brandon Evans, SANS Senior Instructor and lead author of SEC510, guides cloud and DevSecOps professionals in securing AWS, Azure and GCP workloads through hands-on training.
Learn more

Eric Johnson is a Fellow at the SANS Institute and Principal Security Engineer at Puma Security. He leads hands-on training in SEC540: Cloud Native Security and DevSecOps Automation, co-authors SEC549 and SEC510, and develops open-source tools to help practitioners secure cloud pipelines.
Learn more

SANS Fellow Frank Kim helps to develop the next generation of CISOs and cyber leaders while teaching LDR512 and LDR514.
Learn more
Shaun McCullough spent 20+ years at the NSA working in cyber operations as a software engineer and technical director of Blue, Red, and Hunt teams. He is currently a staff level Cloud Security Engineer at GitHub.
Learn more

Ryan Nicholson, SANS Senior Instructor and SEC502 and SEC541 author, brings DoD and cloud security experience to help practitioners detect threats, secure modern environments, and apply defensive strategies that work in real-world operations.
Learn moreNon-human identities are multiplying, and static secrets can’t keep up. This webcast shows how SPIFFE enables dynamic, short-lived credentials and runtime authorization to secure modern cloud workloads without relying on long-lived keys or tokens.
Microservices and AI workloads demand deeper visibility. In Part 4, learn how to use OpenTelemetry and Kong Gateway to collect metrics, logs, and traces in Kubernetes - build dashboards, monitor traffic, and detect attacks in real time.

Endpoint Detection and Response (EDR) has become the backbone of modern security programs—and for good reason.

Move beyond chat-based AI. This session shows how agentic AI can automate cloud security workflows, mapping Copilot CLI concepts to real use cases like Terraform compliance, CIS benchmarks, and detection validation.

Zero-downtime patching is critical in cloud-native environments. In Part 5, learn how to use kubectl-ai and Kubernetes blue/green and canary deployments to roll out updates, reduce vulnerability windows, and maintain continuous service availability.

Join the 5th annual SANS Cloud Security Exchange—a one-of-a-kind virtual event where cloud and cybersecurity experts from SANS Institute, Amazon Web Services, Google Cloud, and Microsoft will come together to share thought leadership and technical insights.

SANS 2026 Cloud Security Exchange Summit Solutions Track delivers a focused look at the tools, architectures, and operational strategies driving secure and resilient cloud environments across AWS, Google Cloud, and Microsoft Azure.

This session focuses on AI coding guardrails: practical, developer-friendly controls that help teams adopt coding assistants with confidence while maintaining strong security, governance, and assurance.
The 2026 SANS Cloud Security Research Survey brings together insights from security leaders and practitioners worldwide. This year’s study examines the current state of cloud security, highlighting key challenges, top threats, and the tools organizations are using—or wish they had—to secure cloud environments at scale. Join us for this exclusive webcast to explore the survey findings, gain practical insights, and benchmark your organization’s approach to cloud security.







Obtain hands-on, practical skills from the world's best instructors by taking a SANS course at SANS Security Awareness Summit 2025.


